15. AES hardware accelerator (AES)
15.1 Introduction
The AES hardware accelerator (AES) encrypts or decrypts data, using an algorithm and implementation fully compliant with the advanced encryption standard (AES) defined in Federal information processing standards (FIPS) publication 197.
Multiple chaining modes are supported (ECB, CBC, CTR), for key size of 128 bits.
The AES accelerator is a 32-bit AHB peripheral. It supports DMA single transfers for incoming and outgoing data (two DMA channels required).
The AES peripheral provides hardware acceleration to AES cryptographic algorithms packaged in STM32 cryptographic library.
AES is an AMBA AHB slave peripheral, accessible through 32-bit word single accesses only (otherwise an AHB bus error is generated and write accesses are ignored).
15.2 AES main features
- • Compliance with NIST “ Advanced encryption standard (AES), FIPS publication 197 ” from November 2001
- • 128-bit data block processing
- • Support for cipher key length of 128-bit
- • Encryption and decryption with multiple chaining modes:
- – Electronic codebook (ECB) mode
- – Cipher block chaining (CBC) mode
- – Counter (CTR) mode
- • 213 clock cycle latency for processing one 128-bit block of data
- • Integrated key scheduler with its key derivation stage (ECB or CBC decryption only)
- • AMBA AHB slave peripheral, accessible through 32-bit word single accesses only
- • 128-bit register for storing the cryptographic key (four 32-bit registers)
- • 128-bit register for storing initialization vector (four 32-bit registers)
- – Used for the initialization vector when AES is configured in CBC mode or for the 32-bit counter initialization when CTR mode is selected
- • 32-bit buffer for data input and output
- • Automatic data flow control with support of single-transfer direct memory access (DMA) using two channels (one for incoming data, one for processed data)
- • Data-swapping logic to support 1-, 8-, 16- or 32-bit data
15.3 AES implementation
The device has a single instance of AES peripheral.
15.4 AES functional description
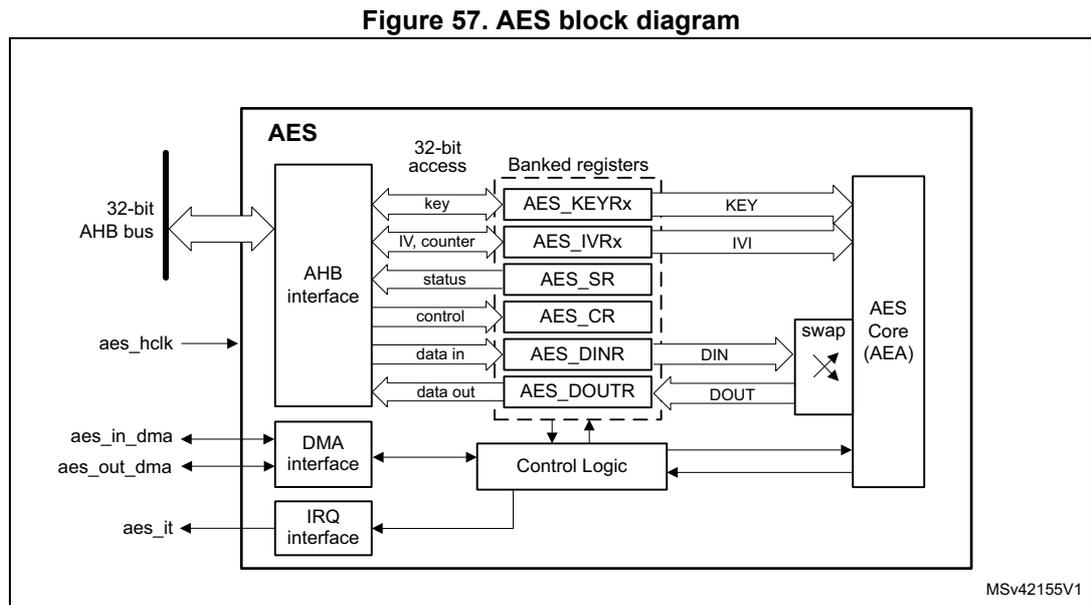
15.4.1 AES block diagram
Figure 57 shows the block diagram of AES.
15.4.2 AES internal signals
Table 68 describes the user relevant internal signals interfacing the AES peripheral.
Table 68. AES internal input/output signals
| Signal name | Signal type | Description |
|---|---|---|
| aes_hclk | digital input | AHB bus clock |
| aes_it | digital output | AES interrupt request |
| aes_in_dma | digital input/output | Input DMA single request/acknowledge |
| aes_out_dma | digital input/output | Output DMA single request/acknowledge |
15.4.3 AES cryptographic core
Overview
The AES cryptographic core consists of the following components:
- • AES algorithm (AEA)
- • key input
- • initialization vector (IV) input
The AES core works on 128-bit data blocks (four words) with 128-bit key length. Depending on the chaining mode, the AES requires zero or one 96-bit initialization vector IV (and a 32-bit counter field).
The AES features the following modes of operation:
- •
Mode 1:
Plaintext encryption using a key stored in the AES_KEYRx registers - •
Mode 2:
ECB or CBC decryption key preparation. It must be used prior to selecting Mode 3 with ECB or CBC chaining modes. The key prepared for decryption is stored automatically in the AES_KEYRx registers. Now the AES peripheral is ready to switch to Mode 3 for executing data decryption. - •
Mode 3:
Ciphertext decryption using a key stored in the AES_KEYRx registers. When ECB and CBC chaining modes are selected, the key must be prepared beforehand, through Mode 2. - •
Mode 4:
ECB or CBC ciphertext single decryption using the key stored in the AES_KEYRx registers (the initial key is derived automatically).
Note: Mode 2 and mode 4 are only used when performing ECB and CBC decryption.
When Mode 4 is selected only one decryption can be done, therefore usage of Mode 2 and Mode 3 is recommended instead.
The operating mode is selected by programming the MODE[1:0] bitfield of the AES_CR register. It may be done only when the AES peripheral is disabled.
Typical data processing
Typical usage of the AES is described in Section 15.4.4: AES procedure to perform a cipher operation on page 342 .
Note: The outputs of the intermediate AEA stages are never revealed outside the cryptographic boundary, with the exclusion of the IVI bitfield.
Chaining modes
The following chaining modes are supported by AES, selected through the CHMOD[1:0] bitfield of the AES_CR register:
- • Electronic code book (ECB)
- • Cipher block chaining (CBC)
- • Counter (CTR)
Note: The chaining mode may be changed only when AES is disabled (bit EN of the AES_CR register set).
Principle of each AES chaining mode is provided in the following subsections.
Detailed information is in dedicated sections, starting from Section 15.4.8: AES basic chaining modes (ECB, CBC) .
Electronic codebook (ECB) mode
Figure 58. ECB encryption and decryption principle
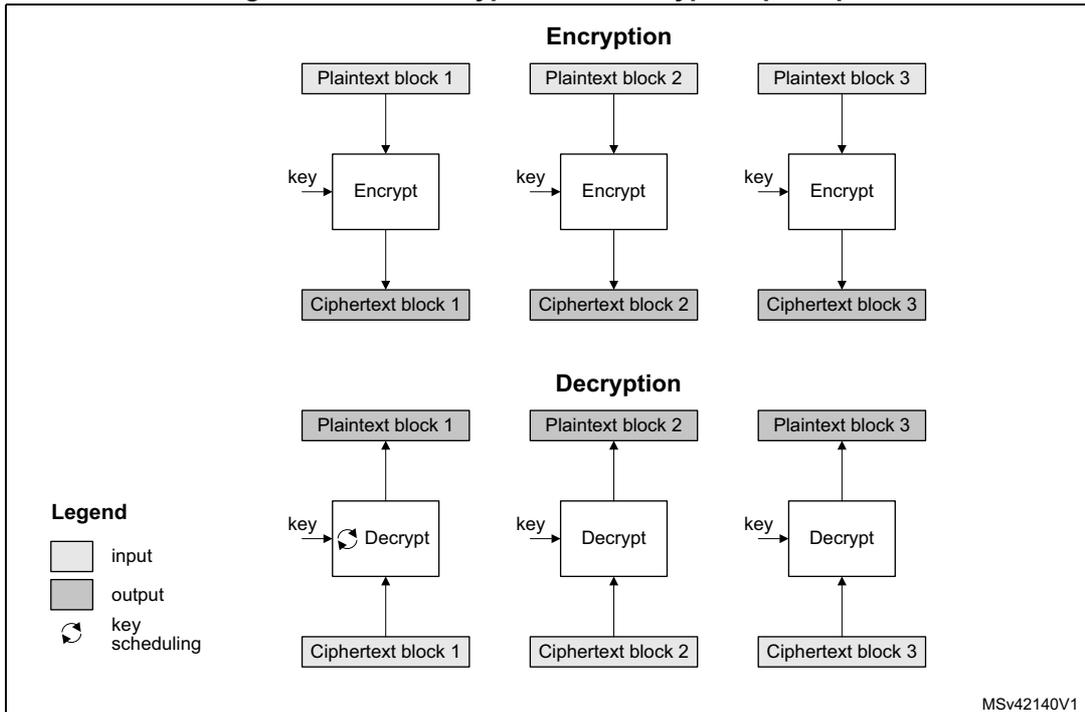
The diagram is divided into two main sections: Encryption and Decryption .
Encryption: Three separate paths are shown. Each path starts with a Plaintext block (1, 2, or 3) in a light gray box. An arrow points down to an Encrypt block. A key is input to the Encrypt block from the left. An arrow points down from the Encrypt block to a Ciphertext block (1, 2, or 3) in a dark gray box.
Decryption: Three separate paths are shown. Each path starts with a Ciphertext block (1, 2, or 3) in a dark gray box at the bottom. An arrow points up to a Decrypt block. A key is input to the Decrypt block from the left. A circular arrow icon is next to the key input, indicating key scheduling. An arrow points up from the Decrypt block to a Plaintext block (1, 2, or 3) in a light gray box.
Legend:
- Light gray box: input
- Dark gray box: output
- Circular arrow icon: key scheduling
MSv42140V1
ECB is the simplest mode of operation. There are no chaining operations, and no special initialization stage. The message is divided into blocks and each block is encrypted or decrypted separately.
Note: For decryption, a special key scheduling is required before processing the first block.
