4. Embedded flash memory (FLASH)
4.1 FLASH introduction
The flash memory interface manages the CPU1 AHB ICode and DCode accesses and the CPU2 AHB access to the flash memory. It implements the access arbitration between the two CPUs, the erase and program flash memory operations, the security mechanisms, and the read and write protection.
The flash memory interface accelerates code execution with a system of instruction prefetch and cache lines.
4.2 FLASH main features
- • Up to 256 Kbytes of flash memory single bank architecture
- • Memory organization: 1 bank
- – Main memory: up to 256 Kbytes
- – Page size: 2 Kbytes
- • 72-bit wide data read (64 bits plus 8 ECC bits)
- • 72-bit wide data write (64 bits plus 8 ECC bits)
- • Page erase (2 Kbytes) and mass erase
Flash memory interface features:
- • Flash memory read operations
- • Flash memory program/erase operations
- • Readout protection activated by option (RDP)
- • 2 write protection areas selected by option (WRP)
- • 2 proprietary code readout protection area selected by option (PCROP)
- • CPU2 security area
- • CPU2 hide protection area
- • Flash empty check
- • Program and erase suspension feature
- • Prefetch on CPU1 ICODE and CPU2 S-bus
- • CPU1 instruction cache: 32 cache lines of 4 x 64 bits on ICode (1-Kbyte RAM)
- • CPU1 data cache: 8 cache lines of 4 x 64 bits on DCode (256-byte RAM)
- • CPU2 instruction cache: 4 cache lines of 1 x 64 bits on S-bus (32-byte RAM)
- • Error code correction (ECC): 8 bits for 64-bit
- • Option byte loader
4.3 FLASH functional description
4.3.1 Flash memory organization
The flash memory is organized as 72-bit wide memory cells (64 bits plus 8 ECC bits) that can be used for storing both code and data constants.
The flash memory is organized as follows:
- • A main memory block containing 128 pages of 2 Kbytes, each page with eight rows of 256 bytes.
- • An information block containing:
- – System memory, from which the CPU1 boots in system memory boot mode
This area is reserved and contains the bootloader used to reprogram the flash memory through one of the following interfaces: USART1, USART2, I2C1, I2C2, I2C3, SPI1, SPI2S2. It is programmed by STMicroelectronics when the device is manufactured and protected against spurious write/erase operations. For further details, refer to AN2606 “ STM32 microcontroller system memory boot mode ”. - – System memory from which the CPU2 boots in System memory boot mode
This area is reserved and contains the SFI/RSS firmware used to authenticate and install the firmware in flash memory through one of the following interfaces: USART1, USART2, I2C1, I2C2, I2C3, SPI1, SPI2S2. It is programmed by STMicroelectronics when the device is manufactured, and protected against spurious write/erase operations. - – 1-Kbyte (128 double-word) OTP (one-time programmable) for user data
The OTP data cannot be erased and can be written only once. If only one bit is at 0, the entire double-word (64 bits) cannot be written anymore, even with the value 0x0000 0000 0000 0000. - – Option bytes for user configuration
- – System memory, from which the CPU1 boots in system memory boot mode
The memory organization is based on a main area and an information block, as shown in the table below.
Table 11. Flash memory - Single bank organization
| Area | Addresses | Size (Kbytes) | Name |
|---|---|---|---|
| Main memory | 0x0800 0000 - 0x0800 07FF | 2 | Page 0 |
| 0x0800 0800 - 0x0800 0FFF | 2 | Page 1 | |
| 0x0800 1000 - 0x0800 17FF | 2 | Page 2 | |
| 0x0800 1800 - 0x0800 1FFF | 2 | Page 3 | |
| ... | ... | ... | |
| 0x0803 F000 - 0x0803 F7FF | 2 | Page 126 | |
| 0x0803 F800 - 0x0803 FFFF | 2 | Page 127 | |
| Information block | 0x1FFF 0000 - 0x1FFF 6FFF | 28 | System memory |
| 0x1FFF 7000 - 0x1FFF 73FF | 1 | OTP area | |
| 0x1FFF 7800 - 0x1FFF 7FFF | 2 | Option bytes |
4.3.2 Empty check
During the OBL phase, after loading all options, the flash memory interface checks whether the first location of the main memory is programmed. The result of this check, in conjunction with the BOOT0 and BOOT1 information, is used to determine where the system must boot from. It prevents the system to boot from the flash main memory area when, for example, no user code is programmed.
The flash main memory empty check status can be read from the EMPTY bit in the FLASH_ACR register. Software can modify the flash main memory empty status by writing to the EMPTY bit.
The internal empty check flag (EMPTY bit in FLASH_ACR) is implemented to allow easy programming of virgin devices by the bootloader. This flag is used when the BOOT0 pin defines the main flash memory as target boot area. When this flag is set, the device is considered as empty and the system memory (bootloader) is selected instead of the main flash memory as a boot area, to allow the user to program the flash memory. Therefore, some of the GPIOs are reconfigured from the high-Z state. Refer to the application note AN2606 for more details concerning the bootloader and GPIO configuration in system memory boot mode. This feature can be disabled by configuring the option bytes to force a boot from the main flash memory (nSWBOOT0 = 0, nBOOT0 = 1).
This empty check flag is updated only during the loading of option bytes: it is set when the content of the address 0x08000 0000 is read as 0xFFFF FFFF, otherwise it is cleared. A power reset or setting of OBL_LAUNCH bit in FLASH_CR is needed to clear this flag after programming of a virgin device to execute user code after a system reset. The EMPTY bit can also directly be written by software.
4.3.3 Error code correction (ECC)
Data in flash memory words are 72-bit wide: eight bits are added per each double-word (64 bits).
The ECC mechanism supports the following modes:
- • one error detection and correction
- • two errors detection
When one error is detected and corrected, the flag ECCC (ECC correction) is set in FLASH_ECCR. If ECCCIE is set, an interrupt is generated.
When two errors are detected, the flag ECCD (ECC detection) is set in FLASH_ECCR. In this case, an NMI is generated.
When an ECC error is detected, the address of the failing double-word is saved in ADDR_ECC[16:0] in FLASH_ECCR. ADDR_ECC[2:0] bits are always cleared. The bus-ID of the CPU accessing the address is saved in CPUID[2:0].
While ECCC or ECCD is set, FLASH_ECCR is not updated if a new ECC error occurs. FLASH_ECCR is updated only when ECC flags are cleared.
Note: For virgin data (0xFF FFFF FFFF FFFF FFFF), one error is detected and corrected, but the two errors detection mode is not supported.
When an ECC error is reported, a new read at the failing address may not generate an ECC error if the data is still present in the current buffer, even if ECCC and ECCD are cleared. If this is not the desired behavior, the user must reset the cache.
4.3.4 Read access latency
To correctly read data from the flash memory, the number of wait states (LATENCY[2:0]) must be correctly programmed in FLASH_ACR according to the frequency of the flash memory clock (HCLK3) and the internal voltage range of the device ( \( V_{CORE} \) ). Refer to Section 6.1.4: Dynamic voltage scaling management .
Table 12 shows the correspondence between wait states and frequency of the memory clock.
Table 12. Number of wait states according to flash clock (HCLK3) frequency
| Wait states (WS) (access) | HCLK3 (MHz) | |
|---|---|---|
| V CORE range 1 | V CORE range 2 | |
| 0 WS (1 HCLK cycle) | ≤ 18 | ≤ 6 |
| 1 WS (2 HCLK cycles) | ≤ 36 | ≤ 12 |
| 2 WS (3 HCLK cycles) | ≤ 48 | ≤ 16 |
After power-on reset and wake-up from Standby, the HCLK3 clock frequency is 4 MHz in range 1 and 0 wait state (WS) is configured in FLASH_ACR.
When changing the frequency of the flash memory clock or the V CORE range, the software sequences detailed below must be applied in order to tune the number of wait states needed to access the flash memory:
Increase the CPU frequency
- 1. Program the new number of wait states to the LATENCY[2:0] bits in FLASH_ACR.
- 2. Check that the new number of wait states is taken into account to access the flash memory by reading back the LATENCY[2:0] bits in FLASH_ACR, and wait until the new programmed number is read.
- 3. Modify the system clock source by writing the SW[1:0] bits in RCC_CFGR.
- 4. If needed, modify the CPU clock prescaler by writing the SHDHPRE[3:0] bits in RCC_EXTCFGR.
- 5. Optionally, check that the new system clock source or/and the new flash memory clock prescaler value is/are taken into account by reading the clock source status (SWS[1:0] bits) in RCC_CFGR, or/and the AHB prescaler value (SHDHHPREF bit) in RCC_EXTCFGR.
Decrease the CPU frequency
- 1. Modify the system clock source by writing the SW[1:0] bits in RCC_CFGR.
- 2. If needed, modify the flash memory clock prescaler by writing the SHDHPRE[3:0] bits in RCC_EXTCFGR.
- 3. Check that the new system clock source or/and the new flash memory clock prescaler value is/are taken into account by reading the clock source status (SWS[1:0] bits) in RCC_CFGR, or/and the AHB prescaler value (SHDHHPREF bit) in RCC_EXTCFGR. Wait until the new programmed system clock source or/and new flash memory clock prescaler value is/are read.
- 4. Program the new number of wait states to the LATENCY[2:0] bits in FLASH_ACR.
- 5. Optionally, check that the new number of wait states is used to access the flash memory by reading back the LATENCY[2:0] bits in FLASH_ACR.
4.3.5 Adaptive real-time memory accelerator (ART Accelerator)
The proprietary adaptive real-time (ART) memory accelerator is optimized for STM32 industry-standard Arm Cortex-M4 with DSP processors. It balances the inherent
performance advantage of the Cortex-M4 with DSP over flash memory technologies, which normally require the processor to wait for the flash memory at higher operating frequencies.
To release the processor full performance, the accelerator implements an instruction prefetch queue and branch cache that increases program execution speed from the 64-bit flash memory. Based on CoreMark® benchmark, the performance achieved thanks to the ART Accelerator is equivalent to 0 wait state program execution from the flash memory at a CPU frequency up to 48 MHz.
Instruction prefetch
The CPU1 fetches the instruction over the ICode bus and the literal pool (constant/data) over the DCode bus. The prefetch block aims at increasing the efficiency of ICode bus accesses.
The CPU2 fetches the instruction and the literal pool (constant/data) over the S-bus. The prefetch block aims at increasing the efficiency of S-bus accesses.
Each flash memory read operation provides 64 bits from either two instructions of 32 bits or four instructions of 16 bits according to the program launched. This 64-bit current instruction line is saved in a current buffer. In case of sequential code, at least two CPU cycles are needed to execute the previous read instruction line. Prefetch on the CPU1 ICode bus or CPU2 S-bus can be used to read the next sequential instruction line from the flash memory while the current instruction line is being requested by the CPU.
Prefetch is enabled by setting PRFTEN in FLASH_ACR for CPU1 or FLASH_C2ACR for CPU2. This feature is useful if at least one wait state is needed to access the flash memory.
The figure below shows the execution of sequential 16-bit instructions with and without prefetch when three wait states are needed to access the flash memory.
Figure 7. Sequential 16 bits instructions execution
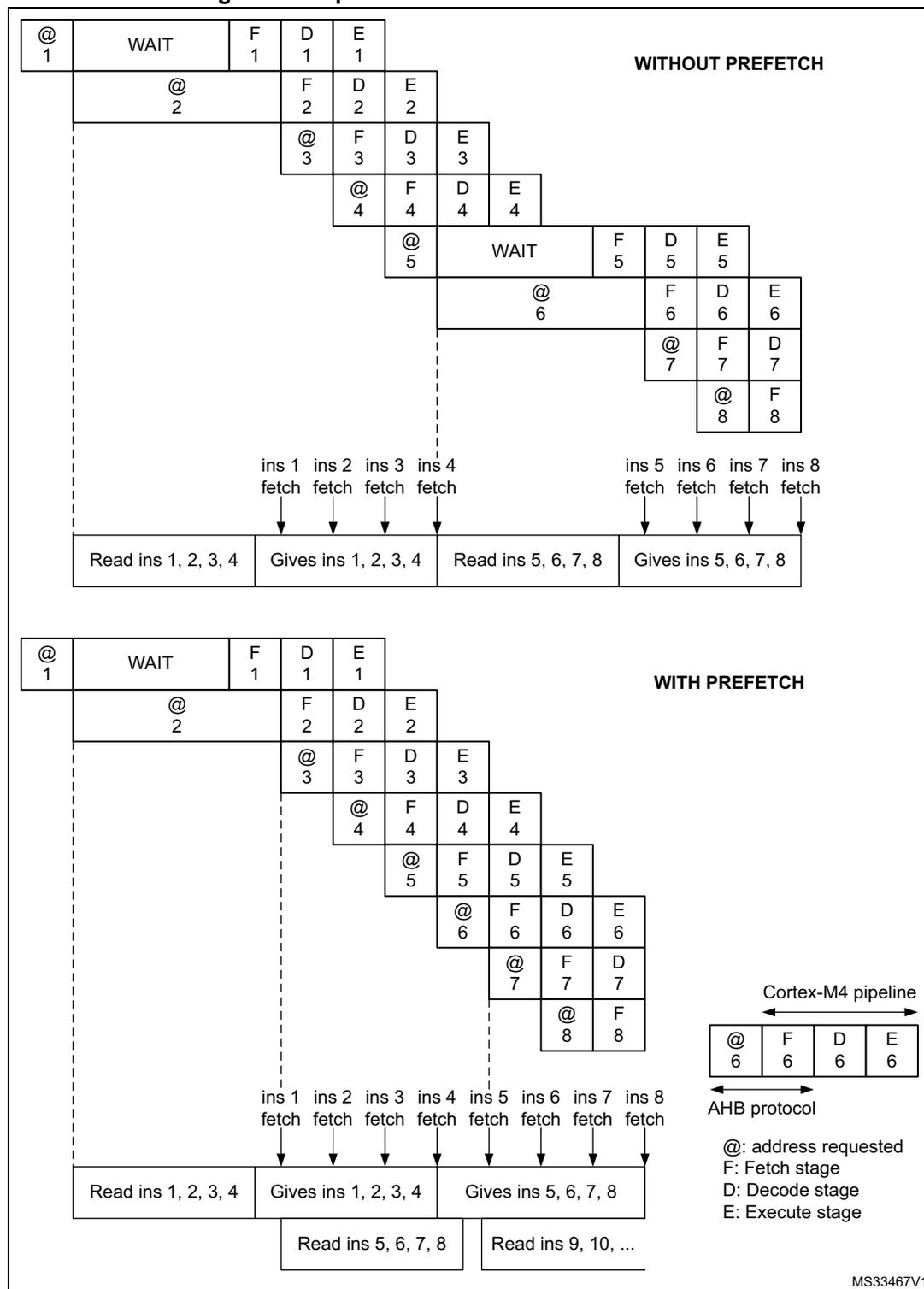
WITHOUT PREFETCH
| @ 1 | WAIT | F 1 | D 1 | E 1 | ||||
| @ 2 | F 2 | D 2 | E 2 | |||||
| @ 3 | F 3 | D 3 | E 3 | |||||
| @ 4 | F 4 | D 4 | E 4 | |||||
| @ 5 | WAIT | F 5 | D 5 | E 5 | ||||
| @ 6 | F 6 | D 6 | E 6 | |||||
| @ 7 | F 7 | D 7 | ||||||
| @ 8 | F 8 | |||||||
ins 1 ins 2 ins 3 ins 4 ins 5 ins 6 ins 7 ins 8
fetch fetch fetch fetch fetch fetch fetch fetch
Read ins 1, 2, 3, 4 | Gives ins 1, 2, 3, 4 | Read ins 5, 6, 7, 8 | Gives ins 5, 6, 7, 8
WITH PREFETCH
| @ 1 | WAIT | F 1 | D 1 | E 1 | ||||
| @ 2 | F 2 | D 2 | E 2 | |||||
| @ 3 | F 3 | D 3 | E 3 | |||||
| @ 4 | F 4 | D 4 | E 4 | |||||
| @ 5 | F 5 | D 5 | E 5 | |||||
| @ 6 | F 6 | D 6 | E 6 | |||||
| @ 7 | F 7 | D 7 | ||||||
| @ 8 | F 8 | |||||||
ins 1 ins 2 ins 3 ins 4 ins 5 ins 6 ins 7 ins 8
fetch fetch fetch fetch fetch fetch fetch fetch
Read ins 1, 2, 3, 4 | Gives ins 1, 2, 3, 4 | Gives ins 5, 6, 7, 8
Read ins 5, 6, 7, 8 | Read ins 9, 10, ...
