13. Hardware semaphore (HSEM)
13.1 HSEM introduction
The hardware semaphore block provides 16 (32-bit) register based semaphores.
The semaphores can be used to ensure synchronization between different processes running on the core. The HSEM provides a non-blocking mechanism to lock semaphores in an atomic way. The following functions are provided:
- • Semaphore lock, in two ways:
- – 2-step lock: by writing LOCKID and PROCID, SEC and PRIV to the semaphore, followed by a read check
- – 1-step lock: by reading the LOCKID, SEC and PRIV from the semaphore
- • Interrupt generation when a semaphore is unlocked
- – Each semaphore may generate an interrupt (secure and nonsecure) on one of the interrupt lines
- • Semaphore clear protection
- – A semaphore is only unlocked when LOCKID and PROCID, SEC, and PRIV match
- • Global semaphore clear per LOCKID
- • Secure semaphore lock support
- • Privileged / unprivileged semaphore lock support
- • Semaphore lock protection via semaphore attribute
13.2 HSEM main features
The HSEM includes the following features:
- • 16 (32-bit) semaphores with security, privilege attributes
- • 8-bit PROCID
- • 4-bit LOCKID
- • 1-bit secure domain indication
- • 1-bit privileged domain indication
- • One nonsecure and one secure interrupt lines
- • Lock indication
13.3 Functional description
13.3.1 HSEM block diagram
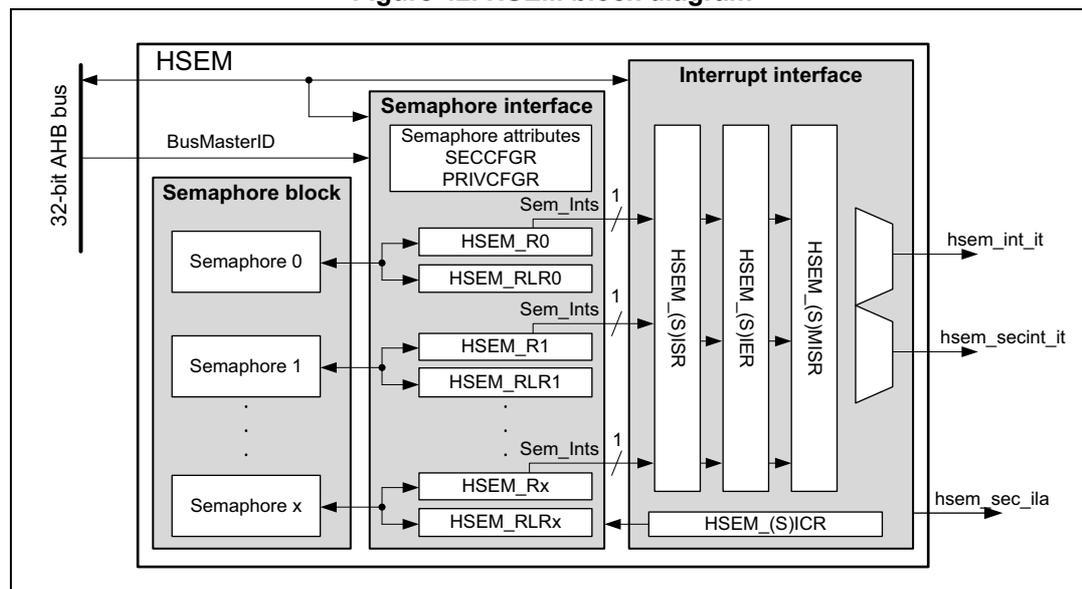
As shown in Figure 42 , the HSEM is based on three sub-blocks:
- • Semaphore, containing the semaphore status and IDs
- • Semaphore interface, providing AHB access to the semaphore via the HSEM_Rx and HSEM_RLRx registers, and the semaphore security, privilege,
- • Interrupt interface, providing control for the interrupts via HSEM_ISR, HSEM_(S)IER, HSEM_(S)MISR, and HSEM_(S)ICR registers.
Figure 42. HSEM block diagram
13.3.2 HSEM internal signals
Table 110. HSEM internal input/output signals
| Signal name | Signal type | Description |
|---|---|---|
| AHB bus | Digital input/output | AHB register access bus |
| BusMasterID | Digital input | AHB bus master ID |
| hsem_int_it | Digital output | Nonsecure interrupt line |
| hsem_secint_it | Digital output | Secure interrupt line |
| hsem_sec_ila | Digital output | Illegal secure access event |
13.3.3 HSEM lock procedures
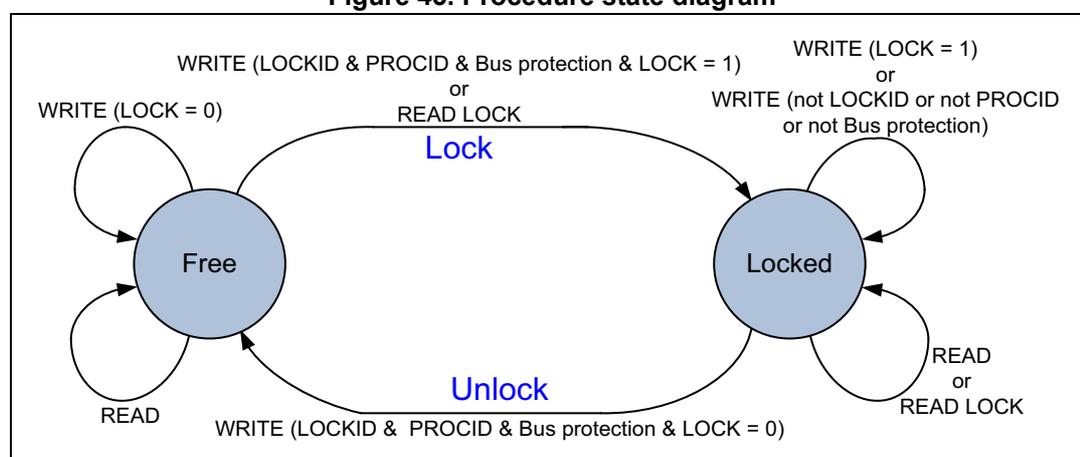
There are two lock procedures, namely 2-step (write) and 1-step (read) lock. The two procedures can be used concurrently.
