39. Memory cipher engine (MCE)
39.1 MCE introduction
Memory cipher engine (MCE) defines, in a given address space, multiple regions with specific security setup (encryption, privilege, write). All system bus traffic going through an encrypted region is managed on-the-fly by the MCE, automatically decrypting reads and encrypting writes if authorized.
Multiple ciphering option (stream, block, fast block) are available to offer the best security versus performance trade-off.
Note: When MCE is used in conjunction with XSPI it is mandatory to access the flash memory using the memory map mode of the flash memory controller.
39.2 MCE main features
- • System bus in-line encryption (for writes) and decryption (for reads), based on embedded firewall programming
- – Four encryption modes per region (maximum 4 regions available): no encryption (bypass mode), stream cipher, block cipher and fast block cipher modes
- – Start and end of regions defined with 4-Kbytes granularity
- – Default filtering (region 0): any access granted
- – Region 1 to 4 access filtering criteria: privilege, write
- • Supported block ciphers: AES or Noekeon (12 round version)
- • Supported chaining modes: block and stream
- – Block mode with AES cipher is compatible with ECB mode specified in NIST FIPS publication 197 Advanced encryption standard (AES) (normal or fast).
- – Stream mode with AES cipher is compliant with CTR mode specified in NIST SP800-38A Recommendation for Block Cipher Modes of Operation .
- – Includes a leakage resilient mode of operation as defense against side channel attacks (SCA).
- • One set of write-only and lockable master key registers per block cipher (normal, fast)
- • Two sets of lockable cipher contexts (128-bit key, IV), usable for stream and block ciphers
- • Optimization for XSPI data pre-fetching mechanism (stream cipher only)
- • Read-write arbitration scheme, for better read performances
- • AHB configuration port, privileged aware
- – Accessible through 32-bit word single accesses only (otherwise an AHB bus error is generated, and write accesses are ignored)
- • AXI system bus master/slave interfaces (64-bit)
- – Support for any AXI-64bit read transactions
- – When encryption is enabled, support for AXI-64bit INCRx ( \( x = 1 \) to \( 8 \) ) and WRAPx ( \( x = 4 \) ) write transactions
39.3 MCE implementation
This manual describes the full set of features implemented in MCE peripheral. In this device MCE1, MCE2 and MCE3 instances implement the set of features defined on Table 358 .
Table 358. MCE implementation
| MCE features | MCE1 | MCE2 and MCE3 |
|---|---|---|
| Number of regions | 4 | |
| Cipher engines | AES x2 | 12 rounds Noekeon x2 |
| Derive key function | normal, fast | |
| Master key | 2 | |
| Chaining modes (encryption mode) | block, stream | block |
| Cipher context(s) | 2 | 0 |
MCE peripheral generates interrupts to the Cortex® CPU interrupt controller (mce_it).
39.4 MCE functional description
39.4.1 MCE block diagram
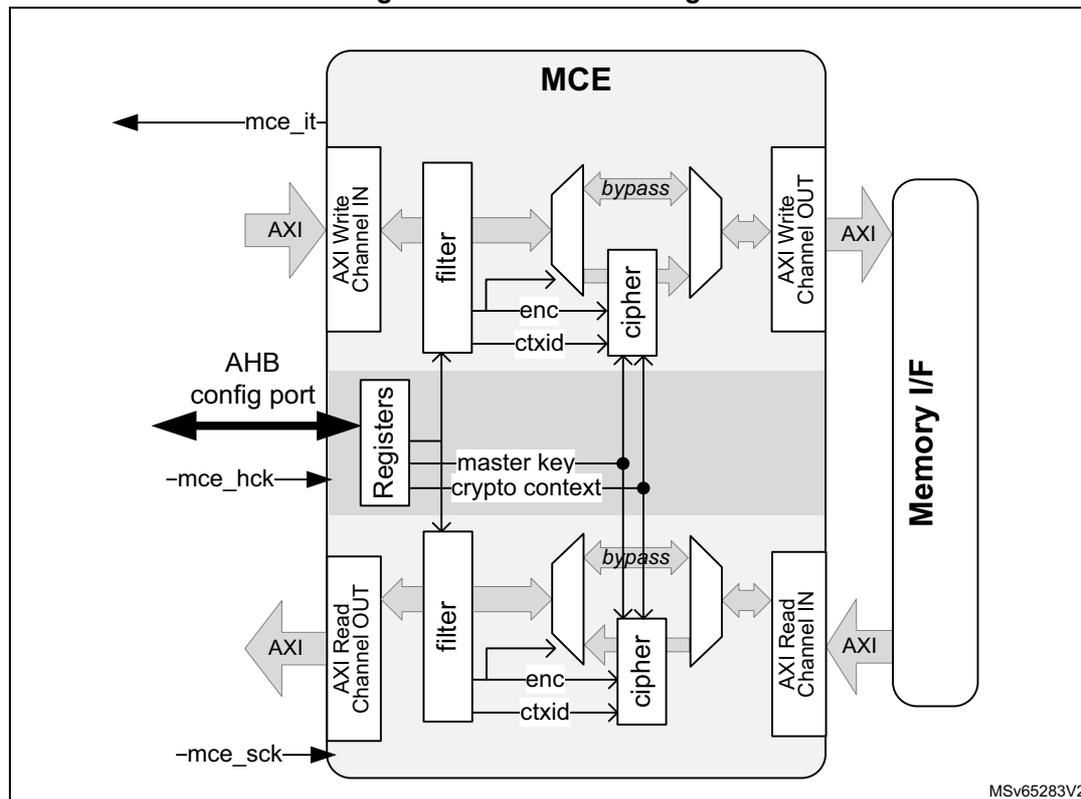
Figure 392 shows the memory cipher engine block diagram, associated with one or more memory interface peripheral.
Figure 392. MCE block diagram
39.4.2 MCE internal signals
Table 359 describes the user relevant internal signals interfacing the MCE peripheral.
Table 359. MCE internal input/output signals
| Signal name | Signal type (1) | Description |
|---|---|---|
| mce_sck | input | AXI input clock |
| mce_hck | input | AHB input clock for MCE |
| mce_it | output | MCE interrupt request |
1. All digital.
39.4.3 MCE programming
Overview
Through MCE registers application software defines security regions, as shown on Figure 393 .