Cipher block chaining (CBC) mode Figure 59. CBC encryption and decryption principle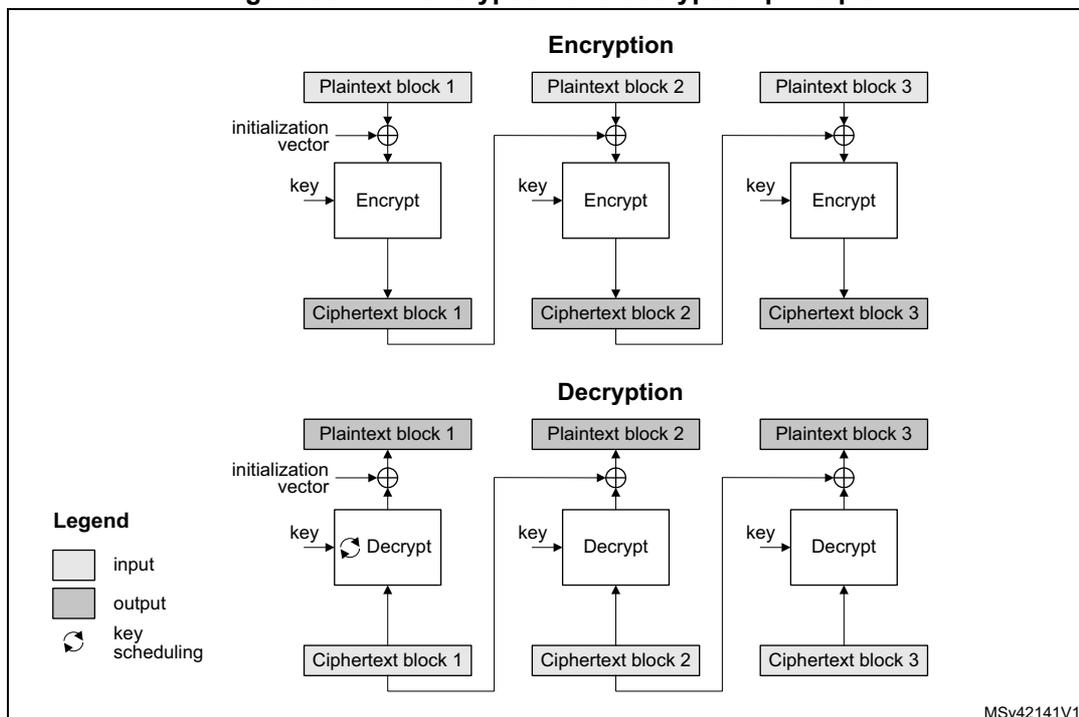
Encryption
initialization vector
key → Encrypt
Decryption
initialization vector
key → Decrypt
Legend
- input
- output
- ↻ key scheduling
MSv42141V1
In CBC mode the output of each block chains with the input of the following block. To make each message unique, an initialization vector is used during the first block processing.
Note: For decryption, a special key scheduling is required before processing the first block.
Counter (CTR) mode
Figure 60. CTR encryption and decryption principle
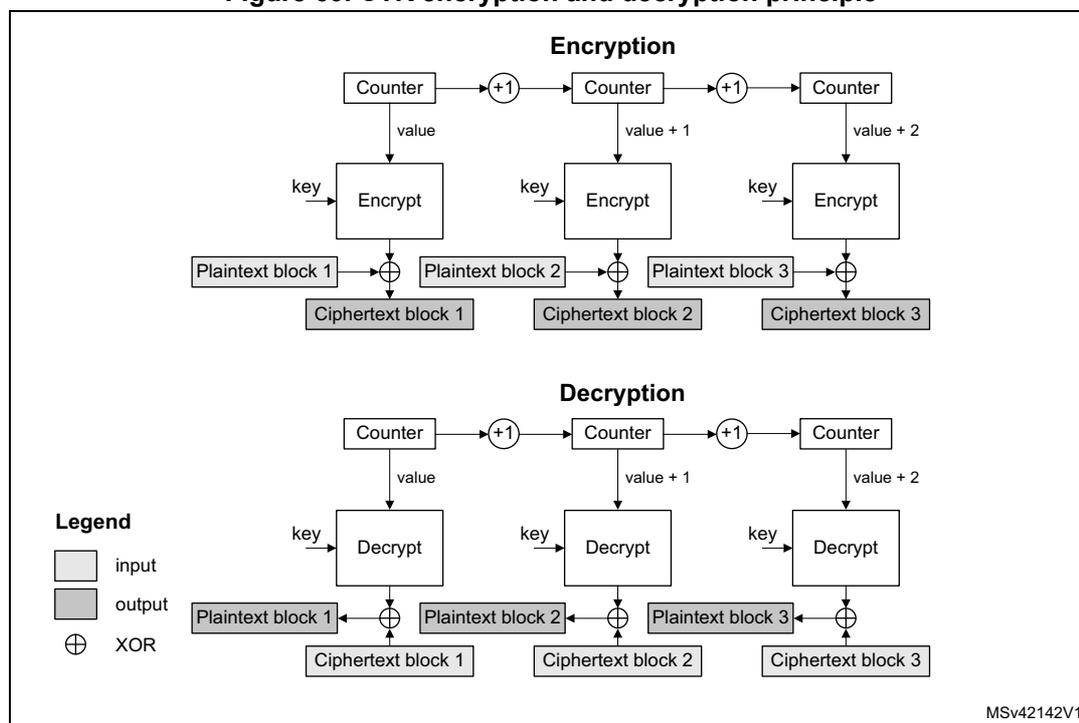
The CTR mode uses the AES core to generate a key stream. The keys are then XORed with the plaintext to obtain the ciphertext as specified in NIST Special Publication 800-38A, Recommendation for Block Cipher Modes of Operation .
Note: Unlike with ECB and CBC modes, no key scheduling is required for the CTR decryption, since in this chaining scheme the AES core is always used in encryption mode for producing the key stream, or counter blocks.
15.4.4 AES procedure to perform a cipher operation
Introduction
A typical cipher operation is explained below. Detailed information is provided in sections starting from Section 15.4.8: AES basic chaining modes (ECB, CBC) .
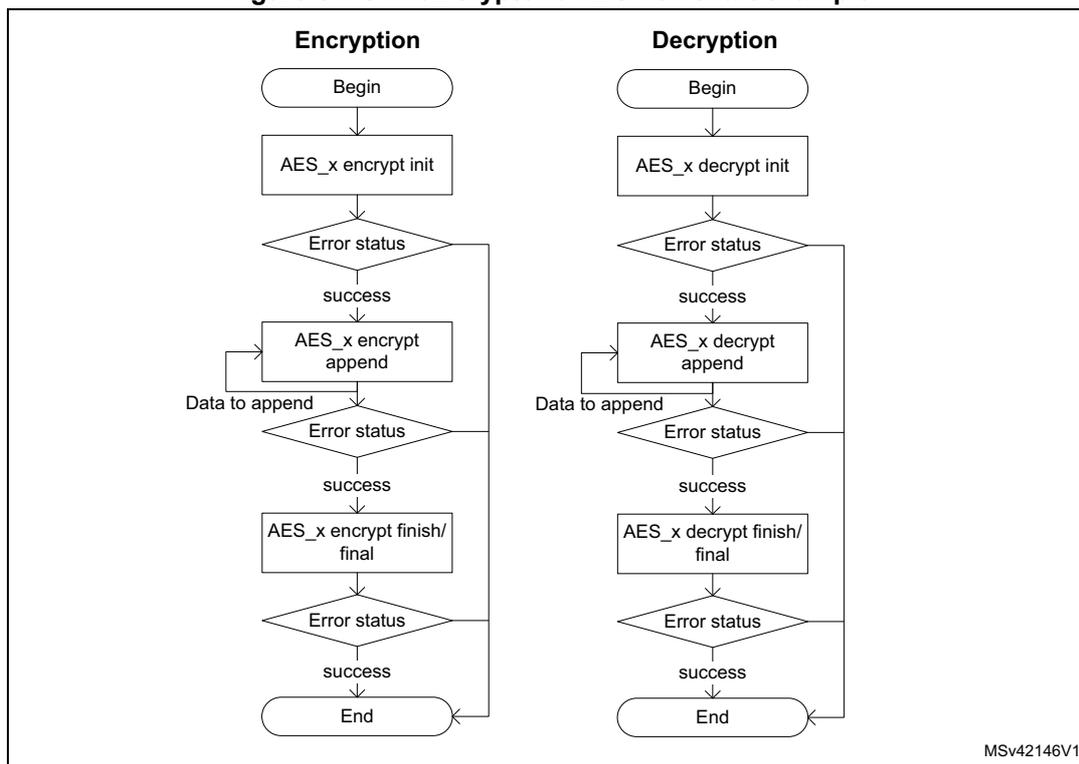
The flowcharts shown in Figure 61 describe the way STM32 cryptographic library implements the AES algorithm. AES accelerates the execution of the AES-128 cryptographic algorithm in ECB, CBC, and CTR operating modes.
Note: For more details on the cryptographic library, refer to the UM1924 user manual “STM32 crypto library” available from www.st.com .
Figure 61. STM32 cryptolib AES flowchart example
graph TD
subgraph Encryption
E1([Begin]) --> E2[AES_x encrypt init]
E2 --> E3{Error status}
E3 -- success --> E4[AES_x encrypt append]
E4 -- "Data to append" --> E5{Error status}
E5 -- success --> E6[AES_x encrypt finish/final]
E6 --> E7{Error status}
E7 -- success --> E8([End])
E3 -- error --> E8
E5 -- error --> E8
E7 -- error --> E8
end
subgraph Decryption
D1([Begin]) --> D2[AES_x decrypt init]
D2 --> D3{Error status}
D3 -- success --> D4[AES_x decrypt append]
D4 -- "Data to append" --> D5{Error status}
D5 -- success --> D6[AES_x decrypt finish/final]
D6 --> D7{Error status}
D7 -- success --> D8([End])
D3 -- error --> D8
D5 -- error --> D8
D7 -- error --> D8
end
MSv42146V1
Initialization of AES
To initialize AES, first disable it by clearing the EN bit of the AES_CR register. Then perform the following steps in any order:
- • Configure the AES mode, by programming the MODE[1:0] bitfield of the AES_CR register.
- – For encryption, Mode 1 must be selected (MODE[1:0] = 00).
- – For decryption, Mode 3 must be selected (MODE[1:0] = 10), unless ECB or CBC chaining modes are used. In this latter case, an initial key derivation of the encryption key must be performed, as described in Section 15.4.5: AES decryption key preparation .
- • Select the chaining mode, by programming the CHMOD[1:0] bitfield of the AES_CR register
- • Write a symmetric key into the AES_KEYRx registers .
- • Configure the data type (1-, 8-, 16- or 32-bit), with the DATATYPE[1:0] bitfield in the AES_CR register.
- • When it is required (for example in CBC or CTR chaining modes), write the initialization vectors into the AES_IVRx register.
Data append
This section describes different ways of appending data for processing, where the size of data to process is not a multiple of 128 bits.
For ECB or CBC mode, refer to Section 15.4.6: AES ciphertext stealing and data padding . The second-last and the last block management in these cases is more complex than in the sequence described in this section.
Data append through polling
This method uses flag polling to control the data append.
For all other cases, the data is appended through the following sequence:
- 1. Enable the AES peripheral by setting the EN bit of the AES_CR register.
- 2. Repeat the following sub-sequence until the payload is entirely processed:
- a) Write four input data words into the AES_DINR register.
- b) Wait until the status flag CCF is set in the AES_SR, then read the four data words from the AES_DOUTR register.