Cortex-M4 pipeline
| @ 6 | F 6 | D 6 | E 6 |
AHB protocol
@: address requested
F: Fetch stage
D: Decode stage
E: Execute stage
MS33467V1
When the code is not sequential (branch), the instruction may not be present in the currently used instruction line or in the prefetched instruction line. In this case (miss), the penalty in terms of number of cycles is at least equal to the number of wait states.
If a loop is present in the current buffer, no new access is performed.
CPU1 instruction cache memory (I-Cache)
To limit the CPU1 time lost due to jumps, it is possible to retain 32 lines of 4 x 64 bits (1 Kbyte) in an instruction cache memory. This feature is enabled for the CPU1 by setting the instruction cache enable (ICEN) bit in FLASH_ACR. Each time a miss occurs (requested data not present in the currently used instruction line, in the prefetched instruction line or in the instruction cache memory), the line read is copied into the instruction cache memory. If some data contained in the instruction cache memory are requested by the CPU1, they are provided without inserting any delay. Once all the instruction cache memory lines have been filled, the LRU (least recently used) policy is used to determine the line to replace in the instruction memory cache. This feature is particularly useful in case of code containing loops.
The instruction cache memory is enabled after system reset.
CPU1 data cache memory (D-Cache)
CPU1 literal pools are fetched from the flash memory through the DCode bus during the execution stage of the CPU1 pipeline. Each CPU1 DCode bus read access fetches 64 bits that are saved in a current buffer. The CPU1 pipeline is consequently stalled until the requested literal pool is provided. To limit the time lost due to literal pools, accesses through the AHB data bus DCode have priority over accesses through the AHB instruction bus ICode.
If some literal pools are frequently used, the CPU1 data cache memory can be enabled by setting the data cache enable (DCEN) bit in FLASH_ACR. This feature works like the instruction cache memory but the retained data size is limited to eight lines of 4 x 64 bits (256 bytes).
The data cache memory is enabled after system reset.
Note: The D-Cache is active only when data is requested by the CPU1 (not by DMAs). Data in option bytes block are not cacheable.
CPU2 cache memory (S-bus)
To limit the CPU2 time lost due to jumps, it is possible to retain four lines of 64 bits (32 bytes) in an instruction cache memory. This feature can be enabled for the CPU2 by setting the instruction cache enable (ICEN) bit in FLASH_C2ACR. Each time a miss occurs (requested data not present in the currently used instruction line, in the prefetched instruction line or in the instruction cache memory), the line read is copied into the instruction cache memory. If some data contained in the instruction cache memory are requested by the CPU2, they are provided without inserting any delay. Once all the instruction cache memory lines have been filled, the LRU (least recently used) policy is used to determine the line to replace in the instruction memory cache. This feature is particularly useful in case of code containing loops.
The instruction cache memory is enabled after system reset.
CPU2 literal pools are fetched from the flash memory through the S-bus during the execution stage of the CPU2 pipeline. Each CPU2 S-bus read access fetches 64 bits that
are saved in a current buffer. The CPU2 pipeline is consequently stalled until the requested literal pool is provided.
No data cache is available on CPU2.
4.3.6 Flash program and erase operations
The embedded flash memory can be programmed using in-circuit programming or in-application programming.
The in-circuit programming (ICP) method is used to update the entire contents of the flash memory using the JTAG, SWD protocol or the supported interfaces by the system bootloader, to load the user application for CPU1 and CPU2, into the microcontroller. ICP offers quick and efficient design iterations and eliminates unnecessary package handling or socketing of devices.
In contrast to the ICP method, in-application programming (IAP) can use any communication interface supported by the microcontroller (such as I/Os, UART, I 2 C or SPI) to download programming data into memory. IAP allows the user to re-program the flash memory while the application is running. Nevertheless, part of the application must have been previously programmed in the flash memory using ICP.
The contents of the flash memory are not guaranteed if a device reset occurs during a flash memory operation.
During a program/erase operation to the flash memory, any attempt to read the memory stalls the bus. The read operation proceeds correctly once the program/erase operation is completed.
Note: In a multi CPU system, it is good practice to use semaphores to manage flash program and erase operations, and prevent simultaneous operations by the CPUs.
Secure flash programming
When the system is secure (ESE=1), the secure CPU2 application can only be programmed by in-circuit programming (ICP) using SFI/RSS or in-application programming (IAP) running on the secure CPU2. Only the secure CPU2 is able to download programming data into secure part of the memory. Secure IAP allows the user to re-program the flash memory while the application is running. Nevertheless, part of the application must have been previously programmed in the flash memory using ICP.
Unlocking the flash memory
After a reset, write is not allowed in FLASH_CR or FLASH_C2CR to protect the flash memory against possible unwanted operations (for example, electric disturbances).
The following sequence is used to unlock these registers:
- 1. Write KEY1 = 0x4567 0123 in FLASH_KEYR.
- 2. Write KEY2 = 0xCDEF 89AB in FLASH_KEYR.
Any wrong sequence locks up FLASH_CR and FLASH_C2CR until the next system reset. In the case of a wrong key sequence, a bus error is detected and a hard fault interrupt is generated.
FLASH_CR and FLASH_C2CR can be locked again by software by setting their respective LOCK bit.
Note: FLASH_CR and FLASH_C2CR cannot be written when BSY is set respectively in FLASH_SR or FLASH_C2SR. Any attempt to write to these registers with BSY set causes the AHB bus to stall until BSY is cleared.
4.3.7 Flash main memory erase sequences
Erase can be performed by page (page erase) or on the whole memory (mass erase). Mass erase does not affect the information block (system flash memory, OTP, and option bytes).
Flash memory page erase
The CPU1 is only able to page erase the non-secure part of the user flash memory.
The secure CPU2 is able to page erase both the secure and non-secure parts of the user flash memory.
A page erase only starts when allowed by PESD in FLASH_SR and FLASH_C2SR.
When a page is protected by PCROP or WRP, it is not erased. Hide protection area and hide protection area disable provide no protection for erase. A hide protection area when not protected by PCROP or WRP, can be erased.
Table 13. Page erase overview
| Page | PCROP | WRP | PCROP_RDP | Comment | WRPERR | CPU1 bus error | CPU2 bus error | Illegal access event |
|---|---|---|---|---|---|---|---|---|
| Non-secure | No | No | x | Page is erased | No | No | No | No |
| No | Yes | |||||||
| Yes | No | Page erase aborted (no page erase started) | Yes | |||||
| Yes | Yes | |||||||
| Secure | No | No | x | Requested by CPU2. Secure page is erased. | No | N/A | No | Yes (1) |
| Requested by CPU1. Secure page erase is aborted (no secure page erase started) | No | N/A | ||||||
| No | Yes | |||||||
| Yes | No | Page erase aborted (no page erase started) | Yes (2) | No | No | |||
| Yes | Yes |
1. When PER requested by the non-secure CPU1.
2. When requested by a secure bus master. When requested by a non-secure bus master, no WRPERR is generated and an illegal access event is generated instead.
To erase a 2-Kbyte page, follow the steps detailed below:
- 1. Check that no flash memory operation is ongoing by checking BSY in FLASH_SR or FLASH_C2SR.
- 2. Check that flash program and erase operation is allowed by checking PESD in FLASH_SR or FLASH_C2SR (these checks are recommended even if status may change due to flash operation requests by the other CPU, to limit the risk of receiving a bus error when starting page erase).
- 3. Check and clear all error programming flags due to a previous programming. If not, PGSERR is set.
- 4. Set PER and select the page to erase (PNB[6:0]) in FLASH_CR or FLASH_C2CR.
- 5. Set STRT in FLASH_CR or FLASH_C2CR.
- 6. Wait for BSY to be cleared in FLASH_SR or FLASH_C2SR.
Note: The internal oscillator HSI16 (16 MHz) is enabled automatically when the STRT bit is set, and disabled automatically when the STRT bit is cleared, except if the HSI16 is previously enabled with HSION in the RCC_CR register.
Flash mass erase
A user flash memory mass erase requested by the CPU1 is only performed when the system is non-secure (ESE = 0). When the system is secure (ESE = 1), a flash memory mass erase by the CPU1 is ignored and an illegal access event is generated.
When PCROP or WRP is enabled, any flash memory mass erase is aborted and no erase started.
Hide protection area and hide protection area disable provide no protection for mass erase.
Table 14. Mass erase overview
| ESE | PCROP | WRP | PCROP_RDP | Comment | WRPERR | CPU1 bus error | CPU2 bus error | Illegal access event |
|---|---|---|---|---|---|---|---|---|
| 0 | No | No | x | Memory is erased | No | No | No | No |
| No | Yes | Erase aborted (no erase started) | Yes | |||||
| Yes | No | |||||||
| Yes | Yes | |||||||
| 1 | No | No | x | Requested by secure CPU2. The flash memory is mass erased. | No | N/A | No | Yes (1) |
| Requested by CPU1. Mass erase aborted (no erase started) | No | N/A | ||||||
| No | Yes | Erase aborted (no erase started) | Yes (2) | No | No | |||
| Yes | No | |||||||
| Yes | Yes | |||||||
1. When MER requested by the non-secure CPU1.
2. When requested by a secure bus master. When requested by a non-secure bus master, no WRPERR is generated and an illegal access event is generated instead.
To perform a mass erase, follow the steps detailed below:
- 1. Check that no flash memory operation is ongoing by checking BSY in FLASH_SR or FLASH_C2SR.
- 2. Check and clear all error programming flags due to a previous programming. If not, PGSERR is set.
- 3. Set MER in FLASH_CR or FLASH_C2CR.
- 4. Set STRT in FLASH_CR or FLASH_C2CR.
- 5. Wait for BSY to be cleared in FLASH_SR or FLASH_C2SR.
Note: The internal oscillator HSI16 (16 MHz) is enabled automatically when the STRT bit is set, and disabled automatically when the STRT bit is cleared, except if the HSI16 is previously enabled with HSION in the RCC_CR register.
4.3.8 Flash main memory programming sequences
The flash memory is programmed with 72 bits at a time (a double-word of 64 bits plus 8 bits ECC).
Programming in a previously programmed double-word is only allowed when programming an all 0 value. It is not allowed to program any other value in a previously programmed double-word. Any attempt sets PROGERR flag in FLASH_SR or FLASH_C2SR, except when programming an already programmed double-word with an all 0 value.
It is only possible to program a double-word (2 x 32-bit data), otherwise:
- • Any attempt to write a byte (8 bits) or half-word (16 bits) sets SIZERR in FLASH_SR or FLASH_C2SR.
- • Any attempt to write a double-word that is not aligned with a double-word address sets the PGAERR flag in FLASH_SR or FLASH_C2SR.
When the system is secure (ESE = 1), only the secure CPU2 is able to download programming data into the secure part of the memory. When the system is secure (ESE = 1), a flash memory programming by the CPU1 in the secure flash memory area is ignored and an illegal access event is generated. Also unprivileged programming of a privileged location is ignored.
When access rights between programming two word address is changed, the double-word programming fails and the flags controller is blocked in the programming sequence (no error flags are set). A system reset is needed to overcome this situation.
Note: For correct operation, the firmware must guarantee that the flash page access protection is not changed during the programming sequence.
Standard programming
The flash memory programming sequence in standard mode is as follows:
- 1. Check that no flash main memory operation is ongoing by checking BSY in FLASH_SR or FLASH_C2SR.
- 2. Check that flash program and erase operation is allowed by checking PESD in FLASH_SR or FLASH_C2SR (these checks are recommended even if status may change due to flash operation requests by the other CPU, to limit the risk of receiving a bus error when starting programming).
- 3. Check and clear all error programming flags due to a previous programming. If not, PGSERR is set.
- 4. Set PG in FLASH_CR or FLASH_C2CR.
- 5. Perform the data write operation at the desired memory address, inside the main memory block or OTP area. Only double-word (64 bits) can be programmed.
- a) Write a first word in an address aligned with double-word
- b) Write the second word (see the note below)
Note: When the flash memory interface received a good sequence (a double-word), programming is automatically launched and the BSY bit is set. The internal oscillator HSI16 (16 MHz) is enabled automatically when the PG bit is set, and disabled automatically when the PG bit is cleared, except if the HSI16 is previously enabled with HSION in the RCC_CR register.
If the user needs to program only one word, double-word must be completed with the erase value 0xFFFF FFFF to launch automatically the programming.
ECC is calculated from the double-word to program.
For correct operation, the firmware must guarantee that the flash page access protection is not changed during the programming sequence. This is between the first and second word write.
- 6. Wait until BSY is cleared in FLASH_SR or FLASH_C2SR.
- 7. Check that EOP is set in FLASH_SR or FLASH_C2SR (meaning the programming operation succeeded), and clear it by software.
- 8. Clear PG in FLASH_SR or FLASH_C2SR if there no more programming request.
Fast programming
This mode allows a row to be programmed, 32 double-words (256 bytes), and the page programming time to be reduced by eliminating the need for verifying the flash memory locations before they are programmed and to avoid rising and falling time of high voltage for each double-word. During fast programming, the flash clock frequency (HCLK3) must be at least 8 MHz.
Fast row programming must be performed by executing firmware from SRAM and disabling interrupts when not relocating the CPU interrupt vector table. A read access form the CPU requesting row programming causes a bus error. A read from any other source (such as the other CPU or DMA) is stalled until the row programming is finished (standard double-word programming does not cause a bus error to the requesting CPU but stalls any read until standard programming is finished).
Only the main memory can be programmed in Fast programming mode.
The flash main memory programming sequence in Fast programming mode is described below:
- 1. Perform a mass erase. If not, PGSERR is set.
- 2. Check that no flash main memory operation is ongoing by checking BSY bit FLASH_SR or FLASH_C2SR.
- 3. Check that flash memory program and erase operation is allowed by checking PESD in FLASH_SR or FLASH_C2SR (these checks are recommended even if status may change due to flash operation requests by the other CPU, to limit the risk of receiving a bus error when starting programming).
- 4. Check and clear all error programming flag due to a previous programming.
- 5. Set FSTPG in FLASH_CR or FLASH_C2CR.
- 6. Write the 32 double-words to program a row (256 bytes).
- 7. Wait until BSY is cleared in FLASH_SR or FLASH_C2SR.
- 8. Check that the EOP flag is set in FLASH_SR or FLASH_C2SR (meaning the programming operation succeeded), and clear it by software.
- 9. Clear FSTPG in FLASH_SR or FLASH_C2SR if there are no more programming requests.
Note: For correct operation, the firmware must guarantee that the flash page access protection is not changed during the fast programming sequence. This is between any of the 32 word writes.
Note: When attempting to write in Fast programming mode while a read operation is ongoing, the programming is aborted without any system notification (no error flag is set).
When the flash memory interface receives the first double-word, programming is automatically launched. The BSY bit is set when the high voltage is applied for the first double-word, and it is cleared when the last double-word is programmed or in case of error. The internal oscillator HSI16 (16 MHz) is enabled automatically when FSTPG is set, and disabled automatically when the FSTPG bit is cleared, except if the HSI16 is previously enabled with HSION in the RCC_CR register.
The 32 double-word must be written successively. The high voltage is kept on the flash memory for all the programming. Maximum time between two double-words write requests is the time programming (~ 20 µs). If a second double-word arrives after this time programming, fast programming is interrupted and MISSERR is set.
High voltage must not exceed 8 ms for a full row between two erases. This is guaranteed by the sequence of 32 double-words successively written with a clock system greater or equal to 8 MHz. An internal time-out counter counts 7 ms when Fast programming is set and stops the programming when time-out is over. In this case FASTERR is set.
If an error occurs, high voltage is stopped and next double-word to programmed is not programmed. Anyway, all previous double-words have been properly programmed.