Figure 393. MCE region programming
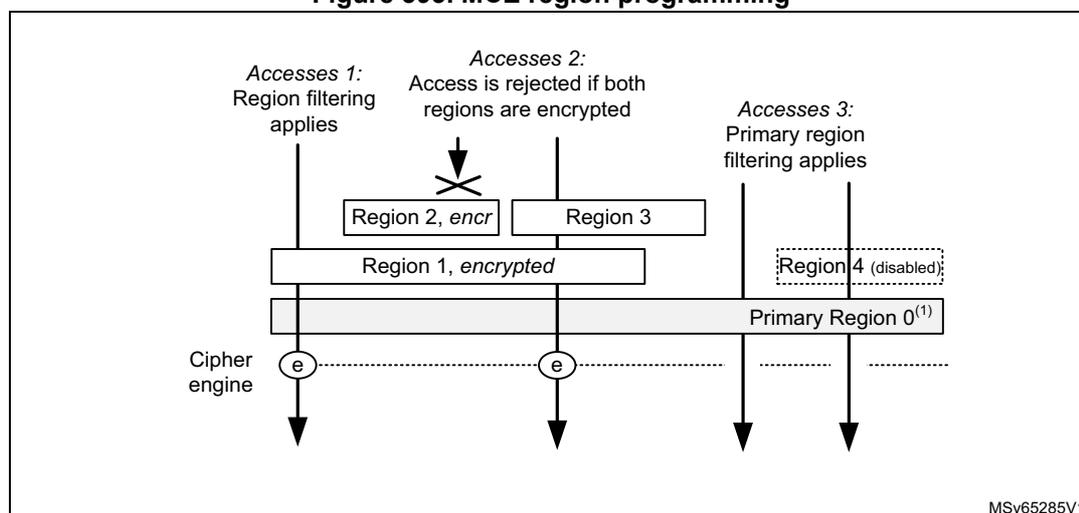
The diagram shows a memory layout with several regions. At the bottom is a wide bar labeled 'Primary Region 0 (1) '. Above it, 'Region 1, encrypted' is shown. Above Region 1, 'Region 2, encr' and 'Region 3' are shown, both overlapping with Region 1. To the right, 'Region 4 (disabled)' is shown as a dashed box. Three access scenarios are depicted with arrows pointing down to the memory:
- Accesses 1: Points to Region 1. Text: 'Region filtering applies'.
- Accesses 2: Points to the overlap of Region 2 and Region 3. Text: 'Access is rejected if both regions are encrypted'. An 'X' is drawn over the arrow.
- Accesses 3: Points to the area outside Regions 1, 2, 3, and 4. Text: 'Primary region filtering applies'.
- 1. Covers all addressable space.
There are three types of accesses filtered by MCE:
- 1. Access to an area located in one enabled region (accesses 1). In this cases region filtering rules applies. If encryption is enabled cipher engine is used accordingly.
- 2. Access to an area overlapping two enabled regions (access 2):
- – If one region is encrypted this region defines the write and privileged accesses, as well as the encryption.
- – If both regions are encrypted, access is automatically rejected with an error
- – If both regions are not encrypted, lowest index region defines the write and privileged accesses
Access to an area not belonging to any enabled region (accesses 3). In this case primary region 0 filtering apply (any access granted, no encryption).
Configuring regions
When application needs to use any region x following sequence can be used, for example at boot time.
- 1. Application sets a start and end address for each of the required region x, using MCE_SADDRx and MCE_EADDRx registers.
- 2. For each of the above region x application programs MCE_ATTRx, granting write access to the memory or not.
- 3. Application finalizes the programming by configuring MCE_REGCRx setting up security parameters (encryption, privilege). Initializing encryption is detailed in Section 39.4.5 and Section 39.4.5 .
- 4. After final check on above configuration application enables each required region z, setting BREN bit in MCE_REGCRz.
MCE configuration can be fixed until next SoC reset when GLOCK is set in MCE_CR register.
Above application must be privileged if PRIV bit is set in register MCE_PRIVCFGR.
Note: When ENCDIS bit is set in MCE_SR, if ENC bit and BREN bits are set in MCE_REGCRx all writes to this region x are ignored and all read requests return zero. See Section 39.4.8 for details.
Note: When an MCE instance uses at least one crypto context, to avoid issues at runtime it is recommended to verify in MCE_CCxCFGR registers that, each time CCEN = 1, KEYCRC is different from zero. After this check it is recommended to set GLOCK in MCE_CR to freeze the MCE configuration.
Runtime modification of region configuration
While it is possible to update on-the-fly the enabled region access filtering (write, privilege), changes to the following configurations are ignored when BREN bit is set in MCE_REGCRx register:
- • MCE_SADDRx and MCE_EADDRx address registers
- • ENC and CTXID bitfields in MCE_REGCx register
Note: When BREN is cleared primary region 0 access rules applies instead of base region rules (see Overview).
GLOCK bit should be used to write lock the following registers: MCE_MKEYRx, MCE_FMKEYRx, MCE_CCxCFGR, MCE_CCxNR0/1 and MCE_CCxKEYR, in order to avoid unexpected changes to the cipher keys/context while used by the MCE.
Encrypting with MCE
MCE automatically encrypts on-the-fly any granted write transaction to a region with encryption properly initialized. When stream cipher is selected it is important to activate write protection as soon as the whole region has been encrypted (read-only region).
When MCE is used in conjunction with XSPI it is mandatory to set the Flash memory controller in memory map mode. It is also required to use the DMA to perform writes to the flash memory using 16 bytes bursts.
39.4.4 MCE reset and clocks
MCE configuration port is clocked by the AHB bus clock.
MCE system bus interface is clocked by the AXI clock. AHB interface does not need to be clocked for the system bus to be usable.
When MCE is kept under reset, no traffic can go through the system bus. Out of reset default firewall configuration applies, as described in Section 39.4.3 .
The clocks of MCE peripheral and its associated memory controller are enabled together in the RCC, and the MCE peripheral is reset by a system reset or when associated memory controller is reset (see Section 7: Reset and clock control (RCC) ).
39.4.5 MCE block cipher encryption mode
Caution: When MCE is used in conjunction with XSPI it is mandatory to read or write the flash memory using the memory map mode of the flash memory controller.
Figure 394 details the block cipher implementations in the MCE peripheral. Top figure is a standard encryption (for writes), bottom figure is a fast decryption (for reads).
Figure 394. MCE implementation of block ciphers
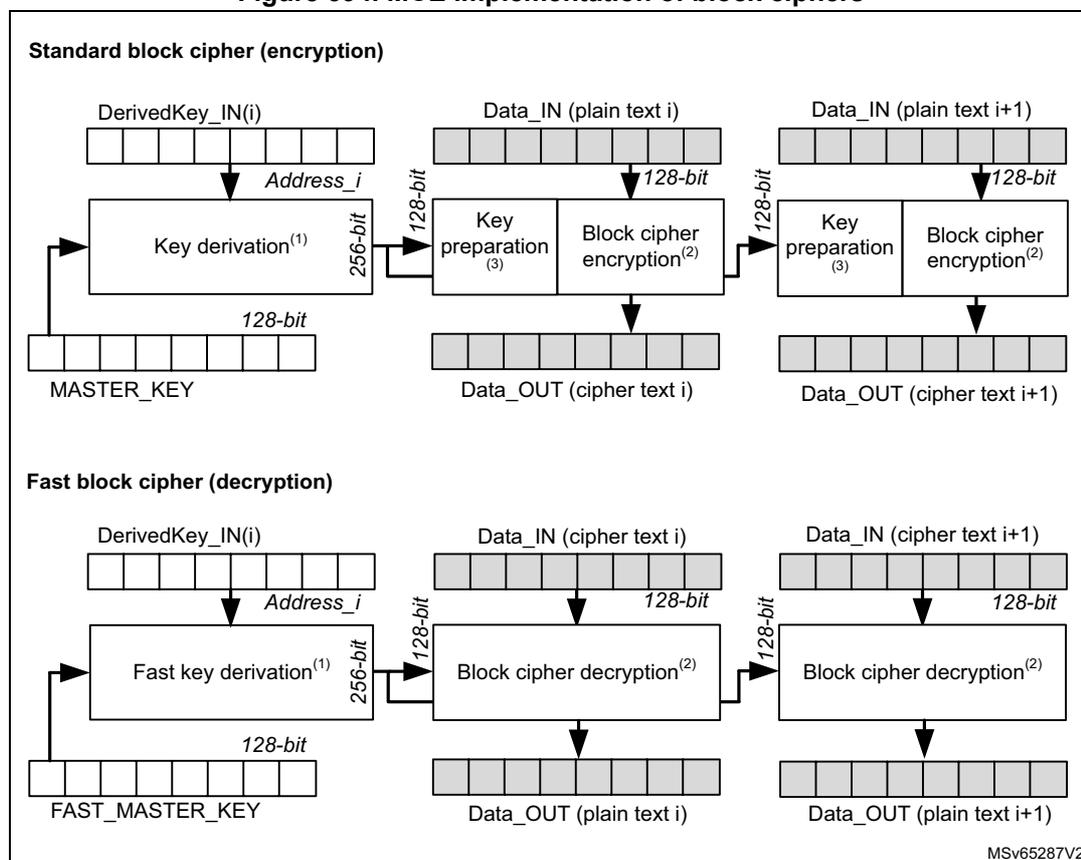
- 1. Operation starts from the capture of the address.
