8. Illegal access controller (IAC)
8.1 IAC introduction
The RIF (resource isolation framework) is a comprehensive set of hardware blocks designed to enforce and manage the isolation of STM32 hardware resources, such as memory and peripherals.
The RIF uses the IAC (illegal access controller) to centralize the detection of RIF-related illegal accesses, managed by a secure application.
8.2 IAC main features
- • Centralized detection of RIF-related illegal accesses, managed by a secure application. Supported illegal accesses are: secure, privileged.
- • Only accessible by secure privileged CPU
8.3 IAC implementation
The index of the peripherals managed by the IAC in this device is defined in Table 28 . Indexes 0 to 127 are also used in the RIFSC to configure the proper access control using RISUP blocks.
Table 28. Peripheral indexes in IAC
| Peripherals 31 to 0 | |||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 | 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| TIM5 | TIM4 | TIM3 | TIM2 | TIM1 | FDCAN1/2/3 | LPUART1 | USART10 | UART9 | UART8 | UART7 | USART6 | UART5 | UART4 | USART3 | USART2 | USART1 | I3C2 | I3C1 | I2C4 | I2C3 | I2C2 | I2C1 | SAI2 | - | SAI1 | SPI6/I2S6 | SPI5 | SPI4 | SPI3/I2S3 | SPI2/I2S2 | SPI1/I2S1 |
| Peripherals 63 to 32 | |||||||||||||||||||||||||||||||
| 63 | 62 | 61 | 60 | 59 | 58 | 57 | 56 | 55 | 54 | 53 | 52 | 51 | 50 | 49 | 48 | 47 | 46 | 45 | 44 | 43 | 42 | 41 | 40 | 39 | 38 | 37 | 36 | 35 | 34 | 33 | 32 |
| - | SYSCONF | SPDIFRX | GB-ETH | - | UCPD | OTG1_FS | OTG1_HS | MDIOS | SDMMC2 | SDMMC1 | MDF1 | ADF1 | LPTIM5 | LPTIM4 | LPTIM3 | LPTIM2 | LPTIM1 | GFXTIM | TIM18 | TIM17 | TIM16 | TIM15 | TIM14 | TIM13 | TIM12 | TIM11 | TIM10 | TIM9 | TIM8 | TIM7 | TIM6 |
| Peripherals 95 to 64 | |||||||||||||||||||||||||||||||
| 95 | 94 | 93 | 92 | 91 | 90 | 89 | 88 | 87 | 86 | 85 | 84 | 83 | 82 | 81 | 80 | 79 | 78 | 77 | 76 | 75 | 74 | 73 | 72 | 71 | 70 | 69 | 68 | 67 | 66 | 65 | 64 |
| - | DCMI | DCMIPP | CSI2HOST | - | FMC | XSPIM | XSPI3 | XSPI2 | XSPI1 | - | MCE4 | MCE3 | MCE2 | MCE1 | CRYPT1 | HASH | SAES | PKA | RNG | - | - | - | - | - | - | WWDG | IWDG | CRC | - | VREFBUF | ADC12 |
Table 28. Peripheral indexes in IAC (continued)
| Peripherals 127 to 96 | |||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 127 | 126 | 125 | 124 | 123 | 122 | 121 | 120 | 119 | 118 | 117 | 116 | 115 | 114 | 113 | 112 | 111 | 110 | 109 | 108 | 107 | 106 | 105 | 104 | 103 | 102 | 101 | 100 | 99 | 98 | 97 | 96 |
| - | - | - | - | - | - | - | - | - | - | - | - | - | - | - | - | - | - | - | - | - | NPU - Neural ART | - | LTDC_L2 | LTDC_L1 | LTDC_CMN | DMA2D | GFXMMU | GPU | ICACHE | VENC | JPEG |
| Peripherals 159 to 128 | |||||||||||||||||||||||||||||||
| 159 | 158 | 157 | 156 | 155 | 154 | 153 | 152 | 151 | 150 | 149 | 148 | 147 | 146 | 145 | 144 | 143 | 142 | 141 | 140 | 139 | 138 | 137 | 136 | 135 | 134 | 133 | 132 | 131 | 130 | 129 | 128 |
| - | RIFSC | RISAF23 (BKPSRAM) | RISAF22 (AHB RAM2) | RISAF21 (AHB RAM1) | - | RISAF15 (Cache config) | RISAF14 (FMC) | RISAF13 (XSPI3) | RISAF12 (XSPI2) | RISAF11 (XSPI1) | - | RISAF9 (VENGRAM) | RISAF8 (CACHEAXI) | RISAF7 (FLEXRAM) | RISAF6 (CPU_MST) | RISAF5 (NPU_MST1) | RISAF4 (NPU_MST0) | RISAF3 (AXISRAM2) | RISAF2 (AXISRAM1) | RISAF1 (TCM) | IAC | PWR_CTRL | RCC | BSEC | TAMP | RTC | - | HPDMA1 | GPDMA1 | EXTI | CM55 |
8.4 IAC functional description
8.4.1 IAC block diagram
Figure 9 shows the IAC block diagram, in context.