Programming errors signaled by flags
Several kind of errors can be detected. In case of error, the flash operation (programming or erasing) is aborted.
- • PROGERR: programming error
In standard programming, PROGERR is set if the word to write, with a different value than all zero, is not previously erased (except if the value to program is all zero).
If any other error occurs (such as SIZERR, PAGERR, PGSERR, WRPERR), PROGRERR may not be set even if there is a word re-programming without erase error.
- • SIZERR: size programming error
In standard programming or in fast programming: only double-word can be programmed and only 32-bit data can be written. SIZERR is set if a byte or an half-word is written.
- • PGAERR: alignment programming error
PGAERR is set if one of the following conditions occurs:
- – In standard programming, the first word to be programmed is not aligned with a double-word address, or the second word does not belong to the same double-word address.
- – In fast programming, the data to program does not belong to the same row than the previous programmed double-words, or the address to program is not greater than the previous one.
Alignment programming errors are individually checked per CPU. No checks are available for simultaneous multi CPU programming. HSEM or other firmware mechanisms must be used to prevent simultaneous multi CPU programming.
- • PGSERR: programming sequence error
PGSERR is set if one of the following conditions occurs:
- – In the standard programming sequence or the fast programming sequence, a data is written when PG and FSTPG are cleared.
- – In the standard programming sequence or the fast programming sequence, MER and PER are not cleared when PG or FSTPG is set.
- – In the fast programming sequence, the mass erase is not performed before setting the FSTPG bit.
- – In the mass erase sequence, PG, FSTPG, and PER are not cleared when MER is set, when the security of the flash allows a mass erase. A non-secure mass erase request on a secure flash memory does not set a PGSERR. An illegal access event is generated instead.
- – In the page erase sequence, PG, FSTPG and MER are not cleared when PER is set, when the security of the page allows access. When the security of this page does not allow access, no PGSERR is set but an illegal access event is generated instead.
- – PGSERR is set also if PROGERR, SIZERR, PGAERR, WRPERR, MISSERR, FASTERR or PGSERR is set due to a previous programming error.
- – In the fast programming sequence, if the page containing the row to be programmed has not been erased by the last page erase action (If a mass erase has been done, it is allowed to program rows on higher order pages but not on lower order)
- • WRPERR: write protection error
WRPERR is set if one of the following conditions occurs:
- – Attempt to program or erase in a write protected area (WRP) or in a PCROP area, when the security of the area allows access. When the security of this area does not allow access, no WRPERR is set but an illegal access event is generated instead.
- – Attempt to perform a mass erase when one page or more is protected by WRP or PCROP, when the security of the flash allows a mass erase. A non-secure mass erase request on a secure flash memory does not set a WRPERR. An illegal access event is generated instead.
- – The debug features are connected or the boot is executed from SRAM or from system flash memory when the readout protection (RDP) is set to level 1.
- – Attempt to modify the option bytes when the readout protection (RDP) is set to Level 2, except when requested by the secure CPU2.
- • MISSERR: fast programming data miss error
In fast programming, all the data must be written successively. MISSERR is set if the previous data programming is finished and the next data to program is not written yet.
- • FASTERR: fast programming error
In fast programming, FASTERR is set if one of the following conditions occurs:
- – When FSTPG bit is set for more than 7 µs (generating a time-out detection).
- – When the row fast programming is interrupted by a MISSERR, PGAERR, WRPERR or SIZERR.
If an error occurs during a program or erase operation, one of the following error flags is set in FLASH_SR and FLASH_C2SR:
- • PROGERR, SIZERR, PGAERR, PGSERR, MISSERR (program error flags)
- • WRPERR (protection error flag)
In this case, if the error interrupt enable bit ERRIE is set in FLASH_CR or FLASH_C2CR, an interrupt is generated and the operation error flag OPERR is set in FLASH_SR and FLASH_C2SR.
Note: If several successive errors are detected (for example, in case of DMA transfer to the flash memory), the error flags cannot be cleared until the end of the successive write request.
PGSERR and PGAERR in a page-based row programming
In case of fast programming, the table below describes how PGAERR and PGSERR are handled.
Table 15. Errors in page-based row programming
| Last page/row | Current page/row | MER active | PPER active |
|---|---|---|---|
| page [x]/row [y] | page [x] / row [x-n] | PGAERR | PGAERR |
| page [x-n] / row [any] | PGAERR & PGSERR | PGAERR & PGSERR | |
| page [x+n] / row [any] | No error | PGSERR |
After a system reset, no MER or PER is performed. Any programming attempt causes a PGAERR and a PGSERR.
Programming errors causing a bus error
The error conditions listed below do not generate an error flag but a bus error instead:
- • AHB write to any page when RDP level 1 and boot is performed from the system flash memory or SRAM1
- • AHB write when the flash memory is powered down
- • Read or write from the flash memory through the debugger
- • Read from the flash memory when fast row programming is ongoing, for the source which requested the fast row programming
- • New programming request when the previous one is not finished
- • FLASH_CR register write between the two accesses of a double-word programming
- • FLASH_CR register write when PESD is active (set)
- • Write a wrong key in FLASH_KEYR or FLASH_OPTKEYR register
- • Any subsequent write to FLASH_KEYR or FLASH_OPTKEYR after unlocking the respective feature
Programming and caches
If a flash memory write access impacts data in the data cache, the flash memory write access modifies the data in the memory and in the cache.
If an erase operation in the flash memory also concerns data in the data cache or instruction cache, the user must ensure that these data are rewritten before they are accessed during code execution. Upon an erase operation, the cache content is invalidated.
Note: The ICACHE and DCACHE must be flushed only when disabled (ICEN or DCEN = 0).
4.4 FLASH option bytes
4.4.1 Option bytes description
The option bytes can be read from the memory locations listed in the table below or from the following option byte registers:
- • FLASH option register (FLASH_OPTR)
- • FLASH PCROP zone A start address register (FLASH_PCROP1ASR)
- • FLASH PCROP zone A end address register (FLASH_PCROP1AER)
- • FLASH PCROP zone B start address register (FLASH_PCROP1BSR)
- • FLASH PCROP zone B end address register (FLASH_PCROP1BER)
- • FLASH WRP area A address register (FLASH_WRP1AR)
- • FLASH WRP area B address register (FLASH_WRP1BR)
- • FLASH IPCC mailbox data buffer address register (FLASH_IPCCBR)
- • FLASH CPU2 access control register (FLASH_C2ACR)
- • FLASH secure SRAM start address and CPU2 reset vector register (FLASH_SRRVR)
Table 16. Option bytes organization
| Address (1) | 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 | 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 | |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0x1FFF 7800 | C2BOOT LOCK | BOOT LOCK | Res. | Res. | nBOOT0 | nSWBOOT0 | SRAM_RST | SRAM2PAR | nBOOT1 | Res. | Res. | Res. | WWDG_SW | IWDG_STDBY | IWDG_STOP | IWDG_SW | Res. | nRST_SHDW | nRST_STDBY | nRST_STOP | BOR_1EV[2:0] | ESE | RDP[7:0] | ||||||||||
| 0x1FFF 7808 | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PCROP1A_STRT[7:0] | ||||||||
| 0x1FFF 7810 | PCROP_RDP | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PCROP1A_END[7:0] | ||||||||
| 0x1FFF 7818 | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WRP1A_END[6:0] | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WRP1A_STRT[6:0] | ||||||||||||
| 0x1FFF 7820 | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WRP1B_END[6:0] | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WRP1B_STRT[6:0] | ||||||||||||
| 0x1FFF 7828 | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PCROP1B_STRT[7:0] | ||||||||
| 0x1FFF 7830 | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PCROP1B_END[7:0] | ||||||||
| 0x1FFF 7838 to 0x1FFF 7860 | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 0x1FFF 7868 | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | IPCCDBA[13:0] | ||||||||||||||
Table 16. Option bytes organization (continued)
| Address (1) | 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 | 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0x1FFF 7870 | SUBGHZSPISD | Res. | Res. | Res. | Res. | Res. | Res. | Res. | HDPAD | HDPSA[6:0] | Res. | Res. | Res. | DDS | Res. | Res. | Res. | Res. | FSD | SFSA[6:0] | ||||||||||||
| 0x1FFF 7878 | C2OPT | NBRSD | SNBRSA[4:0] | Res. | BRSD | SBRSA[4:0] | Res. | Res. | SBRV[15:0] | |||||||||||||||||||||||
| 0x1FFF 7FF8 | OPTVAL[31:0] | |||||||||||||||||||||||||||||||
1. The upper 32 bits of the double-word address contain the inverted data from the lower 32 bits.
4.4.2 Option bytes programming
After a reset, the options related bits in FLASH_CR and FLASH_C2CR are write-protected. To run any operation on the option bytes page, the option lock bit OPTLOCK in FLASH_CR must be cleared.
The following sequence is used to unlock the FLASH_CR and flash memory option registers:
- 1. Unlock FLASH_CR with the LOCK clearing sequence (refer to Unlocking the flash memory ).
- 2. Write OPTKEY1 = 0x0819 2A3B in FLASH_OPTKEYR
- 3. Write OPTKEY2 = 0x4C5D 6E7F in FLASH_OPTKEYR
Any wrong sequence locks up the flash option register until the next system reset. In the case of a wrong key sequence, a bus error is detected and a hard fault interrupt is generated.
The user options can be protected against unwanted erase/program operations by setting the OPTLOCK bit by software.
Note: If LOCK is set by software, OPTLOCK is automatically set as well.
Note: In a multi-CPU system, it is good practice to use semaphores to manage option programming and prevent simultaneous option programming by the CPUs.
Modify user options
The option bytes are programmed differently from a main memory user address.
To modify the user options value, follow the procedure below:
- 1. Clear OPTLOCK option lock bit with the clearing sequence described above
- 2. Write the desired options value in the options registers.
- 3. Check that no flash memory operation is ongoing by checking the BSY bit in FLASH_SR or FLASH_C2SR.
- 4. Check that flash program and erase operation is allowed by checking the PESD bit in FLASH_SR or FLASH_C2SR (these checks are recommended even if status may change due to flash operation requests by the other CPU, to limit the risk of receiving a bus error when modifying user options).
- 5. Set the options start bit OPTSTRT in FLASH_CR.
- 6. Wait for the BSY bit to be cleared.
Note: Any modification of the value of one option is automatically performed by erasing user option bytes pages first, and then programming all the option bytes with the values contained in the flash option registers.
Warning: On RDP regression from level 1 to level 0, starting the option programming by the OPTSTRT bit causes the flash memory, SRAM1 and SRAM2 to be erased. All device software in all memories is erased. A subsequent OBL_LAUNCH must be started by an external tool or a POR must be performed to restart the device and reload the options.
Secure user options
When the system is secure (ESE = 1), the secure option bytes flash in FLASH_C2ACR and FLASH_SRRVR can only be written by the secure CPU2.
Option byte loading
After the BSY bit is cleared, all new options are updated into the flash memory but not applied to the system. A read from the option registers still returns the last loaded option byte values. The new options have effect on the system only after they are loaded.
Option bytes loading is performed in the following two cases:
- • when OBL_LAUNCH bit is set in FLASH_CR
- • after a power reset (BOR reset or exit from Standby/Shutdown modes)
Option byte loader performs a read of the options block and stores the data into internal option registers. These internal registers configure the system and can be read by software. Setting OBL_LAUNCH generates a reset so the option byte loading is performed under system reset.
Each option bit has also its complement in the same double-word. During option loading, a verification of the option bit and its complement allows the correct loading to be checked.
During option byte loading, the options are read by double-word. ECC on option words is not taken into account during OBL but only during direct software read of option area.
If the word and its complement are matching, the option word/byte is copied into the option register.
If the comparison between the word and its complement fails, a status bit OPTVERR is set. Mismatch values are forced into the option registers as follows:
- • For USR OPT option, the value of mismatch is all options at '1', except for BOR_LEV that is "000" (lowest threshold).
- • For WRP option, the value of mismatch is the default value "No protection".
- • For RDP option, the value of mismatch is the default value "Level 1".
- • For PCROP, the value of mismatch is "all memory protected".
- • For CxBOOT_LOCK option, the value of mismatch is "CPU1 boot lock disabled", "CPU2 boot lock disabled".
- • For FSD and SFSA option, the value of mismatch is “flash memory completely secured”.
- • For BRSD, SBRSA and NBRSD, SNBRASA options, the value of mismatch is none secured (memories are erased).
- • For DDS option, the value of mismatch is “CPU2 debug disabled”.
- • For C2OPT and SBRV options, the value of mismatch is “CPU2 boot from start address of last flash page”.
- • For HDPAD and HDPSA options, the value on mismatch is “Complete flash memory hide protected”.
- • For SUBGHSPISD option, the value of mismatch is “sub-GHz radio SPI secure”.
- • For OPTVAL option, the value of mismatch is “not valid”. OPTVAL is a check word programmed at the last user option address. It is used to check if all user options have been programmed during an OPTSTART. If the user option program sequence has not terminated completely, OPTVAL is not be programmed and OPTNV is set.
If the OPTVAL option indicates “not valid”, the flash memory is secured and fully hide protected, SRAM1, SRAM2, and PKA SRAM memories are erased, CPU2 debug is disabled, sub-GHz radio SPI is secured.
Table 17. Option loading control
| OPTVERR | OPTNV | Description |
|---|---|---|
| 0 | 0 | Options correctly loaded and OPTVAL is “Valid”. Security is applied according to options. |
| 0 | 1 | Does not occur |
| 1 | 0 | OPTVAL option is correctly loaded as “Valid” but some or all other options and engineering bits are corrupted: mismatch values are loaded. – When secure option is loaded correctly, security is applied according to the loaded secure option values. – When secure option is corrupted, security is applied on the full memory as indicated by the loaded mismatch value. |
| 1 | 1 | Some or all options and engineering bits are corrupted: mismatch values are loaded. OPTVAL is correctly loaded as “not Valid”. Security applied on full memories irrespective of the loaded secure option values. |
On system reset rising, internal option registers are copied into the following option registers that can be read and written by software:
- • FLASH_OPTR
- • FLASH_PCROP1xSR (x = A or B)
- • FLASH_PCROP1xER (x = A or B)
- • FLASH_WRP1xR (x = A or B)
- • FLASH_IPCCDBA
- • FLASH_SFR
- • FLASH_SRRVR
These registers are also used to modify the options. If these registers are not modified by the user, they reflect the options states of the system. See Modify user options for more details.
4.4.3 Sub-GHz radio SPI security
When the system is secure (ESE = 1), the access to the sub-GHz radio SPI interface for the radio system can be made secure by the user option SUBGHSPISD. When secure, only the secure CPU2 has access to the sub-GHz radio SPI.
Access can be further restricted to secure privileged access only by the PRIV2 bit for sub-GHz radio SPI in GTZC TZSC privileged configuration register (GTZC_TZSC_PRIVCFG1) .
4.5 Secure system memory
4.5.1 Introduction
The secure system memory stores RSS (root secure services) firmware that is programmed by ST during STM32WL5x production. The RSS provides secure services to the bootloader and the user firmware.
4.5.2 RSSLIB functions
The RSS provides runtime services thanks to the RSS library. As other microcontroller peripheral features and mapping, the RSS library functions are exposed to user within the CMSIS device header file provided by the STM32CubeWL firmware package. Refer to the user manual Getting started with STM32CubeWL for STM32WL Series (UM2643) for more details.
RSS library functions (named RSSLIB functions hereafter) are described in the CMSIS and can only be called by Cortex-M0+ firmware.
These functions are located at the address RSSLIB_PFUNC. RSSLIBPFUNC is used to call the function (see example below).
CloseExitHDP
Prototype:
uint32_t CloseExitHDP(uint32_t HdpArea, uint32_t VectorTableAddr)
Arguments:
- • HdpArea: Input parameter, bitfield that identifies which HDP area to close. Values can be: RSSLIB_HDP_AREA1
- • VectorTableAddr: Input parameter, address of the next vector table to apply. The vector table format is the one used by the Cortex-M0+ core.
