19. True random number generator (RNG)
19.1 Introduction
The RNG is a true random number generator that continuously provides 32-bit entropy samples, based on an analog noise source. It can be used by the application as a live entropy source to build a NIST compliant deterministic random bit generator (DRBG).
The RNG true random number generator has been tested using NIST statistical test suite SP800-22 rev1a (April 2010).
19.2 RNG main features
- • The RNG delivers 32-bit true random numbers, produced by an analog entropy source post-processed with linear-feedback shift registers (LFSR).
- • In the NIST configuration, it produces one 32-bit random samples every 42 RNG clock cycles(dedicated clock).
- • It allows embedded continuous basic health tests with associated error management
- – Includes too low sampling clock detection and repetition count tests.
- • It can be disabled to reduce power consumption.
- • It has an AMBA AHB slave peripheral, accessible through 32-bit word single accesses only (else an AHB bus error is generated). Warning! any write not equal to 32 bits might corrupt the register content.
19.3 RNG functional description
19.3.1 RNG block diagram
Figure 116 shows the RNG block diagram.
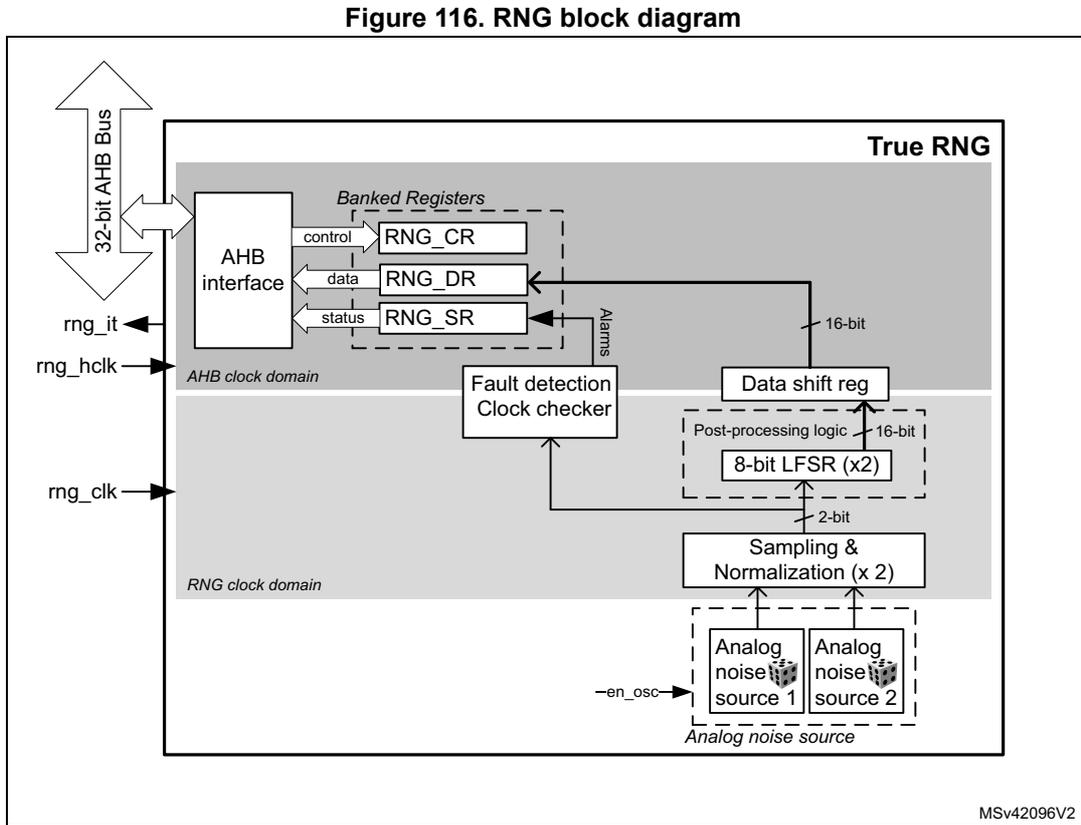
Figure 116. RNG block diagram
MSV42096V2
19.3.2 RNG internal signals
Table 121 describes a list of useful-to-know internal signals available at the RNG level, not at the STM32 product level (on pads).
