7. Resource isolation slave unit for address space protection (full version) (RISAF)
7.1 RISAF introduction
The RIF (resource isolation framework) is a comprehensive set of hardware blocks designed to enforce and manage isolation of STM32 hardware resources, like memory and peripherals.
Through RISAF registers, a secure privileged software application or the application to whom the configuration has been delegated, assigns memory regions and subregions to one or more security domains (secure, privileged, compartment).
7.2 RISAF main features
- • Assign variable sized address space regions and subregions to security domains.
- • Make memory regions:
- – Restricted to one or more than one hardware compartments
- – Secure-only or nonsecure-only
- – Privileged-only or privileged/unprivileged
- – Read-only, write-only, or read/write
- • The secure privileged software can delegate configuration and positioning of a subregion (within a region) to another security domain.
- • The secure privileged software can delegate configuration and positioning of a subregion (within a nonsecure region) to a nonsecure privileged software.
7.3 RISAF implementation
The following table describes the characteristics of the available RISAFs, including watermark programming details (such as granularity and protected address space).
Table 24. RISAF resource assignment
| Protected memory | Resource name | Target bus | IAC index | Number of configurable base regions | Granularity | Address space size and alignment | CID management |
|---|---|---|---|---|---|---|---|
| TCM | RISAF1 | AXI | 139 | 7 | 4 Kbytes | 1 Gbyte | Programmable CID filtering on system bus (CID=0 to 7). To delegate to nonsecure set DCCID = 1. |
| AXISRAM1 | RISAF2 | 140 | 1 Mbyte | ||||
| AXISRAM2 | RISAF3 | 141 | |||||
| NPU master 0 | RISAF4 | 142 | 11 | 4 Gbytes | |||
| NPU master 1 | RISAF5 | 143 | |||||
| CPU master | RISAF6 | 144 | |||||
| FLEXRAM | RISAF7 | AXI | 145 | 7 | 4 Kbytes | 400 Kbytes | |
| CACHEAXI/ AXISRAM7 | RISAF8 | 146 | 256 Kbytes | ||||
| VENCRAM/ AXISRAM8 | RISAF9 | 147 | 128 Kbytes | ||||
| XSPI1 | RISAF11 | 149 | 256 Mbytes | ||||
| XSPI2 | RISAF12 | 150 | |||||
| XSPI3 | RISAF13 | 151 | |||||
| FMC | RISAF14 | 152 | |||||
| CACHEAXI configuration port | RISAF15 | AHB | 153 | 2 | 4 bytes | 4 Kbytes | Fixed CID0 filtering on system bus. To delegate to nonsecure set DCCID = 0. |
| AHB RAM1 | RISAF21 | 154 | 7 | 512 bytes | 16 Kbytes | ||
| AHB RAM2 | RISAF22 | 155 | |||||
| Backup RAM | RISAF23 | 156 | 3 | 4 Kbytes | |||
RISAF4/5/6 are used to partition the 2-Mbyte NPU RAM. This memory is implemented as four RAM cuts, each with its own AXI target port, but using an interleaved (re-mapped) addressing scheme. To retain the software normal view of memory addressing, the RISAFs protecting these RAMs are placed on the three entry ports of the NPU interconnect. The user must program an identical partitioning into each of the three RISAFs. These RISAFs are furnished with two extra regions that the secure privileged software must configure to be transparent (permissive) to all accesses either side of the NPU RAMs.
As summarized in the CID management column of Table 24 , the AHB bus does not carry CID information (it is fixed at 0). The RISAFs on the AHB bus only filter on security and privilege, in read or in write (using RDENC0 or WRENC0 bits, respectively). All accesses are effectively assumed to be owned by the CPU. When a secure privileged application delegates to the nonsecure world the access control configuration of subregions in a nonsecure base region, DCEN must be set, and DCCID and SRCID must stay at 0 for this specific base region.
As summarized in Table 24 the AXI bus carries CID information. All AHB configuration accesses to AXI RISAF registers are assumed to come from CID1. When a secure privileged application delegates to the nonsecure world the access control configuration of subregions in a nonsecure base region, DCEN must be set and DCCID must be 0x1.
For STM32N6x5xx devices the configuration port of the CACHEAXI is not functional and must not be addressed. For STM32N6x7xx devices the AHB configuration port of the CACHEAXI is protected by a small RISAF that offers two base regions. These must be configured to cover the register address spaces, each side of the registers controlling cache invalidation. The cache invalidation operation can thus be reserved for use only by the secure privileged software, because the controlling registers are left in the default region 0.
7.4 RISAF functional description
7.4.1 RISAF block diagram
The following figure shows the block diagram of the RISAF associated with the IAC, and optionally, a memory controller.
Figure 6. RISAF block diagram
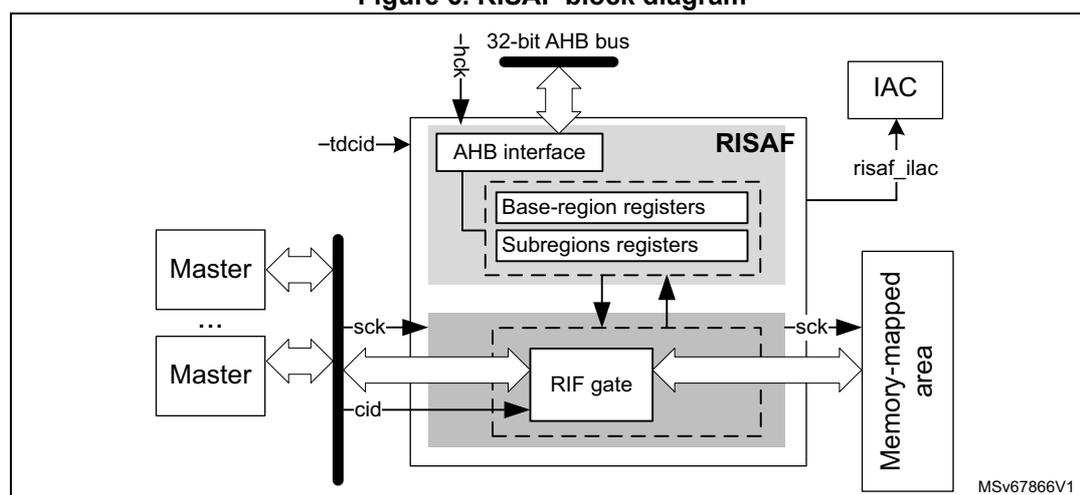
- 1. The tdcid input value is equal to CID = 1.
7.4.2 RISAF internal signals
Table 25 describes internal signals available at RISAF level, not at product level (on pins).