- c) Clear the CCF flag, by setting the CCFC bit of the AES_CR register.
- d) If the data block just processed is the second-last block of the message and the significant data in the last block to process is inferior to 128 bits, pad the remainder of the last block with zeros
- 3. Discard the data that is not part of the payload, then disable the AES peripheral by clearing the EN bit of the AES_CR register.
Note: Up to three wait cycles are automatically inserted between two consecutive writes to the AES_DINR register, to allow sending the key to the AES processor.
Data append using interrupt
The method uses interrupt from the AES peripheral to control the data append, through the following sequence:
- 1. Enable interrupts from AES by setting the CCFIE bit of the AES_CR register.
- 2. Enable the AES peripheral by setting the EN bit of the AES_CR register.
- 3. Write first four input data words into the AES_DINR register.
- 4. Handle the data in the AES interrupt service routine, upon interrupt:
- a) Read four output data words from the AES_DOUTR register.
- b) Clear the CCF flag and thus the pending interrupt, by setting the CCFC bit of the AES_CR register
- c) If the data block just processed is the second-last block of an message and the significant data in the last block to process is inferior to 128 bits, pad the remainder of the last block with zeros. Then proceed with point 4e).
- d) If the data block just processed is the last block of the message, discard the data that is not part of the payload, then disable the AES peripheral by clearing the EN bit of the AES_CR register and quit the interrupt service routine.
- e) Write next four input data words into the AES_DINR register and quit the interrupt service routine.
Note: AES is tolerant of delays between consecutive read or write operations, which allows, for example, an interrupt from another peripheral to be served between two AES computations.
Data append using DMA
With this method, all the transfers and processing are managed by DMA and AES. To use the method, proceed as follows:
- 1. Prepare the last four-word data block (if the data to process does not fill it completely), by padding the remainder of the block with zeros.
- 2. Configure the DMA controller so as to transfer the data to process from the memory to the AES peripheral input and the processed data from the AES peripheral output to the memory, as described in Section 15.4.13: AES DMA interface . Configure the DMA controller so as to generate an interrupt on transfer completion.
- 3. Enable the AES peripheral by setting the EN bit of the AES_CR register
- 4. Enable DMA requests by setting the DMAINEN and DMAOUTEN bits of the AES_CR register.
- 5. Upon DMA interrupt indicating the transfer completion, get the AES-processed data from the memory.
Note: The CCF flag has no use with this method, because the reading of the AES_DOUTR register is managed by DMA automatically, without any software action, at the end of the computation phase.
15.4.5 AES decryption key preparation
For an ECB or CBC decryption, a key for the first round of decryption must be derived from the key of the last round of encryption. This is why a complete key schedule of encryption is required before performing the decryption. This key preparation is not required for AES decryption in modes other than ECB or CBC.
Recommended method is to select the Mode 2 by setting to 01 the MODE[1:0] bitfield of the AES_CR (key process only), then proceed with the decryption by setting MODE[1:0] to 10 (Mode 3, decryption only). Mode 2 usage is described below:
- 1. Disable the AES peripheral by clearing the EN bit of the AES_CR register.
- 2. Select Mode 2 by setting to 01 the MODE[1:0] bitfield of the AES_CR. The CHMOD[1:0] bitfield is not significant in this case because this key derivation mode is independent of the chaining algorithm selected.
- 3. Write the AES_KEYRx registers (128bits) with encryption key, as shown in Figure 62 . Writes to the AES_IVRx registers have no effect.
- 4. Enable the AES peripheral, by setting the EN bit of the AES_CR register.
- 5. Wait until the CCF flag is set in the AES_SR register.
- 6. Derived key is available in AES core, ready to use for decryption. Application can also read the AES_KEYRx register to obtain the derived key if needed, as shown in Figure 62 (the processed key is loaded automatically into the AES_KEYRx registers).
Note: The AES is disabled by hardware when the derivation key is available.
To restart a derivation key computation, repeat steps 3, 4, 5 and 6 .
Figure 62. Encryption key derivation for ECB/CBC decryption (Mode 2)
![Figure 62: Encryption key derivation for ECB/CBC decryption (Mode 2). The diagram shows a sequence of operations: Input phase (4 write operations into AES_KEYRx[31:0] with WR EK3, WR EK2, WR EK1, WR EK0), Computation phase (Wait until flag CCF = 1, with EN = 1 into AES_CR), and Output phase (optional, 4 read operations of AES_KEYRx[31:0] with RD DK3, RD DK2, RD DK1, RD DK0). The input phase is labeled MSB to LSB, and the output phase is also labeled MSB to LSB. A legend defines EK as encryption key (4 words EK3, ..., EK0) and DK as decryption key (4 words DK3, ..., DK0). The diagram is labeled MS18937V2.](/RM0377-STM32L0x1/c747f23d3c916cb48bebaa14372b8d75_img.jpg)
Diagram illustrating the encryption key derivation process for ECB/CBC decryption (Mode 2). The process is divided into three phases:
- Input phase:
4 write operations into
AES_KEYRx[31:0](MSB to LSB):WR EK3,WR EK2,WR EK1,WR EK0. - Computation phase:
Wait until flag
CCF = 1. This phase is initiated by settingEN = 1intoAES_CR. - Output phase (optional):
4 read operations of
AES_KEYRx[31:0](MSB to LSB):RD DK3,RD DK2,RD DK1,RD DK0. This results in a 128-bit derivation key stored intoAES_KEYRx.
Legend:
- EK = encryption key = 4 words (EK3, ..., EK0)
- DK = decryption key = 4 words (DK3, ..., DK0)
MS18937V2
If the software stores the initial key prepared for decryption, it is enough to do the key schedule operation only once for all the data to be decrypted with a given cipher key.
Note:
Alternative key preparation is to select Mode 4 by setting to 11 the
MODE[1:0]
bitfield of the
AES_CR
register. In this case Mode 3 cannot be used.
15.4.6 AES ciphertext stealing and data padding
When using AES in ECB or CBC modes to manage messages the size of which is not a multiple of the block size (128 bits), ciphertext stealing techniques are used, such as those described in NIST Special Publication 800-38A, Recommendation for Block Cipher Modes of Operation: Three Variants of Ciphertext Stealing for CBC Mode . Since the AES peripheral on the device does not support such techniques, the last two blocks of input data must be handled in a special way by the application.
Note: Ciphertext stealing techniques are not documented in this reference manual.
Similarly, when AES is used in other modes than ECB or CBC, an incomplete input data block (that is, block with input data shorter than 128 bits) must be padded with zeros prior to encryption (that is, extra bits must be appended to the trailing end of the data string). After decryption, the extra bits must be discarded. As AES does not implement automatic data padding operation to the last block , the application must follow the recommendation given in Section 15.4.4: AES procedure to perform a cipher operation on page 342 to manage messages the size of which is not a multiple of 128 bits.
Note:
Padding data are swapped in a similar way as normal data, according to the
DATATYPE[1:0]
field of the
AES_CR
register (see
Section 15.4.10: AES data registers and data swapping on page 355
for details).
15.4.7 AES task suspend and resume
A message can be suspended if another message with a higher priority must be processed. When this highest priority message is sent, the suspended message can resume in both encryption or decryption mode.
Suspend/resume operations do not break the chaining operation and the message processing can resume as soon as AES is enabled again to receive the next data block.
Figure 63 gives an example of suspend/resume operation: Message 1 is suspended in order to send a shorter and higher-priority Message 2.
Figure 63. Example of suspend mode management
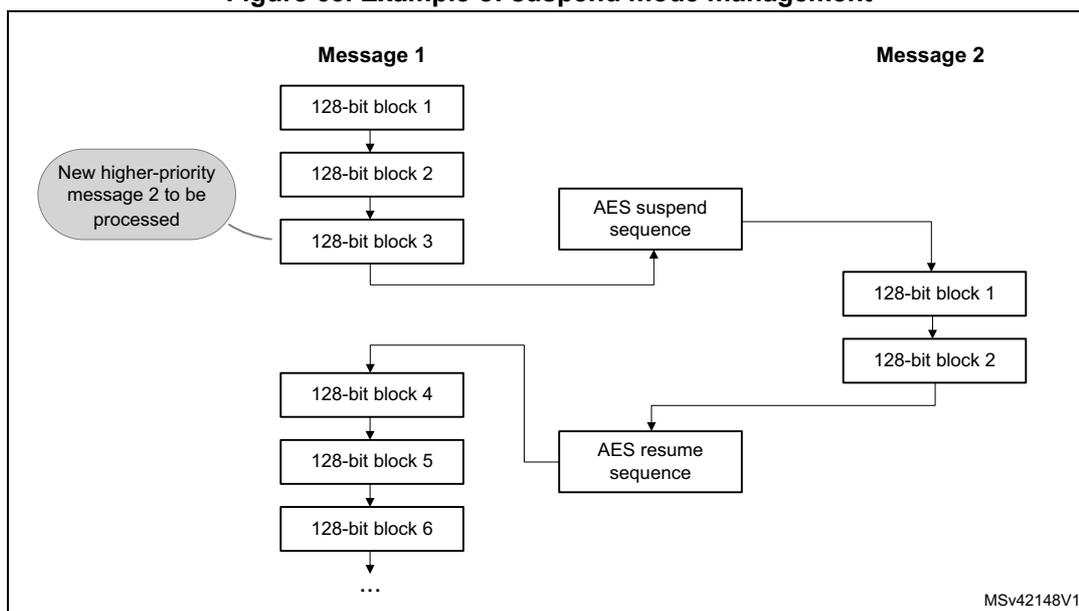
A detailed description of suspend/resume operations is in the sections dedicated to each AES mode.
15.4.8 AES basic chaining modes (ECB, CBC)
Overview
This section gives a brief explanation of the four basic operation modes provided by the AES computing core: ECB encryption, ECB decryption, CBC encryption and CBC decryption. For detailed information, refer to the FIPS publication 197 from November 26, 2001.
Figure 64 illustrates the electronic codebook (ECB) encryption.
Figure 64. ECB encryption
![Figure 64: ECB encryption. The diagram shows two parallel processing paths for Block 1 and Block 2. For Block 1, AES_DINR (plaintext P1) is input to a 'Swap management' block controlled by DATATYPE[1:0], producing I1. I1 is then processed by an 'Encrypt' block using AES_KEYRx (KEY) to produce O1. O1 is then processed by another 'Swap management' block controlled by DATATYPE[1:0] to produce AES_DOUTR (ciphertext C1). The same process is repeated for Block 2, producing I2, O2, and AES_DOUTR (ciphertext C2). A legend indicates that white boxes represent input and grey boxes represent output. The diagram is labeled MSV19105V2.](/RM0377-STM32L0x1/e55bc5b56bfb1b617e15b20ffa1081af_img.jpg)
In ECB encrypt mode, the 128-bit plaintext input data block \( P_x \) in the AES_DINR register first goes through bit/byte/half-word swapping. The swap result \( I_x \) is processed with the AES core set in encrypt mode, using a 128-bit key. The encryption result \( O_x \) goes through bit/byte/half-word swapping, then is stored in the AES_DOUTR register as 128-bit ciphertext.
output data block Cx. The ECB encryption continues in this way until the last complete plaintext block is encrypted.