Table 121. RNG internal input/output signals
| Signal name | Signal type | Description |
|---|---|---|
| rng_it | Digital output | RNG global interrupt request |
| rng_hclk | Digital input | AHB clock |
| rng_clk | Digital input | RNG dedicated clock, asynchronous to rng_hclk |
19.3.3 Random number generation
The true random number generator (RNG) delivers truly random data through its AHB interface at deterministic intervals. Within its boundary the RNG implements the entropy source model pictured on Figure 117 , and provides three main functions to the application:
- • Collects the bitstring output of the entropy source box
- • Obtains samples of the noise source for validation purpose
- • Collects error messages from continuous health tests
Figure 117. Entropy source model
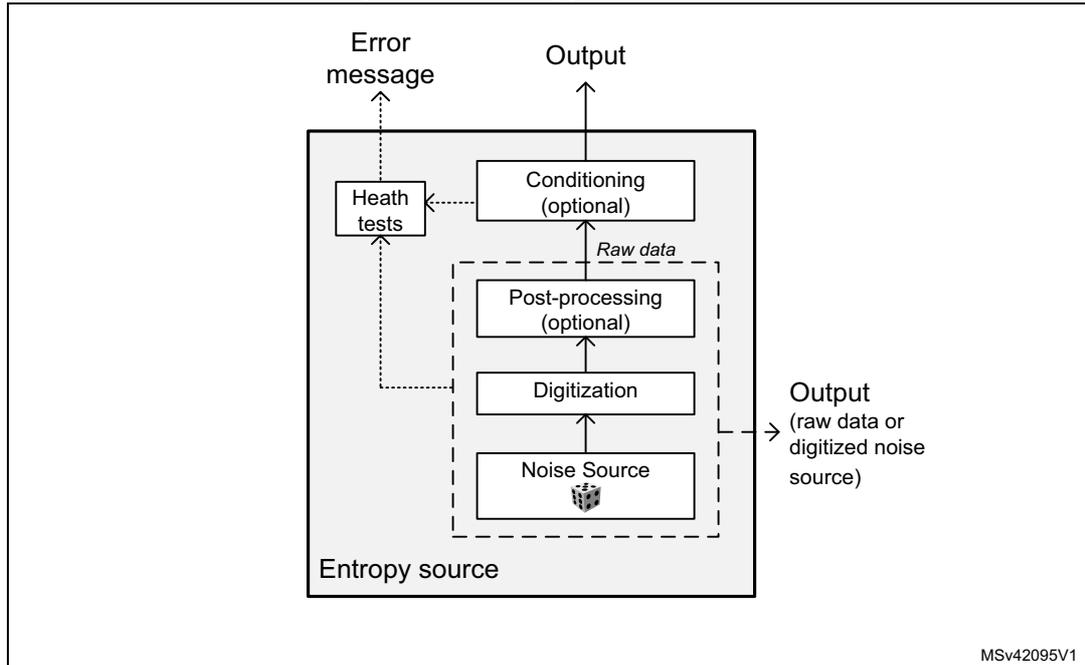
The main components of the RNG are:
- • A source of physical randomness (analog noise source)
- • A digitization stage for this analog noise source
- • A stage delivering post-processed noise source (raw data)
- • An output buffer for the raw data. If further cryptographic conditioning is required by the application it needs to be performed by software.
- • An optional output for the digitized noise source (unbuffered, on digital pads)
- • Basic health tests on the digitized noise source
The components pictured above are detailed hereafter.
Noise source
The noise source is the component that contains the non-deterministic, entropy-providing activity that is ultimately responsible for the uncertainty associated with the bitstring output by the entropy source. It is composed of:
- • Two analog noise sources, each based on three XORed free-running ring oscillator outputs. It is possible to disable those analog oscillators to save power, as described in Section 19.3.8 .