Description:
The user calls
CloseExitHDP()
to close flash HDP secure memory area and to jump to the reset handler embedded within the vector table, which address is passed as input parameter. On successful execution, the function does not return and does not push LR onto the stack. In case of failure (bad input parameter value), this function returns RSSLIB_ERROR.
Example:
Call
CloseExitHDP()
function that closes HDP area and jumps to vector table located at address 0x8020000.
RSSLIB_PFUNC->CloseExitHDP(RSSLIB_HDP_AREA1, 0x8020000);
4.6 Flash memory protection
The main flash memory can be protected against external accesses with the readout protection (RDP). The pages can also be protected against unwanted write (WRP) due to loss of program counter context. The write protection WRP granularity is 2 Kbytes.
Apart from the RDP and WRP, the flash memory can also be protected against read and write from third parties (PCROP). The PCROP granularity is 1 Kbyte.
Part of the flash main memory can be secured, granting exclusive access to this part of the memory to CPU2.
4.6.1 Readout protection (RDP)
The readout protection is activated by setting the RDP option byte and performing an option byte programming with OPTSTRT followed by a OBL_LAUNCH, POR or wake-up from Standby or Shutdown mode. The readout protection protects the main flash memory, the option bytes, the backup registers (TAMP_BKPxR in TAMP) and SRAM2.
There is no exception while the debugger is connected.
There are three levels of readout protection from no protection (level 0) to maximum protection or no debug (level 2).
The flash memory is protected when the RDP option byte and its complement contain the pair of values shown in the table below.
Table 18. Flash memory readout protection status
| RDP byte value | RDP complement value | RDP level |
|---|---|---|
| 0xAA | 0x55 | Level 0 |
| Any value except 0xAA or 0xCC | Any value (not necessarily complementary), except 0x55 and 0x33 | Level 1 (default) |
| 0xCC | 0x33 | Level 2 |
The system memory area is read accessible whatever the protection level. It is never accessible for program/erase operation.
Level 0: no protection
Read, program and erase operations into the main flash memory area are possible. The option bytes, SRAM2 and backup registers are also accessible by all operations.
Level 1: readout protection
This is the default protection level when the RDP option byte is erased. It is defined as well when the RDP value is at any value different from 0xAA and 0xCC, or even if the complement is not correct.
- • User mode
The code executing in user mode (Boot flash) can access the main flash memory, option bytes, SRAM2 and backup registers with all operations.
- • Debug, boot RAM and bootloader and SFI/RSS modes
In debug mode or when the code is running from boot RAM or bootloader or SFI/RSS, the main flash memory, backup registers (RTC_BKPxR in the RTC) and SRAM2 are totally inaccessible. In these modes, a read or write access to the flash memory generates a bus error and a hard fault interrupt.
Caution: In case the level 1 is configured and no PCROP areas are defined, it is mandatory to set PCROP_RDP bit to 1 (full mass erase when the RDP level is decreased from level 1 to level 0). In case the level 1 is configured and a PCROP area is defined, if the user code needs to be protected by RDP but not by PCROP, it must not be placed in a page containing a PCROP area.
Level 2: no debug
In this level, the protection level 1 is guaranteed. In addition, the CPU1 and CPU2 debug port, the boot from RAM (boot RAM mode) and the boot from system memory (bootloader mode) are no more available. Boot in SFI/RSS mode is still possible. When not needed, this can be disabled by locking CPU2 boot in C2BOOT_LOCK. In user execution mode (boot FLASH mode), all operations are allowed on the main flash memory. On the contrary, only read and secure write operations can be performed on the option bytes. Option bytes, can only be programmed and erased by a secure CPU2.
When the system is non-secure (ESE = 0), the level 2 cannot be removed at all. It is an irreversible operation. When attempting to modify the options bytes, the protection error flag WRPERR is set in FLASH_SR and FLASH_C2SR, and an interrupt can be generated.
Note: The debug feature is also disabled under reset.
STMicroelectronics is not able to perform analysis on defective parts on which the level 2 protection has been set and the system is non-secure (ESE = 0).
Change the readout protection level
It is easy to move from level 0 to level 1 by changing the value of the RDP byte to any value (except 0xCC). By programming the 0xCC value in the RDP byte, it is possible to go to level 2 directly from level 0 or from level 1. Once in level 2 and the system is non-secure (ESE = 0 ), it is no more possible to modify the readout protection level.
When the RDP is reprogrammed to the value 0xAA to move from level 1 to level 0, a mass erase of the main flash memory is performed if PCROP_RDP is set in FLASH_PCROP1AER. Backup registers (RTC_BKPxR in the RTC), SRAM1, SRAM2 and PKA SRAM are also erased. The user options except PCROP protection are set to their previous values copied from FLASH_OPTR, FLASH_WRP1xR (x= A or B). PCROP is disabled. The OTP area is not affected by mass erase and remains unchanged.
If the bit PCROP_RDP is cleared in FLASH_PCROP1AER, the full mass erase is replaced by a partial mass erase that is successive page erases, except for the pages protected by PCROP. This is done in order to keep the PCROP code. Only when the flash memory is erased, options are re-programmed with their previous values. This is also true for FLASH_PCROP1xSR and FLASH_PCROP1xER registers (x= A or B).
If the CPU2 is secure (ESE = 1) the full mass erase is replaced by a partial mass erase that is successive page erases, except for the pages protected by CPU2 security (SFSA). This is done in order to keep the CPU2 secure code.
Table 19. RDP regression from level 1 to level 0 and memory erase
| ESE | PCROP | PCROP_RDP | Comment |
|---|---|---|---|
| 0 | None | x | FLASH, SRAM1, SRAM2, PKA SRAM and backup registers mass erase |
| Partial | 1 | ||
| 0 | Flash multiple page erase of all non-PCROP pages SRAM1, SRAM2, PKA SRAM and backup registers erased (PCROP flash pages conserved) | ||
| Complete | Flash, SRAM1, SRAM2 and backup registers conserved. PKA SRAM erase. | ||
| 1 partial | None | x | Flash multiple page erase of all non-secure pages SRAM1, SRAM2, PKA SRAM and backup registers erased (secure flash pages conserved) |
| Partial | 1 | ||
| 0 | Flash multiple page erase of all non-PCROP pages and non-secure pages SRAM1, SRAM2, PKA SRAM and backup registers erased (PCROP flash pages and secure flash pages conserved) | ||
| Complete non-secure | Flash, SRAM1, SRAM2, and backup registers conserved PKA SRAM erased | ||
| 1 complete flash | x | x | Flash, SRAM1, SRAM2, and backup registers conserved PKA SRAM erased |
| 1 → 0 | None | x | Flash, SRAM1, SRAM2, PKA SRAM and backup registers mass erased |
| Partial | 1 | ||
| 0 | Flash multiple page erase of all non-secure non-PCROP pages and secure pages SRAM1, SRAM2, PKA SRAM and backup registers erased (non-secure PCROP flash pages conserved) | ||
| Complete non-secure | Flash multiple page erase of all secure pages SRAM1, SRAM2, PKA SRAM and backup registers erased (non-secure PCROP flash pages conserved) |
Note: Full or partial mass erase is performed only when level 1 is active and level 0 is requested. When the protection level is increased (0→1, 1→2, 0→2, or directly decreased from level 2 to level 0), there is no mass erase.
To validate the protection level change, the option bytes must be reloaded through the OBL_LAUNCH bit in FLASH_CR, or a POR, or wake-up from Standby or Shutdown mode.
Figure 8. Changing the RDP level
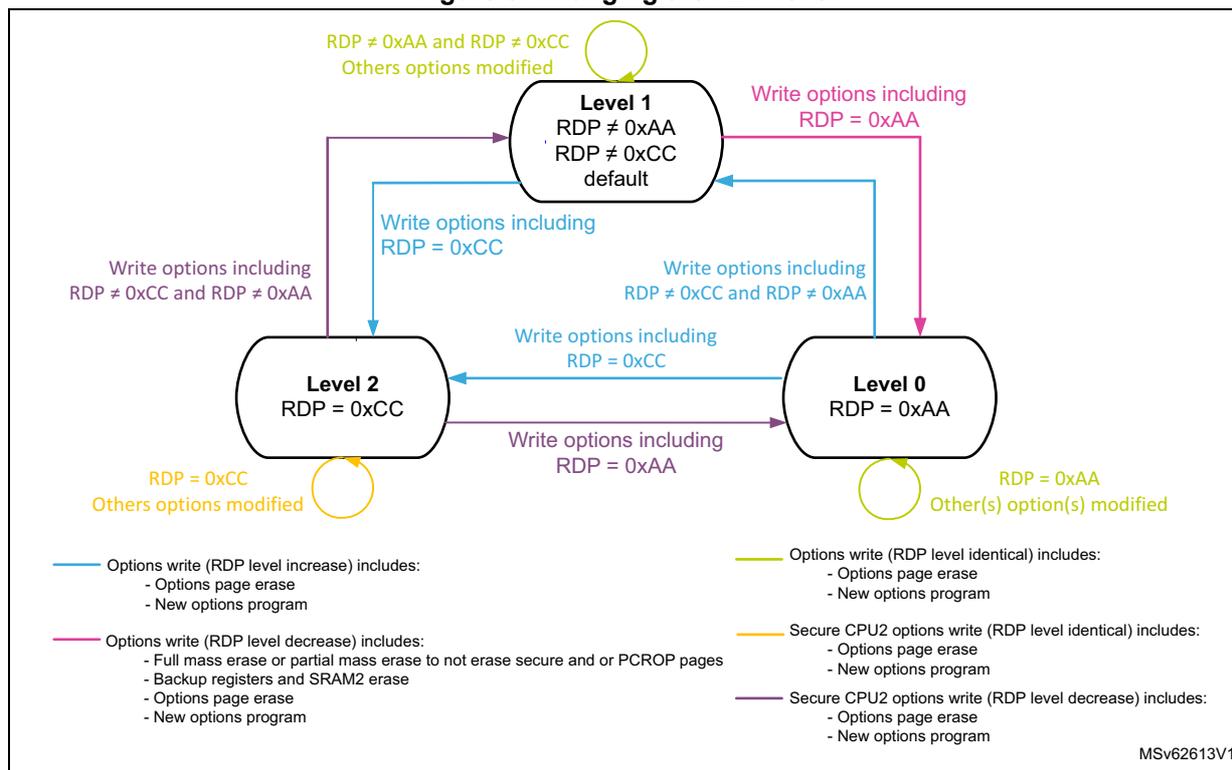
Legend:
- —
Options write (RDP level increase) includes:
- - Options page erase
- - New options program
- —
Options write (RDP level identical) includes:
- - Options page erase
- - New options program
- —
Secure CPU2 options write (RDP level identical) includes:
- - Options page erase
- - New options program
- —
Secure CPU2 options write (RDP level decrease) includes:
- - Options page erase
- - New options program
- —
Options write (RDP level decrease) includes:
- - Full mass erase or partial mass erase to not erase secure and or PCROP pages
- - Backup registers and SRAM2 erase
- - Options page erase
- - New options program
MSV62613V1
Table 20. Access status versus protection level and execution modes
| Area | Protection level | User execution (BootFromFlash) | Debug/ BootFromRam/ BootFromLoader/ BootFromSFI /RSS | ||||
|---|---|---|---|---|---|---|---|
| Read | Write | Erase | Read | Write | Erase | ||
| Main flash memory | 1 | Yes | Yes | Yes | No | No | No (4) |
| 2 | Yes | Yes | Yes | N/A (1) | N/A (1) | N/A (1) | |
| System memory (2) | 1 | Yes | No | No | Yes | No | No |
| 2 | Yes | No | No | N/A (1) | N/A (1) | N/A (1) | |
| Option bytes | 1 | Yes | Yes (3) | Yes | Yes | Yes (3) | Yes |
| 2 | Yes | CPU1 and CPU2 none secure - No CPU2 secure - Yes | CPU1 and CPU2 none secure - No CPU2 secure - Yes | N/A (1) | N/A (1) | N/A (1) | |
| Backup registers | 1 | Yes | Yes | N/A | No | No | No (4) |
| 2 | Yes | Yes | N/A | N/A (1) | N/A (1) | N/A (1) | |
| SRAM2 | 1 | Yes | Yes | N/A | No | No | No (5) |
| 2 | Yes | Yes | N/A | N/A (1) | N/A (1) | N/A (1) | |
- 1. When the protection level 2 is active, the debug port, the boot from RAM and the boot from system memory are disabled.
- 2. The system memory is only read-accessible, whatever the protection level (0, 1 or 2) and execution mode.
- 3. The flash non secure main memory is erased when the RDP option byte is programmed from level 1 to level 0. The flash secure main memory is also erased when the ESE option byte is regressed at the same time as the RDP option byte programming from level 1 to level 0.
- 4. The backup registers are erased when RDP changes from level 1 to level 0.
5. SRAM1, SRAM2 and PKA SRAM are erased when RDP changes from level 1 to level 0.
4.6.2 Proprietary code readout protection (PCROP)
Two parts of the flash memory can be protected against read and write from third parties.
The protected area is execute-only: it can only be reached by the STM32 CPUs with an instruction code, while all other accesses (DMA, debug and CPU data read, write and erase) are strictly prohibited. The PCROP areas have a 1-Kbyte granularity. An additional option bit (PCROP_RDP) defines if the PCROP area is erased or not when the RDP protection is changed from level 1 to level 0 (refer to Change the readout protection level ).
Each PCROP area is defined by a start page offset and an end page offset into the flash memory. These offsets are defined in the PCROP address registers (FLASH_PCROP1ASR, FLASH_PCROP1AER), FLASH_PCROP1BSR and FLASH_PCROP1BER).
A PCROP area is defined from the address:
Flash memory base address + [PCROP1x_STRT x 0x400] (included) to the address
Flash memory base address + [(PCROP1x_END+1) x 0x400] (excluded).
The minimum PCROP area size is two PCROP pages (2 Kbytes)
PCROP1x_END = PCROP1x_STRT + 1.
When PCROP1x_END = PCROP1x_STRT, the full flash memory is PCROP protected.
For example, to protect by PCROP from the address 0x0801 2F80 (included) to the address 0x0801 D004 (included), if boot in flash is selected, one of the FLASH_PCROP1xSR and FLASH_PCROP1xER registers (x =A or B) must be programmed with:
- • PCROP1x_STRT = 0x4B (PCROP area first address 0x0801 2C00)
- • PCROP1x_END = 0x74 (PCROP area last address 0x0801 D3FF)
Any data read access performed through a PCROP protected area triggers the RDERR flag error.
Any PCROP protected address is also write protected and any write access to one of these addresses triggers WRPERR.
Any PCROP area is also erase protected. Consequently, any erase to a page in this zone is impossible (including the page containing the start address and the end address of this zone). Moreover, a software mass erase cannot be performed if one zone is PCROP protected.
In the previous example, due to erase by page, all pages from page 0x4B to 0x74 are protected. In case of page erase, all addresses from 0x0801 2C00 to 0x0801 D3FF cannot be erased.
Deactivation of PCROP can only occur when the RDP is changing from level 1 to level 0. If the user options modification tries to clear PCROP or to decrease the PCROP areas, the options programming is launched but PCROP areas stays unchanged. On the contrary, it is possible to increase the PCROP areas.
When option bit PCROP_RDP is cleared and when the RDP is changing from level 1 to level 0, the full mass erase is replaced by a partial mass erase to preserve the PCROP area (refer to Change the readout protection level ). In this case, PCROP1x_STRT and PCROP1x_END (x =A or B) are not erased.
Table 21: PCROP protection| PCROP registers values (x = A or B) | PCROP protection area |
|---|---|
| PCROP1x_STRT = PCROP1x_END | No PCROP1x, unprotected |
| PCROP1x_STRT > PCROP1x_END | No PCROP1x, unprotected |
| PCROP1x_STRT < PCROP1x_END | Pages from PCROP1x_STRT to PCROP1x_END are protected |
Note: It is recommended to align PCROP areas with the page granularity when using PCROP_RDP, or to leave free the rest of the page where PCROP zones starts or ends.