Table 25. RISAF internal input/output signals
| Name | Type | Description |
|---|---|---|
| risaf_sck | Digital input | System bus clock, also used by the protected memory controller |
| risaf_hclk | AHB bus clock | |
| risaf_ilac | Digital output | Illegal access signal to IAC |
7.4.3 RISAF reset and clocks
The RISAF peripheral has two clocks, one for its AHB register interface, and one for its system bus interfaces. The system bus clock is shared with the system bus memory controller target.
The RISAF peripheral has a single reset input.
Address spaces protected by the RISAF are by default secure, privileged, and CID = 1 only.
7.4.4 RISAF address space management
Through RISAF registers, a secure privileged software application, or the application to whom the configuration has been delegated, assigns memory regions to one or more security domains (secure, privilege, compartment ID). Figure 7 illustrates the principle of this allocation.
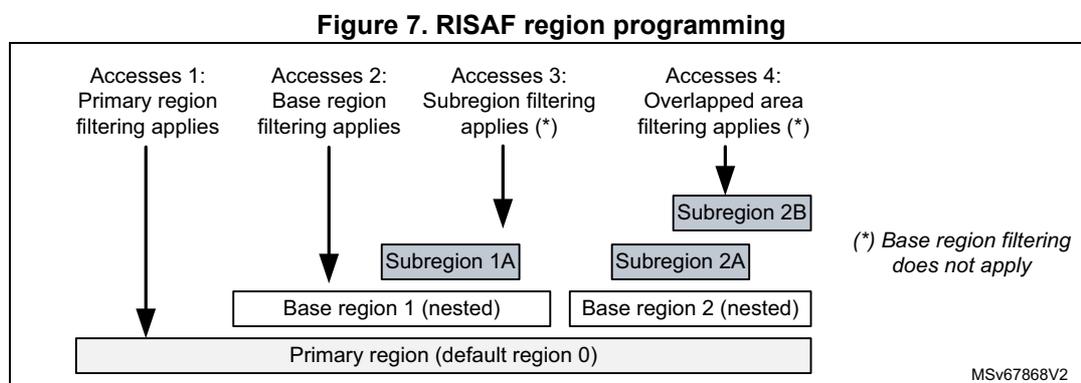
Figure 7. RISAF region programming
The diagram shows a hierarchy of memory regions. At the bottom is a wide bar labeled 'Primary region (default region 0)'. Above it are two nested bars: 'Base region 1 (nested)' on the left and 'Base region 2 (nested)' on the right. Above 'Base region 1' is 'Subregion 1A', and above 'Base region 2' is 'Subregion 2A'. Above the overlap of 'Subregion 1A' and 'Subregion 2A' is 'Subregion 2B'. Four arrows point to different areas: 'Accesses 1' points to the primary region outside all base regions; 'Accesses 2' points to 'Base region 1' outside subregions; 'Accesses 3' points to 'Subregion 1A'; 'Accesses 4' points to the overlap of 'Subregion 1A' and 'Subregion 2A'. A note on the right states '(*) Base region filtering does not apply'.
MSv67868V2
As shown in Figure 7 , there are multiple types of access filtered by RISAF:
- • Accesses 1 - Default region: access to an area not belonging to any enabled base region. Filtering for such access is fixed to secure, privileged and CID = 1 only.
- • Accesses 2 - Application region > 0: access to an area in an enabled base region, not belonging to any enabled subregion. Filtering for such access is defined in the base region, where one or more compartments can be granted specific accesses.
- • Accesses 3 - Non overlapped subregion: access to an area in an enabled nested subregion. Filtering for such access is defined in the subregion, with only one compartment that can be granted access.
- • Accesses 4 - Overlapped subregion: accesses to an area overlapping two enabled nested subregions. In this case, filtering rules for these subregions are used by the RISAF as follows:
- – If both subregions are secure (resp. nonsecure), the overlap is secure (resp. nonsecure).
- – If a subregion is nonsecure (resp. unprivileged), the overlap is nonsecure (resp. unprivileged).
- – If a subregion grants access to a compartment, the access can go through. Up to two compartments can be granted access to an overlapped subregion.
Note: When a base or subregion is disabled, the associated filtering is disabled as well. For access types 3 or 4 (detailed above), base region filtering rules do not apply. When two enabled regions overlap, if one region grants access, the access goes through.
7.4.5 RISAF programming
Only the secure privileged software can set up the access configuration to base region x through RISAF_REGx_CFGR, RISAF_REGx_CIDCFGR, RISAF_REGx_STARTR, and RISAF_REGx_ENDR.
The secure privileged software, or the application to which the subregion z configuration has been delegated in RISAF_REGx_zNESTR, can set up the access configuration to subregion z of base region x through RISAF_REGx_zCFG, RISAF_REGx_zSTARTR, and RISAF_REGx_zENDR (z = A or B).
As shown in Table 26 , subregion right options depend upon the base region privileged and security rights.
Table 26. RISAF subregion security setup matrix
| Base region rights | Nested subregion rights | |||
|---|---|---|---|---|
| Secure, privileged | Secure, unprivileged | Nonsecure, privileged | Nonsecure, unprivileged | |
| Secure, privileged | OK (1) | OK | OK | OK |
| Secure, unprivileged | Not allowed | OK (1) | Not allowed | OK |
| Nonsecure, privileged | Not allowed | Not allowed | OK (1) | OK |
| Nonsecure, unprivileged | Not allowed | Not allowed | Not allowed | OK (1) |
1. Default configuration
Configuring base regions in RISAF
The number of regions, the region watermark granularity, and the address space size depend upon the RISAF instance (see Section 7.3 ).
If the secure privileged software must use a base region x (for example at boot time), the following steps are recommended.
- The secure privileged software sets start and end addresses for each of the required base region x, using RISAF_REGx_STARTR and RISAF_REGx_ENDR:
- These registers are initialized with 32-bit physical addresses when the protected address space size is 4 Gbytes. For different sizes, refer to the register description.
- Base regions must be defined within their primary region. The hardware enforces this rule if the application does not follow it.
- For each of the above region x, the secure privileged software programs RISAF_REGx_CIDCFGR, granting read and/or write access to any compartment.
- For each of the above region x, the secure privileged software finalizes the programming by configuring RISAF_REGx_CFGR, setting up security parameters.
- After a final check on the above configuration, the secure privileged software enables each required base region x, setting the BREN bit in RISAF_REGx_CFGR.
At any time the secure privileged software can lock the RISAF configuration until the next reset, by setting the GLOCK bit in RISAF_CR. Subregion registers are the exception to this rule, as explained in Configuring subregions in RISAF .
Configuring subregions in RISAF
Note: The number of subregions, the subregion watermark granularity, and the primary region address space size depend on the RISAF resource described in Section 7.3 .
Important notes on access control programming and delegation are in Section 7.3 .