- • A sampling stage of these outputs clocked by a dedicated clock input (rng_clk), delivering a 2-bit raw data output.
This noise source sampling is independent to the AHB interface clock frequency (rng_hclk).
Note: In Section 19.6 the recommended RNG clock frequencies are given.
Post processing
The sample values obtained from a true random noise source consist of 2-bit bitstrings. Because this noise source output is biased, the RNG implements a post-processing component that reduces that bias to a tolerable level.
The RNG post-processing consists of two stages, applied to each noise source bits:
- • The RNG takes half of the bits from the sampled noise source, and half of the bits from inverted sampled noise source. Thus, if the source generates more '1' than '0' (or the opposite), it is filtered
- • A linear feedback shift register (LFSR) performs a whitening process, producing 8-bit strings.
This component is clocked by the RNG clock.
The times required between two random number generations, and between the RNG initialization and availability of first sample are described in Section 19.5 .
Output buffer
The RNG_DR data output register can store up to two 16-bit words, which have been output from the post-processing component (LFSR). In order to read back 32-bit random samples, it is required to wait 42 RNG clock cycles.
Whenever a random number is available through the RNG_DR register, the DRDY flag changes from 0 to 1. This flag remains high until the output buffer becomes empty after reading one word from the RNG_DR register.
Note: When interrupts are enabled an interrupt is generated when this data ready flag transitions from 0 to 1. Interrupt is then cleared automatically by the RNG as explained above.
Health checks
This component ensures that the entire entropy source (with its noise source) starts then operates as expected, obtaining assurance that failures are caught quickly and with a high probability and reliability.
The RNG implements the following health check features.
- 1. Continuous health tests, running indefinitely on the output of the noise source
- – Repetition count test, flagging an error when:
- a) One of the noise source has provided more than 64 consecutive bits at a constant value (“0” or “1”)
- b) One of the noise sources has delivered more than 32 consecutive occurrence of two bits patterns (“01” or “10”)
- – Repetition count test, flagging an error when:
- 2. Vendor specific continuous test
- – Real-time “too slow” sampling clock detector, flagging an error when one RNG clock cycle is smaller than AHB clock cycle divided by 16.
The CECS and SECS status bits in the RNG_SR register indicate when an error condition is detected, as detailed in Section 19.3.7 .
Note: An interrupt can be generated when an error is detected.
19.3.4 RNG initialization
When a hardware reset occurs the following chain of events occurs:
- 1. The analog noise source is enabled, and the logic starts sampling the analog output after four RNG clock cycles, filling LFSR shift register and associated 16-bit post-processing shift register.
- 2. The output buffer is refilled automatically according to the RNG usage.
The associated initialization time can be found in Section 19.5 .
19.3.5 RNG operation
Normal operation
To run the RNG using interrupts, the following steps are recommended:
- 1. Enable the interrupts by setting the IE bit in the RNG_CR register. At the same time, enable the RNG by setting the bit RNGEN=1.
- 2. An interrupt is now generated when a random number is ready or when an error occurs. Therefore, at each interrupt, check that:
- – No error occurred. The SEIS and CEIS bits must be set to 0 in the RNG_SR register.
- – A random number is ready. The DRDY bit must be set to 1 in the RNG_SR register.
- – If the above two conditions are true the content of the RNG_DR register can be read.
To run the RNG in polling mode following steps are recommended:
- 1. Enable the random number generation by setting the RNGEN bit to “1” in the RNG_CR register.
- 2. Read the RNG_SR register and check that:
- – No error occurred (the SEIS and CEIS bits must be set to 0)
- – A random number is ready (the DRDY bit must be set to 1)
- 3. If above conditions are true read the content of the RNG_DR register.
Note: When data is not ready (DRDY = 0) RNG_DR returns zero. It is recommended to always verify that RNG_DR is different from zero. Because when it is the case a seed error occurred between RNG_SR polling and RND_DR output reading (rare event).