The semaphore is free when its LOCK bit is 0. In this case, the LOCKID, SEC, PRIV, and PROCID are also 0. When the LOCK bit is 1, the semaphore is locked and the LOCKID indicates which AHB bus master ID has locked it. The PROCID indicates which process of that AHB bus master ID has locked the semaphore. The SEC and PRIV indicated the lock protection, if the AHB bus master that locked the semaphore was running in secure and or privileged mode.
When write locking a semaphore, the written LOCKID, SEC and PRIV must match the AHB bus master ID, SEC and PRIV, and the PROCID is written by the AHB bus master software process taking the lock.
When read locking the semaphore, the LOCKID is taken from the AHB bus master ID, SEC and PRIV are taken from the bus protection, and the PROCID is forced to 0 by hardware. There is no PROCID available with read lock.
Semaphores can be locked only by a processor complying with the attribute settings.
Figure 43. Procedure state diagram
stateDiagram-v2
[*] --> Free
[*] --> Locked
Free --> Free : WRITE (LOCK = 0)
Free --> Free : READ
Free --> Locked : WRITE (LOCKID & PROCID & Bus protection & LOCK = 1) or READ LOCK
Locked --> Free : WRITE (LOCKID & PROCID & Bus protection & LOCK = 0) or Unlock
Locked --> Locked : WRITE (LOCK = 1) or WRITE (not LOCKID or not PROCID or not Bus protection)
Locked --> Locked : READ or READ LOCK
2-step (write) lock procedure
The 2-step lock procedure consists in a write to lock the semaphore, followed by a read to check if the lock has been successful, carried out from the HSEM_Rx register.
- • Write semaphore with PROCID, SEC, PRIV and LOCKID, and LOCK = 1. The SEC, PRIV and LOCKID data written by software must match the AHB bus master information, that is, a secure, privileged, AHB bus master ID = 1 writes data SEC = 1, PRIV = 1 and LOCKID = 1.
Lock is put in place when the semaphore is free at write time.
- • Read-back the semaphore
The software checks the lock status, if PROCID, SEC, PRIV and LOCKID match the written data, then the lock is confirmed.
- • Else retry (the semaphore has been locked by another process or protection level).
A semaphore can be locked only when it is free.
A semaphore can be locked when the PROCID = 0.
Consecutive write attempts with LOCK = 1 to a locked semaphore are ignored.
1-step (read) lock procedure
The 1-step procedure consists in a read to lock and check the semaphore in a single step, carried out from the HSEM_RLRx register.
- • Read lock semaphore with the AHB bus master LOCKID, SEC, PRIV.
- • If read LOCKID, SEC, PRIV matches and PROCID = 0, then lock is put in place. If LOCKID, SEC, PRIV matches and PROCID is not 0, this means that another process from the same LOCKID and protection level, has locked the semaphore with a 2-step (write) procedure.
- • Else retry (the semaphore has been locked by another process or protection level).
A semaphore can only be locked when it is free. When read locking a free semaphore, PROCID is 0. Read locking a locked semaphore returns the LOCKID, SEC, PRIV and PROCID that locked it. All read locks, including the first one that locks the semaphore, return the LOCKID, SEC, PRIV that locks or locked the semaphore.
Note: The 1-step procedure must not be used when running multiple processes of the same AHB bus master ID and protection level. All processes with the same bus protection level using the same semaphore read the same status. When only one process locks the semaphore, each process of that AHB bus master ID and protection level reads the semaphore as locked by itself with the LOCKID, SEC, PRIV.
13.3.4 HSEM write/read/read lock register address
For each semaphore, two AHB register addresses are provided, separated in two banks of 32-bit semaphore registers, spaced by a 0x80 address offset.
In the first register address bank the semaphore can be written (locked/unlocked) and read through the HSEM_Rx registers.
In the second register address bank the semaphore can be read (locked) through the HSEM_RLRx registers.
13.3.5 HSEM unlock procedures
Unlocking a semaphore is a protected process, to prevent accidental clearing by a AHB bus master ID, SEC, PRIV or by a process not having the semaphore lock right. The procedure consists in writing to the semaphore HSEM_Rx register with the corresponding LOCKID, SEC, PRIV and PROCID and LOCK = 0. A semaphore can always be unlocked by the LOCKID, SEC, PRIV, and PROCID that locked it. The semaphore is unlocked regardless of its attribute settings. When unlocked, the LOCKID, SEC, PRIV, and the PROCID are all 0.
Note: When the attributes of a locked semaphore are changed, it can always be unlocked by the AHB bus master ID, SEC, PRIV and process that locked it. To unlock the semaphore the PROCID must match.
When unlocked, an interrupt may be generated to signal the event. To this end, the semaphore nonsecure interrupt and or secure interrupt must be enabled.
The unlock procedure consists in a write to the semaphore HSEM_Rx register with matching LOCKID, SEC, and PRIV, regardless on how the semaphore has been locked (1- or 2-step) and how it is protected by the semaphore attributes.
- • Write semaphore with PROCID, SEC, PRIV, LOCKID, and LOCK = 0
- • If the written data matches the semaphore PROCID, SEC, PRIV and LOCKID and the AHB bus master ID, SEC, PRIV, the semaphore is unlocked and an interrupt may be
generated when enabled, else write is ignored, semaphore remains locked and no interrupt is generated (the semaphore is locked by another process, and bus protection level or the written data does not match the AHB bus master signaling).
Note: Different processes of the AHB bus master ID and bus protection can write any PROCID value. Preventing other processes of the AHB bus master ID and bus protection from unlocking a semaphore must be ensured by software, handling the PROCID correctly.