Figure 9. IAC block diagram
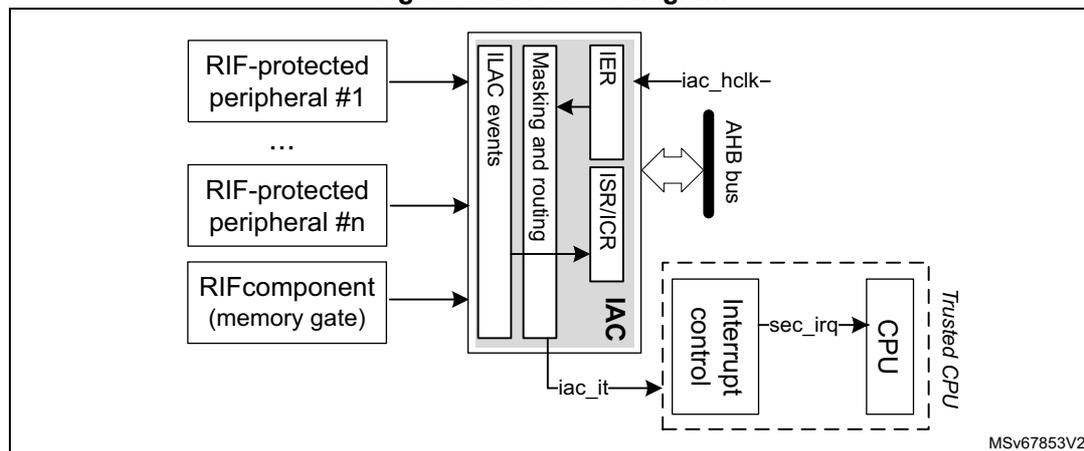
The diagram illustrates the IAC block diagram. On the left, three boxes represent 'RIF-protected peripheral #1', 'RIF-protected peripheral #n', and 'RIF component (memory gate)'. Arrows from these boxes point into a central 'IAC' block. The 'IAC' block contains four sub-components: 'ILAC events', 'Masking and routing', 'IER', and 'ISR/ICR'. An arrow labeled 'iac_hclk' points from the top right into the 'IAC' block. A double-headed arrow labeled 'AHB bus' connects the 'IAC' block to a dashed box on the right. Inside this dashed box, labeled 'Trusted CPU', are two sub-components: 'Interrupt control' and 'CPU'. An arrow labeled 'sec_irq' points from 'Interrupt control' to 'CPU'. An arrow labeled 'iac_it' points from the 'IAC' block to 'Interrupt control'. The diagram is labeled MSV67853V2 in the bottom right corner.
8.4.2 IAC internal signals
Table 29 lists the internal signals available at IAC level, not at product level.
Table 29. IAC internal signals
| Name | Type | Description |
|---|---|---|
| iac_hclk | Digital input | AHB bus clock |
| iac_it | Digital output | Global interrupt request |
8.4.3 IAC reset and clocks
The IAC peripheral has a dedicated clock and reset control in the RCC.
The IAC requires its clock in order to trigger an interrupt request event.