Figure 65 illustrates the electronic codebook (ECB) decryption.
![Diagram of ECB decryption showing two blocks, Block 1 and Block 2. Each block takes a ciphertext input (C1 or C2) from the AES_DINR register, passes it through a 'Swap management' block (controlled by DATATYPE[1:0]), resulting in an intermediate value (I1 or I2). This value is then processed by a 'Decrypt' block using the AES_KEYRx (KEY). The output of the decrypt block (O1 or O2) is passed through another 'Swap management' block (controlled by DATATYPE[1:0]) to produce the final plaintext output (P1 or P2) in the AES_DOUTR register. A legend indicates that white boxes represent input and grey boxes represent output. The diagram is labeled MSv19106V2.](/RM0377-STM32L0x1/a3ce3e5191a737483aa2635e69dd15ff_img.jpg)
Figure 65. ECB decryption
To perform an AES decryption in the ECB mode, the secret key has to be prepared by collecting the last-round encryption key (which requires to first execute the complete key schedule for encryption), and using it as the first-round key for the decryption of the ciphertext. This preparation is supported by the AES core.
In ECB decrypt mode, the 128-bit ciphertext input data block C1 in the AES_DINR register first goes through bit/byte/half-word swapping. The keying sequence is reversed compared to that of the ECB encryption. The swap result I1 is processed with the AES core set in decrypt mode, using the formerly prepared decryption key. The decryption result goes through bit/byte/half-word swapping, then is stored in the AES_DOUTR register as 128-bit plaintext output data block P1. The ECB decryption continues in this way until the last complete ciphertext block is decrypted.
Figure 66 illustrates the cipher block chaining (CBC) encryption mode.
![Diagram of CBC encryption showing two blocks, Block 1 and Block 2. For Block 1, a plaintext input (P1) from the AES_DINR register is passed through a 'Swap management' block (controlled by DATATYPE[1:0]) to produce P1'. P1' is XOR-ed with the AES_IVRx (init. vector) to produce I1. I1 is then processed by a 'Block cipher encryption' block using the AES_KEYRx (KEY) to produce O1. O1 is passed through another 'Swap management' block (controlled by DATATYPE[1:0]) to produce the ciphertext output (C1) in the AES_DOUTR register. For Block 2, the process is similar, but the XOR step uses the previous ciphertext output (O1) as the IV. A legend indicates that white boxes represent input, grey boxes represent output, and a circle with a cross represents XOR. The diagram is labeled MSv19107V2.](/RM0377-STM32L0x1/0c115ad7cb24570c52a70ae36de584b0_img.jpg)
Figure 66. CBC encryption
In CBC encrypt mode, the first plaintext input block, after bit/byte/half-word swapping (P1'), is XOR-ed with a 128-bit IVI bitfield (initialization vector and counter), producing the I1 input data for encrypt with the AES core, using a 128- key. The resulting 128-bit output block O1, after swapping operation, is used as ciphertext C1. The O1 data is then XOR-ed with the
second-block plaintext data P2' to produce the I2 input data for the AES core to produce the second block of ciphertext data. The chaining of data blocks continues in this way until the last plaintext block in the message is encrypted.
If the message size is not a multiple of 128 bits, the final partial data block is encrypted in the way explained in Section 15.4.6: AES ciphertext stealing and data padding .
Figure 67 illustrates the cipher block chaining (CBC) decryption mode.
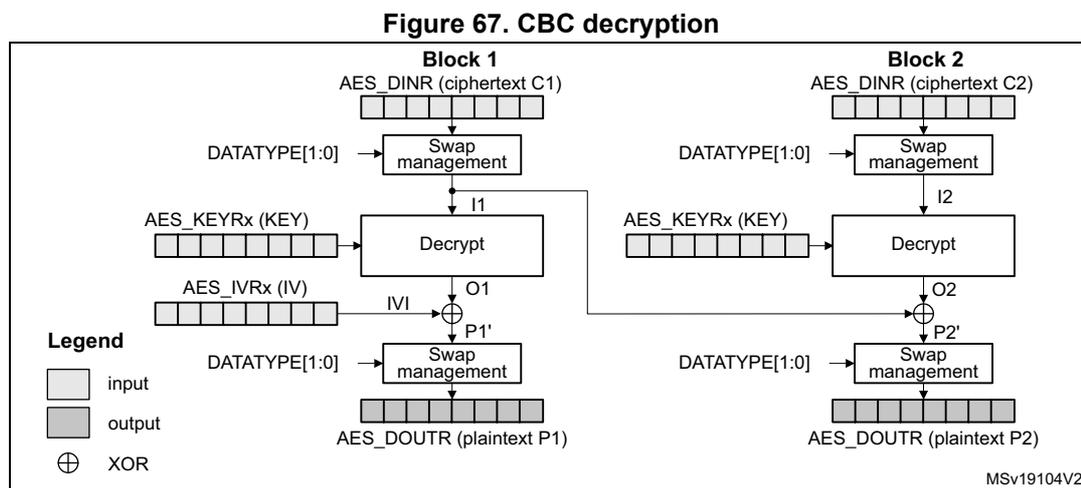
Figure 67. CBC decryption
In CBC decrypt mode, like in ECB decrypt mode, the secret key must be prepared to perform an AES decryption.
After the key preparation process, the decryption goes as follows: the first 128-bit ciphertext block (after the swap operation) is used directly as the AES core input block I1 for decrypt operation, using the 128-bit key. Its output O1 is XOR-ed with the 128-bit IVI field (that must be identical to that used during encryption) to produce the first plaintext block P1.
The second ciphertext block is processed in the same way as the first block, except that the I1 data from the first block is used in place of the initialization vector.
The decryption continues in this way until the last complete ciphertext block is decrypted.
If the message size is not a multiple of 128 bits, the final partial data block is decrypted in the way explained in Section 15.4.6: AES ciphertext stealing and data padding .
For more information on data swapping, refer to Section 15.4.10: AES data registers and data swapping .
ECB/CBC encryption sequence
The sequence of events to perform an ECB/CBC encryption (more detail in Section 15.4.4 ):
- 1. Disable the AES peripheral by clearing the EN bit of the AES_CR register.
- 2. Select the Mode 1 by to 00 the MODE[1:0] bitfield of the AES_CR register and select ECB or CBC chaining mode by setting the CHMOD[1:0] bitfield of the AES_CR register to 00 or 01, respectively. Data type can also be defined, using DATATYPE[1:0] bitfield.
- 3. Write the AES_KEYRx registers (128 bits) with encryption key. Fill the AES_IVRx registers with the initialization vector data if CBC mode has been selected.
- 4. Enable the AES peripheral by setting the EN bit of the AES_CR register.
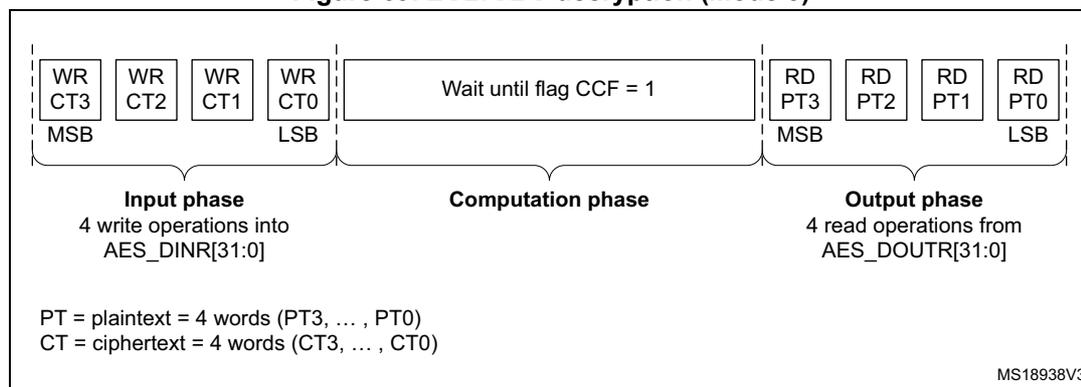
- 5. Write the AES_DINR register four times to input the plaintext (MSB first), as shown in Figure 68 .
- 6. Wait until the CCF flag is set in the AES_SR register.
- 7. Read the AES_DOUTR register four times to get the ciphertext (MSB first) as shown in Figure 68 . Then clear the CCF flag by setting the CCFC bit of the AES_CR register.
- 8. Repeat steps 5,6,7to process all the blocks with the same encryption key.
Figure 68. ECB/CBC encryption (Mode 1)
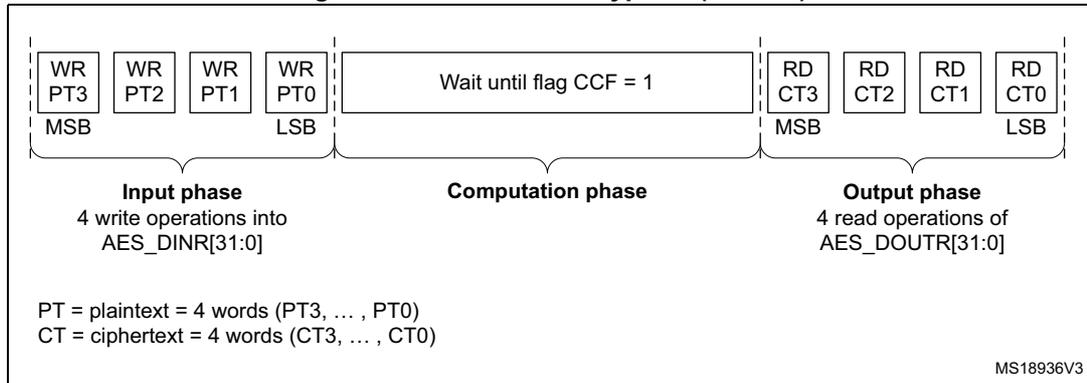
The diagram illustrates the sequence of operations for ECB/CBC encryption in Mode 1. It is divided into three main phases: Input phase, Computation phase, and Output phase.
- Input phase: Consists of four write operations into the AES_DINR register, labeled WR PT3, WR PT2, WR PT1, and WR PT0. These are performed from MSB to LSB. The text below indicates: "Input phase: 4 write operations into AES_DINR[31:0]".
- Computation phase: A central block labeled "Wait until flag CCF = 1". The text below indicates: "Computation phase".
- Output phase: Consists of four read operations from the AES_DOUTR register, labeled RD CT3, RD CT2, RD CT1, and RD CT0. These are performed from MSB to LSB. The text below indicates: "Output phase: 4 read operations of AES_DOUTR[31:0]".