- 2. Operation starts from availability of data input.
- 3. Only required for AES cipher.
Address_i is most significant bits of physical address of block (i) + block (i+1). Result of key derivation primitive can be used for two consecutive 16-byte data words. Since the normal key derivation function is leakage resilient the master key information is protected against side channel attacks (SCA).
MASTER_KEY must be stored in write-only MCE_MKEYRx registers.
FAST_MASTER_KEY must be stored in write-only MCE_FMKEYRx registers. Alternatively, MCE_CCzKEYRx registers can be used if cipher context z is selected in MCE_REGCR (CTXID = z).
Each time a key material has been successfully written in MCE, the following flags are set:
- • MKVALID bit in MCE_SR is set when a complete key has been written in MCE_MKEYR registers.
- • FMKVALID bit in MCE_SR is set when a complete key has been written in MCE_FMKEYR registers.
- • KEYCRC[7:0] in MCE_CCzCFGGR is loaded with 8-bit checksum when a complete key has been written in MCE_CCzKEYR registers. See KEYCRC bitfield for details.
Bypass mode is selected instead of cipher mode if the selected key is not marked as valid with above flags. See ENC bitfield description for details.
Note:
With AES block cipher, writing (encryption) requires extra cycles in order to perform the required key scheduling to obtain the encryption key. See next table for details.
Fast key derivation function may be sensitive against side channel attacks. Hence master key used in normal mode is never used in fast mode.
Relative performances are described on Table 360 . Refer to Section 39.3: MCE implementation to identify which cipher is used for which MCE instance.
Table 360. MCE block cipher latencies
| Cipher type | Block mode | ENC bit in MCE_REGCRx | Latency in AXI cycles | Optimization for sequential accesses | |
|---|---|---|---|---|---|
| for 16 bytes data | for 32 bytes data | ||||
| AES (1) | Normal (2) | 10 | 14+11= 25 | 14+11x2= 36 | no |
| Fast | 11 | 4+11= 15 | 4+11x2= 26 | ||
| Noekeon | Normal | 10 | 14+7= 21 | 14+7x2= 28 | no |
| Fast | 11 | 4+7= 11 | 4+7x2= 18 | ||
1. Additional 10 cycles are required when performing encryption/ writes
2. Leakage resilient mode of operation as defense against side channel attacks.
39.4.6 MCE stream cipher encryption mode
Figure 395 details the stream cipher implementations in the MCE peripheral. It pictures encryptions for AXI writes.
Figure 395. MCE implementation of stream cipher
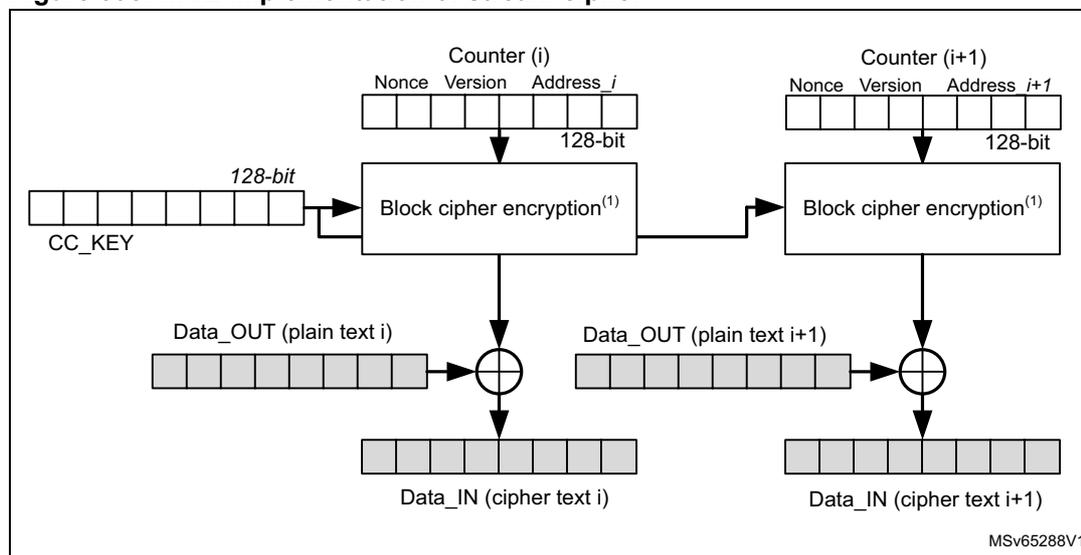
The diagram illustrates the stream cipher encryption process. It shows two stages for data blocks 'i' and 'i+1'. For each stage, a 128-bit counter information (Nonce, Version, Address) is input to a 'Block cipher encryption' block along with a 128-bit 'CC_KEY'. The output of the encryption block is XORed with the 'Data_OUT (plain text)' to produce the 'Data_IN (cipher text)'. The counter information for block 'i+1' is derived from the counter information for block 'i'.
1. Operation starts from the capture of the address.
Every 128-bit data block (i), a counter (i) information is computed, as defined below:
- Counter[127:0] = MCE_CCzNR1[31:0] || MCE_CCzNR0[31:0] || 0b0000 0000 0000 0000 || MCE_CCzCFGR[31:16] || 0b0000 || Address_i [31:4].
Address i is the physical address of block (i), modulo 16 bytes.
Version and Nonce are stored by application respectively in MCE_CCzCFGR and MCE_CCzNRx registers, with cipher context z selected in MCE_REGCR (CTXID = z).
The least significant byte of Data_IN and Data_OUT are stored in the first 8 bits of the data blocks.
CC_KEY is stored in write-only MCE_CCzKEYRx registers, with cipher context z selected in MCE_REGCR (CTXID = z). Bypass mode is selected instead of stream cipher mode if the selected key is not marked as valid, that is KEYCRC[7:0] in MCE_CCyCFGR is different from 0x0.
Note: Stream cipher mode offers no protection against bit-flip attacks, and is sensitive against side channel attacks.
Caution: In order to secure the confidentiality of the information encrypted with the stream cipher in region x, it is important to clear the WREN bit in MCE_ATTRx register as soon as the whole region has been encrypted by the application (read-only region).