8.4.4 IAC use in RIF
The IAC gathers illegal events generated within the system when an illegal access is detected. The IAC can then generate a secure interrupt towards the secure CPU, if needed. By default, all events in the IAC are masked.
The IAC has room for 160 interrupt sources. Each source corresponds to an IAC index from 0 to 159. The interrupt sources from non-RIF-aware peripherals occupy most of the first 128 indexes. The interrupt sources from RIF-aware peripherals and RIF firewalls occupy indexes from 128 onwards. All these sources are defined in Section 8.3 .
8.4.5 IAC management by trusted application
For each interrupt source of index <i>, an illegal access sets the IAFi flag in IAC_ISRx. A secure privileged application can clear this flag using the corresponding bit in IAC_ICRx. An IAC interrupt is triggered when IAFi is set while IAIEi is set in IAC_IERx.
Indexes between 0 to 127 are assigned to non-RIF-aware peripherals, with a RISUP block instantiated in front of its configuration port to filter configuration accesses. The programming of these RISUP blocks (in the RIFSC) uses the same index as the IAC.
Indexes 128 and above are assigned to RIF components and RIF-aware peripherals. These peripherals can block illegal accesses to their configuration registers (without RISUP).
For RIF-aware peripherals protecting a memory (RISAF), a secure privileged application can obtain, in the peripheral, more details about the cause of the illegal access event:
- • The illegal access status register (xx_IASR) indicates if it is a configuration access error (CAEF= 1), or/and a system bus access error (IAEF = 1).
- • The illegal access error status register (xx_IAESR) and the illegal address register (xx_IADDR) give detailed information on the system bus access error.
The IAC interrupt handler must clear IAFi in IAC_ISR before clearing the error flag(s) in the firewall peripheral xx (using xx_IACR register). Otherwise, an illegal access can occur between clearing the flags in the firewall and clearing the flag in the IAC, and the application is unaware of this error.
8.5 IAC interrupts
The RIF interrupt management in the IAC is summarized in Table 30 .
Note: Only secure privileged application can enable, read, and clear illegal access interrupts. If there is an illegal access to the IAC itself, the status flag corresponding to the IAC index in Section 8.3 is set.
Table 30. IAC interrupt request
| Acronym | Interrupt event | Event flag in IAC_ISR | Enable control bit in IAC_IER | Interrupt clear method |
|---|---|---|---|---|
| IAC | Illegal access error | IAF | IAIE | Set IAF bit in IAC_ICR |
8.6 IAC registers
All IAC registers are accessed only by words (32 bits).
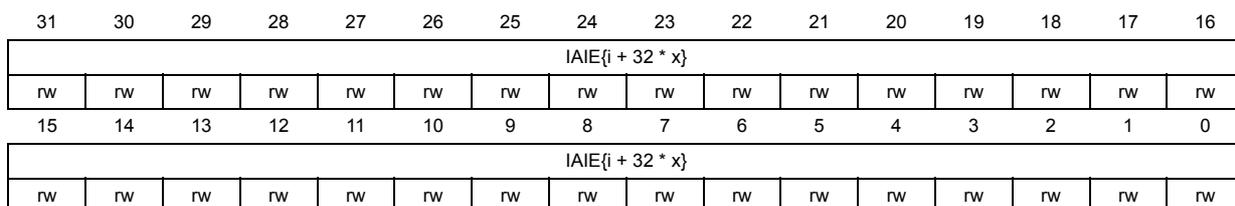
8.6.1 IAC interrupt enable register x (IAC_IERx)
Address offset: 0x000 + 0x4 * x (x = 0 to 5)
Reset value: 0x0000 0000
Secure privileged, read and write only.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| IAIE{i + 32 * x} | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| IAIE{i + 32 * x} | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 IAIE{i + 32 * x} : Illegal access interrupt enable for peripheral {i + 32 * x} (i = 0 to 31)
Each bit is set to unmask illegal access events from peripheral {i + 32 * x}.
0: Illegal access event from peripheral does not generate interrupt (masked).
1: Illegal access event from peripheral can generate interrupts (unmasked).