Additional information provided in the diagram:
- PT = plaintext = 4 words (PT3, ... , PT0)
- CT = ciphertext = 4 words (CT3, ... , CT0)
- Reference code: MS18936V3
ECB/CBC decryption sequence
The sequence of events to perform an AES ECB/CBC decryption is as follows (more detail in Section 15.4.4 ):
- 1. Follow the steps described in Section 15.4.5: AES decryption key preparation on page 345 , in order to prepare the decryption key in AES core.
- 2. Disable the AES peripheral by clearing the EN bit of the AES_CR register.
- 3. Select the Mode 3 by setting to 10 the MODE[1:0] bitfield of the AES_CR register and select ECB or CBC chaining mode by setting the CHMOD[1:0] bitfield of the AES_CR register to 00 or 01, respectively. Data type can also be defined, using DATATYPE[1:0] bitfield.
- 4. Write the AES_IVRx registers with the initialization vector (required in CBC mode only).
- 5. Enable AES by setting the EN bit of the AES_CR register.
- 6. Write the AES_DINR register four times to input the cipher text (MSB first), as shown in Figure 69 .
- 7. Wait until the CCF flag is set in the AES_SR register.
- 8. Read the AES_DOUTR register four times to get the plain text (MSB first), as shown in Figure 69 . Then clear the CCF flag by setting the CCFC bit of the AES_CR register.
- Repeat steps 6,7,8 to process all the blocks encrypted with the same key.
Figure 69. ECB/CBC decryption (Mode 3)
The diagram illustrates the ECB/CBC decryption process in Mode 3, divided into three phases:
- Input phase: Four write operations into the AES_DINR[31:0] register. The data is written in four words: WR CT3 (MSB), WR CT2, WR CT1, and WR CT0 (LSB). The plaintext (PT) consists of 4 words (PT3, ..., PT0) and the ciphertext (CT) consists of 4 words (CT3, ..., CT0).
- Computation phase: A period where the user waits until the CCF flag is set to 1.
- Output phase: Four read operations from the AES_DOUTR[31:0] register. The data is read in four words: RD PT3 (MSB), RD PT2, RD PT1, and RD PT0 (LSB).
MS18938V3
Suspend/resume operations in ECB/CBC modes
To suspend the processing of a message, proceed as follows:
- If DMA is used, stop the AES DMA transfers to the IN FIFO by clearing the DMAINEN bit of the AES_CR register.
- If DMA is not used, read four times the AES_DOUTR register to save the last processed block. If DMA is used, wait until the CCF flag is set in the AES_SR register then stop the DMA transfers from the OUT FIFO by clearing the DMAOUTEN bit of the AES_CR register.
- If DMA is not used, poll the CCF flag of the AES_SR register until it becomes 1 (computation completed).
- Clear the CCF flag by setting the CCFC bit of the AES_CR register.
- Save initialization vector registers (only required in CBC mode as AES_IVRx registers are altered during the data processing).
- Disable the AES peripheral by clearing the bit EN of the AES_CR register.
- Save the current AES configuration in the memory (except AES initialization vector values).
- If DMA is used, save the DMA controller status (pointers for IN and OUT data transfers, number of remaining bytes, and so on).
Note: In point 7, the derived key information stored in AES_KEYRx registers can optionally be saved in memory if the interrupted process is a decryption. Otherwise those registers do not need to be saved as the original key value is known by the application
To resume the processing of a message , proceed as follows:
- 1. If DMA is used, configure the DMA controller so as to complete the rest of the FIFO IN and FIFO OUT transfers.
- 2. Ensure that AES is disabled (the EN bit of the AES_CR must be 0).
- 3. Restore the AES_CR and AES_KEYRx register setting, using the values of the saved configuration. In case of decryption, derived key information can be written in AES_KEYRx register instead of the original key value.
- 4. Prepare the decryption key as described in Section 15.4.5: AES decryption key preparation (only required for ECB or CBC decryption). This step is not necessary if derived key information has been loaded in AES_KEYRx registers.
- 5. Restore AES_IVRx registers using the saved configuration (only required in CBC mode).
- 6. Enable the AES peripheral by setting the EN bit of the AES_CR register.
- 7. If DMA is used, enable AES DMA transfers by setting the DMAINEN and DMAOUTEN bits of the AES_CR register.
Alternative single ECB/CBC decryption using Mode 4
The sequence of events to perform a single round of ECB/CBC decryption using Mode 4 is:
- 1. Disable the AES peripheral by clearing the EN bit of the AES_CR register.
- 2. Select the Mode 4 by setting to 11 the MODE[1:0] bitfield of the AES_CR register and select ECB or CBC chaining mode by setting the CHMOD[21:0] bitfield of the AES_CR register to 000 or 001, respectively.
- 3. Select key length of 128 or 256 bits via KEYSIZE bitfield of the AES_CR register.
- 4. Write the AES_KEYRx registers with the encryption key. Write the AES_IVRx registers if the CBC mode is selected.
- 5. Enable the AES peripheral by setting the EN bit of the AES_CR register.
- 6. Write the AES_DINR register four times to input the cipher text (MSB first).
- 7. Wait until the CCF flag is set in the AES_SR register.
- 8. Read the AES_DOUTR register four times to get the plain text (MSB first). Then clear the CCF flag by setting the CCFC bit of the AES_CR register.
Note: When mode 4 is selected mode 3 cannot be used.
In mode 4, the AES_KEYRx registers contain the encryption key during all phases of the processing. No derivation key is stored in these registers. It is stored internally in AES.
15.4.9 AES counter (CTR) mode
Overview
The counter mode (CTR) uses AES as a key-stream generator. The generated keys are then XOR-ed with the plaintext to obtain the ciphertext.
CTR chaining is defined in NIST Special Publication 800-38A, Recommendation for Block Cipher Modes of Operation . A typical message construction in CTR mode is given in Figure 70 .
Figure 70. Message construction in CTR mode
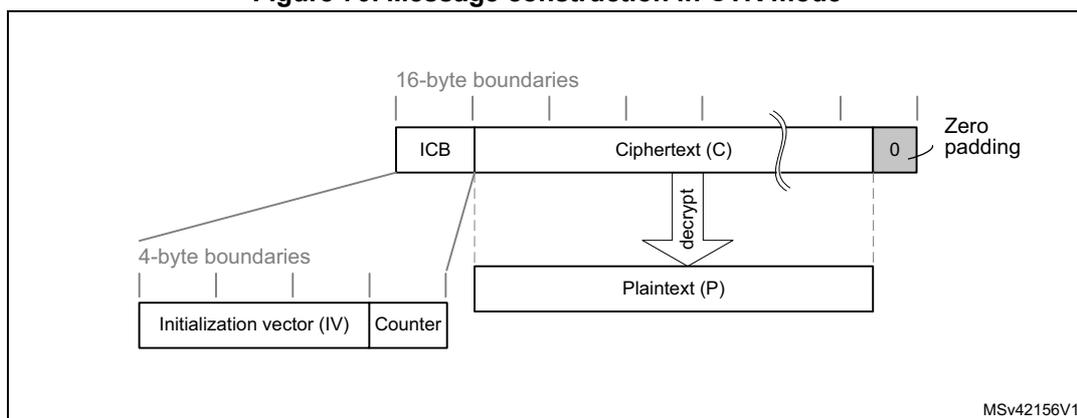
The diagram illustrates the message construction in CTR mode. It shows a 16-byte Initial Counter Block (ICB) followed by Ciphertext (C) and zero padding. The ICB is composed of a 12-byte Initialization vector (IV) and a 4-byte Counter. The Ciphertext (C) is derived from Plaintext (P) via a decrypt operation. The message is structured with 16-byte boundaries for the ICB and Ciphertext, and 4-byte boundaries for the IV and Counter.
The structure of this message is:
- • A 16-byte initial counter block (ICB), composed of two distinct fields:
- – Initialization vector (IV) : a 96-bit value that must be unique for each encryption cycle with a given key.
- – Counter : a 32-bit big-endian integer that is incremented each time a block processing is completed. The initial value of the counter should be set to 1.
- • The plaintext P is encrypted as ciphertext C, with a known length. This length can be non-multiple of 16 bytes, in which case a plaintext padding is required.
CTR encryption and decryption
Figure 71 and Figure 72 describe the CTR encryption and decryption process, respectively, as implemented in the AES peripheral. The CTR mode is selected by writing 10 to the CHMOD[1:0] bitfield of AES_CR register.
Figure 71. CTR encryption
![Figure 71: CTR encryption. The diagram shows the encryption process for two blocks, Block 1 and Block 2. For each block, the AES_IVRx register (containing IV + 32-bit counter) is input to an Encrypt block along with the AES_KEYRx (KEY). The output of the Encrypt block is XORed with the AES_DINR (plaintext) to produce the ciphertext (AES_DOUTR). The counter is incremented by 1 for each block. A Swap management block is used to handle the data type (DATATYPE[1:0]).](/RM0377-STM32L0x1/a7dc4a01f6983360f46e914a81abf97f_img.jpg)
The diagram illustrates the CTR encryption process for two blocks, Block 1 and Block 2. For each block, the AES_IVRx register (containing IV + 32-bit counter) is input to an Encrypt block along with the AES_KEYRx (KEY). The output of the Encrypt block is XORed with the AES_DINR (plaintext) to produce the ciphertext (AES_DOUTR). The counter is incremented by 1 for each block. A Swap management block is used to handle the data type (DATATYPE[1:0]).
Legend
- input
- output
- ⊕ XOR
Figure 72. CTR decryption
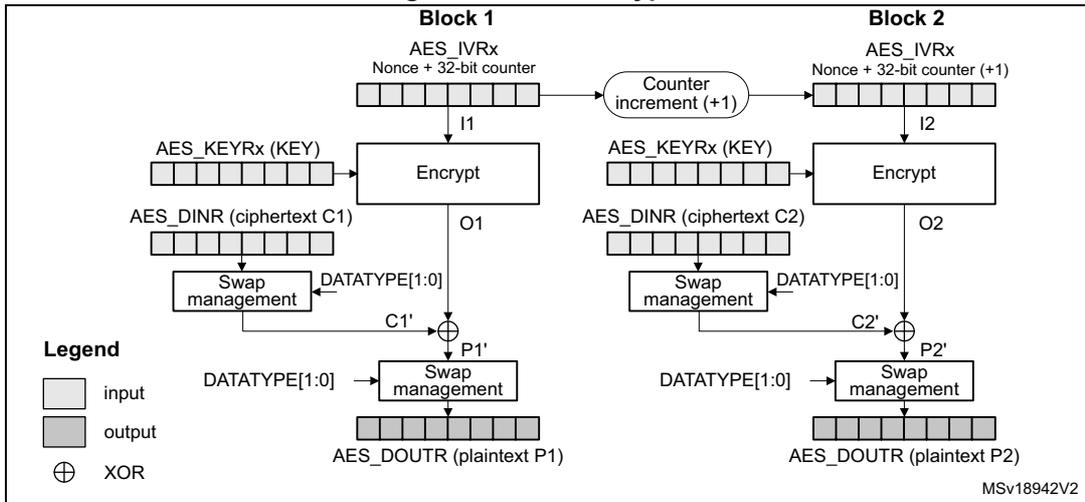
In CTR mode, the cryptographic core output (also called keystream) \( O_x \) is XOR-ed with relevant input block ( \( P_x' \) for encryption, \( C_x' \) for decryption), to produce the correct output block ( \( C_x' \) for encryption, \( P_x' \) for decryption). Initialization vectors in AES must be initialized as shown in Table 69.