Caution: When MCE is used in conjunction with XSPI it is mandatory to read or write the flash memory using the memory map mode of the flash memory controller.
Relative performances are described on Table 361 . Refer to Section 39.3: MCE implementation to identify which cipher is used for which MCE instance.
Table 361. MCE stream cipher latencies
| Cipher type | Stream mode | ENC bit in MCE_REGCRx | Latency for 16 bytes data (in AXI cycles) | Optimization for sequential accesses |
|---|---|---|---|---|
| AES | Normal | 01 | 11 | Yes |
39.4.7 MCE AXI traffic management
MCE includes a special AXI-64 read-write arbitration scheme, designed to speed-up multiple reads. More specifically, when no write is ongoing in MCE the two cipher cores can be allocated to decrypt two reads in parallel. In this case an incoming write request is stalled until the cipher core allocated to writes is free.
Note: Best performances are obtained when transactions are aligned on two 64-bit words for regions where block cipher is selected. See Section 39.4.5 for details.
39.4.8 MCE encryption disable options
When MCE feature is not available in the product encryption/decryption feature of MCE is not usable, for any region. It means that reads (resp. writes) through MCE are not decrypted (resp. encrypted).
When an unexpected event occurs, the ENCDIS bit is set in MCE_SR register and the following effects apply:
- • All previously written key materials are erased.
- • If ENC bit and BREN bits are set in MCE_REGCRx, all writes to this region x are ignored and all read requests return zero.
In such an event, the application must reset the MCE peripheral to be able to use encrypted regions again.
39.4.9 MCE error management
When an illegal access to a configuration register occurs (bad privilege) corresponding CAEF bit is set in MCE_IASR. Application cleans this flag using CAEF bit in MCE_IACR.
When an illegal access through the system bus occurs (bad privilege, forbidden write, overlapping encrypted regions) corresponding IAEF bit is set in MCE_IASR. Application cleans this flag using IAEF bit in MCE_IACR.
Additional debug information on system bus illegal accesses can be read in illegal access error status register (MCE_IAESR) and optionally the illegal address register (MCE_IADDR).
Illegal read (resp. write) through the system bus returns zero (resp. is ignored).
Read to write-only or write to read-only registers do not trigger an interrupt. Reading any MCE key register returns zeros.
39.5 MCE interrupts
There are two individual maskable interrupt sources generated by the MCE, signaling the following error events:
- • Illegal access through the configuration bus (CAEF), see Section 39.4.9
- • Illegal access through the system bus (IAEF), see Section 39.4.9
Those interrupt sources are connected to the same global interrupt request signal mce_it.
Setting the appropriate mask bit in MCE_IAIER register enables the interrupt. The status of the individual interrupt events can be read from MCE_IASR, and cleared in MCE_IACR register.
Table 362 gives a summary of the available features.
Table 362. MCE interrupt requests
| Interrupt acronym | Interrupt event | Event flag (1) | Enable control bit | Interrupt clear method |
|---|---|---|---|---|
| MCE | Configuration access error | CAEF | CAEIE | Set CAEF bit in MCE_IACR |
| Illegal access error | IAEF | IAEIE | Set IAEF bit in MCE_IACR |
- 1. Read in MCE_IASR register
39.6 MCE registers
39.6.1 MCE configuration register (MCE_CR)
Address offset: 0x000
Reset value: 0x0000 0000
Privileged read and write access only if PRIV is set in MCE_PRIVCFGR.
Writes are ignored if GLOCK is set in MCE_CR register.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | MK LOCK | GLOCK |
| rs | rs |
Bits 31:2 Reserved, must be kept at reset value.
Bit 1 MKLOCK : Master keys lock
Lock the master key configurations until next reset. This bit is cleared by default and once set it cannot be reset until MCE reset.
0: Writes to MCE_MKEYRx and MCE_FMKEYRx registers are allowed
1: Writes to MCE_MKEYRx and MCE_FMKEYRx registers are ignored until next MCE reset.
Effect of this bit depends on the number of master keys. See Section 39.3: MCE implementation for details.
Bit 0 GLOCK : Global lock
Lock the configuration of most MCE registers until next reset. This bit is cleared by default and once set it cannot be reset until MCE reset.
0: MCE registers are writable
1: All writes to MCE registers are ignored, with the exception of MCE_IACR and MCE_IAIER registers.
39.6.2 MCE status register (MCE_SR)
Address offset: 0x004
Reset value: 0x0000 0000
Privileged read access only if PRIV is set in MCE_PRIVCFGR.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | ENC DIS | Res. | FMK VALID | Res. | MK VALID |
| r | r | r |
Bits 31:5 Reserved, must be kept at reset value.
Bit 4 ENCDIS : encryption disabled
This bit is set by hardware when the encryption feature is not functional.
0: When ENC bit and BREN are set in MCE_REGCRx all allowed write accesses in region x are encrypted, and all allowed read requests are decrypted.
1: When ENC bit and BREN are set in any MCE_REGCRx all write accesses in region x are ignored, and all read requests return zero. All previously written key material are also erased.
When ENCDIS is set application must reset MCE peripheral to be able to use the encryption feature again.
Bit 3 Reserved, must be kept at reset value.
Bit 2 FMKVALID : Fast master key valid
0: A valid key has not been written in MCE_FMKEYRx registers, or a valid unlocked fast master key has been erased by hardware (if bit was set before)
1: A valid key has been written in MCE_FMKEYRx registers (write R0 -> R1 -> R2 -> R3 or the reverse)
This bit is reserved when fast master key is not present in the MCE instance. See Section 39.3: MCE implementation for detail.
Bit 1 Reserved, must be kept at reset value.
Bit 0 MKVALID : Master key valid
0: A valid key has not been written in MCE_MKEYRx registers, or a valid unlocked master key has been erased by hardware (if bit was set before)
1: A valid key has been written in MCE_MKEYRx registers (write R0 -> R1 -> R2 -> R3 or the reverse)
39.6.3 MCE illegal access status register (MCE_IASR)
Address offset: 0x008
Reset value: 0x0000 0000
Privileged read access only if PRIV is set in MCE_PRIVCFGR.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | IAEF | CAEF |
| r | r |
Bits 31:2 Reserved, must be kept at reset value.
Bit 1 IAEF : Illegal access error flag
This bit is set when an illegal access is detected on the system bus. More details on the error can be found in MCE_IAESR and MCE_IADDR registers.
This bit is cleared by setting corresponding bit in MCE_IACR register.
Bit 0 CAEF : Configuration access error flag
This bit is set when an illegal access to any MCE configuration register is detected. Bit is cleared by setting corresponding bit in MCE_IACR register. No additional details on the error is available.
39.6.4 MCE illegal access clear register (MCE_IACR)
Address offset: 0x00C
Reset value: 0x0000 0000
Privileged write access only if PRIV is set in MCE_PRIVCFGR.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | IAEF | CAEF |
| w | w |
Bits 31:2 Reserved, must be kept at reset value.
Bit 1 IAEF : Illegal access error flag clear
Set this bit to clear IAEF bit in MCE_IASR register. Clearing IAEF bit permits to capture new error information in MCE_IAESR and MCE_IADDR registers.
Note that clearing this bit does not clear RISAB_IADDR register.