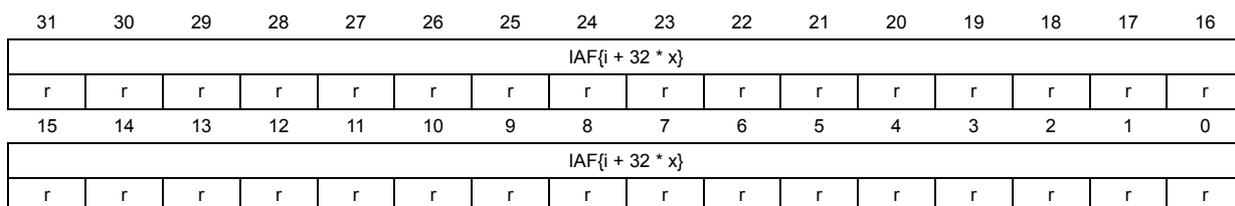
8.6.2 IAC interrupt status register x (IAC_ISRx)
Address offset: 0x080 + 0x4 * x (x = 0 to 5)
Reset value: 0x0000 0000
Secure privileged, read only.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| IAF{i + 32 * x} | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| IAF{i + 32 * x} | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
Bits 31:0 IAF{i + 32 * x} : Illegal access interrupt enable for peripheral {i + 32 * x} (i = 0 to 31)
Each bit is set when an illegal access event occurs in the peripheral {i + 32 * x} (see Section 8.3 for details). This bit is cleared when the corresponding IAF bit is set in IAC_ICRx.
0: No illegal access event detected for the peripheral (since reset or the last time this bit was cleared).
1: At least one illegal access event has been detected for the peripheral (since the last time this bit was cleared).
8.6.3 IAC interrupt clear register x (IAC_ICRx)
Address offset: 0x100 + 0x4 * x (x = 0 to 5)
Reset value: 0x0000 0000
Secure, privileged write only.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| IAF{i + 32 * x} | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| IAF{i + 32 * x} | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
Bits 31:0 IAF{i + 32 * x} : Illegal access flag clear for peripheral {i + 32 * x} (i = 0 to 31)
Setting each bit clears the status flag of the illegal access event {i + 32 * x} in IAC_ISRx.
0: IAF {i + 32 * x} flag status not affected
1: IAF {i + 32 * x} flag status cleared in IAC_ISRx
8.6.4 IAC ILAC input status register x (IAC_IISRx)
Address offset: 0x36C + 0x4 * x (x = 0 to 5)
Reset value: 0xFFFF FF7F, 0x77FF FFFF, 0x77DF F03B, 0x0000 05FF, 0x7BEF FFEF, 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| ILACIN{i + 32 * x} | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| ILACIN{i + 32 * x} | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
Bits 31:0 ILACIN{i + 32 * x} : Illegal access input {i + 32 * x} (i = 0 to 31)
0: ILAC input {i + 32 * x} to IAC not present
1: ILAC input {i + 32 * x} to IAC present
8.6.5 IAC register map
Table 31. IAC register map and reset values
| Offset | Register name | 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 | 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0x000 +0x4*x (x = 0 to 5) Last address: 0x014 | IAC_IERx | IAIE{i + 32 * x} | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x018-0x07C | Reserved | Reserved | |||||||||||||||||||||||||||||||
| 0x080 +0x4*x (x = 0 to 5) Last address: 0x094 | IAC_ISRx | IAF{i + 32 * x} | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x098-0x0FC | Reserved | Reserved | |||||||||||||||||||||||||||||||
| 0x100 +0x4*x (x = 0 to 5) Last address: 0x114 | IAC_ICRx | IAF{i + 32 * x} | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x118-0x368 | Reserved | Reserved | |||||||||||||||||||||||||||||||
| 0x36C +0x4*x (x = 0 to 5) Last address: 0x384 | IAC_IISRx | ILACIN{i + 32 * x} | |||||||||||||||||||||||||||||||
| Reset value | 0xFFFF FF7F, 0x77FF FFFF, 0x77DF F03B, 0x0000 05FF, 0x7BEF FFEF, 0x0000 0000 | ||||||||||||||||||||||||||||||||
Refer to Section 2.3: Memory organization for the register boundary addresses.