5. Secure memory management (SMM)
5.1 Introduction
STM32H73x microcontrollers offer a first set of protection mechanisms, which are similar to other STM32 Series:
- • Global readout device protection (RDP)
- • Write protection (WRP)
- • Proprietary code readout protection (PCROP)
A detailed description of these protection mechanisms is given in Section 4: Embedded Flash memory (FLASH) .
STM32H73x also offer an additional enhanced protection mode, the Secure access mode, that makes possible the development of user-defined secure services (e.g. secure firmware update or secure boot) and guarantees of a safe execution and protection of both code and data. This mechanism is described in details in Section 5.3: Secure access mode , Section 5.4: Root secure services (RSS) and Section 5.5: Secure user software .
The secure memory management unit is contained inside the D1 domain.
5.2 Glossary
The following terms will be used in herein:
Table 26. List of preferred terms
| Term | Description |
|---|---|
| Device Security Level | |
| Standard mode | Device state which allows the access to the user Flash memory, the option bytes and the bootloader area. |
| Secure access mode | Device state which allows the access to all the memory areas of the device. |
| Memory areas | |
| System memory | ST reserved memory area used to store ST ROM code. |
| User Flash memory | Flash memory area used to store user code and data. |
| Secure user memory/area (1) | This area can be configured to be accessed once after reset and be hidden for the firmware stored in the user Flash memory after the code stored in this area is executed. |
| Software services | |
| Bootloader | STMicroelectronics software executed at reset which allows the download of firmware from regular communication ports. |
| Root secure services (RSS) | STMicroelectronics software which allows the access to secure services. |
| Secure user software | User software executed once after reset, which can be used to implement secure boot and secure firmware update (SFU). Secure user software is located in secure user memory. |
- 1. Secure user memory/areas are also named secure-hide protected (HDP) memory/areas.
5.3 Secure access mode
Some sensitive functions require safe execution from potential malicious software attacks. Secure firmware update (SFU) software is a good example of code that requires a high level of protection since it handles secret data (such as cryptographic keys) that shall not be retrieved by other processes.
STM32H73x microcontrollers feature secure memory areas with restricted access. They allow building secure services that will be executed prior to any user application. These secure areas, together with the software they contain, are only accessible when configuring the device in Secure access mode.
Figure 14 gives an overview of Flash memory areas and services in Standard and Secure access modes.
Figure 14. Flash memory areas and services in Standard and Secure access modes
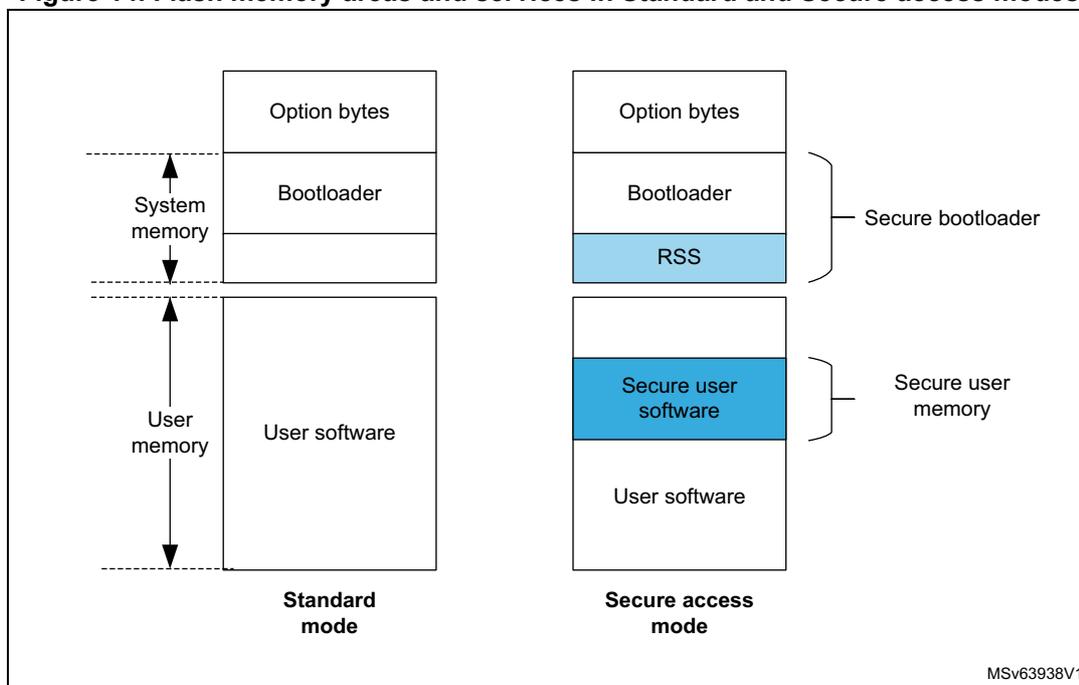
The diagram illustrates the Flash memory layout for two modes: Standard mode and Secure access mode. Both modes show a vertical stack of memory regions. In Standard mode, the regions are Option bytes, Bootloader, and User software. In Secure access mode, the regions are Option bytes, Bootloader, RSS (Root Secure Services), Secure user software, and User software. The RSS and Secure user software regions are highlighted in blue. Brackets on the right side of the Secure access mode diagram group the Bootloader and RSS as 'Secure bootloader' and the Secure user software and User software as 'Secure user memory'. On the left side, arrows indicate 'System memory' for the top section and 'User memory' for the bottom section. The diagram is labeled 'MSv63938V1' in the bottom right corner.