Bit 0 CAEF : Configuration access error flag clear
Set this bit to clear CAEF bit in MCE_IASR register.
39.6.5 MCE illegal access interrupt enable register (MCE_IAIER)
Address offset: 0x010
Reset value: 0x0000 0000
Privileged read and write access only if PRIV is set in MCE_PRIVCFGR.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | IAEIE | CAEIE |
| rw | rw |
Bits 31:2 Reserved, must be kept at reset value.
Bit 1 IAEIE : Illegal access error interrupt enable
0: Interrupt generation on illegal access errors is disabled
1: Interrupt generation when an illegal access error occurs (IAEF = 1)
Bit 0 CAEIE : Configuration access error interrupt enable
0: Interrupt generation on configuration access errors is disabled
1: Interrupt generation when a configuration access error occurs (CAEF = 1)
39.6.6 MCE privileged configuration register (MCE_PRIVCFGR)
Address offset: 0x1C
Reset value: 0x0000 0000
Privileged write access only.
Any read is allowed. Writes are ignored if GLOCK is set in MCE_CR register.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PRIV |
| r/w |
Bits 31:1 Reserved, must be kept at reset value.
Bit 0 PRIV : Privileged configuration
0: Privileged and unprivileged access are granted to MCE registers
1: Only privileged access are granted to MCE registers
39.6.7 MCE illegal access error status register (MCE_IAESR)
Address offset: 0x020
Reset value: 0x0000 0000
Privileged read access only if PRIV is set in MCE_PRIVCFGR.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | IANRW | Res. | Res. | IAPRIV | Res. | Res. | Res. | Res. |
| r | r |
Bits 31:8 Reserved, must be kept at reset value.
Bit 7 IANRW : Illegal access read/write
When IAEF bit is set in MCE_IASR register IANRW bit captures the access type of the illegal access detected.
0: Illegal access was a data read or an instruction fetch.
1: Illegal access was a data write.
Bits 6:5 Reserved, must be kept at reset value.
Bit 4 IAPRIV : Illegal access privilege
When IAEF bit is set in MCE_IASR register IAPRIV bit captures the privileged state of the master that issued the illegal access detected on the AXI system bus.
0: Illegal access was unprivileged.
1: Illegal access was privileged.
Bits 3:0 Reserved, must be kept at reset value.
39.6.8 MCE illegal address register (MCE_IADDR)
Address offset: 0x024
Reset value: 0x0000 0000
Privileged read access only if PRIV is set in MCE_PRIVCFGR.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| IADD[31:16] | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| IADD[15:0] | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
Bits 31:0 IADD[31:0] : Illegal address
When IAEF bit is set in MCE_IASR register, IADD bitfield captures the 32-bit bus address of the erroneous access. Additional information can be found in MCE_IAESR register.
39.6.9 MCE region x configuration register (MCE_REGCRx)
Address offset: 0x040 + 0x10 * (x - 1), (x = 1 to 4)
Reset value: 0x0000 0000
Privileged read and write access only if PRIV is set in MCE_PRIVCFGR. Writes are ignored if GLOCK is set in MCE_CR register.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PRIV |
| rw | |||||||||||||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| ENC[1] | ENC[0] | Res. | Res. | Res. | CTXID[1] | CTXID[0] | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | BREN |
| rw | rw | rw | rw | rw |
Bits 31:17 Reserved, must be kept at reset value.
Bit 16 PRIV : Privileged region
This bit is taken into account only if BREN is set.
0: Application can access to region x in privileged and unprivileged mode.
1: Application can access to region x in privileged mode only.
Bits 15:14 ENC[1:0] : Encrypted region
Those bits are taken into account only if BREN is set and if the corresponding encryption feature is available in the MCE instance (see Section 39.3: MCE implementation ). Write to these bits is ignored if BREN is set.
00: No effect
01: Stream cipher - All allowed read (resp. write) requests are decrypted (resp. encrypted) using the stream cipher, when CCEN bit is set in MCE_CCzCFGR (where CTXID = z).
10: Block cipher - All allowed read (resp. write) requests are decrypted (resp. encrypted) using the SCA resistant block cipher. If CTXID = 0 and MKVALID = 0 bypass mode is selected instead. If CTXID = z and CCEN bit is cleared in MCE_CCzCFGR bypass mode is also selected.
11: Fast block cipher - All allowed read (resp. write) requests are decrypted (resp. encrypted) using the fast block cipher. If CTXID = 0 and FMKVALID = 0 bypass mode is selected instead. If CTXID = z and CCEN bit is cleared in MCE_CCzCFGR bypass mode is also selected.
Bits 13:11 Reserved, must be kept at reset value.
Bits 10:9 CTXID[1:0] : Context ID
This bitfield defines the cryptographic context used by the cipher engine assigned to this region. If ENC = 00 bitfield CTXID is ignored. If BREN is set write to this bitfield is ignored.
00: If ENC = 10 (resp. 11) the key stored in MCE_MKEYR (resp. MCE_FMKEYR) registers is used by the block cipher. If ENC = 01 bypass mode is selected instead of stream cipher.
01: If ENC = 10 or 11 the key stored in MCE_CC1KEYR is used by the block cipher. If ENC = 01 the key stored in MCE_CC1KEYR is used by the stream cipher. The nonce in MCE_CC1NRx registers and the version in MCE_CC1CR register are also used.
10: If ENC = 10 or 11 the key stored in MCE_CC2KEYR is used by the block cipher. If ENC = 01 the key stored in MCE_CC2KEYR is used by the stream cipher. The nonce in MCE_CC2NRx registers and the version in MCE_CC2CR register are also used.
11: Reserved
Bits 8:1 Reserved, must be kept at reset value.
Bit 0 BREN : Base region enable
0: Region x is disabled. Access control of primary region (privileged or unprivileged, no encryption) applies to any access between this region start and end addresses.
1: Region x is enable. Access controls and encryption option defined in this region apply to any access between this region start and end addresses.
BREN cannot be set if BADDRSTART > BADDREND.
39.6.10 MCE start address for region x register (MCE_SADDRx)
Address offset: \( 0x044 + 0x10 * (x - 1) \) , ( \( x = 1 \) to \( 4 \) )
Reset value: 0x0000 0000
Privileged read and write access only if PRIV is set in MCE_PRIVCFGR. Writes are ignored if GLOCK is set in MCE_CR register, or if BREN is set in MCE_REGCRx.
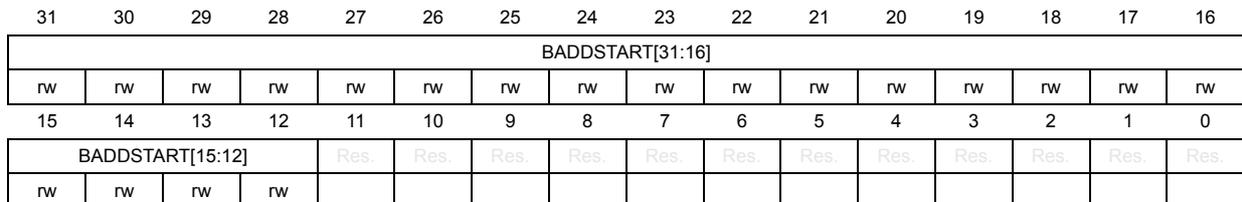
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| BADDSTART[31:16] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| BADDSTART[15:12] | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | |||
| rw | rw | rw | rw | ||||||||||||
Bits 31:12 BADDSTART[31:12] : Region address start
This bitfield defines the absolute start address of the region x on 4 Kbyte boundary (inclusive).