4.6.3 Write protection (WRP)
The user area in the flash memory can be protected against unwanted write operations. Two write-protected (WRP) areas can be defined, with 2-Kbyte granularity page. Each area is defined by a start page offset and an end page offset related to the physical flash memory base address. These offsets are defined in the WRP address registers FLASH_WRP1AR and FLASH_WRP1BR.
The WRP “x” area (x = A, B) is defined from the address:
Flash memory Base address + [WRP1x_STRT x 0x800] (included) to the address:
Flash memory Base address + [(WRP1x_END+1) x 0x800] (excluded).
The minimum WRP area size is one WRP 2_Kbyte page, WRP1x_END = WRP1x_STRT.
For example, to protect by WRP from the address 0x0801 2000 (included) to the address 0x0801 9FFF (included), if boot in flash is selected, FLASH_WRP1AR register must be programmed with:
- • WRP1A_STRT = 0x24
- • WRP1A_END = 0x33
WRP1B_STRT and WRP1B_END in FLASH_WRP1BR can be used instead (area “B” in flash memory).
When WRP is active, it cannot be erased or programmed. Consequently, a software mass erase cannot be performed if one area is write-protected.
If an erase/program operation to a write-protected part of the flash memory is attempted, the write protection error flag (WRPERR) is set in FLASH_SR. This flag is also set for any write access to on the following area:
- • OTP area
- • part of the flash memory that can never be written like the ICP
- • PCROP area
Note: When the flash memory readout protection level is selected (RDP level1), it is not possible to program or erase the memory if the CPU debug features are connected (JTAG or single wire) or boot code is being executed from RAM or system flash, even if WRP is not activated. Any attempt generates an hard fault (BusFault).
Table 22: WRP protection
| WRPx registers values (x = A or B) | WRP protection area |
|---|---|
| WRP1x_STRT = WRP1x_END | Page WRP1x is protected |
| WRP1x_STRT > WRP1x_END | No WRP, unprotected |
| WRP1x_STRT < WRP1x_END | Pages from WRP1x_STRT to WRP1x_END are protected |
Note: To validate the WRP options, the option bytes must be reloaded through the OBL_LAUNCH bit in FLASH_CR.
4.6.4 CPU2 security (ESE)
All or a part of the flash memory and SRAM1, SRAM2 memories can be made secure, exclusively accessible by the CPU2, protected against execution, read and write from third parties. Only the CPU2 can execute, read and write in these areas, which can only be reached by the CPU2, while all other accesses (CPU1 and DMA) are strictly prohibited.
CPU2 security is enabled when part or all of the flash memory is secure (FSD = 0) or when option byte loading fails. In this case, the ESE bit in FLASH_OPTR is set.
Changing the CPU2 security mode
It is easy to enable the CPU2 security by loading the user option FSD with 0. Security is applied in any RDP level.
CPU2 security start address can be modified by the secure CPU2 by loading a new user option SFSA. To totally disable the security, CPU2 sets the FSD bit. It is a good practice, prior to removing security from part or all of the memory, to page erase the flash memory part that becomes non-secure.
Non-secure CPU1 and secure CPU2 can both remove security by setting the ESE bit to 0 in FLASH_OPTR and regressing the RDP level from level 1 to level 0. In this case the main flash memory, backup registers (RTC_BKPxR in the RTC), SRAM1, SRAM2 and PKA SRAM are erased as described in Change the readout protection level .
CPU2 secure flash area
The CPU2 secure flash area has a 2-Kbyte granularity sector and is defined by the secure flash start page offset user option (SFSA) into the flash memory. This offset is controlled from the SFSA field in FLASH_SFR.
The CPU2 secure flash area is defined as:
Flash memory base address + [SFSA x 0x0800] (included) to the last flash address.
When CPU2 security is enabled, the minimum CPU2 secure area size is one sector (2 Kbytes).
For example, with a CPU2 secure area from the address 0x0802 7000 (included) to the address 0x0803 FFFF (included), FLASH_SFR must be programmed with SFSA = 0x4E.
The ESE flag in FLASH_OPTR indicates if the CPU2 security is enabled.
Any CPU1 access to a CPU2 security area triggers RDERR or WRPERR flag error.
CPU2 secure SRAM areas
SRAM1 and SRAM2 areas are only secure when the flash memory security is enabled (ESE = 1).
The CPU2 secure SRAM2 and SRAM1 areas have a 1-Kbyte granularity and are defined by the secure “backup” ram (SRAM2) start address user options (BRSD and SBRSA) and the secure “non-backup” ram (SRAM1) start address user option (NBRSD and SNBRSA) into the flash memory. These offset are controlled from the SBRSA and SNBRSA fields in FLASH_SRRVR.
The CPU2 secure SRAM2 area is defined as:
SRAM2 base address + [SBRSA x 0x0400] (included) to the last SRAM2 address.
For example, with a CPU2 secure SRAM2 area from the address 0x2000 A800 (included) to the address 0x2000 FFFF (included), FLASH_SRRVR must be programmed with SBRSA = 0x0A.
Any CPU1 read access returns zero data. A write access to a CPU2 security SRAM2 area is discarded and generates an illegal access event.
When BRSD is set to 1, the SRAM2 is non-secure.
The CPU2 secure “non-backup” SRAM1 area is defined as:
“non-backup” SRAM1 base address + [SNBRSA x 0x0400] (included) to the last SRAM1 address.
For example, with a CPU2 secure SRAM1 area from the address 0x2000 6C00 (included) to the address 0x2000 7FFF (included), FLASH_SRRVR must be programmed with SNBRSA = 0x1B.
Any CPU1 read access returns zero data. A write access to a CPU2 security SRAM1 area is discarded and generates an illegal access event.
When NBRSD is set to 1, the SRAM1 is non-secure.
CPU2 debug access
Debug access to the CPU2 is controlled as follows:
- • user option DDS. This variable is accessible from the DDS field in FLASH_SFR.
- • Additionally, when CPU2 debug is enabled in user option DDS, the CPU2 debug access can be controlled by software with the C2SWDBGEN bit in FLASH_ACR2. When CPU2 debug is disabled in user option DDS, C2SWDBGEN has no meaning.
The selection for CPU2 debug access is independent from security (ESE = don't care).
When CPU2 debug access is disabled, the debugger has no access to the CPU2 and the secure areas.
When the system is non-secure (ESE =0 ), CPU1 and CPU2 can enable and disable the CPU2 debug access via the DDS bit in FLASH_SFR. In this case, the C2SWDBGEN bit is not writable and its default value is debug enabled. CPU2 DDS debug is enabled/disabled after restarting OBL.
When the system is secure (ESE =1 ) CPU2 debug access can only be enabled by the secure CPU2 via DDS and C2SWDBGEN bits. CPU2 debug can be disabled directly by the CPU2 via the DDS bit, and indirectly by both CPUs when regressing ESE. CPU2 debug is enabled/disabled after restarting OBL.
When ESE = 1 and the secure hide protection area is disabled, the CPU2 debug is enabled with the C2SWDBGEN bit after restarting OBL. However when the secure hide protection area is enabled, the CPU2 debug is disabled with the C2SWDBGEN bit and may subsequently be enabled by software.
4.6.5 Hide protection area (HDPAD)
This feature is only available when the system is secure (ESE = 1).
All or a part of the flash memory can be made hide protected, providing only access to this flash memory area when enabled. Once hide protection access is disabled with the HDPADIS bit, the area is protected against execution, read and write from any bus master. The flash hide protect area is no longer accessible.
The hide protect area is an area in user flash which is accessible after a reset and where all access (execute, read, write) can be prohibited by setting the HDPADIS bit. This hide protect register bit is set by the hide protect code at the end of its execution. The hide protection area is useful to provide SFU functions, only available after a device reset.
4.6.6 CPU1 boot lock chain of trust
The BOOT_LOCK forces the CPU1 to boot from the user flash memory, regardless of what is selected by BOOT0 and BOOT1. When BOOT_LOCK is enabled and BOOT0/BOOT1 select anything different than the user flash memory boot, the system boots anyway from the user flash memory. System boot via BOOT0/BOOT1 from SRAM1 or bootloader or CPU2 SFI/RSS boot is no longer possible.
It is still possible to boot the CPU1 according to the software selected remap by MEM_MODE bits in SYSCFG memory remap register (SYSCFG_MEMRMP) from SRAM1 or bootloader.
4.6.7 CPU2 boot lock chain of trust
When the BOOT0/BOOT1 select a CPU2 boot mode, the C2BOOT_LOCK forces the CPU2 to boot from the SBRV and C2OPT. When C2BOOT_LOCK is enabled and BOOT0/BOOT1 select system CPU2 SFI/RSSI boot, the system boots anyway from the user flash SBRV and C2OPT instead. In this case, CPU1 is on hold.
When C2BOOT_LOCK is enabled, SBRV and C2OPT can no longer be modified.
The C2BOOT_LOCK does not impact the CPU1 boot. CPU1 still boots according to BOOT0 and BOOT1 settings (system flash, user flash or SRAM1).
4.7 FLASH program erase suspension
Flash program and erase operation can be suspended by setting the PES bit in FLASH_ACR or FLASH_C2ACR. This feature is useful when executing time critical sections by a CPU. It makes possible to suspend any new program or erase operation from being started, preventing CPU instruction and data fetches from being blocked.
When at least one PES bit is set, the following occurs:
- Any ongoing program or erase operation is completed.
The maximum latency for a flash program erase suspension is the maximum time for one program or erase operation to complete (see product datasheets for more information on the flash program and erase timing).
- All new requested program and erase operations is not started but suspended.
PESD bits in FLASH_SR and FLASH_C2SR are set as soon as any PES is set, no matter if a program/erase is currently suspended. This allows a CPU to test PESD prior to requesting a program or an erase operation.
When all PES bits are reset to 0, a suspended program or erase operation is started: the PESD bits are cleared.
4.8 FLASH interrupts
Table 23. Flash interrupt requests
| Interrupt event | Event flag | Event flag/interrupt clearing method | Interrupt enable control bit |
|---|---|---|---|
| End of operation | EOP (1) | Write EOP=1 | EOPIE |
| Operation error | OPERR (2) | Write OPERR=1 | ERRIE |
| Readout protection error | RDERR | Write RDERR=1 | RDERRIE |
| Write protection error | WRPERR | Write WRPERR=1 | N/A |
| Size error | SIZERR | Write SIZERR=1 | N/A |
| Programming sequential error | PROGERR | Write PROGERR=1 | N/A |
| Programming alignment error | PGAERR | Write PGAERR=1 | N/A |
| Programming sequence error | PGSERR | Write PGSERR=1 | N/A |
| Data miss during fast programming error | MISSERR | Write MISSERR=1 | N/A |
| Fast programming error | FASTERR | Write FASTERR=1 | N/A |
| ECC error correction | ECCC | Write ECCC=1 | ECCIE |
| ECC double-error (NMI) | ECCD | Write ECCD=1 | N/A |
1. EOP is set only if EOPIE is set.
2. OPERR is set only if ERRIE is set.
4.8.1 Illegal access interrupts
Unprivileged access to privileged registers generates an illegal access event. This event is connected to the GTZC_TZIC.
Non-secure access to secure registers generates an illegal access event. This event is connected to the GTZC_TZIC.
For more information on illegal access events see: Section 3: Global security controller (GTZC) .
4.9 Register access protection
The user option registers may be protected by security and privilege.
When the system is secure (ESE = 1) and the user option registers in the flash memory are also protected by privileged (FLASH_PRIVMODER.PRIV = 1), the flash memory secure user option bits (FSD, SFSA, BRSD, SBRSA, NBRSD, SNBRSA, SBRV, C2OPT, HDPAD, HDPSA and DDS) are secure and privileged. They can be written only by the secure privileged CPU2 and read by any CPU secure and non-secure, unprivileged and privileged. When the CPU1 or the unprivileged CPU2 tries to write, the write is discarded and a flash memory illegal access interrupt is generated.
When the system is secure (ESE = 1) and the user option bits in the flash memory are also protected by privileged (FLASH_PRIVMODER.PRIV = 1), the other non-secure user option bits are privileged. They can be written only by a privileged CPU1 or CPU2, and read by CPU1, CPU2 unprivileged and privileged. On an unprivileged write access, the write is discarded and a flash memory illegal access interrupt is generated.
Table 24: Register protection overview
| Registers | Security | PRIVMODE (1) |
|---|---|---|
| FLASH_CxACR | No | No |
| FLASH_ACR2 | Yes (2) | No |
| FLASH_KEYR | No | No |
| FLASH_OPTKEYR | No | No |
| FLASH_CxSR | No | No |
| FLASH_CxCR | No | No |
| FLASH_ECCR | No | No |
| FLASH_OPTR | No | Yes |
| FLASH_PCROP1xSR/ER | No | Yes |
| FLASH_WRP1xR | No | Yes |
| FLASH_IPCCBR | No | Yes |
| FLASH_SFR | Yes (3) | Yes |
| FLASH_SRRVR | Yes (3) | Yes |
- 1. PRIVMODE privilege protection is only available when the device is secure ESE = 1.
- 2. Secure-privileged write access protected at any time, regardless of the device security ESE and PRIVMODE values.
- 3. Secure write access protection is only applicable when the device is secure ESE = 1
4.10 FLASH registers
4.10.1 FLASH access control register (FLASH_ACR)
Address offset: 0x000
Reset value: 0x0000 0600
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | EMPTY |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| PES | Res. | Res. | DCRST | ICRST | DCEN | ICEN | PRFTEN | Res. | Res. | Res. | Res. | Res. | LATENCY[2:0] | ||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | |||||||
Bits 31:17 Reserved, must be kept at reset value.
Bit 16 EMPTY : Flash user area empty
When read, this bit indicates whether the first location of the user flash is erased or has a programmed value.
0: Read: user flash programmed
1: Read: user flash empty
Bit 15 PES : CPU1 program/erase suspend request
0: Flash program and erase operations granted
1: Any new flash program and erase operation is suspended until this bit and the same bit in FLASH_C2ACR are cleared. The PESD bit in FLASH_SR and FLASH_C2SR are reset when at least one PES bit in FLASH_ACR or FLASH_C2ACR is set.
Bits 14:13 Reserved, must be kept at reset value.
Bit 12 DCRST : CPU1 data cache reset
0: CPU1 data cache not reset
1: CPU1 data cache reset
This bit can be written only when the data cache is disabled.
Bit 11 ICRST : CPU1 instruction cache reset
0: CPU1 instruction cache not reset
1: CPU1 instruction cache reset
This bit can be written only when the instruction cache is disabled.
Bit 10 DCEN : CPU1 data cache enable
0: CPU1 data cache disabled
1: CPU1 data cache enabled
Bit 9 ICEN : CPU1 instruction cache enable
0: CPU1 instruction cache disabled
1: CPU1 instruction cache enabled
Bit 8 PRFTEN : CPU1 prefetch enable
0: CPU1 prefetch disabled
1: CPU1 prefetch enabled
Bits 7:3 Reserved, must be kept at reset value.
Bits 2:0 LATENCY[2:0] : Latency
These bits represent the ratio of the flash HCLK clock period to the flash memory access time.
000: Zero wait state
001: One wait state
010: Two wait states
Others: reserved
4.10.2 FLASH access control register 2 (FLASH_ACR2)
Address offset: 0x004
Reset value: 0x0000 0000 (Default)
Default reset when HDPAD = 0, 0x0000 0004 when HDPAD = 1
This register provides write access security and privilege. It can only be written by the secure privileged CPU2. A write access from the unprivileged CPU2 or a CPU1 is ignored. A non-secure or unprivileged write access generates an illegal access event. On any read access, the register value is returned.
There are no read restrictions.
Note: When the system is non-secure (ESE = 0), this register cannot be written.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | C2SWDBGEN | HDPADIS | PRIVMODE |
| rw | rw | rw |
Bits 31:3 Reserved, must be kept at reset value.
Bit 2 C2SWDBGEN : CPU2 software debug enable
This bit is set and reset by software.
When HDPAD = 0 (hide protection area enabled), the CPU2 software debug is disabled after a system reset.
When HDPAD = 1 (hide protection area disabled), the CPU2 software debug is enabled after a system reset.