13.3.6 HSEM LOCKID semaphore clear
All semaphores locked by a LOCKID and bus protection can be unlocked at once by using the HSEM_CR register. Write LOCKID, SEC, PRIV and correct KEY value in HSEM_CR. All locked semaphores with a matching LOCKID, SEC, PRIV are unlocked, and may generate an interrupt when enabled.
An interrupt may be generated for the unlocked semaphore(s). To this end, the semaphore interrupt must be enabled in the HSEM_(S)IER register.
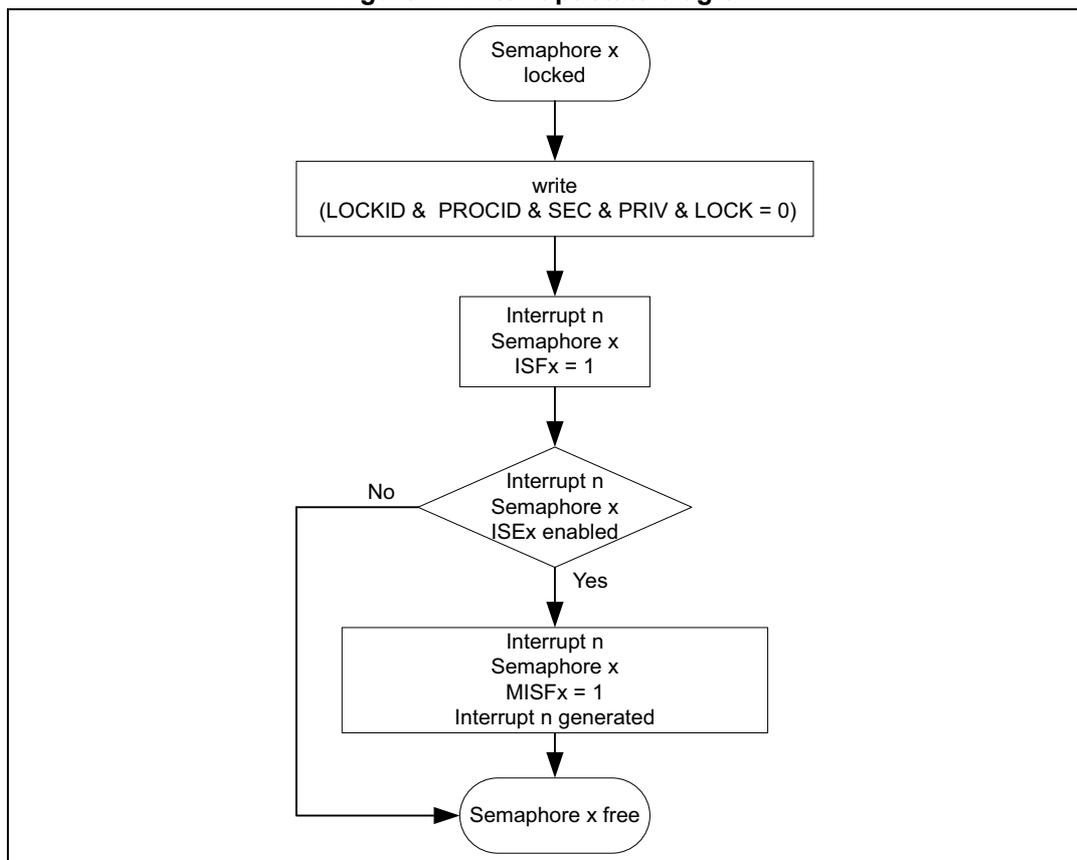
13.3.7 HSEM interrupts
An interrupt line hsem_int_it (nonsecure) and hsem_secint_it (secure) allows each semaphore to generate an interrupt.
An interrupt line provides the following features per semaphore:
- • interrupt enable
- • interrupt clear
- • interrupt status
- • masked interrupt status
- • interrupt generation based on semaphore security attribute settings
With the interrupt enable (HSEM_(S)IER) the semaphores affecting the interrupt line can be enabled. Disabled (masked) semaphore interrupts do not set the masked interrupt status MISF for that semaphore, and do not generate an interrupt on the interrupt line.
The interrupt clear (HSEM_(S)ICR) clears the interrupt status ISF and masked interrupt status MISF of the associated semaphore for the interrupt line.
The interrupt status (HSEM_(S)ISR) mirrors the semaphore interrupt status ISF before the enable.
The masked interrupt status (HSEM_(S)MISR) only mirrors the semaphore enabled interrupt status MISF on the interrupt line. All masked interrupt status MISF of the enabled semaphores must be cleared to clear the interrupt line.
A semaphore with its security attribute set to secure generates only a secure interrupt, nonsecure interrupts are omitted. On the other hand, a nonsecure semaphore may generate nonsecure and secure interrupts.
Figure 44. Interrupt state diagram
graph TD; A([Semaphore x locked]) --> B[write
(LOCKID & PROCID & SEC & PRIV & LOCK = 0)]; B --> C[Interrupt n
Semaphore x
ISFx = 1]; C --> D{Interrupt n
Semaphore x
ISEx enabled}; D -- No --> E([Semaphore x free]); D -- Yes --> F[Interrupt n
Semaphore x
MISFx = 1
Interrupt n generated]; F --> E;
The diagram illustrates the interrupt state transitions for a hardware semaphore (HSEM). It begins with the semaphore in a 'locked' state. A 'write' operation is performed with the condition
(LOCKID & PROCID & SEC & PRIV & LOCK = 0)
. This results in 'Interrupt n' being generated, with the semaphore status 'ISFx = 1'. A decision is then made: 'Interrupt n Semaphore x ISEx enabled'. If 'No', the semaphore becomes 'free'. If 'Yes', the interrupt state changes to 'MISFx = 1' and 'Interrupt n generated', which then leads to the 'Semaphore x free' state.
The procedure to get an interrupt when a semaphore becomes free is described hereafter.
Try to lock semaphore x
- • If the semaphore lock is obtained, no interrupt is needed.
- • If the semaphore lock fails:
- • Clear pending semaphore x interrupt status for the (nonsecure) interrupt line or secure interrupt line in HSEM_(S)ICR.