When an application needs to use the subregion z defined in the base region x, there are two configuration options in RISAF_REGx_zNESTR:
- • The secure privileged software programs the RIF configuration for this subregion. In this case DCEN is cleared.
- • The secure privileged software delegates the RIF configuration to a single CID, defined with DCCID. In this case DCEN must also be set.
Configuring a subregion z consists in the following steps.
- 1. Define the start and end address of the subregion using RISAF_REGx_zSTARTR and RISAF_REGx_zENDR registers.
- – When programming subregion watermarks, use similar rules as for base regions (see Configuring base regions in RISAF ).
- – Subregions must be defined within their base region. The RISAF enforces this rule if the application does not follow it.
- 2. Modify WREN and RDEN in RISAF_REGx_zCFGR to modify the access right of allowed compartment (defined with SCID bits).
- 3. In the same registers, modify the security and privileged access rights for the allowed compartment, if needed (see Table 26 for applicable restrictions).
- 4. After a final check on the above configuration, the subregion must be enabled by setting SREN bit in RISAF_REGx_zCFGR.
After a secure privileged software has locked all base regions (using GLOCK bit), subregion owners can lock their configuration using the RLOCK bit in RISAF_REGx_zCFGR.
Note: Only a secure application can change SEC in RISAF_REGx_zCFGR. If the base region is secure, only a secure application can configure subregion registers.
7.4.6 RISAF runtime modification of region or subregion configuration
The RISAF supports the on-the-fly update of the base region and subregion programming, except for the start- and end-address boundaries:
- • To change RISAF_REGx_STARTR and RISAF_REGx_ENDR, the base region must be disabled (BREN = 0). In this case, the default primary region access rules apply immediately (secure, privileged, CID = 1 only).
- • To change RISAF_REGx_zSTARTR and RISAF_REGx_zENDR (z = A or B), the subregion must be disabled (SREN = 0). In this case, the base region access rules apply immediately.
If the first solution introduces too many constraints, a workaround is shown in Figure 8 .
Figure 8. RISAF region on-the-fly resizing
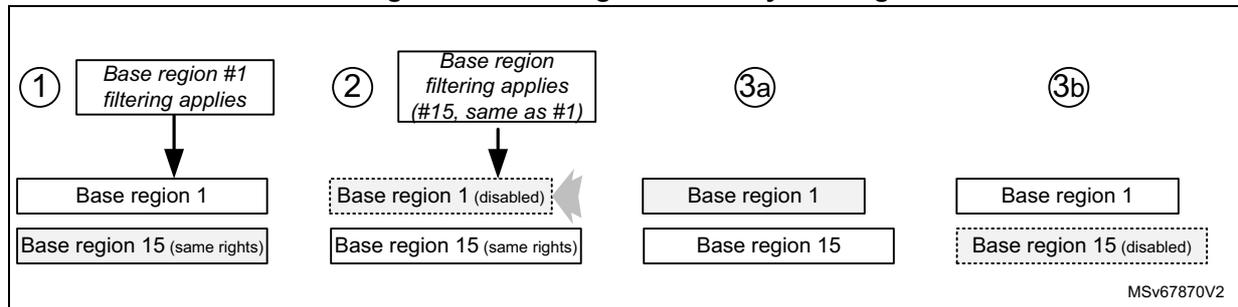
Diagram illustrating the on-the-fly resizing of base region 1 in the RISAF. The diagram is divided into four numbered sections: 1, 2, 3a, and 3b. Section 1 shows 'Base region #1 filtering applies' pointing to 'Base region 1' and 'Base region 15 (same rights)'. Section 2 shows 'Base region filtering applies (#15, same as #1)' pointing to 'Base region 1 (disabled)' and 'Base region 15 (same rights)'. Section 3a shows 'Base region 1' and 'Base region 15'. Section 3b shows 'Base region 1' and 'Base region 15 (disabled)'. A dashed arrow points from section 2 to section 3b. The text 'MSV67870V2' is in the bottom right corner.
The recommended on-the-fly resizing of base region 1 becomes:
- 1. Define a spare base region (for example 15), exactly as current region 1.
- 2. Disable region 1 by clearing BREN. The region 15 access control (identical to region 1) immediately applies. No effect is experienced at system level. The region 1 can be safely resized.
- 3. Enable region 1, then disable region 15. The new region 1 access control immediately applies. Optionally, subregions can be added on top.
7.4.7 Managing illegal accesses
As a RIF component, the RISAF does not use the standard interrupt lines toward NVIC or GIC concentrators. The IAC captures all RIF interrupt events, called illegal access events.
Refer to Section 8: Illegal access controller (IAC) for more information on how illegal accesses are managed.
7.5 RISAF registers
The registers are accessible through the interface of the RISAF. Only word (32-bit) accesses are supported.
7.5.1 RISAF configuration register (RISAF_CR)
Address offset: 0x000
Reset value: 0x0000 0000
Secure, privileged, trusted domain CID = 1, write access only. Any read access is allowed, writes are ignored if GLOCK is set.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | GLOCK |
| rs |
Bits 31:1 Reserved, must be kept at reset value.
Bit 0 GLOCK : Global lock
This bit locks the configuration of RISAF registers until next reset. It is cleared by default, and, once set, cannot be reset until global RISAF reset.
0: RISAF registers are writable.
1: All writes to RISAF registers are ignored, except RISAF_IACR, RISAF_REGx_zCFG, RISAF_REGx_zSTARTR, and RISAF_REGx_zENDR (z = A to B).
7.5.2 RISAF illegal access status register (RISAF_IASR)
Address offset: 0x008
Reset value: 0x0000 0000
Secure, privileged, trusted domain CID = 1, read access only.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | IAEF | CAEF |
| r | r |
Bits 31:2 Reserved, must be kept at reset value.
Bit 1 IAEF : Illegal access error flag
This bit is set when an illegal access is detected on the system bus. More details on the error can be found in RISAF_IAESR and RISAF_IADDR.
This bit is cleared by setting corresponding bit in RISAF_IACR.
Bit 0 CAEF : Configuration access error flag
This bit is set when an illegal access to any RISAF configuration register is detected. It is cleared by setting the corresponding bit in RISAF_IACR.
7.5.3 RISAF illegal access clear register (RISAF_IACR)
Address offset: 0x00C
Reset value: 0x0000 0000
Secure, privileged, trusted domain CID = 1, write access only.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | IAEF | CAEF |
| w | w |
Bits 31:2 Reserved, must be kept at reset value.
Bit 1 IAEF : Illegal access error flag
Set this bit to clear IAEF in RISAF_IASR, allowing the capture of a new error information from RIF in RISAF_IAESR and RISAF_IADDR registers.