Low-power operation
If the power consumption is a concern to the application, low-power strategies can be used, as described in Section 19.3.8 .
Software post-processing
If a NIST approved DRBG with 128 bits of security strength is required an approved random generator software must be built around the RNG true random number generator.
19.3.6 RNG clocking
The RNG runs on two different clocks: the AHB bus clock and a dedicated RNG clock.
The AHB clock is used to clock the AHB banked registers and the post-processing component. The RNG clock is used for noise source sampling. Recommended clock configurations are detailed in Section 19.6: RNG entropy source validation .
Note: When the CED bit in the RNG_CR register is set to 0, the RNG clock frequency must be higher than the AHB clock frequency divided by 16, otherwise the clock checker always flags a clock error (CECS = 1 in the RNG_SR register).
See Section 19.3.1: RNG block diagram for details (AHB and RNG clock domains).
19.3.7 Error management
In parallel to random number generation a health check block verifies the correct noise source behavior and the frequency of the RNG source clock as detailed in this section. Associated error state is also described.
Clock error detection
When the clock error detection is enabled (CED = 0) and if the RNG clock frequency is too low, the RNG sets to 1 both the CEIS and CECS bits to indicate that a clock error occurred. In this case, the application must check that the RNG clock is configured correctly (see Section 19.3.6: RNG clocking ) and then it must clear the CEIS bit interrupt flag. The CECS bit is automatically cleared when the clocking condition is normal.
Note: The clock error has no impact on generated random numbers that is the application can still read the RNG_DR register.
CEIS is set only when CECS is set to 1 by RNG.
Noise source error detection
When a noise source (or seed) error occurs, the RNG stops generating random numbers and sets to 1 both SEIS and SECS bits to indicate that a seed error occurred. If a value is available in the RNG_DR register, it must not be used as it may not have enough entropy.
In order to fully recover from a seed error application must clear the SEIS bit by writing it to “0”, then clear and set the RNGEN bit to reinitialize and restart the RNG.
19.3.8 RNG low-power use
If power consumption is a concern, the RNG can be disabled as soon as the DRDY bit is set to “1” by setting the RNGEN bit to “0” in the RNG_CR register. The 32-bit random value stored in the RNG_DR register is still available. If a new random is needed the application needs to re-enable the RNG and wait for 42+4 RNG clock cycles.
When disabling the RNG the user deactivates all the analog seed generators, whose power consumption is given in the datasheet electrical characteristics section.
19.4 RNG interrupts
In the RNG an interrupt can be produced on the following events:
- • Data ready flag
- • Seed error, see Section 19.3.7: Error management
- • Clock error, see Section 19.3.7: Error management
Dedicated interrupt enable control bits are available as shown in Table 122 .
Table 122. RNG interrupt requests
| Interrupt acronym | Interrupt event | Event flag | Enable control bit | Interrupt clear method |
|---|---|---|---|---|
| RNG | Data ready flag | DRDY | IE | None (automatic) |
| Seed error flag | SEIS | IE | Write 0 to SEIS. | |
| Clock error flag | CEIS | IE | Write 0 to CEIS |
The user can enable or disable the above interrupt sources individually by changing the mask bits or the general interrupt control bit IE in the RNG_CR register. The status of the individual interrupt sources can be read from the RNG_SR register.
Note: Interrupts are generated only when RNG is enabled.
19.5 RNG processing time
The RNG can produce one 32-bit random numbers every 42 RNG clock cycles.
After enabling or re-enabling the RNG using the RNGEN bit, it takes 46 RNG clock cycles before random data are available.
19.6 RNG entropy source validation
19.6.1 Introduction
In order to assess the amount of entropy available from the RNG, STMicroelectronics has tested the peripheral using NIST SP800-22 rev1a statistical tests. The results can be provided on demand or the customer can reproduce the tests.