Re-try to lock the semaphore x again:- – If the semaphore lock is obtained, no interrupt is needed (semaphore has been freed between first try to lock and clear semaphore interrupt status).
- – If the semaphore lock fails, enable the semaphore x (nonsecure) interrupt or secure interrupt line in HSEM_(S)IER.
- • Clear pending semaphore x interrupt status for the (nonsecure) interrupt line or secure interrupt line in HSEM_(S)ICR.
On semaphore x free interrupt, try to lock semaphore x
- • If the semaphore lock is obtained:
Disable the semaphore x (nonsecure) interrupt or secure interrupt in HSEM_(S)IER.
Clear pending semaphore x interrupt status in HSEM_(S)ICR.
- • If the semaphore x lock fails:
Clear pending semaphore x interrupt status in HSEM_(S)ICR.
Try again to lock the semaphore x:- – If the semaphore lock is obtained (semaphore has been freed between first try to lock and semaphore interrupt status clear), disable the semaphore (nonsecure) interrupt or secure interrupt in HSEM_(S)IER.
- – If the semaphore lock fails, wait for semaphore free interrupt.
Note: An interrupt does not lock the semaphore. After an interrupt, either the AHB bus master or the process must still perform the lock procedure to lock the semaphore.
It is possible to have multiple AHB bus masters informed by the semaphore free interrupts. Each AHB bus master gets its interrupt, and the first one to react locks the semaphore.
13.3.8 Semaphore attributes
The HSEM allows semaphores to be protected by the following attributes:
- • security as defined in HSEM_SECCFGR
- • privilege as defined in HSEM_PRIVCFGR
Semaphores with security attribute set to secure can be locked only by a secure access, and generate only a secure interrupt.
Semaphores with privilege attribute set to privilege can be locked only by a privileged access.
Table 111. Semaphore attributes
| Attributes | Interrupt | Description | ||
|---|---|---|---|---|
| Security | Privilege | Secure | Non secure | |
| 0 | 0 | No protection. All locks allowed, any interrupt generated. | ||
| 0 | 1 | Yes | Privileged protection. Only privileged locks allowed, any interrupt generated. | |
| 1 | 0 | Yes | Security protection. Only secure locks allowed and secure interrupt generated. | |
| 1 | 1 | No | Security and privileged protection. Only secure privileged locks allowed and secure interrupt generated. | |
The HSEM allows only authorized AHB bus master ID to lock and unlock semaphores.
- • The AHB bus master 2-step lock write access to the semaphore HSEM_Rx register is checked against the valid bus master ID.
- – Accesses from unauthorized AHB bus master IDs are discarded and do not lock the semaphore.
- • The AHB bus master 1-step lock read access from the semaphore HSEM_RLRx register is checked against the valid bus master ID.
- – An unauthorized AHB bus master ID read from HSEM_RLRx returns all 0.
- • The semaphore unlock write access to the HSEM_CR register is checked against the valid bus master ID. Only the valid bus master ID can write to the HSEM_CR register and unlock any of the LOCKID semaphores.
- – Accesses from unauthorized AHB bus master IDs are discarded and do not clear the LOCKID semaphores.
The relation between bus master/processor and LOCKID is detailed in Table 112 .
Table 112. Authorized AHB bus master ID
| Bus master 0 (CPU) |
| LOCKID = 2 |
Note: Accesses from unauthorized AHB bus master IDs to other registers are granted.
13.4 HSEM registers
Registers must be accessed using word format. Byte and half-word accesses are ignored and have no effect on the semaphores, they generate a bus error.
13.4.1 HSEM register semaphore x (HSEM_Rx)
Address offset: \( 0x000 + 0x4 * x \) ( \( x = 0 \) to \( 15 \) )
Reset value: \( 0x0000\ 0000 \)
The HSEM_Rx must be used to perform a 2-step write lock, read back, and for unlocking a semaphore. Only write accesses with authorized AHB bus master ID is granted. Write accesses with unauthorized AHB bus master IDs are discarded.
When the semaphore x security attribute SECx is enabled the semaphore can only be locked by a secure access. A nonsecure write access generates a secure illegal access event. When the semaphore x security attribute SECx is disabled both secure and nonsecure accesses may lock the semaphore.
When the semaphore x privileged attribute PRIVx is enabled the semaphore can only be locked by a privileged access. An unprivileged write access generates a privileged illegal access event. When the semaphore x privileged attribute PRIVx is disabled both privileged and unprivileged accesses may lock the semaphore.
A locked semaphore can always be unlocked with the semaphore PRIV, SEC and LOCKID that locked the semaphore, regardless of the semaphore attribute settings. To unlock the semaphore the PROCID must match.
When reading the semaphore x with a nonsecure access, the semaphore data are returned only if:
- • the semaphore security attribute SECx is disabled (nonsecure semaphore)
- • the semaphore has been locked with semaphore SEC = 0 (before security attribute SECx has been enabled) and the semaphore PRIV and LOCKID matches.
Else a 0 is returned, and a secure illegal access event is generated.
When reading the semaphore x with an unprivileged access, the semaphore data are returned only when:
- • The semaphore privileged attribute PRIVx is disabled (unprivileged semaphore)
- • The semaphore has been locked with semaphore PRIV = 0 (before security attribute PRIVx has been enabled) and the semaphore SEC and LOCKID matches.
Else a 0 is returned, and an privileged illegal access event is generated.
Semaphore data can only be read when the read access protection (SEC, PRIV and LOCKID) complies with the semaphore attribute protection rules or by a read access from the AHB bus master with the SEC, PRIV and LOCKID that locked the semaphore.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| LOCK | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| rw | |||||||||||||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | PRIV | SEC | LOCKID[3:0] | PROCID[7:0] | ||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | ||
This bit can be written and read by software.
0: On write free semaphore (only when LOCKID and PROCID match), on read semaphore is free.
1: On write try to lock semaphore, on read semaphore is locked.
Bits 30:14 Reserved, must be kept at reset value.