Note: Clearing this bit does not clear RISAF_IADDR.
Bit 0 CAEF : Configuration access error flag
Set this bit to clear CAEF in RISAF_IASR.
7.5.4 RISAF illegal access error status register (RISAF_IAESR)
Address offset: 0x020
Reset value: 0x0000 0000
Secure, privileged, trusted domain CID = 1, read access only.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | IANRW | Res. | IASEC | IAPRIV | Res. | IACID[2:0] | ||
| r | r | r | r | r | r |
Bits 31:8 Reserved, must be kept at reset value.
Bit 7 IANRW : Illegal access read/write
When IAEF = 1 in RISAF_IASR, IANRW captures the access type of the illegal access that has been detected.
0: Illegal access was a data read or an instruction fetch
1: Illegal access was a data write
Bit 6 Reserved, must be kept at reset value.
Bit 5 IASEC : Illegal access security
When IAEF = 1 in RISAF_IASR, IASEC captures the security type of the illegal access that has been detected.
0: Illegal access was nonsecure
1: Illegal access was secure
Bit 4 IAPRIV : Illegal access privileged
When IAEF = 1 in RISAF_IASR, IAPRIV captures the privilege state of the master that issued the illegal access detected.
0: Illegal access was unprivileged
1: Illegal access was privileged
Bit 3 Reserved, must be kept at reset value.
Bits 2:0 IACID[2:0] : Illegal access compartment ID
When IAEF = 1 in RISAF_IASR, IACID[2:0] captures the compartment ID of the master that issued the illegal access detected.
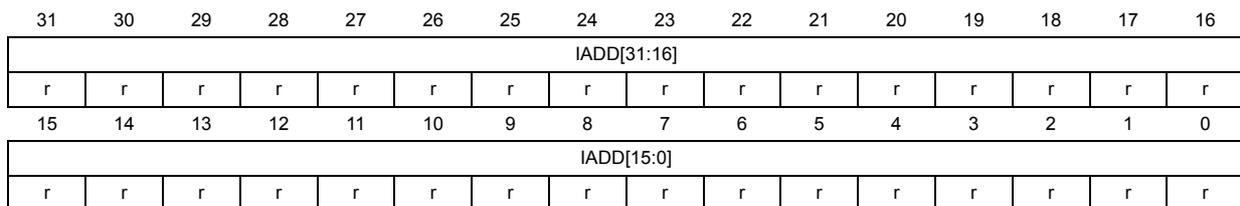
7.5.5 RISAF illegal address register (RISAF_IADDR)
Address offset: 0x024
Reset value: 0x0000 0000
Secure, privileged, trusted domain CID = 1, read access only.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| IADD[31:16] | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| IADD[15:0] | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
Bits 31:0 IADD[31:0] : Illegal address
When IAEF = 1 in RISAF_IASR, IADD[31:0] captures the address of the erroneous access. Additional information can be found in RISAF_IAESR. Captured address information is the byte offset from the base of the protected address space.
7.5.6 RISAF region x configuration register (RISAF_REGx_CFGR)
Address offset: 0x040 + 0x40 * (x - 1) (x = 1 to 15)
Reset value: 0x0000 0000
Secure, privileged, trusted domain CID = 1, write access only. Any read access is allowed on this register. Writes are ignored if GLOCK is set in RISAF_CR.
Refer to Section 7.3 to verify the number of base regions supported by this RISAF instance.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PRIV C7 | PRIV C6 | PRIV C5 | PRIV C4 | PRIV C3 | PRIV C2 | PRIV C1 | PRIV C0 |
| rw | rw | rw | rw | rw | rw | rw | rw | ||||||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | SEC | Res. | Res. | Res. | Res. | Res. | Res. | Res. | BREN |
| rw | rw |
Bits 31:24 Reserved, must be kept at reset value.
Bits 23:16 PRIVCy : Privileged access for compartment y (y = 7 to 0)
This bit is taken into account only if BREN = 1.
0: Application running in compartment y can access to region x in privileged and unprivileged mode.
1: Application running in compartment y can access to region x in privileged mode only.
Bits 15:9 Reserved, must be kept at reset value.
Bit 8 SEC : Secure region
This bit is taken into account only if BREN = 1.
0: Only nonsecure requests can access region x. SEC value in RISAF_REGx_zCFGR is internally treated as 0-ed by RISAF (only nonsecure requests to subregions).
1: Only secure requests can access region x, and optional subregions can be defined as secure or nonsecure.
Bits 7:1 Reserved, must be kept at reset value.
Bit 0 BREN : Base region enable
0: Base region x is disabled. Access control of primary region 0 (secure, privileged, trusted domain CID = 1) applies to any access between region x start and end addresses. Associated subregions are also disabled.
1: Base region x is enabled. Access controls defined in region x apply to any access between region x start and end addresses.
Note: The filtering starts from start address RISAF_REGx_STARTR (included) and ends at end address RISAF_REGx_ENDR (included).
7.5.7 RISAF region x start-address register (RISAF_REGx_STARTR)
Address offset: \( 0x044 + 0x40 * (x - 1) \) (x = 1 to 15)
Reset value: 0x0000 0000
Secure, privileged, trusted domain CID = 1, write access only. Any read access is allowed on this register. Writes are ignored if GLOCK is set in RISAF_CR, or if BREN is set in RISAF_REGx_CFGR.
Refer to Section 7.3 to verify the number of base regions supported by this RISAF instance, and for details on protected address space size and watermark granularity.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| BADDSTART[31:16] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| BADDSTART[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 BADDSTART[31:0] : Base region address start
This bitfield defines the byte-address offset (relative to the base address of the protected address space) of the lowest byte-address in base region x.
Address bits less than the granularity and greater than the protected address space size cannot be written to, and remain 0.
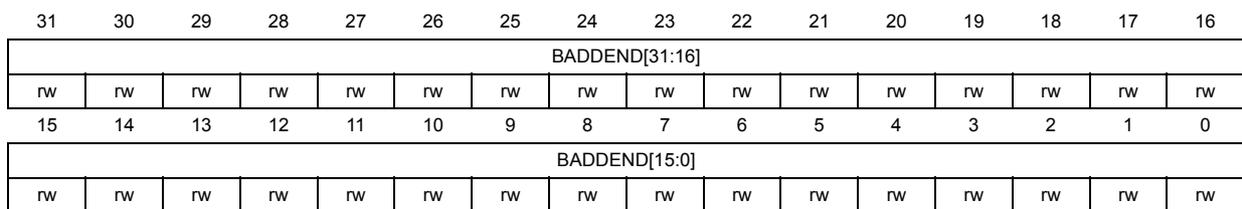
7.5.8 RISAF region x end-address register (RISAF_REGx_ENDR)
Address offset: \( 0x048 + 0x40 * (x - 1) \) ( \( x = 1 \) to 15)
Reset value: 0x0000 0FFF
The reset value given here applies when the granularity is 4 Kbytes. If the granularity is \( 2^n \) , the reset value is \( 2^n - 1 \) .