BREN cannot be set if BADDRSTART > BADDREND.
When MCE determines the region, the first 12 bits (LSB) and the last 4 bits (MSB) in this register are ignored, and when this register is accessed in read the 4 MSB bits and the 12 LSB bits return zeros (reference value in MCE).
Bits 11:0 Reserved, must be kept at reset value.
39.6.11 MCE end address for region x register (MCE_EADDRx)
Address offset: \( 0x048 + 0x10 * (x - 1) \) , ( \( x = 1 \) to \( 4 \) )
Reset value: 0x0000 0FFF
Privileged read and write access only if PRIV is set in MCE_PRIVCFGR. Writes are ignored if GLOCK is set in MCE_CR register, or if BREN is set in MCE_REGCRx.
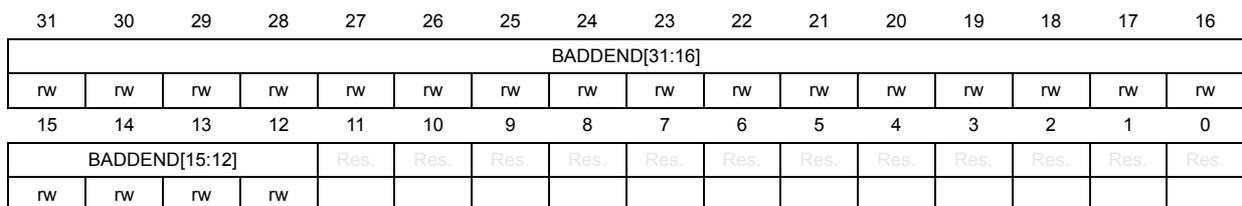
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| BADDEND[31:16] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| BADDEND[15:12] | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | |||
| rw | rw | rw | rw | ||||||||||||
Bits 31:12 BADDEND[31:12] : Region address end
This bitfield defines the absolute end address of the region x on 4 Kbyte boundary (inclusive).
BREN cannot be set if BADDRSTART > BADDREND.
When MCE determines the region, the first 12 bits (LSB) and the last 4 bits (MSB) in this register are ignored, and when this register is accessed in read the 4 MSB bits return zeros and the 12 LSB bits return ones (reference value in MCE).
Bits 11:0 Reserved, must be kept at reset value.
39.6.12 MCE attribute for region x register (MCE_ATTRx)
Address offset: \( 0x04C + 0x10 \times (x - 1) \) , ( \( x = 1 \) to \( 4 \) )
Reset value: 0x0000 0000
Privileged read and write access only if PRIV is set in MCE_PRIVCFGR. Writes are ignored if GLOCK is set in MCE_CR register
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WREN |
| rw | |||||||||||||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
Bits 31:17 Reserved, must be kept at reset value.
Bit 16 WREN : Write enable
This bit is taken into account only if BREN is set.
0: Writes to region x are ignored. Reads are allowed.
1: Region x can be read and written. Restrictions linked to PRIV bit in MCE_REGCRx apply.
Bits 15:0 Reserved, must be kept at reset value.
39.6.13 MCE master key x (MCE_MKEYRx)
Address offset: \( 0x200 + 0x4 \times x \) , ( \( x = 0 \) to \( 3 \) )
Reset value: 0x0000 0000
Privileged write access only if PRIV is set in MCE_PRIVCFGR.
Writes are ignored if MKLOCK or GLOCK bit is set in MCE_CR register.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| MKEY{32 * x + i} | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| MKEY{32 * x + i} | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
Bits 31:0 MKEY{32 * x + i} : Master key bit ( \( i = 0 \) to \( 31 \) )
This key is used by the MCE block cipher in normal, SCA resistant mode, if CTXID = 0x0 in MCE_REGCR register.
39.6.14 MCE fast master key x (MCE_FMKEYRx)
Address offset: \( 0x220 + 0x4 \times x \) , ( \( x = 0 \) to \( 3 \) )
Reset value: 0x0000 0000
Privileged write access only if PRIV is set in MCE_PRIVCFGR.
Writes are ignored if MKLOCK or GLOCK bit is set in MCE_CR register.
Refer to Section 39.3 to verify if this instance of MCE implements this register.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| FMKEY{32 * x + i} | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| FMKEY{32 * x + i} | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
Bits 31:0 FMKEY{32 * x + i} : Fast master key bit (i = 0 to 31)
This key is used by the MCE block cipher in fast mode, if CTXID = 0x0 in MCE_REGCR register.
39.6.15 MCE cipher context z configuration register (MCE_CCzCFGR)
Address offset: 0x240 + 0x30 *(z - 1) (z = 1 to 2)
Reset value: 0x0000 0000
Privileged read and write access only if PRIV is set in MCE_PRIVCFGR.
Writes are ignored if CCLOCK bit is set in this register. Writes are also ignored if GLOCK is set in MCE_CR register.
Refer to Section 39.3 to verify if this instance of MCE implements those registers.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| VERSION[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| KEYCRC[7:0] | Res | Res | Res | Res | Res | KEYLOCK | CCLOCK | CCEN | |||||||
| r | r | r | r | r | r | r | rs | rs | rw | ||||||
This 16-bit bitfield must be correctly initialized before CCEN bit is set. Bitfield usage is defined in Section 39.4.6: MCE stream cipher encryption mode .
Bits 15:8 KEYCRC[7:0] : Key CRCWhen KEYLOCK = 0, KEYCRC information is automatically computed by hardware while loading the key of this region in this exact sequence: KEYR0 then KEYR1 then KEYR2 then finally KEYR3 (all written once). A new KEYCRC computation starts as soon as a new valid sequence is initiated. KEYCRC bitfield reads as zero until a valid sequence is completed (after it return the computed CRC value).
When GLOCK = 1, KEYCRC bitfield always return the computed CRC value until the next reset.
CRC computation is an 8-bit checksum using the standard CRC-8-CCITT algorithm \( X^8 + X^2 + X + 1 \) (according the convention).
CRC information is updated, and the key is usable by MCE, only after the last bit of the key has been written.
When GLOCK = 0 any write to MCE_CCxKEYR registers clears KEYCRC in MCE_CCxCFGR, and makes the cipher context key un-usable (bypass mode is selected instead). To be able to use the key again application must perform this sequence: write to KEYR0 then KEYR1 then KEYR2 then finally KEYR3 (all written once). As KEYLOCK = 1 all those writes are ignored, so the correct key is used instead.
Bits 7:3 Reserved, must be kept at reset value.
Bit 2 KEYLOCK : Key lock0: Writes to MCE_CCzKEYR registers are allowed
1: Writes to MCE_CCzKEYR registers are ignored until next MCE reset.
Note: This bit is set once. If this bit is set, it can only be cleared to 0 if MCE is reset.
Bit 1 CCLOCK : Cipher context lock0: Writes to MCE_CCxCFGR and MCE_CCzNR registers are allowed
1: Writes to MCE_CCxCFGR and MCE_CCzNR registers are ignored until next MCE reset.
Note: This bit is set once. If this bit is set, it can only be cleared to 0 if MCE is reset. Setting this bit forces KEYLOCK bit to 1.