Bit 13 PRIV: Semaphore privilegeWritten by software
- When the semaphore is free and the LOCK bit is at the same time written to 1, and the LOCKID matches the AHB bus master ID, SEC and PRIV matches the AHB bus master definition.
- When the semaphore is unlocked (LOCK written to 0 and AHB bus master ID matched LOCKID, SEC and PRIV matches the AHB bus master definition, the PRIV is cleared to 0.
- When the semaphore is unlocked (LOCK bit written to 0 and AHB bus master ID does not match LOCKID and/or SEC or PRIV do not match AHB bus master definition, the PRIV is not affected.
- Write when LOCK bit is already 1 (semaphore locked), the PRIV is not affected.
- An authorized read returns the stored PRIV value.
0: Semaphore free or locked by unprivileged compartment.
1: Semaphore locked by privilege compartment.
Bit 12 SEC: Semaphore secureWritten by software
- When the semaphore is free and the LOCK bit is at the same time written to 1, and the LOCKID matches the AHB bus master ID, SEC and PRIV matches the AHB bus master definition.
- When the semaphore is unlocked (LOCK written to 0 and AHB bus master ID matched LOCKID, SEC and PRIV matches the AHB bus master definition, the SEC is cleared to 0.
- When the semaphore is unlocked (LOCK bit written to 0 and AHB bus master ID does not match LOCKID and/or SEC or PRIV do not match AHB bus master definition, the SEC is not affected.
- Write when LOCK bit is already 1 (semaphore locked), the SEC is not affected.
- An authorized read returns the stored SEC value.
0: Semaphore free or locked by nonsecure compartment.
1: Semaphore locked by secure compartment.
Bits 11:8 LOCKID[3:0]: Semaphore LOCKIDWritten by software
- When the semaphore is free and the LOCK bit is at the same time written to 1 and the LOCKID matches the AHB bus master ID, SEC and PRIV matches the AHB bus master protection.
- When the semaphore is unlocked (LOCK written to 0 and AHB bus master ID matched LOCKID, SEC and PRIV matches the AHB bus master protection, the LOCKID is cleared to 0.
- When the semaphore is unlocked (LOCK bit written to 0 or AHB bus master ID does not match LOCKID and/or SEC or PRIV do not match AHB bus master protection, the LOCKID is not affected.
- Write when LOCK bit is already 1 (semaphore locked), the LOCKID is not affected.
- An authorized read returns the stored LOCKID value.
Bits 7:0 PROCID[7:0] : Semaphore PROCID
Written by software
-When the semaphore is free and the LOCK is written to 1, and the LOCKID matches the AHB bus master ID, SEC and PRIV matches the AHB bus master definition, PROCID is set to the written data.
- When the semaphore is unlocked, LOCK written to 0 and AHB bus master ID matched LOCKID, SEC and PRIV matches the AHB bus master protection, the PROCID is cleared to 0.
- When the semaphore is unlocked, LOCK bit written to 0 and AHB bus master ID does not match LOCKID and/or SEC or PRIV do not match the AHB bus master definition, the PROCID is not affected.
- Write when LOCK bit is already 1 (semaphore locked), the PROCID is not affected.
- An authorized read returns the stored PROCID value.
13.4.2 HSEM read lock register semaphore x (HSEM_RLRx)
Address offset: 0x080 + 0x4 * x (x = 0 to 15)
Reset value: 0x0000 0000
Accesses the same physical bits as HSEM_Rx. The HSEM_RLRx must be used to perform a 1-step read lock. Only read accesses with authorized AHB bus master ID is granted. Read accesses with unauthorized AHB bus master IDs are discarded and return 0.
When the semaphore x security attribute SECx is enabled the semaphore can only be locked by a secure access. A nonsecure read access returns 0 and generates a secure illegal access event. When the semaphore x security attribute SECx is disabled both secure and nonsecure accesses may lock the semaphore.
When the semaphore x privileged attribute PRIVx is enabled the semaphore can be locked only by a privileged access. An unprivileged read access reads 0 and generates a privileged illegal access event. When the semaphore x privileged attribute PRIVx is disabled both privileged and unprivileged accesses may lock the semaphore.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| LOCK | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| r | |||||||||||||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | PRIV | SEC | LOCKID[3:0] | PROCID[7:0] | ||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | ||
Bit 31 LOCK : Lock indication
This bit is read only by software at this address.
- When the semaphore is free:
A read with a valid AHB bus master ID and SEC and PRIV locks the semaphore and returns 1.
- When the semaphore is locked:
A read with a valid AHB bus master ID and SEC and PRIV returns 1 (the LOCKID and SEC and PRIV and PROCID reflect the already locked semaphore information).
Bits 30:14 Reserved, must be kept at reset value.
Bit 13 PRIV : Semaphore privilege
This field is read only by software at this address.
- When the semaphore is free:
A read with a valid AHB bus master ID and SEC and PRIV locks the semaphore and hardware sets the PRIV to the valid AHB bus master privileged definition.
- When the semaphore is locked:
A read with a valid AHB bus master ID and SEC and PRIV returns the PRIV of the AHB bus master that has locked the semaphore.
0: Semaphore free or locked by unprivileged compartment.
1: Semaphore locked by privileged compartment.
Bit 12 SEC : Semaphore secure.
This field is read only by software at this address.
- When the semaphore is free:
A read with a valid AHB bus master ID and SEC and PRIV locks the semaphore and hardware sets the SEC to the valid AHB bus master security definition.
- When the semaphore is locked:
A read with a valid AHB bus master ID and SEC and PRIV returns the SEC of the AHB bus master that has locked the semaphore.
0: Semaphore free or locked by nonsecure compartment.
1: Semaphore locked by secure compartment.
Bits 11:8 LOCKID[3:0] : Semaphore LOCKID
This field is read only by software at this address.
On a read, when the semaphore is free, the hardware sets the LOCKID to the AHB bus master ID reading the semaphore. The LOCKID of the AHB bus master locking the semaphore is read.