Secure, privileged, trusted domain CID = 1, write access only. Any read access is allowed on this register. Writes are ignored if GLOCK is set in RISAF_CR, or if BREN is set in RISAF_REGx_CFGR.
Refer to Section 7.3 to verify the number of base regions supported by this RISAF instance, and for details on protected address space size and watermark granularity.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| BADDEND[31:16] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| BADDEND[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 BADDEND[31:0] : Base region address end
This bitfield defines the byte-address offset (relative to the base address of the protected address space) of the highest byte-address in base region x.
Address bits less than the granularity cannot be modified, and remain 1.
Address bits greater than the protected address space size cannot be written, and remain 0.
7.5.9 RISAF region x CID configuration register (RISAF_REGx_CIDCFGR)
Address offset: \( 0x04C + 0x40 * (x - 1) \) ( \( x = 1 \) to 15)
Reset value: 0x0000 0000
Secure, privileged, trusted domain CID = 1, write access only. Any read access is allowed on this register. Writes are ignored if GLOCK is set in RISAF_CR.
Refer to Section 7.3 to verify the number of base regions supported by this RISAF instance.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WREN C7 | WREN C6 | WREN C5 | WREN C4 | WREN C3 | WREN C2 | WREN C1 | WREN C0 |
| rw | rw | rw | rw | rw | rw | rw | rw | ||||||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | RDEN C7 | RDEN C6 | RDEN C5 | RDEN C4 | RDEN C3 | RDEN C2 | RDEN C1 | RDEN C0 |
| rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:24 Reserved, must be kept at reset value.
Bits 23:16 WRENCy : Write enable for compartment y (y = 7 to 0)
This bit is taken into account only if BREN = 1 in RISAF_REGx_CFGR.
0: Application running in compartment y cannot write to region x (write ignored).
1: Application running in compartment y can write to region x. Additional control defined by SEC and PRIVCy in RISAF_REGx_CFGR, also applies.
Bits 15:8 Reserved, must be kept at reset value.
Bits 7:0 RDENCY : Read enable for compartment y (y = 7 to 0)
This bit is taken into account only if BREN = 1 in RISAF_REGx_CFGR.
0: Application running in compartment y cannot read region x (read as 0).
1: Application running in compartment y can read region x. Additional control defined by SEC and PRIVCy in RISAF_REGx_CFGR, also applies.
7.5.10 RISAF region x subregion A configuration register (RISAF_REGx_ACFGR)
Address offset: 0x050 + 0x40 * (x - 1) (x = 1 to 15)
Reset value: 0x0000 0000
Unprivileged writes are ignored. Nonsecure writes are ignored if SEC = 1 in RISAF_REGx_CFGR, or if DCEN = 0 in RISAF_REGx_ANESTR. Any read access is allowed to this register. Writes are ignored if RLOCK = 1 in this register.
When the delegated configuration is enabled (DCEN = 1 in RISAF_REGx_ANESTR), only the compartment DCCID defined in RISAF_REGx_ANESTR can write to this register.
When the delegation is disabled (DCEN = 0), only the secure privileged software can program this register.
Refer to Section 7.3 to verify the number of base regions and subregions supported by this RISAF instance.
Caution: Check Section 7.3 before programming SRCID[2:0] bitfield.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | WREN | RDEN | Res. | Res. | PRIV | SEC | Res. | SRCID [2] | SRCID [1] | SRCID [0] | Res. | Res. | RLOCK | SREN |
| rw | rw | rw | rw | rw | rw | rw | rs | rw |
Bits 31:14 Reserved, must be kept at reset value.
Bit 13 WREN : Write enableThis bit is taken into account only if SREN = 1 in this register.
0: Any write to subregion A of region x is ignored
1: Subregion A of region x can be written
Bit 12 RDEN : Read enableThis bit is taken into account only if SREN = 1 in this register.
0: Any read to subregion A of region x returns 0
1: Subregion A of region x can be read
Bits 11:10 Reserved, must be kept at reset value.
Bit 9 PRIV : Privileged subregionThis bit is taken into account only if SREN = 1 in this register.
0: Privileged and unprivileged accesses are granted in subregion A of region x
1: Only privileged accesses are granted in subregion A of region x
Note: When base region x is defined as unprivileged for the SCID compartment (PRIVCy = 0 in RISAF_REGx_CFGR, with SRCID = Cy), unprivileged accesses to subregion A are always granted.
Bit 8 SEC : Secure subregionThis bit is taken into account only if SREN = 1 in this register. Nonsecure modification to it are discarded.
0: Only nonsecure requests can access subregion A of region x
1: Only secure requests can access subregion A of region x
Note: When base region x is defined as nonsecure (SEC = 0 in RISAF_REGx_CFGR), only nonsecure accesses to subregion A are granted.
Bit 7 Reserved, must be kept at reset value.
Bits 6:4 SRCID[2:0] : Subregion CIDWhen SREN = 1 in this register, SRCID[2:0] defines which compartment has access to subregion A of RISAF region x.
Bits 3:2 Reserved, must be kept at reset value.
Bit 1 RLOCK : Resource lockWhen this bit is set, the subregion resource is locked.
0: RISAF_REGx_ACFGR, RISAF_REGx_ASTARTR, and RISAF_REGx_AENDR are writable
1: Writes to RISAF_REGx_ACFGR, RISAF_REGx_ASTARTR, and RISAF_REGx_AENDR are ignored
Note: This bit is set once, cleared only by RISAF reset. It cannot be set if GLOCK = 0 in RISAF_CR.
Bit 0 SREN : Subregion enable0: Subregion A is disabled. Access control of base region x applies to any access between this subregion start and end addresses.
1: Subregion A of region x is enabled. Access control defined in subregion A applies to any access between subregion A start and end addresses.
Note: The filtering starts from address RISAF_REGx_ASTARTR (included), and ends at address RISAF_REGx_AENDR (included).