Bit 0 CCEN : Cipher context enable0: If an enabled region selects CTXID = z bypass mode is selected by MCE
1: If an enabled region selects CTXID = z with ENC = 01 MCE selects with the stream cipher the information stored in MCE_CCxCFGR, MCE_CCzNR and MCE_CCzKEYR. If the enabled region selects ENC = 10 or 11 instead MCE selects with the block cipher the key information stored in MCE_CCzKEYR.
39.6.16 MCE cipher context z nonce register 0 (MCE_CCzNR0)
Address offset: \( 0x244 + 0x30 \cdot (z - 1) \) ( \( z = 1 \) to \( 2 \) )
Reset value: 0x0000 0000
Privileged read and write access only if PRIV is set in MCE_PRIVCFGR.
Writes are ignored if CCLOCK is set in MCE_CCzCFGR register, or GLOCK bit is set in MCE_CR register.
Refer to Section 39.3 to verify if this instance of MCE implements those registers.
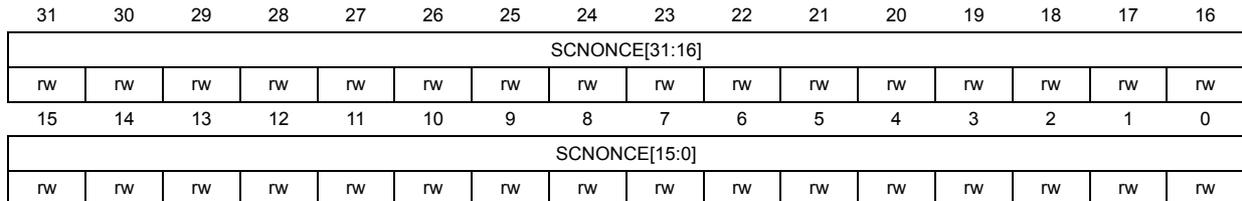
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| SCNONCE[31:16] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| SCNONCE[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 SCNONCE[31:0] : Stream cipher nonce, bits [31:0]
This register is used by stream cipher to compute keystream. It must be correctly initialize before CCEN bit is set in MCE_CCzCFGR register. Bitfield usage is defined in Section 39.4.6: MCE stream cipher encryption mode .
39.6.17 MCE cipher context z nonce register 1 (MCE_CCzNR1)
Address offset: \( 0x248 + 0x30 \cdot (z - 1) \) ( \( z = 1 \) to \( 2 \) )
Reset value: 0x0000 0000
Privileged read and write access only if PRIV is set in MCE_PRIVCFGR.
Writes are ignored if CCLOCK is set in MCE_CCzCFGR register, or GLOCK bit is set in MCE_CR register.
Refer to Section 39.3 to verify if this instance of MCE implements those registers.
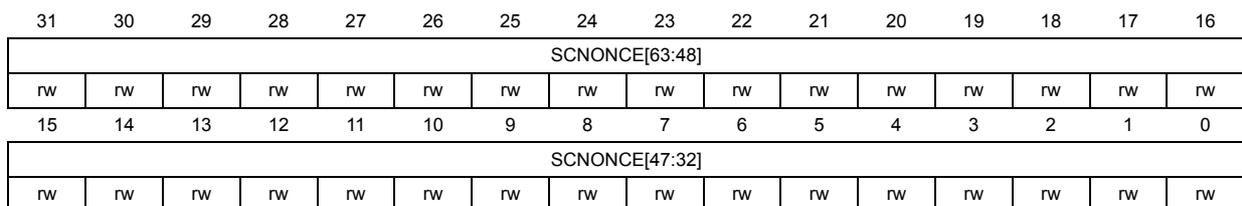
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| SCNONCE[63:48] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| SCNONCE[47:32] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 SCNONCE[63:32] : Stream cipher nonce, bits [63:32]
Refer to the MCE_CCzNR0 register for description of the SCNONCE[63:0] bitfield.
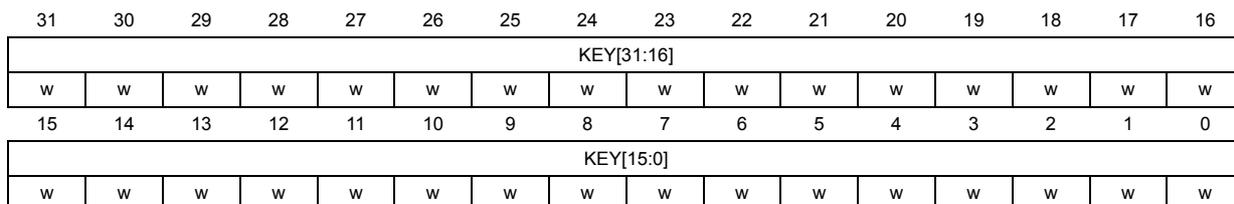
39.6.18 MCE cipher context z key register 0 (MCE_CCzKEYR0)
Address offset: \( 0x24C + 0x30 \cdot (z - 1) \) ( \( z = 1 \) to \( 2 \) )
Reset value: 0x0000 0000
Privileged write access only if PRIV is set in MCE_PRIVCFGR.
Writes are ignored if CCLOCK or KEYLOCK are set in MCE_CCzCFGR register, or GLOCK bit is set in MCE_CR register.
Refer to Section 39.3 to verify if this instance of MCE implements those registers.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| KEY[31:16] | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| KEY[15:0] | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
Bits 31:0 KEY[31:0] : cipher key, bits [31:0]
This register is used by the block or stream cipher of MCE when CTXID = z in encrypted region configuration register. KEY[127:0] must be correctly initialize before CCEN bit is set in MCE_CCzCFGR register.
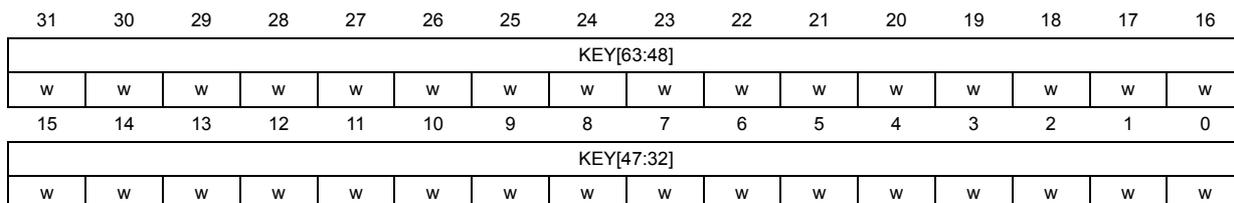
39.6.19 MCE cipher context z key register 1 (MCE_CCzKEYR1)
Address offset: \( 0x250 + 0x30 \cdot (z - 1) \) ( \( z = 1 \) to \( 2 \) )
Reset value: 0x0000 0000
Privileged write access only if PRIV is set in MCE_PRIVCFGR.
Writes are ignored if CCLOCK or KEYLOCK are set in MCE_CCzCFGR register, or GLOCK bit is set in MCE_CR register.
Refer to Section 39.3 to verify if this instance of MCE implements those registers.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| KEY[63:48] | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| KEY[47:32] | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
Bits 31:0 KEY[63:32] : cipher key, bits [63:32]
Refer to the MCE_CCzKEYR0 register for description of the KEY[127:0] bitfield.