- 1. The protected areas that can only be accessed in Secure access mode are shown in blue.
5.3.1 Associated features
The Secure access mode can be configured through option bytes. When it is set, it enables access to:
- • STMicroelectronics root secure services to set secure user areas (see Section 5.4: Root secure services (RSS) )
- • Secure user memory which embeds secure user code and data.
For a summary of access rights for each core, refer to Section 5.6: Summary of Flash protection mechanisms .
5.3.2 Boot state machine
In Secure access mode, booting is forced in the RSS whatever the boot configuration (boot pins and boot addresses). The RSS can either set a secure user memory area if one has been requested (see Section 5.5.2: Setting secure user memory area ) or jump directly to the existing secure user memory. The code located in secure user memory is executed before the main user application and the bootloader. If no service is required and no secure area is defined, the RSS jumps to the boot address selected by BOOT0 pin value.
Figure 15 shows the boot state machine.
Figure 15. Bootloader state machine in Secure access mode
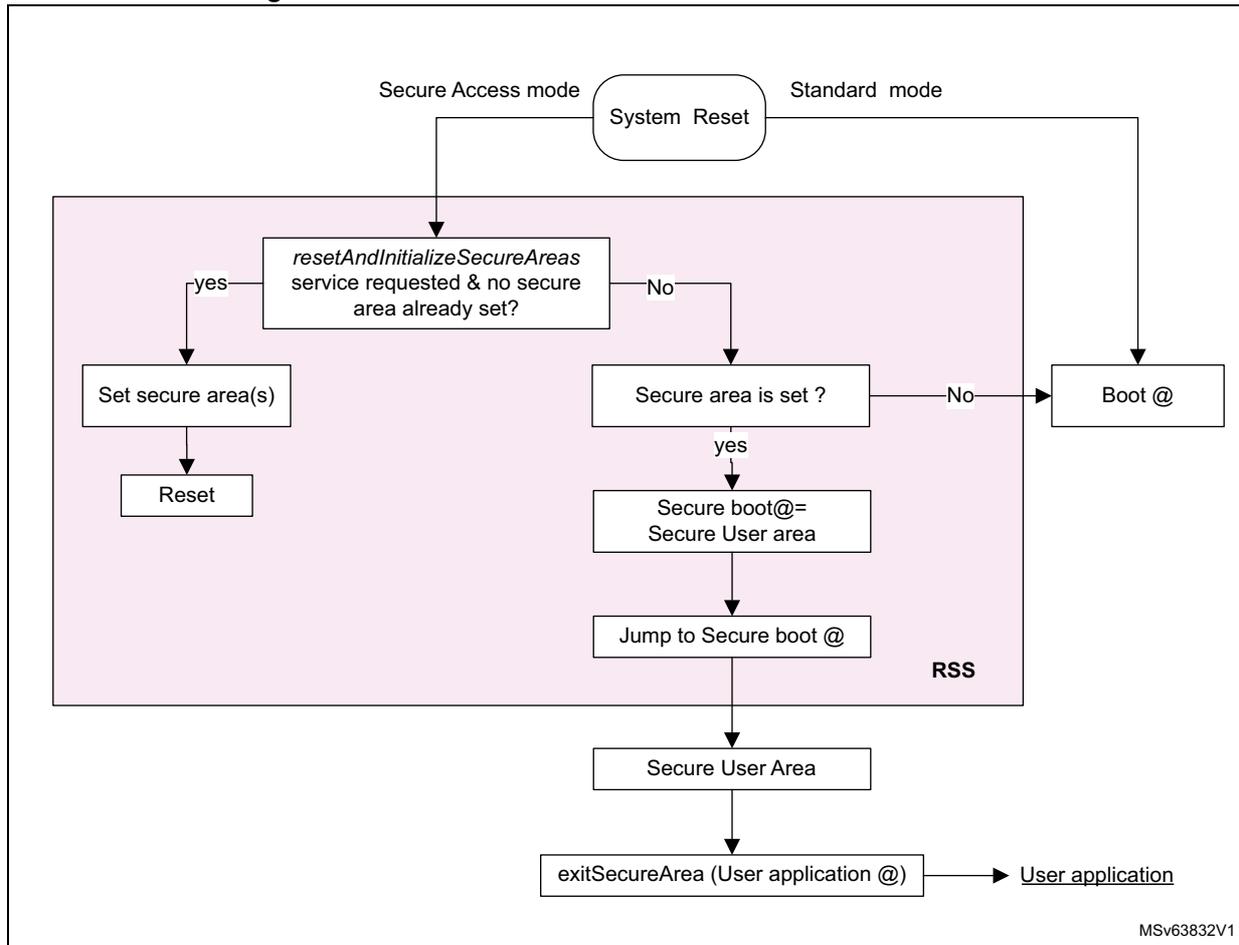
graph TD; SystemReset([System Reset]) -- Secure Access mode --> RSS; SystemReset -- Standard mode --> BootAt[Boot @]; subgraph RSS; resetAndInitializeSecureAreas[resetAndInitializeSecureAreas service requested & no secure area already set?]; resetAndInitializeSecureAreas -- yes --> SetSecureArea[Set secure area(s)]; SetSecureArea --> Reset[Reset]; resetAndInitializeSecureAreas -- No --> SecureAreaIsSet[Secure area is set?]; SecureAreaIsSet -- yes --> SecureBoot[Secure boot@= Secure User area]; SecureAreaIsSet -- No --> BootAt; SecureBoot --> JumpSecureBoot[Jump to Secure boot @]; end; JumpSecureBoot --> SecureUserArea[Secure User Area]; SecureUserArea --> ExitSecureArea[exitSecureArea (User application @)]; ExitSecureArea --> UserApplication[User application]; MSV63832V1[MSV63832V1];
5.3.3 Secure access mode configuration
Enabling Secure access mode
There is no restriction on how to activate Secure access mode on the device. It is configured through the SECURITY option bit in FLASH_OPTSR_CUR register (see Section 4.9.8: FLASH option status register (FLASH_OPTSR_CUR) ).
The Secure access mode becomes active after a system reset.
Disabling Secure access mode
Disabling Secure access mode is a more sensitive task as it can only be done if no more protected code exists on the device. As a result, to come back to Standard mode, secure user memories and PCROP/execute-only areas shall be removed before clearing the SECURITY option bit in the FLASH_OPTSR_CUR register.