For more information on running this NIST statistical test suite, refer to STM32 microcontrollers random number generation validation using NIST statistical test suite application note (AN4230), available on STMicroelectronics website.
19.6.2 Validation conditions
STMicroelectronics has tested the RNG true random number generator in the following conditions:
- • RNG clock rng_clk= 48 MHz (CED bit = ‘0’ in RNG_CR register) and rng_clk = 400 kHz (CED bit = ‘1’ in RNG_CR register).
Table 123. RNG configurations
| Configuration | RNG_CR bits | Loop number (N) | RNG_HTCR register | RNG_NSCR register | |||||
|---|---|---|---|---|---|---|---|---|---|
| NISTC bit | RNG_CONFIG1 [5:0] | CLKDIV [3:0] | RNG_CONFIG2 [2:0] (1) | RNG_CONFIG3 [3:0] (2) | CED bit | ||||
| A | Refer to NIST compliant RNG configuration table in AN4230 available from www.st.com . This application note also indicates if this configuration is part of an existing NIST SP800-90B Entropy Certificate listed on https://csrc.nist.gov/projects/cryptographic-module-validation-program . | ||||||||
| B | 1 | 0x18 | 0x0 (3) | 0x0 | 0x0 | 0 | 1 | 0x0000 NA (4) | default |
| C | 0 | 0x0F | 0x0 | 0xD | 0 | 2 | default | ||
- 1. 0x1 value is recommended instead of 0x0 for RNG_CONFIG2[2:0], when RNG power consumption is critical. See the end of Section 19.3.8 for details.
- 2. RNG_CONFIG3[1:0] defines the loop number N: 0x0 corresponds to N=1, 0x1 to N=2, 0x2 to N=3, 0x3 to N=4
- 3. The noise source sampling must be NA or less. Hence, if the RNG clock is different from NA, this value of CLKDIV must be adapted. See the CLKDIV bitfield description in Section 19.7.1 for details.
- 4. This value can be fixed in the RNG driver (it does not depend upon the STM32 product).
19.6.3 Data collection
In order to run statistical tests, it is required to collect samples from the entropy source at the raw data level as well as at the output of the entropy source. For details on data collection and the running of statistical test suites refer to AN4230 “ STM32 microcontrollers random number generation validation using NIST statistical test suite ” available from www.st.com .
In bypass mode the bits [31:30] of the fourth word are always stuck at 0. Hence the continuous capture of samples is started from the fifth word.
19.7 RNG registers
The RNG is associated with a control register, a data register and a status register.
19.7.1 RNG control register (RNG_CR)
Address offset: 0x000
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | CED | Res. | IE | RNGEN | Res. | Res. |
| rw | rw | rw |
Bits 31:6 Reserved, must be kept at reset value.
Bit 5 CED : Clock error detection
0: Clock error detection enabled
1: Clock error detection is disabled
The clock error detection cannot be enabled nor disabled on-the-fly when the RNG is enabled, that is to enable or disable CED, the RNG must be disabled.
Bit 4 Reserved, must be kept at reset value.
Bit 3 IE : Interrupt enable
0: RNG interrupt is disabled
1: RNG interrupt is enabled. An interrupt is pending as soon as the DRDY, SEIS, or CEIS is set in the RNG_SR register.
Bit 2 RNGEN : True random number generator enable
0: True random number generator is disabled. Analog noise sources are powered off and logic clocked by the RNG clock is gated.
1: True random number generator is enabled.
Bits 1:0 Reserved, must be kept at reset value.
19.7.2 RNG status register (RNG_SR)
Address offset: 0x004
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | SEIS | CEIS | Res. | Res. | SECS | CECS | DRDY |
| rc_w0 | rc_w0 | r | r | r |
Bits 31:7 Reserved, must be kept at reset value.
Bit 6 SEIS : Seed error interrupt status
This bit is set at the same time as SECS. It is cleared by writing 0. Writing 1 has no effect.
0: No faulty sequence detected
1: At least one faulty sequence is detected. See SECS bit description for details.