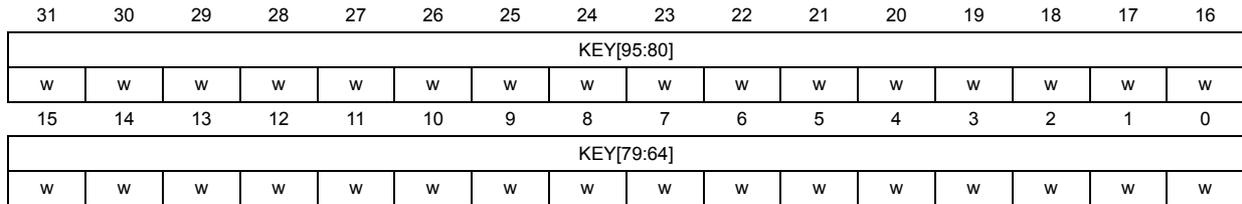
39.6.20 MCE cipher context z key register 2 (MCE_CCzKEYR2)
Address offset: \( 0x254 + 0x30 \cdot (z - 1) \) ( \( z = 1 \) to \( 2 \) )
Reset value: 0x0000 0000
Privileged write access only if PRIV is set in MCE_PRIVCFGR.
Writes are ignored if CCLOCK or KEYLOCK are set in MCE_CCzCFGR register, or GLOCK bit is set in MCE_CR register.
Refer to Section 39.3 to verify if this instance of MCE implements those registers.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| KEY[95:80] | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| KEY[79:64] | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
Bits 31:0 KEY[95:64] : cipher key, bits [95:64]
Refer to the MCE_CCzKEYR0 register for description of the KEY[127:0] bitfield.
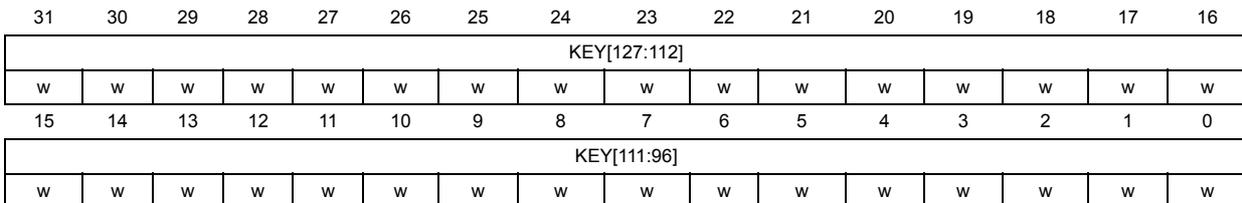
39.6.21 MCE cipher context z key register 3 (MCE_CCzKEYR3)
Address offset: \( 0x258 + 0x30 \cdot (z - 1) \) ( \( z = 1 \) to \( 2 \) )
Reset value: 0x0000 0000
Privileged write access only if PRIV is set in MCE_PRIVCFGR.
Writes are ignored if CCLOCK or KEYLOCK are set in MCE_CCzCFGR register, or GLOCK bit is set in MCE_CR register.
Refer to Section 39.3 to verify if this instance of MCE implements those registers.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| KEY[127:112] | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| KEY[111:96] | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
Bits 31:0 KEY[127:96] : cipher key, bits [127:96]
Refer to the MCE_CCzKEYR0 register for description of the KEY[127:0] bitfield.
39.6.22 MCE register map
Table 363. MCE register map and reset values
| Offset | Register name reset value | 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 | 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0x000 | MCE_CR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | MKLOCK | GLOCK |
| Reset value | 0 | 0 | |||||||||||||||||||||||||||||||
| 0x004 | MCE_SR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | ENCDIS | Res. | FMKVALID | Res. | MKVALID |
| Reset value | 0 | 0 | 0 | ||||||||||||||||||||||||||||||
| 0x008 | MCE_IASR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | IAEF | CAEF |
| Reset value | 0 | 0 | |||||||||||||||||||||||||||||||
| 0x00C | MCE_IACR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | IAEF | CAEF |
| Reset value | 0 | 0 | |||||||||||||||||||||||||||||||
| 0x010 | MCE_IAIER | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | IAEIE | CAEIE |
| Reset value | 0 | 0 | |||||||||||||||||||||||||||||||
| 0x01C | MCE_PRIVCFGR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PRIV |
| Reset value | 0 | ||||||||||||||||||||||||||||||||
| 0x020 | MCE_IAESR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | IANRW | Res. | Res. | Res. | IAPRIV | Res. | Res. | Res. |
| Reset value | 0 | 0 | |||||||||||||||||||||||||||||||
| 0x024 | MCE_IADDR | IADDR[31:10] | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | |||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||
| 0x040+ 0x10 * (x-1), (x = 1 to 4) | MCE_REGCRx | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PRIV | ENC[1] | ENC[0] | Res. | Res. | Res. | Res. | CTXID[1] | CTXID[0] | Res. | Res. | Res. | Res. | Res. | Res. | Res. | BREN |
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||||||||||||||||||
| 0x044+ 0x10 * (x-1), (x = 1 to 4) | MCE_SADDRx | BADDSTART[31:16] | BADDSTART[15:12] | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | ||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||||||||
| 0x048+ 0x10 * (x-1), (x = 1 to 4) | MCE_EADDRx | BADDEND[31:16] | BADDEND[15:12] | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | ||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||||||||
| 0x04C+ 0x10 * (x-1), (x = 1 to 4) | MCE_ATTRx | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WREN | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| Reset value | 0 | ||||||||||||||||||||||||||||||||
| 0x200+0x 4 * x, (x = 0 to 3) | MCE_MKEYRx | MKEY{32 * x + i} (i = 0 to 31) | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x220+0x 4 * x, (x = 0 to 3) | MCE_FMKEYRx | FMKEY{32 * x + i} (i = 0 to 31) | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x240 | MCE_CC1CFGR | VERSION[15:0] | KEYCRC[7:0] | Res. | Res. | Res. | Res. | Res. | KEYLOCK | CCLOCK | CCEN | ||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||||||
Table 363. MCE register map and reset values (continued)
| Offset | Register name reset value | 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 | 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0x244 | MCE_CC1NR0 | SCNONCE[31:0] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x248 | MCE_CC1NR1 | SCNONCE[63:32] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x24C | MCE_CC1KEYR0 | KEY[31:0] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x250 | MCE_CC1KEYR1 | KEY[63:32] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x254 | MCE_CC1KEYR2 | KEY[95:64] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x258 | MCE_CC1KEYR3 | KEY[127:96] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x270 | MCE_CC2CFGR | VERSION[15:0] | KEYCRC[7:0] | Res. | Res. | Res. | Res. | Res. | KEYLOCK | CCLOCK | CCEN | ||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |||||||
| 0x274 | MCE_CC2NR0 | SCNONCE[31:0] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x278 | MCE_CC2NR1 | SCNONCE[63:32] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x27C | MCE_CC2KEYR0 | KEY[31:0] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x280 | MCE_CC2KEYR1 | KEY[63:32] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x284 | MCE_CC2KEYR2 | KEY[95:64] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x288 | MCE_CC2KEYR3 | KEY[127:96] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
Refer to Section 2.3: Memory organization for the register boundary addresses.