Protected areas can be removed by performing a Flash mass erase (refer to Section 4.3.10: FLASH erase operations for more details on mass erase sequence).
5.4 Root secure services (RSS)
5.4.1 Secure area setting service
STMicroelectronics provides a service to perform the initialization of secure areas. This service can be called only once. It is executed after a system reset in Secure access mode prior to any other software stored in the device.
Caution: RSS software cannot be accessed (read, write, execute and debug) when the STM32H73x operate in Standard mode. The service can be automatically accessed with ST programming tool, STM32CubeProgrammer, or called through a direct call to the resetAndInitializeSecureAreas function defined below.
resetAndInitializeSecureAreas
| Prototype | void resetAndInitializeSecureAreas(RSS_SecureArea_t area) |
| Arguments | Secure user area start and end addresses. This service sets secure user area boundaries, following the values stored in the option byte registers: |
| Description | – SEC_AREA_START and SEC_AREA_END This service can be used only when a secure area is set for the first time. A system reset is triggered after service completion. |
5.4.2 Secure area exiting service
The RSS also provides the exitSecureArea service. This service must be called to jump to user application. It allows closing safely the secure user area to guarantee that its content can no more be accessed.
Contrary to the resetAndInitializeSecureAreas service, it does not trigger any system reset. exitSecureArea function is defined below:
exitSecureArea
| Prototype | void exitSecureArea (unsigned int vectors, unsigned int jtagState) |
| Arguments | Address of application vectors where to jump after exit and state of JTAG after exit: RSS_ENABLE_JTAG_AT_EXIT: JTAG enabled after exiting the secure area RSS_KEEP_JTAG_DISABLED_AT_EXIT: JTAG disabled after exiting the secure area |
| Description | This service is used to exit from secure user software and jump to user main application. There is no system reset triggered by this service |
5.4.3 OTFDEC encryption service
The RSS includes the RSS_OTFD_resetAndEncrypt service to perform in-place encryption of the provided payload in RAM. Refer to AN5281 “How to use OTFDEC for encryption/decryption in trusted environment on STM32 MCUs” for more details.
5.5 Secure user software
A secure user software is a trusted piece of code that is executed after device power-on or after a system reset. It allows building secure applications such as:
- • code signature or integrity checking (user secure boot).
- • software license checking
- • secure firmware update
- • secure initialization
5.5.1 Access rules
Only accessible in Secure access mode, the secure user software is stored in the secure memory areas.