On a read when the semaphore is locked, this field returns the LOCKID of the AHB bus master that has locked the semaphore.
Bits 7:0 PROCID[7:0] : Semaphore processor ID
This field is read only by software at this address.
- On a read when the semaphore is free:
A read with a valid AHB bus master ID and SEC and PRIV locks the semaphore and hardware sets the PROCID to 0.
- When the semaphore is locked:
A read with a valid AHB bus master ID and SEC and PRIV returns the PROCID of the AHB bus master that has locked the semaphore.
13.4.3 HSEM nonsecure interrupt enable register (HSEM_IER)
Address offset: 0x100
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| ISE[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:16 Reserved, must be kept at reset value.
Bits 15:0 ISE[15:0] : Nonsecure Interrupt semaphore x enable bit (x = 0 to 15)
This bit is read and written by software.
When semaphore x SECx is disabled, bit x can be accessed with secure and nonsecure access.
When semaphore x SECx is enabled, bit x is forced to 0 and cannot be accessed, write to this bit is discarded and a read returns 0.
When semaphore x PRIVx is disabled, bit x can be accessed with privilege and unprivileged access.
When semaphore x PRIVx is enabled, bit x can be accessed only with privileged access. Unprivileged write to this bit is discarded, unprivileged read returns 0.
0: Nonsecure Interrupt generation for semaphore x disabled (masked)
1: Nonsecure Interrupt generation for semaphore x enabled (not masked)
13.4.4 HSEM nonsecure interrupt clear register (HSEM_ICR)
Address offset: 0x104
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| ISC[15:0] | |||||||||||||||
| rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 |
Bits 31:16 Reserved, must be kept at reset value.
Bits 15:0 ISC[15:0] : Nonsecure Interrupt semaphore x clear bit (x = 0 to 15)
This bit is written by software, and is always read 0.
When semaphore x SECx is disabled, bit x can be accessed with secure and nonsecure access.
When semaphore x SECx is enabled, bit x cannot be accessed, write to this bit is discarded.
When semaphore x PRIVx is disabled, bit x can be accessed with privileged and unprivileged access.
When semaphore x PRIVx is enabled, bit x can only be accessed with privileged access. Unprivileged write to this bit is discarded.
0: Nonsecure Interrupt semaphore x status ISFx and masked status MISFx not affected.
1: Nonsecure Interrupt semaphore x status ISFx and masked status MISFx cleared.
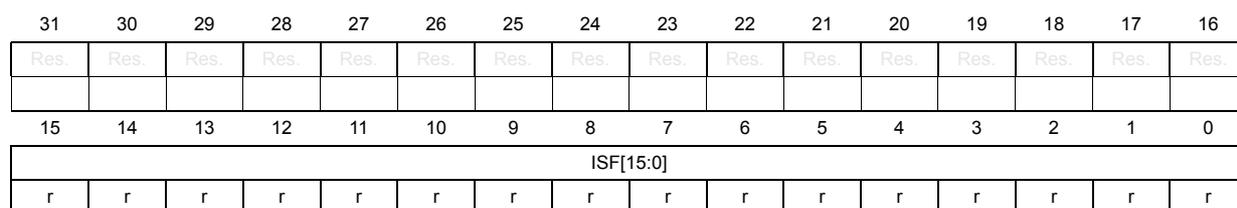
13.4.5 HSEM nonsecure interrupt status register (HSEM_ISR)
Address offset: 0x108
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| ISF[15:0] | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
Bits 31:16 Reserved, must be kept at reset value.
Bits 15:0 ISF[15:0] : Interrupt semaphore x status bit before enable (mask) (x = 0 to 15)
This bit is set by hardware, and reset only by software. This bit is cleared by software writing the corresponding HSEM_ICR bit.
0: Interrupt semaphore x status, no interrupt pending
1: Interrupt semaphore x status, interrupt pending
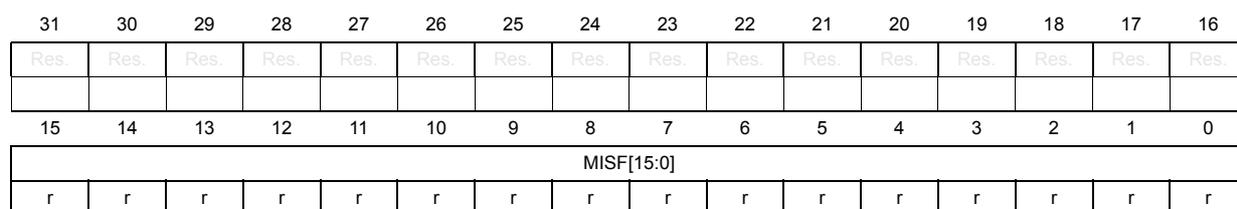
13.4.6 HSEM nonsecure interrupt status register (HSEM_MISR)
Address offset: 0x10C
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| MISF[15:0] | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
Bits 31:16 Reserved, must be kept at reset value.
Bits 15:0 MISF[15:0] : Masked nonsecure interrupt semaphore x status bit after enable (mask) (x = 0 to 15)
This bit is set by hardware and read only by software. This bit is cleared by software writing the corresponding HSEM_ICR bit. This bit is read as 0 when semaphore x status is masked in HSEM_IER bit x.
When semaphore x SECx is disabled, bit x can be accessed with secure and nonsecure access.
When semaphore x SECx is enabled, bit x cannot be accessed, read returns 0.
When semaphore x PRIVx is disabled, bit x can be accessed with privileged and unprivileged access.
When semaphore x PRIVx is enabled, bit x can be accessed only with privileged access.
Unprivileged read returns 0.
0: Nonsecure interrupt semaphore x status after masking not pending
1: Nonsecure interrupt semaphore x status after masking pending
13.4.7 HSEM secure interrupt enable register (HSEM_SIER)
Address offset: 0x180
Reset value: 0x0000 0000
This register provides access security, a nonsecure write access is discarded and a nonsecure read returns all 0. Both nonsecure read and write generate a secure illegal access event (when security is disabled by user option TZEN this register cannot be accessed).