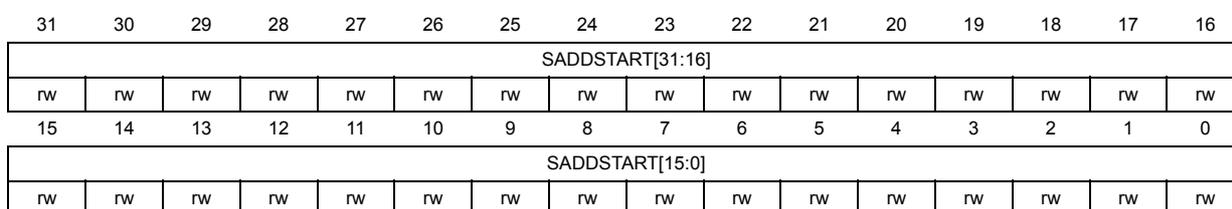
7.5.11 RISAF region x subregion A start-address register (RISAF_REGx_ASTARTR)
Address offset: \( 0x054 + 0x40 \times (x - 1) \) ( \( x = 1 \) to \( 15 \) )
Reset value: 0x0000 0000
Unprivileged writes are ignored. Nonsecure writes are ignored if SEC = 1 in RISAF_REGx_CFGR, or if DCEN = 0 in RISAF_REGx_ANESTR. Any read access is allowed to this register. Writes are ignored if RLOCK = 1 or SREN = 1 in RISAF_REGx_ACFGR.
When the delegated configuration is enabled (DCEN = 1 in RISAF_REGx_ANESTR), only the compartment DCCID defined in RISAF_REGx_ANESTR can write to this register. When the delegation is disabled (DCEN = 0), only the secure privileged software can program this register.
Refer to Section 7.3 to verify the number of base regions and subregions supported by this RISAF instance, and for details on protected address space size and watermark granularity.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| SADDSTART[31:16] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| SADDSTART[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 SADDSTART[31:0] : Subregion address start
This bitfield defines the byte-address offset (relative to the base address of the protected address space) of the lowest byte-address in subregion A in base region x.
Address bits less than the granularity and greater than the protected address space size cannot be written, and remain 0.
The effective subregion is the intersection of the subregion and its base region (there is no point in programming SADDSTART below the associated BADDSTART).
7.5.12 RISAF region x subregion A end-address register (RISAF_REGx_AENDR)
Address offset: \( 0x058 + 0x40 \times (x - 1) \) ( \( x = 1 \) to \( 15 \) )
Reset value: 0x0000 0FFF
This reset value applies when the granularity is 4 Kbytes. More in general, if the granularity is \( 2^n \) , the reset value is \( 2^n - 1 \) .
Unprivileged writes are ignored. Nonsecure writes are ignored if SEC = 1 in RISAF_REGx_CFGR, or if DCEN = 0 in RISAF_REGx_ANESTR. Any read access is allowed to this register. Writes are ignored if RLOCK = 1 or SREN = 1 in RISAF_REGx_ACFGR.
When the delegated configuration is enabled (DCEN = 1 in RISAF_REGx_ANESTR), only the compartment DCCID defined in RISAF_REGx_ANESTR can write to this register. When the delegation is disabled (DCEN = 0), only the secure privileged software can program this register.
Refer to Section 7.3 to verify the number of base regions and subregions supported by this RISAF instance, and for details on protected address space size and watermark granularity.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| SADDEND[31:16] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| SADDEND[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 SADDEND[31:0] : Subregion address end
This bitfield defines the byte-address offset (relative to the base address of the protected address space) of the highest byte-address of subregion A in base region x.
Address bits less than the granularity cannot be modified, and remain 1.
Address bits greater than the protected address space size cannot be written, and remain 0.
The effective subregion is the intersection of the subregion and its base region (there is no point in programming SADDEND higher than the associated BADDEND).
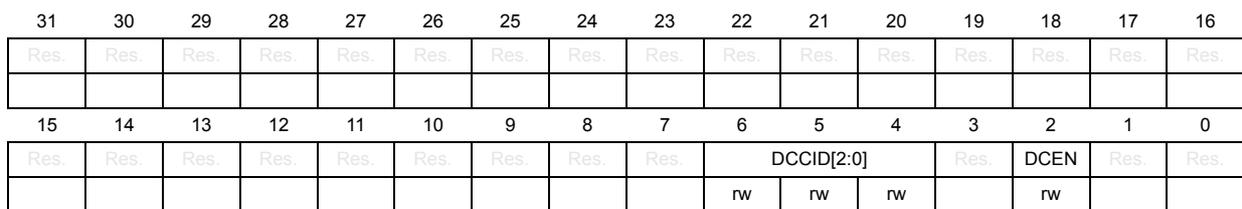
7.5.13 RISAF region x subregion A nested mode register (RISAF_REGx_ANESTR)
Address offset: \( 0x05C + 0x40 \times (x - 1) \) ( \( x = 1 \) to 15)
Reset value: 0x0000 0000
Secure, privileged, trusted domain CID = 1, write access only. Any read access is allowed on this register. Writes are ignored if GLOCK is set in RISAF_CR.
Refer to Section 7.3 to verify the number of base regions and subregions supported by this RISAF instance.
Caution: Check Section 7.3 before setting DCEN bit.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | DCCID[2:0] | Res. | DCEN | Res. | Res. | ||
| rw | rw | rw | rw | ||||||||||||
Bits 31:7 Reserved, must be kept at reset value.
Bits 6:4 DCCID[2:0] : Delegated configuration CID
The secure privileged software can use this bitfield to statically define which compartment can program the RIF configuration of subregion A if DCEN = 1 in this register.
Bit 3 Reserved, must be kept at reset value.
Bit 2 DCEN : Delegated configuration enable
0: RIF configuration for subregion A can be written only by the secure privileged software.
1: RIF configuration for subregion A can be written only by compartment DCCID, defined in this register. If base region x is defined as secure (SEC = 1), nonsecure write accesses to this subregion RIF configuration by compartment DCCID are ignored.
Note: RIF configuration of subregion A is defined as RISAF_REGx_ACFGR, RISAF_REGx_ASTARTR, and RISAF_REGx_AENDR.
Bits 1:0 Reserved, must be kept at reset value.
7.5.14 RISAF region x subregion B configuration register (RISAF_REGx_BCFGR)
Address offset: 0x060 + 0x40 * (x - 1) (x = 1 to 15)
Reset value: 0x0000 0000
Unprivileged writes are ignored. Nonsecure writes are ignored if SEC = 1 in RISAF_REGx_CFGR, or if DCEN = 0 in RISAF_REGx_BNESTR. Any read access is allowed to this register. Writes are ignored if RLOCK = 1 or SREN = 1 in RISAF_REGx_BCFGR.
When the delegated configuration is enabled (DCEN = 1 in RISAF_REGx_BNESTR), only the compartment DCCID defined in RISAF_REGx_BNESTR can write to this register. When the delegation is disabled (DCEN = 0), only the secure privileged software can program this register.
Refer to Section 7.3 to verify the number of base regions and subregions supported by this RISAF instance.