0: CPU2 debug access disabled
1: CPU2 debug access enabled (when also enabled in DDS)
Bit 1 HDPADIS : Flash user hide protection area access disable
This bit is set by software and is only reset by hardware on a system reset.
0: User flash hide protection area access enabled
1: User flash hide protection area access disabled
Bit 0 PRIVMODE : FLASH privileged mode enable
This bit is set and reset by software.
0: FLASH register access privileged mode disabled
1: FLASH register access privileged mode enabled
4.10.3 FLASH key register (FLASH_KEYR)
Address offset: 0x008
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| KEY[31:16] | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| KEY[15:0] | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
Bits 31:0 KEY[31:0] : Flash key
The following values must be written consecutively to unlock FLASH_CR and FLASH_C2CR, thus enabling programming/erasing operations:
KEY1: 0x4567 0123
KEY2: 0xCDEF 89AB
4.10.4 FLASH option key register (FLASH_OPTKEYR)
Address offset: 0x00C
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| OPTKEY[31:16] | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| OPTKEY[15:0] | |||||||||||||||
| w | w | w | w | w | w | w | w | w | w | w | w | w | w | w | w |
Bits 31:0 OPTKEY[31:0] : Option byte key lower bits
The following values must be written consecutively to unlock the flash memory option registers, enabling option byte programming/erasing operations:
KEY1: 0x0819 2A3B
KEY2: 0x4C5D 6E7F
4.10.5 FLASH status register (FLASH_SR)
Address offset: 0x010
Reset value: 0x000X 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PESD | CFGBSY | Res. | BSY |
| r | r | r | |||||||||||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| OPTVERR | RDERR | OPTNV | Res. | Res. | Res. | FASTERR | MISSERR | PGSERR | SIZERR | PGAERR | WRPERR | PROGERR | Res. | OPERR | EOP |
| rc_w1 | rc_w1 | r | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 |
Bits 31:20 Reserved, must be kept at reset value.
Bit 19 PESD : Program/erase operation suspended
This bit is set and reset by hardware.
Set when at least one PES bit in FLASH_ACR or FLASH_C2ACR is set.
Cleared when both PES bits in FLASH_ACR and FLASH_C2ACR are cleared.
When set, new program or erase operations are not started.
Bit 18 CFGBSY : Program or erase configuration busy
This bit is set and reset by hardware (set when first word is sent and reset when program operation completes or is interrupted by an error).
When set, the program and erase settings in PG, PNB[6:0], PER, and MER bits in FLASH_CR are used (busy) and cannot be changed (a programming or erase operation is ongoing).
When reset, the program and erase settings in PG, PNB[6:0], PER, and MER bits in FLASH_CR can be modified.
Bit 17 Reserved, must be kept at reset value.
Bit 16 BSY : Busy
This bit indicates that a flash operation requested in FLASH_CR is in progress. This bit is set at the beginning of a flash operation and reset when the operation finishes or when an error occurs.
Bit 15 OPTVERR : Option and engineering bits loading validity error
Set by hardware when the options and engineering bits read may not be the one configured by the user or production. If options and engineering bits are not properly loaded, OPTVERR is set again after each system reset. Option bytes that fail loading are forced to a safe value (see Section 4.4.2: Option bytes programming ).
This bit is cleared by writing 1.
Bit 14 RDERR : PCROP read error
Set by hardware when an address to be read through the D-bus belongs to a read protected area of the flash memory (PCROP protection). An interrupt is generated if RDERRIE is set in FLASH_CR.
This bit is cleared by writing 1.
Bit 13 OPTNV : User option OPTVAL indication
This bit is set and reset by hardware.
0: The OBL user option OPTVAL indicates “valid” (user option program sequence has not terminated completely).
1: The OBL user option OPTVAL indicates “not valid” (OPTVAL check word has been erroneously read).
Bits 12:10 Reserved, must be kept at reset value.
Bit 9 FASTERR: Fast programming errorSet by hardware when a fast programming sequence (activated by FSTPG) is interrupted due to an error (alignment, size, write protection or data miss). The corresponding status bit (PGAERR, SIZERR, WRPERR or MISSERR) is set at the same time.
This bit is cleared by writing 1.
Bit 8 MISSERR: Fast programming data miss errorIn Fast programming mode, 32 double-words (256 bytes) must be sent to the flash memory successively and the new data must be sent to the logic control before the current data is fully programmed.
This bit is set by hardware when the new data is not present in time and cleared by writing 1.
Bit 7 PGSERR: Programming sequence errorThis bit is set by hardware when a write access to the flash memory is performed by the code, while PG or FSTPG have not been set previously. This bit is also set by hardware when PROGERR, SIZERR, PGAERR, WRPERR, MISSERR or FASTERR is set due to a previous programming error.
This bit is cleared by writing 1.
Bit 6 SIZERR: Size errorThis bit is set by hardware when the size of the access is a byte or half-word during a program or a fast program sequence. Only double-word programming is allowed (consequently: word access).
This bit is cleared by writing 1.
Bit 5 PGAERR: Programming alignment errorThis bit is set by hardware when the data to program cannot be contained in the same double-word (64 bits) flash memory in case of standard programming, or if there is a change of page during fast programming.
This bit is cleared by writing 1.
Bit 4 WRPERR: Write protection errorThis bit is set by hardware when an address to be erased/programmed belongs to a write-protected part (by WRP, PCROP or RDP level 1) of the flash memory.
This bit is cleared by writing 1.
Bit 3 PROGERR: Programming errorThis bit is set by hardware when a double-word address to be programmed contains a value different from 0xFFFF FFFF FFFF FFFF before programming, except if the data to write is 0x0000 0000 0000 0000.
This bit is cleared by writing 1.
Bit 2 Reserved, must be kept at reset value. Bit 1 OPERR: Operation errorThis bit is set by hardware when a flash memory operation (program/erase) completes unsuccessfully. This bit is set only if error interrupts are enabled (ERRIE = 1).
This bit is cleared by writing 1.
Bit 0 EOP: End of operationThis bit is set by hardware when one or more flash memory operation (program/erase) completes successfully. This bit is set only if the end of operation interrupts are enabled (EOPIE = 1).
This bit is cleared by writing 1.
4.10.6 FLASH control register (FLASH_CR)
Address offset: 0x014
Reset value: 0xC000 0000
Access: no wait state when no flash memory operation is ongoing. Word, half-word and byte access.
This register cannot be modified when CFGBSY is set in FLASH_SR.
When PESD is cleared in FLASH_SR, the register write access is stalled until the CFGBSY bit is cleared (for example by the other CPU).
When PESD is set in FLASH_SR and a program or an erase operation is ongoing, the register write access causes a bus error.
When PESD is set in FLASH_SR but there is no ongoing programming or erase operation, the register write access is completed, but the requested operation is suspended. BSY/CFGBSY is set and remains 1 until suspend is deactivated by clearing the PES bits in FALSH_ACR and FLASH_C2ACR. Consequently PESD goes back to 0 and the suspended operation completes.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| LOCK | OPT LOCK | Res. | Res. | OBL LAUNCH | RD ERRIE | ERRIE | EOPIE | Res. | Res. | Res. | Res. | Res. | FSTPG | OPT STRT | STRT |
| rs | rs | rc_w1 | rw | rw | rw | rw | rs | rs | |||||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | PNB[6:0] | MER | PER | PG | ||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | ||||||
Bit 31 LOCK: FLASH_CR lock
This bit can only be set by software. When set, the FLASH_CR register is locked. This bit is cleared by hardware after detecting the unlock sequence.
In case of an unsuccessful unlock operation, this bit remains set until the next system reset.
Bit 30 OPTLOCK: Options lock
This bit can only be set by software. When set, all bits concerning user option in FLASH_CR and so option page are locked. This bit is cleared by hardware after detecting the option unlock sequence. The LOCK bit must be cleared before doing the unlock sequence for OPTLOCK bit.
In case of an unsuccessful option unlock operation, this bit remains set until the next reset.
Bits 29:28 Reserved, must be kept at reset value.
Bit 27 OBL_LAUNCH: forces the option byte loading
When set to 1, this bit forces the option byte reloading. This bit is cleared only when the option byte loading is complete. It cannot be written if OPTLOCK is set.
0: Option byte loading completed
1: Option byte loading requested
Bit 26 RDERRIE: PCROP read error interrupt enable
This bit enables the interrupt generation when the RDERR bit in FLASH_SR is set to 1.
0: PCROP read error interrupt disabled
1: PCROP read error interrupt enabled
Bit 25 ERRIE : error interrupt enable
This bit enables the interrupt generation when the OPERR bit in FLASH_SR is set to 1.
0: OPERR error interrupt disabled
1: OPERR error interrupt enabled
Bit 24 EOPIE : end of operation interrupt enable
This bit enables the interrupt generation when the EOP bit in FLASH_SR is set to 1.
0: EOP Interrupt disabled
1: EOP Interrupt enabled
Bits 23:19 Reserved, must be kept at reset value.
Bit 18 FSTPG : fast programming
0: Fast programming disabled
1: Fast programming enabled
Bit 17 OPTSTRT : options modification start
When set, this bit triggers an options programming operation. When RDP level is regressed from level 1 to level 0, this bit also launches a flash memory, SRAM1 and SRAM2 erase.
This bit is set only by software and cleared when BSY is cleared in FLASH_SR.
Bit 16 STRT : start
When set, this bit triggers an erase operation. If MER and PER are reset and STRT is set, an unpredictable behavior may occur without generating any error flag. This condition is forbidden.
This bit is set only by software and cleared when BSY is cleared in FLASH_SR.
When the system is secure (ESE = 1) starting operations by the CPU1, involving secure flash pages are rejected and a bus error is generated.
Bits 15:10 Reserved, must be kept at reset value.
Bits 9:3 PNB[6:0] : page number selection
These bits select the 2-Kbyte page to erase.
0x00: page 0
0x01: page 1
...
0x7F: page 127
Bit 2 MER : mass erase
When set, this bit triggers the mass erase (all user pages).
Bit 1 PER : page erase
0: page erase disabled
1: page erase enabled
Bit 0 PG : programming
0: Flash programming disabled
1: Flash programming enabled
4.10.7 FLASH ECC register (FLASH_ECCR)
Address offset: 0x018
Reset value: 0x0000 0000
Access: no wait state when no flash memory operation is ongoing. Word, half-word and byte access.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| ECCD | ECCC | Res. | CPUID[2:0] | Res. | ECCIE | Res. | Res. | Res. | SYSF_ECC | Res. | Res. | Res. | ADDR_ECC[16] | ||
| rc_w1 | rc_w1 | r | r | r | rw | r | r | ||||||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| ADDR_ECC[15:0] | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
Bit 31 ECCD : ECC detection
Set by hardware when two ECC errors have been detected. When this bit is set, a NMI is generated.
This bit is cleared by writing 1.
Bit 30 ECCC : ECC correction
Set by hardware when one ECC error has been detected and corrected. An interrupt is generated if ECCIE is set.
This bit is cleared by writing 1.
Bit 29 Reserved, must be kept at reset value.
Bits 28:26 CPUID[2:0] : CPU identification
Set by hardware. This bit indicates the Bus-ID of the CPU access causing the ECC failure.
000: CPUID for CPU1 bus ID value
001: CPUID for CPU2 bus ID value
Bit 25 Reserved, must be kept at reset value.
Bit 24 ECCIE : ECC correction interrupt enable
0: ECCC interrupt disabled
1: ECCC interrupt enabled
Bits 23:21 Reserved, must be kept at reset value.
Bit 20 SYSF_ECC : system flash memory ECC fail
This bit indicates that the ECC error correction or double ECC error detection is located in the system flash memory.
Bits 19:17 Reserved, must be kept at reset value.
Bits 16:0 ADDR_ECC[16:0] : ECC fail double-word address
This bit indicates that double-word address is concerned by the ECC error correction or causes the double ECC error detection.
4.10.8 FLASH option register (FLASH_OPTR)
Address offset: 0x020
Reset value: 0x3FFF F0AA
Default reset value from ST production is given. Subsequently, 0bXX11 XXXX X111 XXXX 1XXX XXXX XXXX XXXX, the option bits are loaded with user values from the flash memory at reset release.
Access: no wait state when no flash memory operation is ongoing. Word, half-word and byte access.
This register can only be written by the CPU1 in RDP level 0 or RDP level 1.
When the system is secure (ESE = 1), this register is further more protected by the PRIVMODE. When privilege protection is enabled in PRIVMODE, this register provides
write access privilege and can only be written by a privileged access. Unprivileged write access is ignored and an illegal access event is generated. Unprivileged read access is still allowed.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| C2BOOT_LOCK | BOOT_LOCK | Res. | Res. | nBOOT0 | nSWBOOT0 | SRAM_RST | SRAM2_PE | nBOOT1 | Res. | Res. | Res. | WWDG_SW | IWDG_STDBY | IWDG_STOP | IWDG_SW |
| r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | |||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | nRST_SHDW | nRST_STDBY | nRST_STOP | BOR_LEV[2:0] | ESE | RDP[7:0] | |||||||||
| r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | |
Bit 31 C2BOOT_LOCK : CPU2 boot lock enable option bit
This bit may be set by software at any time but a write to clear is only taken into account in one of the following conditions:
- - when ESE = 0 and staying in RDP level 0
- - when ESE = 1 and staying in RDP level 0 by regressing FSD
- - when ESE = 0 and regressing RDP level from 1 to 0
- - when ESE = 1 and regressing RDP level from 1 to 0 and regressing ESE and or FSD.
0: CPU2 boot lock disabled
1: CPU2 boot lock enabled
Bit 30 BOOT_LOCK : CPU1 boot lock enable option bit
This bit may be set by software at any time, but a write to clear is only taken into account in one of the following conditions:
- - when staying in RDP level 0
- - when regressing RDP level from 1 to 0
0: CPU1 boot lock disabled
1: CPU1 boot lock enabled
Bits 29:28 Reserved, must be kept at reset value.
Bit 27 nBOOT0 : nBOOT0 option bit
If nSWBOOT0 bit selects BOOT0 to be taken from option bit nBOOT0, then this bit, together with option nBOOT1, selects the boot modes (from the user flash memory, SRAM1 or system flash memory). Refer to Section 2.2: Boot configuration .
0: nBOOT0 = 0
1: nBOOT0 = 1
Bit 26 nSWBOOT0 : software BOOT0 selection
0: BOOT0 taken from the option bit nBOOT0
1: BOOT0 taken from PH3/BOOT0 pin
Bit 25 SRAM_RST : SRAM1 and SRAM2 erase when system reset
0: SRAM1 and SRAM2 erased when a system reset occurs
1: SRAM1 and SRAM2 not erased when a system reset occurs
Note: PKA SRAM is always erased on any system.
Bit 24 SRAM2_PE : SRAM2 parity check enable
0: SRAM2 parity check enabled
1: SRAM2 parity check disable
Bit 23 nBOOT1 : boot configuration
Together with the BOOT0 pin or option bit nBOOT0 (depending on nSWBOOT0 option bit configuration), this bit selects boot mode from the user flash memory, SRAM1 or system flash memory. Refer to Section 2.2: Boot configuration .
Bits 22:20 Reserved, must be kept at reset value.
Bit 19 WWDG_SW : window watchdog selection
- 0: Hardware window watchdog
- 1: Software window watchdog
Bit 18 IWDG_STDBY : independent watchdog counter freeze in Standby mode
- 0: Independent watchdog counter frozen in Standby mode
- 1: Independent watchdog counter running in Standby mode
Bit 17 IWDG_STOP : independent watchdog counter freeze in Stop mode
- 0: Independent watchdog counter frozen in Stop mode
- 1: Independent watchdog counter running in Stop mode
Bit 16 IWDG_SW : independent watchdog selection
- 0: Hardware independent watchdog
- 1: Software independent watchdog
Bit 15 Reserved, must be kept at reset value.
Bit 14 nRST_SHDW : reset generation in Shutdown mode
- 0: Reset generated when entering the Shutdown mode
- 1: No reset generated when entering the Shutdown mode
Bit 13 nRST_STDBY : reset generation in Standby mode
- 0: Reset generated when entering the Standby mode
- 1: No reset generated when entering the Standby mode
Bit 12 nRST_STOP : reset generation in Stop mode
- 0: Reset generated when entering the Stop mode
- 1: No reset generated when entering the Stop mode
Bits 11:9 BOR_LEV[2:0] : BOR reset Level
These bits contain the \( V_{DD} \) supply level threshold that activates/releases the reset.