An interrupt is pending if IE = 1 in the RNG_CR register.
Bit 5 CEIS : Clock error interrupt status
This bit is set at the same time as CECS. It is cleared by writing 0. Writing 1 has no effect.
0: The RNG clock is correct ( \( f_{\text{RNGCLK}} > f_{\text{HCLK}}/16 \) )
1: The RNG is detected too slow ( \( f_{\text{RNGCLK}} < f_{\text{HCLK}}/16 \) )
An interrupt is pending if IE = 1 in the RNG_CR register.
Bits 4:3 Reserved, must be kept at reset value.
Bit 2 SECS : Seed error current status
0: No faulty sequence has currently been detected. If the SEIS bit is set, this means that a faulty sequence was detected and the situation has been recovered.
1: One of the noise sources has provided more than 64 consecutive bits at a constant value ("0" or "1"), or more than 32 consecutive occurrence of two bits patterns ("01" or "10")
Bit 1 CECS : Clock error current status
0: The RNG clock is correct ( \( f_{RNGCLK} > f_{HCLK}/16 \) ). If the CEIS bit is set, this means that a slow clock was detected and the situation has been recovered.
1: The RNG clock is too slow ( \( f_{RNGCLK} < f_{HCLK}/16 \) ).
Note: CECS bit is valid only if the CED bit in the RNG_CR register is set to 0.
Bit 0 DRDY : Data ready
0: The RNG_DR register is not yet valid, no random data is available.
1: The RNG_DR register contains valid random data.
Once the RNG_DR register has been read, this bit returns to 0 until a new random value is generated.
If IE=1 in the RNG_CR register, an interrupt is generated when DRDY = 1.
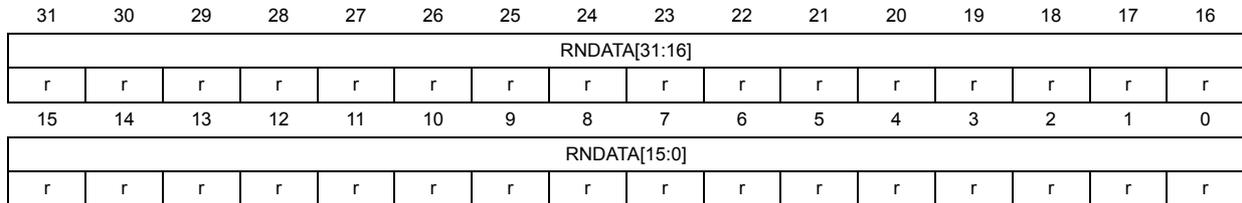
19.7.3 RNG data register (RNG_DR)
Address offset: 0x008
Reset value: 0x0000 0000
The RNG_DR register is a read-only register that delivers a 32-bit random value when read. After being read, this register delivers a new random value after 42 periods of RNG clock if the output FIFO is empty.
The content of this register is valid when the DRDY = 1 and the value is not 0x0, even if RNGEN = 0.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| RNDATA[31:16] | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| RNDATA[15:0] | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
Bits 31:0 RNDATA[31:0] : Random data
32-bit random data, which are valid when DRDY = 1. When DRDY = 0, the RNDATA value is zero.
When DRDY is set, it is recommended to always verify that RNG_DR is different from zero.
The zero value means that a seed error occurred between RNG_SR polling and RND_DR output reading (a rare event).
19.7.4 RNG register map
Table 124. RNG register map and reset map
| Offset | Register name | 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 | 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 | |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0x000 | RNG_CR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | CED | Res. | IE | RNGEN | Res. | Res. |
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | ||||||||||||||||||||||||||||
| 0x004 | RNG_SR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | SEIS | CEIS | Res. | Res. | Res. | SECS | CECS | DRDY |
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||||||||||||||||||||||||||
| 0x008 | RNG_DR | RNDATA[31:0] | ||||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||
Refer to Section 2.2: Memory organization for the register boundary addresses.