After secure user software execution, the code shall jump to the main user application and prevent access to the secure user area. This is done by calling exitSecureAreas secure service with the application code address given as parameter.
Once in the application code, any access to the secure user area triggers a Flash error.
5.5.2 Setting secure user memory area
The secure area size is configurable from 512 bytes to the full memory size with a granularity of 256 bytes.
The secure area boundaries are configured through SEC_AREA_START and SEC_AREA_END option bits in FLASH_SCAR_CUR (see Section 4.9.13: FLASH secure address (FLASH_SCAR_CUR) ).
Note: If the secure area start address is equal to the secure area end address, the whole Flash memory is considered as secure protected.
The above option bits can only be initialized through exitAndInitializeSecureAreas service.
If a secure area already exists, the secure user area code can update its own secure user area size.
5.6 Summary of Flash protection mechanisms
Figure 16 and Table 27 summarize the access rights of the different Flash memory areas, both in Secure access and Standard modes.
Figure 16. Core access to Flash memory areas
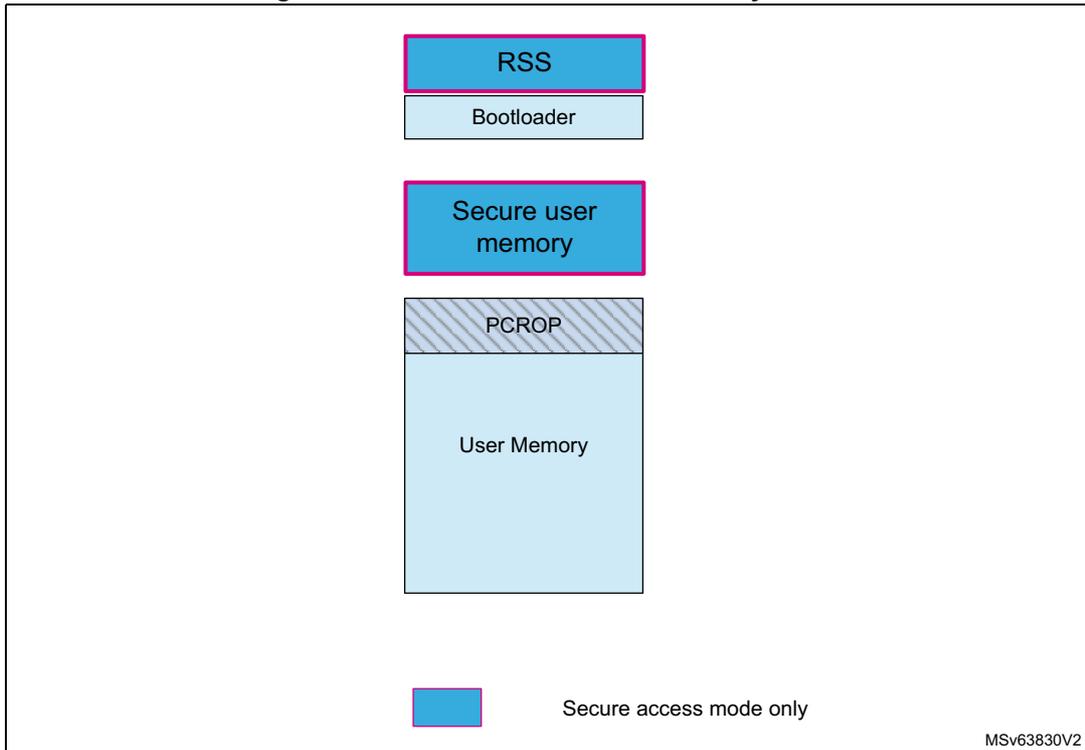
The diagram illustrates the memory layout of a microcontroller. At the top, there is a blue box labeled 'RSS' with a light blue box labeled 'Bootloader' directly below it. Further down is another blue box labeled 'Secure user memory'. Below that is a grey hatched box labeled 'PCROP', and at the bottom is a large light blue box labeled 'User Memory'. A legend at the bottom left shows a blue box next to the text 'Secure access mode only'. The diagram is labeled 'MSV63830V2' in the bottom right corner.
Table 27. Summary of Flash protected areas access rights
| Access type | Software area | Security mode | Access |
|---|---|---|---|
| Execution | PCROP | Any | ✓ |
| Secure user software | Secure access | ✓ (1) | |
| Root secure services | Secure access | ✓ (1) | |
| Read access | PCROP | Any | No |
| Secure user software | Secure access | ✓ (1) | |
| Root secure services | Secure access | ✓ (1) | |
| Debug access | PCROP | Any | No |
| Secure user software | Secure access | No | |
| Root secure services | Secure access | No |
1. Access rights granted after reset until code completion only.