- 000: BOR level 0. Reset level threshold is ~ 1.7 V
- 001: BOR level 1. Reset level threshold is ~ 2.0 V
- 010: BOR level 2. Reset level threshold is ~ 2.2 V
- 011: BOR level 3. Reset level threshold is ~ 2.5 V
- 100: BOR level 4. Reset level threshold is ~ 2.8 V
Bit 8 ESE : system security enable flag
When read, this bit indicates whether the system security is enabled, meaning a not valid option byte has been loaded. Writing 0 to this bit and regressing the RDP from level 1 to level 0 disables the security.
- 0: Security disabled
- 1: Security enabled
Bits 7:0 RDP[7:0] : readout protection level
- 0xAA: Level 0, readout protection not active
- 0xCC: Level 2, chip readout protection active
- Others: Level 1, memories readout protection active
Note: Take care about PCROP_RDP configuration in level 1. Refer to Level 1: readout protection for more details.
4.10.9 FLASH PCROP zone A start address register (FLASH_PCROP1ASR)
Address offset: 0x024
Reset value: 0xFFFF FFFF
Default reset value from ST production is given. Subsequently, 0b1111 1111 1111 1111 1111 1111 XXXX XXXX, the option bits are loaded with user values from the flash memory at reset release.
Access: no wait state when no flash memory operation is ongoing. Word, half-word access.
This register can only be written by the CPU1 in RDP level 0 or RDP level 1.
When the system is secure (ESE = 1), this register is further more protected by the PRIVMODE. When privilege protection is enabled in PRIVMODE, this register provides write access privilege and can only be written by a privileged access. Unprivileged write access is ignored and an illegal access event is generated. Unprivileged read access is still allowed.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PCROP1A_STR[7:0] | |||||||
| rw | rw | rw | rw | rw | rw | rw | rw | ||||||||
Bits 31:8 Reserved, must be kept at reset value.
Bits 7:0 PCROP1A_STR[7:0] : PCROP1A area start offset
PCROP1A_STR contains the first 1-Kbyte page of the PCROP1A area.
4.10.10 FLASH PCROP zone A end address register (FLASH_PCROP1AER)
Address offset: 0x028
Reset value: 0xFFFF FF00
Default reset value from ST production is given. Subsequently, 0bX111 1111 1111 1111 1111 1111 XXXX XXXX, the option bits are loaded with user values from flash memory at reset release.
Access: no wait state when no flash memory operation is ongoing. Word, half-word access. PCROP_RDP bit can be accessed with byte access
This register can only be written by the CPU1 in RDP level 0 or RDP level 1.
When the system is secure ESE = 1, this register is further more protected by the PRIVMODE. When privilege protection is enabled in PRIVMODE, this register provides write access privilege and can only be written by a privileged access. Unprivileged write access is ignored and an illegal access event is generated. Unprivileged read access is still allowed.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| PCROP_RDP | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| rs | |||||||||||||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PCROP1A_END[7:0] | |||||||
| rw | rw | rw | rw | rw | rw | rw | rw | ||||||||
Bit 31 PCROP_RDP : PCROP area preserved when RDP level decreased
This bit is set only. It is reset after a full mass erase due to a change of RDP from level 1 to level 0.
0: PCROP area not erased when the RDP level is decreased from level 1 to level 0
1: PCROP area erased when the RDP level is decreased from level 1 to level 0 (full mass erase)
Bits 30:8 Reserved, must be kept at reset value.
Bits 7:0 PCROP1A_END[7:0] : PCROP1A area end offset
PCROP1A_END contains the last 1-Kbyte page of the PCROP1A area.
4.10.11 FLASH WRP area A address register (FLASH_WRP1AR)
Address offset: 0x02C
Reset value: 0xFF80 FFFF
Default reset value from ST production is given as 0b1111 1111 1XXX XXXX 1111 1111 1XXX XXXX, the option bits are loaded with user values from the flash memory at reset release.
Access: no wait state when no flash memory operation is ongoing. Word, half-word and byte access.
This register can only be written by the CPU1 in RDP level 0 or RDP level 1.
When the system is secure (ESE = 1), this register is further more protected by the PRIVMODE. When privilege protection is enabled in PRIVMODE, this register provides write access privilege and can only be written by a privileged access. Unprivileged write access is ignored and an illegal access event is generated. Unprivileged read access is still allowed.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WRP1A_END[6:0] | ||||||
| rw | rw | rw | rw | rw | rw | rw | |||||||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WRP1A_STRT[6:0] | ||||||
| rw | rw | rw | rw | rw | rw | rw | |||||||||
Bits 31:23 Reserved, must be kept at reset value.
Bits 22:16 WRP1A_END[6:0] : WRP area A end offset
Contains the last 2-Kbyte page of the WRP area A.
Bits 15:7 Reserved, must be kept at reset value.
Bits 6:0
WRP1A_STR[6:0]
: WRP area A start offset
Contains the first 2-Kbyte page of the WRP area A.
4.10.12 FLASH WRP area B address register (FLASH_WRP1BR)
Address offset: 0x030
Reset value: 0xFF80 FFFF
Default reset value from ST production is given as 0b1111 1111 1XXX XXXX 1111 1111 1XXX XXXX, the option bits are loaded with user values from flash memory at reset release.
Access: no wait state when no flash memory operation is ongoing. Word, half-word and byte access.
This register can only be written by the CPU1 in RDP level 0 or RDP level 1.
When the system is secure (ESE = 1), this register is further more protected by the PRIVMODE. When privilege protection is enabled in PRIVMODE, this register provides write access privilege and can only be written by a privileged access. Unprivileged write access is ignored and an illegal access event is generated. Unprivileged read access is still allowed.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WRP1B_END[6:0] | ||||||
| rw | rw | rw | rw | rw | rw | rw | |||||||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WRP1B_STR[6:0] | ||||||
| rw | rw | rw | rw | rw | rw | rw | |||||||||
Bits 31:23 Reserved, must be kept at reset value.
Bits 22:16
WRP1B_END[6:0]
: WRP area B end offset
WRPB1_END contains the last 2-Kbyte page of the WRP area B.
Bits 15:7 Reserved, must be kept at reset value.
Bits 6:0
WRP1B_STR[6:0]
: WRP area B start offset
WRPB1_END contains the first 2-Kbyte page of the WRP area B.
4.10.13 FLASH PCROP zone B start address register (FLASH_PCROP1BSR)
Address offset: 0x034
Reset value: 0xFFFF FFFF
Default reset value from ST production is given. Subsequently, 0b1111 1111 1111 1111 1111 1111 XXXX XXXX, the option bits are loaded with user values from the flash memory at reset release.
Access: no wait state when no flash memory operation is ongoing. Word and half-word access.
This register can only be written by the CPU1 in RDP level 0 or RDP level 1.
When the system is secure (ESE = 1), this register is further more protected by the PRIVMODE. When privilege protection is enabled in PRIVMODE, this register provides write access privilege and can only be written by a privileged access. Unprivileged write access is ignored and an illegal access event is generated. Unprivileged read access is still allowed.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PCROP1B_STRT[7:0] | |||||||
| rw | rw | rw | rw | rw | rw | rw | rw | ||||||||
Bits 31:8 Reserved, must be kept at reset value.
Bits 7:0
PCROP1B_STRT[7:0]
: PCROP1B area start offset
Contains the first 1-Kbyte page of the PCROP1B area.
4.10.14 FLASH PCROP zone B end address register (FLASH_PCROP1BER)
Address offset: 0x038
Reset value: 0xFFFF FF00
Default reset value from ST production is given. Subsequently, 0b1111 1111 1111 1111 1111 1111 XXXX XXXX, the option bits are loaded with user values from the flash memory at reset release.
Access: no wait state when no flash memory operation is ongoing. Word and half-word access.
This register can only be written by the CPU1 in RDP level 0 or RDP level 1.
When the system is secure (ESE = 1), this register is further more protected by the PRIVMODE. When privilege protection is enabled in PRIVMODE, this register provides write access privilege and can only be written by a privileged access. Unprivileged write access is ignored and an illegal access event is generated. Unprivileged read access is still allowed.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PCROP1B_END[7:0] | |||||||
| rw | rw | rw | rw | rw | rw | rw | rw | ||||||||
Bits 31:8 Reserved, must be kept at reset value.
Bits 7:0
PCROP1B_END[7:0]
: PCROP1B area end offset
Contains the first 1-Kbyte page of the PCROP1B area.
4.10.15 FLASH IPCC mailbox data buffer address register (FLASH_IPCCBR)
Address offset: 0x03C
Reset value: 0xFFFF FFFF
Default reset value from ST production is given. Subsequently, 0b1111 1111 1111 1111 11XX XXXX XXXX XXXX, the option bits are loaded with user values from the flash memory at power-on reset release.
This register can only be written by CPU1 in RDP level 0 or RDP level 1.
When the system is secure (ESE = 1), this register is further more protected by the PRIVMODE. When privilege protection is enabled in PRIVMODE, this register provides write access privilege and can only be written by a privileged access. Unprivileged write access is ignored and an illegal access event is generated. Unprivileged read access is still allowed.
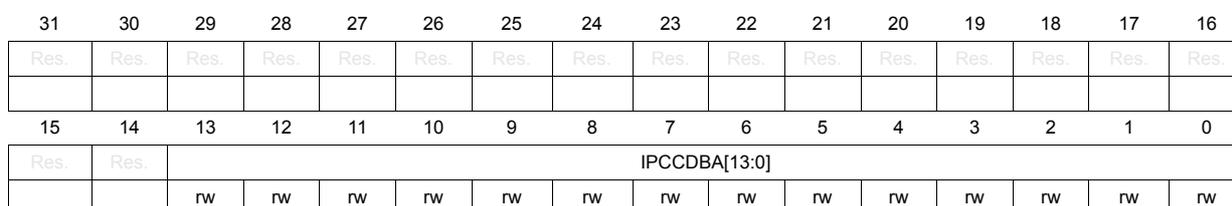
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | IPCCDBA[13:0] | |||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | ||
Bits 31:14 Reserved, must be kept at reset value.
Bits 13:0 IPCCDBA[13:0] : IPCC mailbox data buffer base address offset
IPCCDBA can be used by software to indicate the IPCC buffer structure base address.
Definition and resolution is fully under software control.
4.10.16 FLASH CPU2 access control register (FLASH_C2ACR)
Address offset: 0x05C
Reset value: 0x0000 0600

| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| PES | Res. | Res. | Res. | ICRST | Res. | ICEN | PRFTEN | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| rw | rw | rw | rw |
Bits 31:16 Reserved, must be kept at reset value.
Bit 15 PES : CPU2 program/erase suspend request
0: Flash program and erase operations granted
1: Any new flash program and erase operation is suspended until this bit and the same bit in FLASH_ACR are cleared. The PESD bit in FLASH_SR and FLASH_C2SR are set when at least one PES bit in FLASH_ACR or FLASH_C2ACR is set.
Bits 14:12 Reserved, must be kept at reset value.
Bit 11 ICRST : CPU2 instruction cache reset
0: CPU2 instruction cache not reset
1: CPU2 instruction cache reset
This bit can be written only when the instruction cache is disabled.
Bit 10 Reserved, must be kept at reset value.
Bit 9 ICEN : CPU2 instruction cache enable
0: CPU2 instruction cache disabled
1: CPU2 instruction cache enabled
Bit 8 PRFTEN : CPU2 prefetch enable.
0: CPU2 prefetch disabled
1: CPU2 prefetch enabled.
Bits 7:0 Reserved, must be kept at reset value.
4.10.17 FLASH CPU2 status register (FLASH_C2SR)
Address offset: 0x060
Reset value: 0x0000 0000
Access: no wait state. Word, half-word and byte access.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PESD | CFGBSY | Res. | BSY |
| r | r | r | |||||||||||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | RDERR | Res. | Res. | Res. | Res. | FASTERR | MISSERR | PGSERR | SIZERR | PGAERR | WRPERR | PROGERR | Res. | OPERR | EOP |
| rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 | rc_w1 |
Bits 31:20 Reserved, must be kept at reset value.
Bit 19 PESD : program/erase operation suspended
This bit is set and reset by hardware. This bit is set when at least one PES bit in FLASH_ACR or FLASH_C2ACR is set.
This bit is cleared when both PES in FLASH_ACR and FLASH_C2ACR are cleared.
When set, new program or erase operations are not started.
Bit 18 CFGBSY : program or erase configuration busy
This bit is set and reset by hardware (set when first word is sent and reset when program operation completes or is interrupt by an error).
When set, the program and erase settings in PG, and PNB in FLASH_C2CR are used (busy) and may not be changed. A flash program or erase operation is ongoing.
When reset, program and erase settings in PG and PNB in FLASH_C2CR may be modified.
Bit 17 Reserved, must be kept at reset value.
Bit 16 BSY : Busy
This bit indicates that a flash operation requested in FLASH_C2CR is in progress. This bit is set on the beginning of a flash operation and reset when the operation finishes or when an error occurs.
Bit 15 Reserved, must be kept at reset value.
Bit 14 RDERR : PCROP read errorThis bit is set by hardware when an address to be read through the D-bus belongs to a read protected area of the flash memory (PCROP protection). An interrupt is generated if RDERRIE is set in FLASH_CR.
This bit is cleared by writing 1.
Bits 13:10 Reserved, must be kept at reset value.
Bit 9 FASTERR : fast programming errorThis bit is set by hardware when a fast programming sequence (activated by FSTPG) is interrupted due to an error (alignment, size, write protection or data miss). The corresponding status bit (PGAERR, SIZERR, WRPERR or MISSERR) is set at the same time.
This bit is cleared by writing 1.
Bit 8 MISSERR : fast programming data miss errorIn fast programming mode, 32 double-words (256 bytes) must be sent to the flash memory successively, and the new data must be sent to the flash memory logic control before the current data is fully programmed. This bit is set by hardware when the new data is not present in time.
This bit is cleared by writing 1.
Bit 7 PGSERR : programming sequence errorThis bit is set by hardware when a write access to the flash memory is performed by the code while PG or FSTPG have not been set previously. This bit is also set by hardware when PROGERR, SIZERR, PGAERR, WRPERR, MISSERR or FASTERR is set due to a previous programming error.
This bit is cleared by writing 1.
Bit 6 SIZERR : size errorThis bit is set by hardware when the size of the access is a byte or half-word during a program or a fast program sequence. Only double-word programming is allowed (consequently: word access).
This bit is cleared by writing 1.
Bit 5 PGAERR : programming alignment errorThis bit is set by hardware when the data to program cannot be contained in the same double-word (64-bit) flash memory in case of standard programming, or if there is a change of page during fast programming.
This bit is cleared by writing 1.
Bit 4 WRPERR : write protection errorThis bit is set by hardware when an address to be erased/programmed belongs to a write-protected part (by WRP, PCROP or RDP Level 1) of the flash memory.
This bit is cleared by writing 1.
Bit 3 PROGERR : programming errorThis bit is set by hardware when a double-word address to be programmed contains a value different from 0xFFFF FFFF FFFF FFFF before programming, except if the double-word data to write is 0x0000 0000 0000 0000.
This bit is cleared by writing 1.
Bit 2 Reserved, must be kept at reset value.
Bit 1 OPERR : operation errorThis bit is set by hardware when a flash memory operation (program/erase) completes unsuccessfully.
This bit is set only if error interrupts are enabled (ERRIE = 1) and cleared by writing 1.
Bit 0 EOP : end of operation
This bit is set by hardware when one or more flash memory operation (program/erase) has been completed successfully.
This bit is set only if the end of operation interrupts are enabled (EOPIE = 1) and cleared by writing 1.
4.10.18 FLASH CPU2 control register (FLASH_C2CR)
Address offset: 0x064
Reset value: 0xC000 0000
Access: no wait state when no flash memory operation is ongoing. Word, half-word and byte access.