Table 69. CTR mode initialization vector definition
| AES_IVR3[31:0] | AES_IVR2[31:0] | AES_IVR1[31:0] | AES_IVR0[31:0] |
|---|---|---|---|
| Nonce[31:0] | Nonce[63:32] | Nonce[95:64] | 32-bit counter = 0x0001 |
Unlike in CBC mode that uses the AES_IVRx registers only once when processing the first data block, in CTR mode AES_IVRx registers are used for processing each data block, and the AES peripheral increments the counter bits of the initialization vector (leaving the nonce bits unchanged).
CTR decryption does not differ from CTR encryption, since the core always encrypts the current counter block to produce the key stream that is then XOR-ed with the plaintext (CTR encryption) or ciphertext (CTR decryption) input. In CTR mode, the MODE[1:0] bitfield settings 11, 10 or 00 default all to encryption mode, and the setting 01 (key derivation) is forbidden.
The sequence of events to perform an encryption or a decryption in CTR chaining mode:
- 1. Ensure that AES is disabled (the EN bit of the AES_CR must be 0).
- 2. Select CTR chaining mode by setting to 10 the CHMOD[1:0] bitfield of the AES_CR register. Set MODE[1:0] bitfield to any value other than 01.
- 3. Initialize the AES_KEYRx registers, and load the AES_IVRx registers as described in Table 69 .
- 4. Set the EN bit of the AES_CR register, to start encrypting the current counter (EN is automatically reset when the calculation finishes).
- 5. If it is the last block, pad the data with zeros to have a complete block, if needed.
- 6. Append data in AES, and read the result. The three possible scenarios are described in Section 15.4.4: AES procedure to perform a cipher operation .
- 7. Repeat the previous step till the second-last block is processed. For the last block, apply the two previous steps and discard the bits that are not part of the payload (if the size of the significant data in the last input block is less than 16 bytes).
Suspend/resume operations in CTR mode
Like for the CBC mode, it is possible to interrupt a message to send a higher priority message, and resume the message that was interrupted. Detailed CBC suspend/resume sequence is described in Section 15.4.8: AES basic chaining modes (ECB, CBC) .
Note: Like for CBC mode, the AES_IVRx registers must be reloaded during the resume operation.
15.4.10 AES data registers and data swapping
Data input and output
A 128-bit data block is entered into the AES peripheral with four successive 32-bit word writes into the AES_DINR register (bitfield DIN[127:0]), the most significant word (bits [127:96]) first, the least significant word (bits [31:0]) last.
A 128-bit data block is retrieved from the AES peripheral with four successive 32-bit word reads from the AES_DOUTR register (bitfield DOUT[127:0]), the most significant word (bits [127:96]) first, the least significant word (bits [31:0]) last.
The 32-bit data word for AES_DINR register or from AES_DOUTR register is organized in big endian order, that is:
- • the most significant byte of a word to write into AES_DINR must be put on the lowest address out of the four adjacent memory locations keeping the word to write, or
- • the most significant byte of a word read from AES_DOUTR goes to the lowest address out of the four adjacent memory locations receiving the word
For using DMA for input data block write into AES, the four words of the input block must be stored in the memory consecutively and in big-endian order, that is, the most significant word on the lowest address. See Section 15.4.13: AES DMA interface .
Data swapping
The AES peripheral can be configured to perform a bit-, a byte-, a half-word-, or no swapping on the input data word in the AES_DINR register, before loading it to the AES processing core, and on the data output from the AES processing core, before sending it to the AES_DOUTR register. The choice depends on the type of data. For example, a byte swapping is used for an ASCII text stream.
The data swap type is selected through the DATATYPE[1:0] bitfield of the AES_CR register. The selection applies both to the input and the output of the AES core.
For different data swap types, Figure 73 shows the construction of AES processing core input buffer data P127..0, from the input data entered through the AES_DINR register, or the construction of the output data available through the AES_DOUTR register, from the AES processing core output buffer data P127..0.
Figure 73. 128-bit block construction with respect to data swap
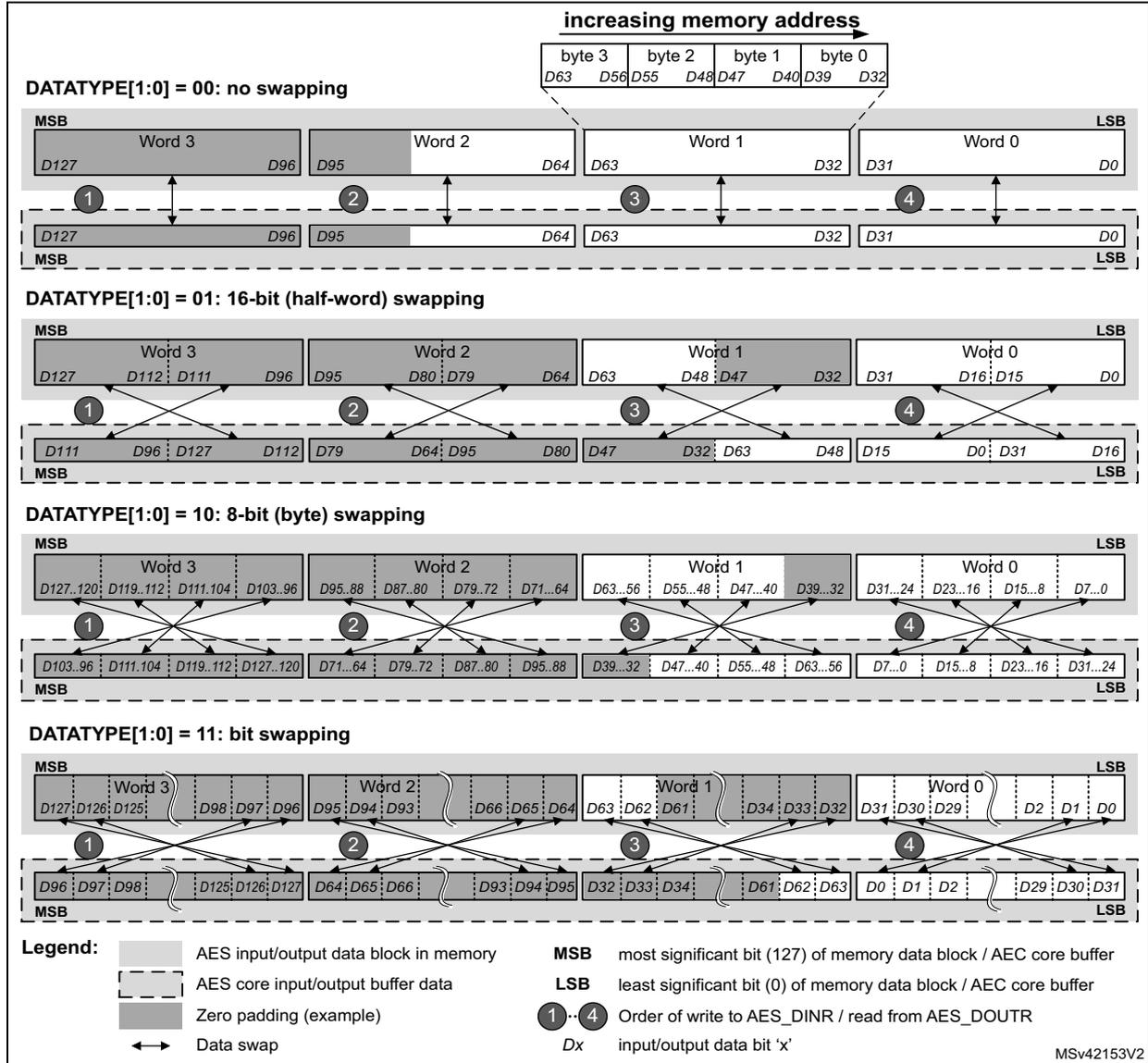
Legend:
- ■ AES input/output data block in memory
- ▭ AES core input/output buffer data
- ▨ Zero padding (example)
- ↔ Data swap
- MSB most significant bit (127) of memory data block / AEC core buffer
- LSB least significant bit (0) of memory data block / AEC core buffer
- ①...④ Order of write to AES_DINR / read from AES_DOUTR
- Dx input/output data bit 'x'
MSv42153V2
Note: The data in AES key registers (AES_KEYRx) and initialization registers (AES_IVRx) are not sensitive to the swap mode selection.
Data padding
Figure 73 also gives an example of memory data block padding with zeros such that the zeroed bits after the data swap form a contiguous zone at the MSB end of the AES core input buffer. The example shows the padding of an input data block containing:
- • 48 message bits, with DATATYPE[1:0] = 01
- • 56 message bits, with DATATYPE[1:0] = 10
- • 34 message bits, with DATATYPE[1:0] = 11
15.4.11 AES key registers
The AES_KEYRx registers store the encryption or decryption key bitfield KEY[127:0]. The data to write to or to read from each register is organized in the memory in little-endian order, that is, with most significant byte on the highest address.
The key is spread over the four registers in little-endian configuration, as shown on Table 70.
Table 70. Key endianness in AES_KEYRx registers
| AES_KEYR3[31:0] | AES_KEYR2[31:0] | AES_KEYR1[31:0] | AES_KEYR0[31:0] |
|---|---|---|---|
| KEY[127:96] | KEY[95:64] | KEY[63:32] | KEY[31:0] |
The key for encryption or decryption may be written into these registers when the AES peripheral is disabled.
The key registers are not affected by the data swapping controlled by DATATYPE[1:0] bitfield of the AES_CR register.
15.4.12 AES initialization vector registers
The four AES_IVRx registers keep the initialization vector input bitfield IVI[127:0]. The data to write to or to read from each register is organized in the memory in little-endian order, that is, with most significant byte on the highest address. The registers are also ordered from lowest address (AES_IVR0) to highest address (AES_IVR3).
The signification of data in the bitfield depends on the chaining mode selected. When used, the bitfield is updated upon each computation cycle of the AES core.
Write operations to the AES_IVRx registers when the AES peripheral is enabled have no effect to the register contents. For modifying the contents of the AES_IVRx registers, the EN bit of the AES_CR register must first be cleared.
Reading the AES_IVRx registers returns the latest counter value (useful for managing suspend mode) when the AES peripheral is disabled and returns zeros when it is enabled.
The AES_IVRx registers are not affected by the data swapping feature controlled by the DATATYPE[1:0] bitfield of the CRYP_CR register.
15.4.13 AES DMA interface
The AES peripheral provides an interface to connect to the DMA (direct memory access) controller. The DMA operation is controlled through the AES_CR register.