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| SISE[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:16 Reserved, must be kept at reset value.
Bits 15:0 SISE[15:0] : Secure interrupt semaphore x enable bit (x = 0 to 15)
This bit is read and written by software.
When semaphore x PRIVx is disabled, bit x can be accessed with secure privilege and secure unprivileged access.
When semaphore x PRIVx is enabled, bit x can be accessed only with secure privilege access. secure unprivileged write to this bit is discarded, secure unprivileged read return 0 value.
0: Secure interrupt generation for semaphore x is disabled (masked).
1: Secure interrupt generation for semaphore x is enabled (not masked).
13.4.8 HSEM secure interrupt clear register (HSEM_SICR)
Address offset: 0x184
Reset value: 0x0000 0000
This register provides access security, a nonsecure write access is discarded and a nonsecure read returns all 0. Both nonsecure read and write generate a secure illegal access event (when security is disabled by user option TZEN this register cannot be accessed).
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| SISC[15:0] | |||||||||||||||
| rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 |
Bits 31:16 Reserved, must be kept at reset value.
Bits 15:0 SISC[15:0] : Secure interrupt semaphore x clear bit (x = 0 to 15)
This bit is written by software, and is always read 0.
When semaphore x PRIVx is disabled, bit x can be accessed with secure privilege and secure unprivileged access.
When semaphore x PRIVx is enabled, bit x can be accessed only with secure privilege access. Secure unprivileged write to this bit is discarded.
0: Secure interrupt semaphore x status ISFx and masked status MISFx not affected.
1: Secure interrupt semaphore x status ISFx and masked status MISFx cleared.
13.4.9 HSEM secure interrupt status register (HSEM_SISR)
Address offset: 0x188
Reset value: 0x0000 0000
This register provides access security, a nonsecure read returns all 0. Both nonsecure read and write generate a secure illegal access event (when security is disabled by user option TZEN, then this register cannot be accessed any longer).
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| SISF[15:0] | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
Bits 31:16 Reserved, must be kept at reset value.
Bits 15:0 SISF[15:0] : Secure interrupt semaphore x status bit before enable (mask) (x = 0 to 15)
This bit is set by hardware and read only by software.
Bit is cleared by software writing the corresponding HSEM_SCnICR bit x.
When semaphore x PRIVx is disabled, bit x can be accessed with secure privilege and secure unprivileged access.
When semaphore x PRIVx is enabled, bit x can be accessed only with secure privilege access. Secure unprivileged read return 0 value.
0: Secure interrupt semaphore x status, no interrupt pending.
1: Secure interrupt semaphore x status, interrupt pending.
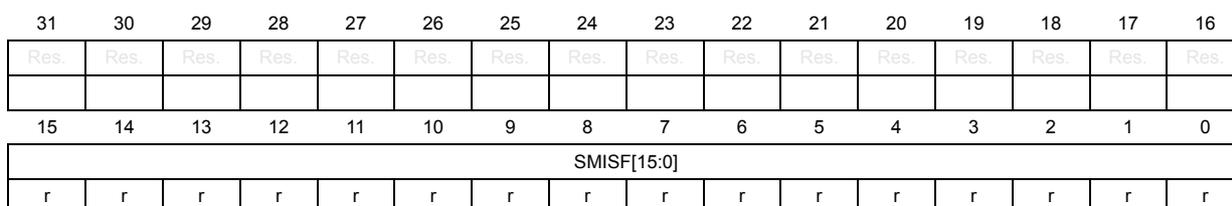
13.4.10 HSEM secure masked interrupt status register (HSEM_SMISR)
Address offset: 0x18C
Reset value: 0x0000 0000
This register provides access security, a nonsecure read returns all 0. Both nonsecure read and write generate a secure illegal access event (when security is disabled by user option TZEN, then this register cannot be accessed).
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| SMISF[15:0] | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
Bits 31:16 Reserved, must be kept at reset value.
Bits 15:0 SMISF[15:0] : Secure masked interrupt semaphore x status bit after enable (mask) (x = 0 to 15)
This bit is set by hardware and read only by software.
Bit is cleared by software writing the corresponding HSEM_SCnICR bit x.
Bit is read as 0 when semaphore x status is masked in HSEM_SCnIER bit x.
When semaphore x PRIVx is disabled, bit x can be accessed with secure privilege and secure unprivileged access.
When semaphore x PRIVx is enabled, bit x can be accessed only with secure privilege access. Secure unprivileged read return 0 value.
0: Secure interrupt semaphore x status after masking not pending.
1: Secure interrupt semaphore x status after masking pending.
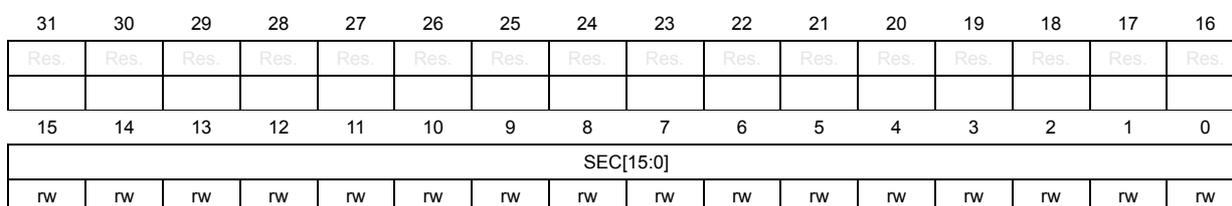
13.4.11 HSEM security configuration register (HSEM_SECCFGR)
Address offset: 0x200
Reset value: 0x0000 0000
This register provides write access security and privileged, a nonsecure or unprivileged write access is discarded and generates an illegal access event. There is no read protection and the register data can be read by any accesses (when security is disabled by user option TZEN this register can no longer be written).
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| SEC[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:16 Reserved, must be kept at reset value.
Bits 15:0 SEC[15:0] : Semaphore x security attribute (x = 0 to 15)
This bit is set and cleared by software.