Caution: Check Section 7.3 before programming SRCID[2:0] bitfield.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | WREN | RDEN | Res. | Res. | PRIV | SEC | Res. | SRCID [2] | SRCID [1] | SRCID [0] | Res. | Res. | RLOCK | SREN |
| rw | rw | rw | rw | rw | rw | rw | rs | rw |
Bits 31:14 Reserved, must be kept at reset value.
Bit 13 WREN : Write enable
This bit is taken into account only if SREN = 1 in this register.
0: Any write to subregion B of region x is ignored
1: Subregion B of region x can be written
Bit 12 RDEN : Read enable
This bit is taken into account only if SREN = 1 in this register.
0: Any read to subregion B of region x returns 0
1: Subregion B of region x can be read
Bits 11:10 Reserved, must be kept at reset value.
Bit 9 PRIV : Privileged subregion
This bit is taken into account only if SREN = 1 in this register.
0: Privileged and unprivileged accesses are granted in subregion B of region x
1: Only privileged accesses are granted in subregion B of region x
Note: When base region x is defined as unprivileged for the SCID compartment (PRIVCy = 0 in RISAF_REGx_CFGR, with SRCID = Cy), unprivileged accesses to subregion B are always granted.
Bit 8 SEC : Secure subregion
This bit is taken into account only if SREN = 1 in this register. Nonsecure modification to it are discarded.
0: Only nonsecure requests can access subregion B of region x
1: Only secure requests can access subregion B of region x
Note: When base region x is defined as nonsecure (SEC = 0 in RISAF_REGx_CFGR), only nonsecure accesses to subregion B are granted.
Bit 7 Reserved, must be kept at reset value.
Bits 6:4 SRCID[2:0] : Subregion CID
When SREN = 1 in this register, SRCID[2:0] defines which compartment has access to subregion B of RISAF region x.
Bits 3:2 Reserved, must be kept at reset value.
Bit 1 RLOCK : Resource lock
When this bit is set, the subregion resource is locked.
0: RISAF_REGx_BCFGR, RISAF_REGx_BSTARTR, and RISAF_REGx_BENDR are writable
1: Writes to RISAF_REGx_BCFGR, RISAF_REGx_BSTARTR, and RISAF_REGx_BENDR are ignored
Note: This bit is set once, cleared only by RISAF reset. It cannot be set if GLOCK = 0 in RISAF_CR.
Bit 0 SREN : Subregion enable
0: Subregion B of region x is disabled. Access control of base region x applies to any access between this subregion start and end addresses.
1: Subregion B of region x is enabled. Access control defined in subregion B applies to any access between subregion B start and end addresses.
Note: The filtering starts from address RISAF_REGx_BSTARTR (included), and ends at address RISAF_REGx_BENDR (included).
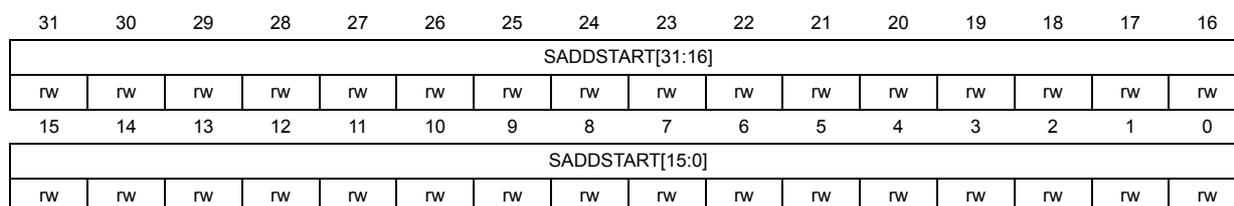
7.5.15 RISAF region x subregion B start-address register (RISAF_REGx_BSTARTR)
Address offset: \( 0x064 + 0x40 \times (x - 1) \) ( \( x = 1 \) to 15)
Reset value: 0x0000 0000
Unprivileged writes are ignored. Nonsecure writes are ignored if SEC = 1 in RISAF_REGx_CFGR, or if DCEN = 0 in RISAF_REGx_BNESTR. Any read access is allowed to this register. Writes are ignored if RLOCK = 1 or SREN = 1 in RISAF_REGx_BCFGR.
When the delegated configuration is enabled (DCEN = 1 in RISAF_REGx_BNESTR), only the compartment DCCID defined in RISAF_REGx_BNESTR can write to this register. When the delegation is disabled (DCEN = 0), only the secure privileged software can program this register.
Refer to Section 7.3 to verify the number of base regions and subregions supported by this RISAF instance, and for details on protected address space size and watermark granularity.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| SADDSTART[31:16] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| SADDSTART[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 SADDSTART[31:0] : Subregion address start
- This bitfield defines the byte-address offset (relative to the base address of the protected address space) of the lowest byte-address in subregion B in base region x.
- Address bits less than the granularity and greater than the protected address space size cannot be written, and remain 0.
- The effective subregion is the intersection of the subregion and its base region (there is no point in programming SADDSTART below the associated BADDSTART).
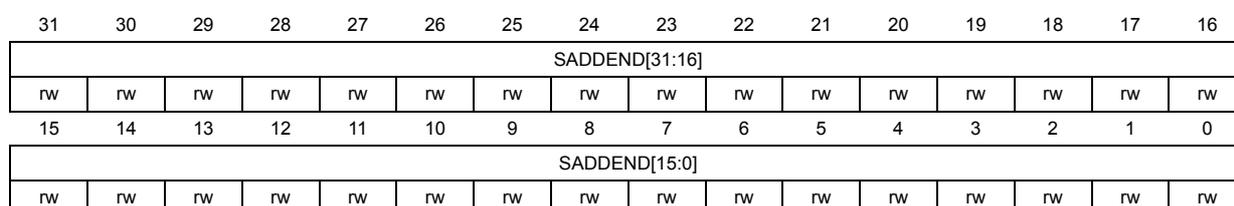
7.5.16 RISAF region x subregion B end-address register (RISAF_REGx_BENDR)
Address offset:
\(
0x068 + 0x40 \times (x - 1)
\)
(
\(
x = 1
\)
to 15)
Reset value: 0x0000 0FFF
This reset value applies when the granularity is 4 Kbytes. More in general, if the granularity is \( 2^n \) , the reset value is \( 2^n - 1 \) .
Unprivileged writes are ignored. Nonsecure writes are ignored if SEC = 1 in RISAF_REGx_CFGR, or if DCEN = 0 in RISAF_REGx_BNESTR. Any read access is allowed to this register. Writes are ignored if RLOCK = 1 or SREN = 1 in RISAF_REGx_BCFGR.
When the delegated configuration is enabled (DCEN = 1 in RISAF_REGx_BNESTR), only the compartment DCCID defined in RISAF_REGx_BNESTR can write to this register. When the delegation is disabled (DCEN = 0), only the secure privileged software can program this register.