This register cannot be modified when CFGBSY is set in FLASH_C2SR.
- • When PESD is cleared in FLASH_C2SR, the register write access is stalled until CFGBSY is cleared (for example by the other CPU).
- • When PESD is set in FLASH_C2SR, the register write access causes a bus error.
- • When PESD is set in FLASH_C2SR but there is no ongoing program or erase operation, the register write access is completed. The requested program or erase operation is suspended, BSY/CFGBSY is asserted and remains 1 until suspend is deactivated. Consequently, PESD bit goes back to 0 and the suspended operation completes.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | RDERRIE | ERRIE | EOPIE | Res. | Res. | Res. | Res. | Res. | FSTPG | Res. | STRT |
| rw | rw | rw | rw | rs | |||||||||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | PNB[6:0] | MER | PER | PG | ||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | ||||||
Bits 31:27 Reserved, must be kept at reset value.
Bit 26 RDERRIE : PCROP read error interrupt enable
This bit enables the interrupt generation when RDERR in FLASH_SR is set to 1.
0: PCROP read error interrupt disabled
1: PCROP read error interrupt enabled
Bit 25 ERRIE : error interrupt enable
This bit enables the interrupt generation when OPERR in FLASH_SR is set to 1.
0: OPERR error interrupt disabled
1: OPERR error interrupt enabled
Bit 24 EOPIE : end of operation interrupt enable
This bit enables the interrupt generation when EOP in FLASH_SR is set to 1.
0: EOP Interrupt disabled
1: EOP Interrupt enabled
Bits 23:19 Reserved, must be kept at reset value.
Bit 18 FSTPG : fast programming
0: Fast programming disabled
1: Fast programming enabled
Bit 17 Reserved, must be kept at reset value.
Bit 16 STRT : start
When set, this bit triggers an erase operation. If MER and PER bits are reset and the STRT bit is set, an unpredictable behavior may occur without generating any error flag. This condition is forbidden.
This bit is set only by software and is cleared when BSY is cleared in FLASH_SR.
When the system is secure (ESE = 1) starting operations by the CPU1, involving secure flash pages is rejected and a bus error is generated.
Bits 15:10 Reserved, must be kept at reset value.
Bits 9:3 PNB[6:0] : page number selection
These bits select the 2-Kbyte page to erase.
0x00: page 0
0x01: page 1
...
0x7F: page 127
Bit 2 MER : mass erase
This bit triggers the mass erase (all user pages) when set.
Bit 1 PER : page erase
0: page erase disabled
1: page erase enabled
Bit 0 PG : programming
0: Flash programming disabled
1: Flash programming enabled
4.10.19 FLASH secure flash start address register (FLASH_SFR)
Address offset: 0x080
Reset value: 0xFFFF EFFF
Default reset value from ST production is given as 0bX111 1111 XXXX XXXX 111X 1111 XXXX XXXX, the option bits are loaded with user values from the flash memory at power-on reset release.
When the system is secure (ESE = 1), this register provides write access security and can only be written by the CPU2. A write access from the CPU1 is ignored and an illegal access event is generated. On any read access the register value is returned.
When the system is secure (ESE = 1), this register is further more protected by the PRIVMODE. When privilege protection is enabled in PRIVMODE, this register provides write access privilege and can only be written by a privileged access. Unprivileged write access from is ignored and an illegal access event is generated. Unprivileged read access is still allowed.
This register, except for the DDS bit, is further write protected by HDPADIS, when HDPAD = 0. The write protected bits can only be written when HDPADIS = 0. When HDPADIS = 1, write access is ignored. Read access returns register data.
Written values are only taken into account after OBL.
There are no read restrictions.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| SUBGHSPISD | Res. | Res. | Res. | Res. | Res. | Res. | Res. | HDPAD | HDPISA[6:0] | ||||||
| r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | |||||||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | DDS | Res. | Res. | Res. | Res. | FSD | SFSA[6:0] | ||||||
| r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | r/w | |||||||
Bit 31 SUBGHSPISD : sub-GHz radio SPI security disable
When FSD = 1, the sub-GHz radio SPI security is disabled whatever the value of this SUBGHSPISD bit.
This bit is write protected when HDPAD = 0 and HDPADIS = 1.
0 (and FSD = 0): sub-GHz radio SPI security enabled
1 (and FSD = 0): sub-GHz radio SPI security disabled
Bits 30:24 Reserved, must be kept at reset value.
Bit 23 HDPAD : user flash memory hide protection area disable
When FSD = 1, the user flash memory hide protection area is disabled whatever the value of this HDPAD bit.
This bit is write protected when HDPAD = 0 and HDPADIS = 1.
0 (and FSD = 0): User flash memory hide protection area enabled. HDPISA[6:0] contains the start address of the first 2-Kbyte page of the user flash memory hide protection area.
1 (and FSD = 0): User flash memory hide protection area disabled
Bits 22:16 HDPISA[6:0] : user flash memory hide protection area start address
This bit is write protected when HDPAD = 0 and HDPADIS = 1.
When FSD = HDPAD = 0, the user flash memory hide protection area enabled.
HDPISA[6:0] contain the start address of the first 2-Kbyte page of the user flash memory hide protection area.
0x00: Flash memory hide protection start address offset 0x0000 0000
0x01: Flash memory hide protection start address offset 0x0000 0800
...
0x7F: Flash memory hide protection start address offset 0x0003 F800
Bits 15:13 Reserved, must be kept at reset value.
Bit 12 DDS : CPU2 debug access disable
0: CPU2 debug access enabled. (when also enabled by C2SWDBGEN)
1: CPU2 debug access disabled.
Bits 11:8 Reserved, must be kept at reset value.
Bit 7 FSD : Flash memory security disabled.
This bit is write protected when HDPAD = 0 and HDPADIS = 1.
0: System and flash memory secure (flash memory secure area given by SFSA[6:0])
1: System and flash memory non-secure
Bits 6:0 SFSA[6:0] : secure flash memory start address
This bit is write protected when HDPAD = 0 and HDPADIS = 1.
When FSD = 0, the system and flash memory are secure. SFSA[6:0] contains the page number of the first 2-Kbyte page of the secure flash memory area.
0x00: secure flash memory start address offset 0x0000 0000
0x01: secure flash memory start address offset 0x0000 0800
...
0x7F: secure flash memory start address offset 0x0003 F800
4.10.20 FLASH secure SRAM start address and CPU2 reset vector register (FLASH_SRRVR)
Address offset: 0x084
Reset value: 0xFFFF 8000
Default reset value from ST production is given. Subsequently, 0bXXXX XXX1 XXXX XX11 XXXX XXXX XXXX XXXX The option bits are loaded with user values from the flash memory at power-on reset release.
When the system is secure (ESE = 1), this register provides write access security and can only be written by the CPU2. A write access from the CPU1 is ignored and an illegal access event is generated. On any read access, the register value is returned.
When the system is secure (ESE = 1), this register is further more protected by the PRIVMODE. When privilege protection is enabled in PRIVMODE, this register provides write access privilege and can only be written by a privileged access. Unprivileged write access from is ignored and an illegal access event is generated. Unprivileged read access is still allowed.
This register, except for C2OPT and SBRV bits, is further write protected by HDPADIS when HDPAD = 0. Write protected bits can only be written when HDPADIS = 0. When HDPADIS = 1, write access is ignored. Read access returns register data.
C2OPT and SBRV bits are further protected by C2BOOT_LOCK,. The protected bits can only be accessed when C2BOOT_LOCK = 0. When C2BOOT_LOCK = 1, write access is ignored and read access returns register data.
Written values are only taken into account after OBL.
There are no read restrictions.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| C2OPT | NBRSD | SNBRSA[4:0] | Res. | BRSD | SBRSA[4:0] | Res. | Res. | ||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | |||
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| SBRV[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bit 31 C2OPT : CPU2 boot reset vector memory selection
This bit can only be accessed by software when C2BOOT_LOCK = 0
0: SBRV offset addresses SRAM1 or SRAM2, from start address 0x2000 0000 + SBRV.
Note: SBRV offset value must be kept within the SRAM area.
1: SBRV offset addresses the flash memory, from start address 0x0800 0000 + SBRV.
Bit 30 NBRSD : “non-backup” SRAM1 security disable
This bit is write protected when HDPAD = 0 and HDPADIS = 1.
When FSD = 1, SRAM1 is non-secure whatever the value of this NBRSD bit.
0 (and FSD = 0): SRAM1 is secure. SNBRSA[4:0] contains the start address of the first 1-Kbyte page of the secure “non-backup” SRAM1 area.
1 (and FSD = 0): SRAM1 is non-secure.
Bits 29:25 SNBRSA[4:0] : secure “non-backup” SRAM1 start address
This bit is write protected when HDPAD = 0 and HDPADIS = 1.
When FSD = NBRSD = 0, SRAM1 is secure. SNBRSA[4:0] contains the start address of the first 1-Kbyte page of the secure “non-backup” SRAM1 area.
0x00: “non-backup” SRAM1 start address offset 0x0000 0000
0x01: “non-backup” SRAM1 start address offset 0x0000 0400
...
0x1F: “non-backup” SRAM1 start address offset 0x0000 7C00
Bit 24 Reserved, must be kept at reset value.
Bit 23 BRSD : “backup” SRAM2 security disable
This bit is write protected when HDPAD = 0 and HDPADIS = 1.
When FSD = 1, SRAM2 is non-secure whatever the value of this BRSD bit.
0 (and FSD = 0): SRAM2 is secure. SBRSA[4:0] contains the start address of the first 1-Kbyte page of the secure “backup” SRAM2 area.
1 (and FSD = 0): SRAM2 is non-secure.
Bits 22:18 SBRSA[4:0] : secure “backup” SRAM2 start address
This bit is write protected when HDPAD = 0 and HDPADIS = 1.
When FSD = BRSD = 0, SRAM2 is secure. SBRSA[4:0] contains the start address of the first 1-Kbyte page of the secure backup SRAM2 area.
0x00: “backup” SRAM2 start address offset 0x0000 0000
0x01: “backup” SRAM2 start address offset 0x0000 0400
...
0x1F: “backup” SRAM2 start address offset 0x0000 7C00
Bits 17:16 Reserved, must be kept at reset value.
Bits 15:0 SBRV[15:0] : CPU2 boot reset vector
This bit can only be accessed by software when C2BOOT_LOCK = 0
Contains the word (4 bytes) aligned CPU2 boot reset start address offset within the selected memory area by C2OPT.
0x0000: CPU2 boot address offset 0x0000 0000
0x0001: CPU2 boot address offset 0x0000 0004
...
0x1FFF: CPU2 boot address offset 0x0000 7FFC
....
0xFFFF: CPU2 boot address offset 0x0003 FFFC
4.10.21 FLASH register map
Table 25. Flash interface register map and reset values
| Offset | Register name | 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 | 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0x000 | FLASH_ACR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | EMPTY | PES | Res. | Res. | DORST | ICRST | DCEN | ICEN | PRFTEN | Res. | Res. | Res. | Res. | Res. | Res. | Res. | LATENCY [2:0] |
| Reset value | 0 | 0 | 0 | 0 | 1 | 1 | 0 | 0 | 0 | 0 | |||||||||||||||||||||||
| 0x004 | FLASH_ACR2 | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | C2SWDBGEN HDPADIS PRIVMODE |
| Reset value | X | 0 | 0 | ||||||||||||||||||||||||||||||
| 0x008 | FLASH_KEYR | KEYR[31:0] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x00C | FLASH_OPTKEYR | OPTKEY[31:0] | |||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |
| 0x010 | FLASH_SR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PESD | CFGBSY | Res. | BSY | OPTVERR | RDERR | OPTNV | Res. | Res. | Res. | FASTERR | MISSERR | PGSERR | SIZERR | PGAERR | WRPERR | PROGERR | Res. | OPERR | EOP |
| Reset value | X | X | X | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||||||||||||||||||
| 0x014 | FLASH_CR | LOCK | OPTLOCK | Res. | Res. | OBL_LAUNCH | RDERRIE | ERRIE | EOPTE | Res. | Res. | Res. | Res. | FSTPG | OPTSTRT | STRT | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PNB[6:0] | MER | PER | PG | ||||||
| Reset value | 1 | 1 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||||||
| 0x018 | FLASH_ECCR | ECCD | ECCC | Res. | CPUID [2:0] | Res. | ECCOIE | Res. | Res. | Res. | SYSF_ECC | Res. | Res. | Res. | ADDR_ECC[16:0] | ||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||||||||||
| 0x020 | FLASH_OPTR | C2BOOT_LOCK | BOOT_LOCK | Res. | Res. | nBOOT0 | nSWBOOT0 | SRAM_RST | SRAM2_PE | nBOOT1 | Res. | Res. | Res. | WWDG_SW | IWDG_STDBY | IWDG_STOP | IWDG_SW | Res. | nRST_SHDW | nRST_STDBY | nRST_STOP | BOR_LEV [2:0] | ESE | RDP[7:0] | |||||||||
| Reset value | 0 | 0 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 0 | 0 | 0 | 0 | 1 | 0 | 1 | 0 | 1 | 0 | 1 | 0 | |||||||
| 0x024 | FLASH_PCROP1ASR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PCROP1A_STR[7:0] | |||||||||
| Reset value | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | |||||||||||||||||||||||
| 0x028 | FLASH_PCROP1AER | PCROP_RDP | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | PCROP1A_END[7:0] | |||||||||
| Reset value | 1 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||||||||||||||||||||||
| 0x02C | FLASH_WRP1AR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WRP1A_END[6:0] | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WRP1A_STR[6:0] | |||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | ||||||||||||||||||
Table 25. Flash interface register map and reset values (continued)
| Offset | Register name | 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 | 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0x030 | FLASH_WRP1BR | Res | Res | Res | Res | Res | Res | Res | Res | Res | WRP1B_END[6:0] | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | WRP1B_STRT[6:0] | |||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 1 | 1 | 1 | 1 | 1 | 1 | ||||||||||||||||||||
| 0x034 | FLASH_PCROP1BSR | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | PCROP1B_STRT[7:0] | |||||
| Reset value | 1 | 1 | 1 | 1 | 1 | 1 | |||||||||||||||||||||||||||
| 0x038 | FLASH_PCROP1BER | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | PCROP1B_END[7:0] | |||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | |||||||||||||||||||||||||||
| 0x03C | FLASH_IPCCBR | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | IPCCDBA[13:0] | ||||||||||
| Reset value | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | |||||||||||||||||||||||
| 0x040 to 0x058 | Reserved | Reserved. | |||||||||||||||||||||||||||||||
| 0x05C | FLASH_C2ACR | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | PES | Res | Res | Res | ICRST | Res | ICEN | PRFTEN | Res | Res | Res | Res | Res | Res | Res | Res |
| Reset value | 0 | 0 | 1 | 0 | |||||||||||||||||||||||||||||
| 0x060 | FLASH_C2SR | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | Res | PESD | CFGBSY | BSY | Res | Res | RDERR | Res | Res | Res | Res | FASTERR | MISSERR | PGSERR | SIZERR | PGAERR | WRPERR | PROGERR | Res | OPERERR | EOP |
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||||||||||||||||||
| 0x064 | FLASH_C2CR | Res | Res | Res | Res | Res | RDERRIE | ERRIE | EOPIE | Res | Res | Res | Res | Res | FSTPG | STRT | Res | Res | Res | Res | Res | Res | Res | PNB[6:0] | MER | PER | PG | ||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||||||||||||||||||
| 0x068 to 0x07C | Reserved | Reserved. | |||||||||||||||||||||||||||||||
| 0x080 | FLASH_SFR | SUBGHZSPID | Res | Res | Res | Res | Res | Res | HDPAD | HDPASA[6:0] | Res | Res | Res | DDS | Res | Res | Res | Res | FSD | SFSA[6:0] | |||||||||||||
| Reset value | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 0 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | |||||||||||||||
| 0x084 | FLASH_SRRVR | C2OPT | NBRSD | SNBRSA[4:0] | Res | BRSD | SBRSA[4:0] | Res | Res | SBRV[15:0] | |||||||||||||||||||||||
| Reset value | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 1 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||