Data input using DMA
Setting the DMAINEN bit of the AES_CR register enables DMA writing into AES. The AES peripheral then initiates a DMA request during the input phase each time it requires a word to be written to the AES_DINR register. It asserts four DMA requests to transfer one 128-bit (four-word) input data block from memory, as shown in Figure 74.
See Table 71 for recommended DMA configuration.
Table 71. DMA channel configuration for memory-to-AES data transfer
| DMA channel control register field | Recommended configuration |
|---|---|
| Transfer size | Message length: a multiple of 128 bits. According to the algorithm and the mode selected, special padding/ciphertext stealing might be required. |
| Source burst size (memory) | Single |
| Destination burst size (peripheral) | Single |
| DMA FIFO size | AES_FIFO_size = 4 bytes. |
| Source transfer width (memory) | 32-bit words |
| Destination transfer width (peripheral) | 32-bit words |
| Source address increment (memory) | Yes, after each 32-bit transfer |
| Destination address increment (peripheral) | Fixed address of AES_DINR (no increment) |
Figure 74. DMA transfer of a 128-bit data block during input phase
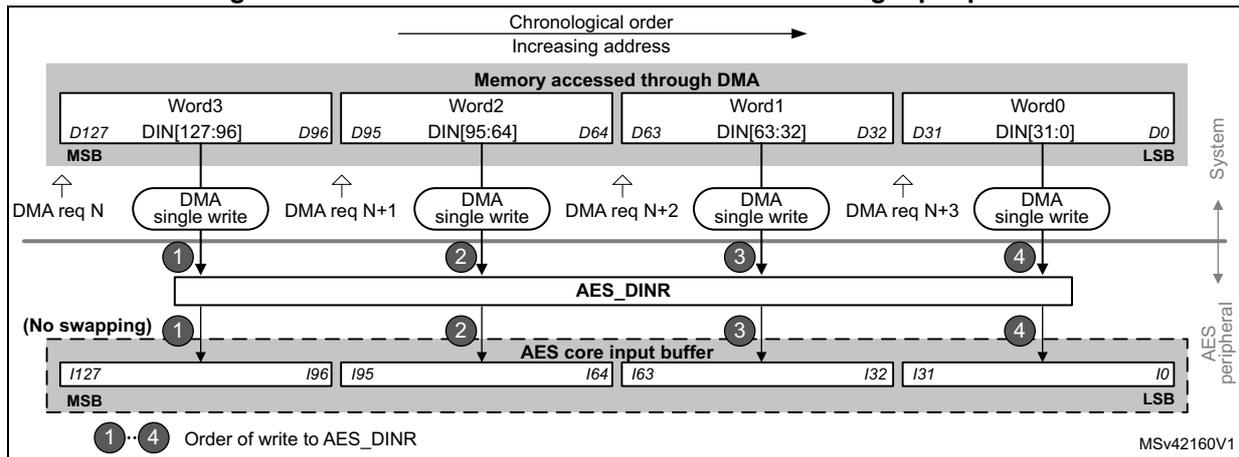
The diagram shows the flow of data from memory to the AES peripheral. At the top, 'Memory accessed through DMA' contains four words: Word3 (D127-D96), Word2 (D95-D64), Word1 (D63-D32), and Word0 (D31-D0). Below this, four DMA requests (DMA req N, DMA req N+1, DMA req N+2, DMA req N+3) are shown, each corresponding to a 'DMA single write' of a 32-bit word. Arrows labeled 1, 2, 3, and 4 show these words being written into the 'AES_DINR' register. Below the register is the 'AES core input buffer' (128 bits, I127-I0). Arrows show the data being transferred from the register into the buffer. A note '(No swapping)' is present. At the bottom, a dashed box shows the 'Order of write to AES_DINR' as 1, 2, 3, 4, which corresponds to Word3, Word2, Word1, Word0 respectively. The diagram is labeled 'System' on the right and 'AES peripheral' on the right. The identifier 'MSV42160V1' is in the bottom right corner.
Data output using DMA
Setting the DMAOUTEN bit of the AES_CR register enables DMA reading from AES. The AES peripheral then initiates a DMA request during the Output phase each time it requires a
word to be read from the AES_DOUTR register. It asserts four DMA requests to transfer one 128-bit (four-word) output data block to memory, as shown in Figure 75.
See Table 72 for recommended DMA configuration.
Table 72. DMA channel configuration for AES-to-memory data transfer
| DMA channel control register field | Recommended configuration |
|---|---|
| Transfer size | It is the message length multiple of AES block size (4 words). According to the case extra bytes will have to be discarded. |
| Source burst size (peripheral) | Single |
| Destination burst size (memory) | Single |
| DMA FIFO size | AES_FIFO_size = 4 bytes |
| Source transfer width (peripheral) | 32-bit words |
| Destination transfer width (memory) | 32-bit words |
| Source address increment (peripheral) | Fixed address of AES_DINR (no increment) |
| Destination address increment (memory) | Yes, after each 32-bit transfer |
Figure 75. DMA transfer of a 128-bit data block during output phase
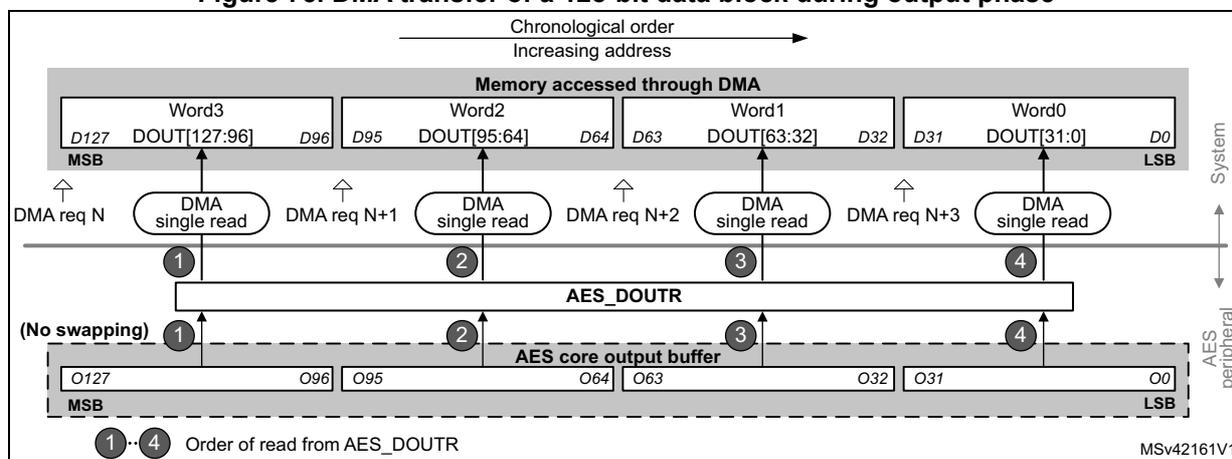
The diagram illustrates the DMA transfer of a 128-bit data block during the output phase. At the top, a horizontal arrow indicates 'Chronological order' and 'Increasing address'. Below this, the 'Memory accessed through DMA' is shown with four words: Word3 (D127 to D96), Word2 (D95 to D64), Word1 (D63 to D32), and Word0 (D31 to D0). Each word is transferred via a 'DMA single read' request (DMA req N, DMA req N+1, DMA req N+2, DMA req N+3). Below the memory, the 'AES_DOUTR' register is shown, which receives data from the 'AES core output buffer'. The buffer contains 128 bits (O127 to O0) and is labeled '(No swapping)'. The 'Order of read from AES_DOUTR' is indicated by numbers 1 to 4, corresponding to the DMA requests. The diagram also shows the 'System' and 'AES peripheral' data paths.
DMA operation in different operating modes
DMA operations are usable when Mode 1 (encryption) or Mode 3 (decryption) are selected via the MODE[1:0] bitfield of the register AES_CR. As in Mode 2 (key derivation) the AES_KEYRx registers must be written by software, enabling the DMA transfer through the DMAINEN and DMAOUTEN bits of the AES_CR register have no effect in that mode.
DMA single requests are generated by AES until it is disabled. So, after the data output phase at the end of processing of a 128-bit data block, AES switches automatically to a new data input phase for the next data block, if any.
When the data transferring between AES and memory is managed by DMA, the CCF flag is not relevant and can be ignored (left set) by software. It must only be cleared when transiting back to data transferring managed by software. See Suspend/resume operations in ECB/CBC modes in Section 15.4.8: AES basic chaining modes (ECB, CBC) as example.
15.4.14 AES error management
The read error flag (RDERR) and write error flag (WRERR) of the AES_SR register are set when an unexpected read or write operation, respectively, is detected. An interrupt can be generated if the error interrupt enable (ERRIE) bit of the AES_CR register is set. For more details, refer to Section 15.5: AES interrupts .
Note: AES is not disabled after an error detection and continues processing.
AES can be re-initialized at any moment by clearing then setting the EN bit of the AES_CR register.
Read error flag (RDERR)
When an unexpected read operation is detected during the computation phase or during the input phase, the AES read error flag (RDERR) is set in the AES_SR register. An interrupt is generated if the ERRIE bit of the AES_CR register is set.
The RDERR flag is cleared by setting the corresponding ERRRC bit of the AES_CR register.
Write error flag (WDERR)
When an unexpected write operation is detected during the computation phase or during the output phase, the AES write error flag (WRERR) is set in the AES_SR register. An interrupt is generated if the ERRIE bit of the AES_CR register is set.
The WDERR flag is cleared by setting the corresponding ERRRC bit of the AES_CR register.
15.5 AES interrupts
There are three individual maskable interrupt sources generated by the AES peripheral, to signal the following events:
- • computation completed
- • read error, see Section 15.4.14
- • write error, see Section 15.4.14
These three sources are combined into a common interrupt signal aes_it that connects to NVIC (nested vectored interrupt controller).
Figure 76. AES interrupt signal generation
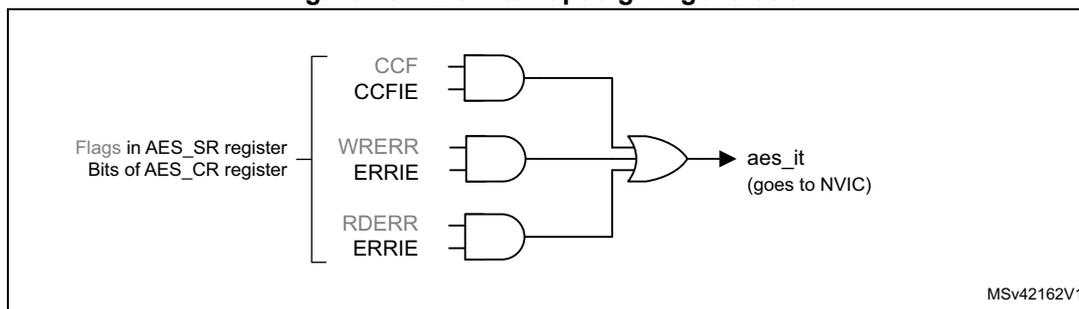
Each AES interrupt source can individually be enabled/disabled, by setting/clearing the corresponding enable bit of the AES_CR register. See Figure 76 .