0: Semaphore x non-security, can be accessed by both secure and nonsecure processors. When unlocking semaphore x both a secure and nonsecure interrupt can be generated.
1: Semaphore x security, can be accessed only by secure processors. When unlocking semaphore x only a secure interrupt can be generated.
13.4.12 HSEM privilege configuration register (HSEM_PRIVCFGR)
Address offset: 0x210
Reset value: 0x0000 0000
This register provides write access privilege protection, an unprivileged write access is discarded. There is no read protection and the register data can be read by both privilege and unprivileged accesses.
There is no read protection and the register data can be read by both secure and nonsecure accesses.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| PRIV[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:16 Reserved, must be kept at reset value.
Bits 15:0 PRIV[15:0] : Semaphore x privilege attribute (x = 0 to 15)
This bit is set and cleared by software.
When semaphore x SECx is disabled, bit x can be write accessed with secure privileged and nonsecure privileged access.
When semaphore x SECx is enabled, bit x can only be write accessed with secure privilege access. Nonsecure privileged write access is discarded. Both secure and nonsecure read return the register bit x value
0: Semaphore x unprivileged, can be accessed by both privileged and unprivileged processors.
1: Semaphore x privileged, can be accessed only by privileged processors.
13.4.13 HSEM clear register (HSEM_CR)
Address offset: 0x230
Reset value: 0x0000 0000
Only write accesses with authorized AHB bus master ID are granted. Write accesses with unauthorized AHB bus master ID are discarded.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| KEY[15:0] | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | PRIV | SEC | LOCKID[3:0] | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | |||
| w | w | w | w | w | w | ||||||||||
Bits 31:16 KEY[15:0] : Semaphore clear key
This field can be written by software and is always read 0.
If this key value does not match HSEM_KEYR.KEY, semaphores are not affected.
If this key value matches HSEM_KEYR.KEY, all semaphores matching the LOCKID are cleared to the free state.
Bits 15:14 Reserved, must be kept at reset value.
Bit 13 PRIV : PRIV value of semaphores to be cleared.
This field can be written by software, is always read 0.
Indicates the PRIV for which the semaphores are cleared when writing the HSEM_CR.
Bit 12 SEC : SEC value of semaphores to be cleared.
This field can be written by software, is always read 0.
Indicates the SEC for which the semaphores are cleared when writing the HSEM_CR
Bits 11:8 LOCKID[3:0] : LOCKID of semaphores to be cleared
This field can be written by software and is always read 0.
This field indicates the LOCKID for which the semaphores are cleared when writing the HSEM_CR.
Bits 7:0 Reserved, must be kept at reset value.
13.4.14 HSEM clear semaphore key register (HSEM_KEYR)
Address offset: 0x234
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| KEY[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
Bits 31:16 KEY[15:0] : Semaphore clear key
This field can be written and read by software.
Key value to match when clearing semaphores.
Bits 15:0 Reserved, must be kept at reset value.
13.4.15 HSEM register map
Table 113. HSEM register map and reset values
| Offset | Register name | 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 | 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0x000 | HSEM_R0 | LOCK | Res. | Res. | Res. | Res. | Res. | LOCKID [3:0] | PROCID[7:0] | ||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||||||||||||
| 0x004 | HSEM_R1 | LOCK | Res. | Res. | Res. | Res. | Res. | LOCKID [3:0] | PROCID[7:0] | ||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||||||||||||
| ⋮ | |||||||||||||||||||||||||||||||||
| 0x03C | HSEM_R15 | LOCK | Res. | Res. | Res. | Res. | Res. | LOCKID [3:0] | PROCID[7:0] | ||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||||||||||||
| 0x080 | HSEM_RLR0 | LOCK | Res. | Res. | Res. | Res. | Res. | LOCKID [3:0] | PROCID[7:0] | ||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||||||||||||
| 0x084 | HSEM_RLR1 | LOCK | Res. | Res. | Res. | Res. | Res. | LOCKID [3:0] | PROCID[7:0] | ||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||||||||||||
| ⋮ | |||||||||||||||||||||||||||||||||
| 0x0BC | HSEM_RLR15 | LOCK | Res. | Res. | Res. | Res. | Res. | LOCKID [3:0] | PROCID[7:0] | ||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||||||||||||
| 0x100 | HSEM_IER | Res. | |||||||||||||||||||||||||||||||
| Reset value | |||||||||||||||||||||||||||||||||
| 0x104 | HSEM_ICR | Res. | |||||||||||||||||||||||||||||||
| Reset value | |||||||||||||||||||||||||||||||||
| 0x108 | HSEM_ISR | Res. | |||||||||||||||||||||||||||||||
| Reset value | |||||||||||||||||||||||||||||||||
| 0x10C | HSEM_MISR | Res. | |||||||||||||||||||||||||||||||
| Reset value | |||||||||||||||||||||||||||||||||
| 0x180 | HSEM_SIER | Res. | |||||||||||||||||||||||||||||||
| Reset value | |||||||||||||||||||||||||||||||||
| 0x184 | HSEM_SICR | Res. | |||||||||||||||||||||||||||||||
| Reset value | |||||||||||||||||||||||||||||||||
| 0x188 | HSEM_SISR | Res. | |||||||||||||||||||||||||||||||
| Reset value | |||||||||||||||||||||||||||||||||
Table 113. HSEM register map and reset values (continued)
| Offset | Register name | 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 | 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0x18C | HSEM_SMISR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | SMISF[15:0] | |||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||||||||||||||||||
| 0x200 | HSEM_SECCFGR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | SEC[15:0] | |||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||||||||||||||||||
| 0x210 | HSEM_PRIVCFGR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PRIV[15:0] | |||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||||||||||||||||||
| 0x230 | HSEM_CR | KEY[15:0] | Res. | Res. | PRIV | SEC | LOCKID[3:0] | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | ||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||
| 0x234 | HSEM_KEYR | KEY[15:0] | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | |||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||||||||
Refer to Section 2.3: Memory organization for the register boundary addresses.