Refer to Section 7.3 to verify the number of base regions and subregions supported by this RISAF instance, and for details on protected address space size and watermark granularity.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| SADDEND[31:16] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| SADDEND[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 SADDEND[31:0] : Subregion address end
This bitfield defines the byte-address offset (relative to the base address of the protected address space) of the highest byte-address of subregion B in base region x.
Address bits less than the granularity cannot be modified, and remain 1.
Address bits greater than the protected address space size cannot be written, and remain 0.
The effective subregion is the intersection of the subregion and its base region (there is no point in programming SADDEND higher than the associated BADDEND).
7.5.17 RISAF region x subregion B nested mode register (RISAF_REGx_BNESTR)
Address offset: \( 0x06C + 0x40 * (x - 1) \) ( \( x = 1 \) to 15)
Reset value: 0x0000 0000
Secure, privileged, trusted domain CID = 1, write access only. Any read access is allowed on this register. Writes are ignored if GLOCK is set in RISAF_CR.
Refer to Section 7.3 to verify the number of base regions and subregions supported by this RISAF instance.
Caution: Check Section 7.3 before setting DCEN bit.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | DCCID[2:0] | Res. | DCEN | Res. | Res. | ||
| rw | rw | rw | rw | ||||||||||||
Bits 31:7 Reserved, must be kept at reset value.
Bits 6:4 DCCID[2:0] : Delegated configuration CID
The secure privileged software can use this bitfield to statically define which compartment can program the RIF configuration of subregion B if DCEN = 1 in this register.
Bit 3 Reserved, must be kept at reset value.
Bit 2 DCEN : Delegated configuration enable
0: RIF configuration for subregion B can be written only by the secure privileged software.
1: RIF configuration for subregion B can be written only by compartment DCCID, defined in this register. If base region x is defined as secure (SEC = 1), nonsecure write accesses to this subregion RIF configuration by compartment DCCID are ignored.
Note: RIF configuration of subregion B is defined as RISAF_REGx_BCFGR, RISAF_REGx_BSTARTR, and RISAF_REGx_BENDR.
Bits 1:0 Reserved, must be kept at reset value.
7.5.18 RISAF register map
Table 27. RISAF register map and reset values
| Offset | Register name | 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 | 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0x000 | RISAF_CR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | GLOCK |
| Reset value | 0 | ||||||||||||||||||||||||||||||||
| 0x004 | Reserved | Reserved | |||||||||||||||||||||||||||||||
| 0x008 | RISAF_IASR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | IAEF | CAEF |
| Reset value | 0 | 0 | |||||||||||||||||||||||||||||||
| 0x00C | RISAF_IACR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | AEF | CAEF |
| Reset value | 0 | 0 | |||||||||||||||||||||||||||||||
| 0x010-0x01C | Reserved | Reserved | |||||||||||||||||||||||||||||||
| 0x020 | RISAF_IAESR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | IANRW | Res. | IASEC | IAPRIV | Res. | IACID [2:0] | ||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||||||||||||||||||
| 0x024 | RISAF_IADDR | IADD[31:0] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x028-0x03C | Reserved | Reserved | |||||||||||||||||||||||||||||||
| 0x040 + 0x040*(x-1) (x=1 to 15) Last address: 0x3C0 | RISAF_REGx_CFGR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PRIVC7 | PRIVC6 | PRIVC5 | PRIVC4 | PRIVC3 | PRIVC2 | PRIVC1 | PRIVC0 | Res. | Res. | Res. | Res. | Res. | Res. | Res. | SEC | Res. | Res. | Res. | Res. | Res. | Res. | Res. | BREN |
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||||||||||||||
| 0x044 + 0x040*(x-1) (x=1 to 15) Last address: 0x3C4 | RISAF_REGx_STARTR | BADDSTART[31:0] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x048 + 0x040*(x-1) (x=1 to 15) Last address: 0x3C8 | RISAF_REGx_ENDR | BADDEND[31:0] | |||||||||||||||||||||||||||||||
| Reset value (1) | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | |
| 0x04C + 0x040*(x-1) (x=1 to 15) Last address: 0x3CC | RISAF_REGx_CIDCFGR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WRENC7 | WRENC6 | WRENC5 | WRENC4 | WRENC3 | WRENC2 | WRENC1 | WRENC0 | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | RDENC7 | RDENC6 | RDENC5 | RDENC4 | RDENC3 | RDENC2 | RDENC1 | RDENC0 |
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||||||||
| 0x050 + 0x040*(x-1) (x=1 to 15) Last address: 0x3D0 | RISAF_REGx_ACFGR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WREN | RDEN | Res. | Res. | PRIV | SEC | Res. | SRCID [2:0] | Res. | Res. | RLOCK | SREN | ||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||||||||||||||||||||||||
| 0x054 + 0x040*(x-1) (x=1 to 15) Last address: 0x3D4 | RISAF_REGx_ASTARTR | SADDSTART[31:0] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
Table 27. RISAF register map and reset values (continued)
| Offset | Register name | 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 | 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0x058 + 0x40*(x-1) (x=1 to 15) Last address: 0x3D8 | RISAF_REGx_AENDR | SADDEND[31:0] | |||||||||||||||||||||||||||||||
| Reset value (1) | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | |
| 0x05C + 0x40*(x-1) (x=1 to 15) Last address: 0x3DC | RISAF_REGx_ANESTR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | DCCID [2:0] | Res. | Res. | DCEN | Res. | Res. | Res. |
| Reset value | 0 | 0 | 0 | 0 | |||||||||||||||||||||||||||||
| 0x060 + 0x40*(x-1) (x=1 to 15) Last address: 0x3E0 | RISAF_REGx_BCFGR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WREN | RDEN | Res. | Res. | PRIV | SEC | Res. | SRCID [2:0] | Res. | Res. | Res. | RLOCK | SREN | |
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||||||||||||||||||||||||
| 0x064 + 0x40*(x-1) (x=1 to 15) Last address: 0x3E4 | RISAF_REGx_BSTARTR | SADDSTART[31:0] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x068 + 0x40*(x-1) (x=1 to 15) Last address: 0x3E8 | RISAF_REGx_BENDR | SADDEND[31:0] | |||||||||||||||||||||||||||||||
| Reset value (1) | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | X | |
| 0x06C + 0x40*(x-1) (x=1 to 15) Last address: 0x3EC | RISAF_REGx_BNESTR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | DCCID [2:0] | Res. | Res. | DCEN | Res. | Res. | Res. |
| Reset value | 0 | 0 | 0 | 0 | |||||||||||||||||||||||||||||
1. Reset value is 0x0000 0FFF when the granularity is 4 Kbytes.
Refer to Section 2.3: Memory organization for the register boundary addresses.