The status of the individual maskable interrupt sources can be read from the AES_SR register.
Table 73 gives a summary of the interrupt sources, their event flags and enable bits.
Table 73. AES interrupt requests
| AES interrupt event | Event flag | Enable bit |
|---|---|---|
| computation completed flag | CCF | CCFIE |
| read error flag | RDERR | ERRIE |
| write error flag | WRERR | ERRIE |
15.6 AES processing latency
The tables below summarize the latency to process a 128-bit block for each mode of operation.
Table 74. Processing latency (in clock cycle)
| Mode of operation | Algorithm | Input phase | Computation phase | Output phase | Total |
|---|---|---|---|---|---|
| Mode 1: Encryption | ECB, CBC, CTR | 8 | 202 | 4 | 214 |
| Mode 2: Key derivation for decryption | ECB, CBC | - | 80 | - | 80 |
| Mode 3: Decryption | ECB, CBC, CTR | 8 | 202 | 4 | 214 |
| Mode 4: Key derivation then decryption | ECB, CBC | 8 | 276 | 4 | 288 |
15.7 AES registers
15.7.1 AES control register (AES_CR)
Address offset: 0x00
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | DMAOUTEN | DMAINEN | ERRIE | CCFIE | ERRC | CCFC | CHMOD[1:0] | MODE[1:0] | DATATYPE[1:0] | EN | |||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bit 31:13 Reserved, must be kept at zero
Bit 12 DMAOUTEN : DMA output enable
This bit enables/disables data transferring with DMA, in the output phase:
0: Disable
1: Enable
When the bit is set, DMA requests are automatically generated by AES during the output data phase. This feature is only effective when Mode 1 or Mode 3 is selected through the MODE[1:0] bitfield. It is not effective for Mode 2 (key derivation).
Usage of DMA with Mode 4 (single decryption) is not recommended.
Bit 11 DMAINEN : DMA input enable
This bit enables/disables data transferring with DMA, in the input phase:
0: Disable
1: Enable
When the bit is set, DMA requests are automatically generated by AES during the input data phase. This feature is only effective when Mode 1 or Mode 3 is selected through the MODE[1:0] bitfield. It is not effective for Mode 2 (key derivation).
Usage of DMA with Mode 4 (single decryption) is not recommended.
Bit 10 ERRIE : Error interrupt enable
This bit enables or disables (masks) the AES interrupt generation when RDERR and/or WRERR is set:
0: Disable (mask)
1: Enable
Bit 9 CCFIE : CCF interrupt enable
This bit enables or disables (masks) the AES interrupt generation when CCF (computation complete flag) is set:
0: Disable (mask)
1: Enable
Bit 8 ERRC: Error flag clearUpon written to 1, this bit clears the RDERR and WRERR error flags in the AES_SR register:
0: No effect
1: Clear RDERR and WRERR flags
Reading the flag always returns zero.
Bit 7 CCFC: Computation complete flag clearUpon written to 1, this bit clears the computation complete flag (CCF) in the AES_SR register:
0: No effect
1: Clear CCF
Reading the flag always returns zero.
Bits 6:5 CHMOD[1:0]: Chaining mode selectionThis bitfield selects the AES chaining mode:
00: Electronic codebook (ECB)
01: Cipher-Block Chaining (CBC)
10: Counter Mode (CTR)
11: Reserved
The bitfield value change is allowed only when AES is disabled, so as to avoid an unpredictable behavior.
Bits 4:3 MODE[1:0]: AES operating modeThis bitfield selects the AES operating mode:
00: Mode 1: encryption
01: Mode 2: key derivation (or key preparation for ECB/CBC decryption)
10: Mode 3: decryption
11: Mode 4: key derivation then single decryption
The bitfield value change is allowed only when AES is disabled, so as to avoid an unpredictable behavior. Any attempt to selecting Mode 4 while either ECB or CBC chaining mode is not selected, defaults to effective selection of Mode 3. It is not possible to select a Mode 3 following a Mode 4.
Bits 2:1 DATATYPE[1:0]: Data type selectionThis bitfield defines the format of data written in the AES_DINR register or read from the AES_DOUTR register, through selecting the mode of data swapping:
00: None
01: Half-word (16-bit)
10: Byte (8-bit)
11: Bit
For more details, refer to Section 15.4.10: AES data registers and data swapping .
The bitfield value change is allowed only when AES is disabled, so as to avoid an unpredictable behavior.
Bit 0 EN: AES enableThis bit enables/disables the AES peripheral:
0: Disable
1: Enable
At any moment, clearing then setting the bit re-initializes the AES peripheral.
This bit is automatically cleared by hardware when the key preparation process ends (Mode 2).
15.7.2 AES status register (AES_SR)
Address offset: 0x04
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. |
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WRERR | RDERR | CCF |
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
Bits 31:3 Reserved, must be kept at zero
Bit 2 WRERR: Write error
This flag indicates the detection of an unexpected write operation to the AES_DINR register (during computation or data output phase):
0: Not detected
1: Detected
The flag is set by hardware. It is cleared by software upon setting the ERRRC bit of the AES_CR register.
Upon the flag setting, an interrupt is generated if enabled through the ERRRIE bit of the AES_CR register.
The flag setting has no impact on the AES operation.
The flag is not effective when key derivation mode is selected.
Bit 1 RDERR: Read error flag
This flag indicates the detection of an unexpected read operation from the AES_DOUTR register (during computation or data input phase):
0: Not detected
1: Detected
The flag is set by hardware. It is cleared by software upon setting the ERRRC bit of the AES_CR register.
Upon the flag setting, an interrupt is generated if enabled through the ERRRIE bit of the AES_CR register.
The flag setting has no impact on the AES operation.
The flag is not effective when key derivation mode is selected.
Bit 0 CCF: Computation completed flag
This flag indicates whether the computation is completed:
0: Not completed
1: Completed
The flag is set by hardware upon the completion of the computation. It is cleared by software, upon setting the CCFC bit of the AES_CR register.
Upon the flag setting, an interrupt is generated if enabled through the CCFIE bit of the AES_CR register.
The flag is significant only when the DMAOUTEN bit is 0. It may stay high when DMA_EN is 1.
15.7.3 AES data input register (AES_DINR)
Address offset: 0x08
Reset value: 0x0000 0000
Only 32-bit access type is supported.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| DIN[x+31:x+16] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| DIN[x+15:x] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 This bitfield feeds a 32-bit input buffer. A 4-fold sequential write to this bitfield during the input phase virtually writes a complete 128-bit block of input data to the AES peripheral. Upon each write, the data from the input buffer are handled by the data swap block according to the DATATYPE[1:0] bitfield, then written into the AES core 128-bit input buffer.
The substitution for ‘x’, from the first to the fourth write operation, is: 96, 64, 32, and 0. In other words, data from the first to the fourth write operation are: DIN[127:96], DIN[95:64], DIN[63:32], and DIN[31:0].
The data signification of the input data block depends on the AES operating mode:
- - Mode 1 (encryption): plaintext
- - Mode 2 (key derivation): the bitfield is not used (AES_KEYRx registers used for input)
- - Mode 3 (decryption) and Mode 4 (key derivation then single decryption): ciphertext
The data swap operation is described in Section 15.4.10: AES data registers and data swapping on page 355 .
15.7.4 AES data output register (AES_DOUTR)
Address offset: 0x0C
Reset value: 0x0000 0000
Only 32-bit access type is supported.
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| DOUT[x+31:x+16] | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| DOUT[x+15:0] | |||||||||||||||
| r | r | r | r | r | r | r | r | r | r | r | r | r | r | r | r |
Bits 31:0 DOUT[x+31:x] : One of four 32-bit words of a 128-bit output data block being read from the peripheral
This bitfield fetches a 32-bit output buffer. A 4-fold sequential read of this bitfield, upon the computation completion (CCF set), virtually reads a complete 128-bit block of output data from the AES peripheral. Before reaching the output buffer, the data produced by the AES core are handled by the data swap block according to the DATATYPE[1:0] bitfield.
The substitution for DOUT[x+31:x], from the first to the fourth read operation, is: 96, 64, 32, and 0. In other words, data from the first to the fourth read operation are: DOUT[127:96], DOUT[95:64], DOUT[63:32], and DOUT[31:0].
The data signification of the output data block depends on the AES operating mode:
- - Mode 1 (encryption): ciphertext
- - Mode 2 (key derivation): the bitfield is not used (AES_KEYRx registers used for output).
- - Mode 3 (decryption) and Mode 4 (key derivation then single decryption): plaintext
The data swap operation is described in Section 15.4.10: AES data registers and data swapping on page 355 .
15.7.5 AES key register 0 (AES_KEYR0)
Address offset: 0x10
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| KEY[31:16] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| KEY[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 KEY[31:0] : Cryptographic key, bits [31:0]
This bitfield contains the bits [31:0] of the AES encryption or decryption key, depending on the operating mode:
- - In Mode 1 (encryption), Mode 2 (key derivation) and Mode 4 (key derivation then single decryption): the value to write into the bitfield is the encryption key.
- - In Mode 3 (decryption): the value to write into the bitfield is the encryption key to be derived before being used for decryption. After writing the encryption key into the bitfield, its reading before enabling AES returns the same value. Its reading after enabling AES and after the CCF flag is set returns the decryption key derived from the encryption key.
Note: In mode 4 (key derivation then single decryption) the bitfield always contains the encryption key.
The AES_KEYRx registers may be written only when the AES peripheral is disabled.
Refer to Section 15.4.11: AES key registers on page 357 for more details.
15.7.6 AES key register 1 (AES_KEYR1)
Address offset: 0x14
Reset value: 0x0000 0000
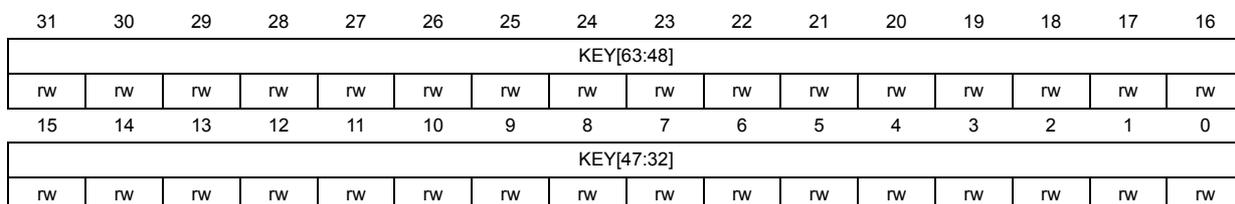
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| KEY[63:48] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| KEY[47:32] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 KEY[63:32] : Cryptographic key, bits [63:32]
Refer to the AES_KEYR0 register for description of the KEY[127:0] bitfield.
15.7.7 AES key register 2 (AES_KEYR2)
Address offset: 0x18
Reset value: 0x0000 0000
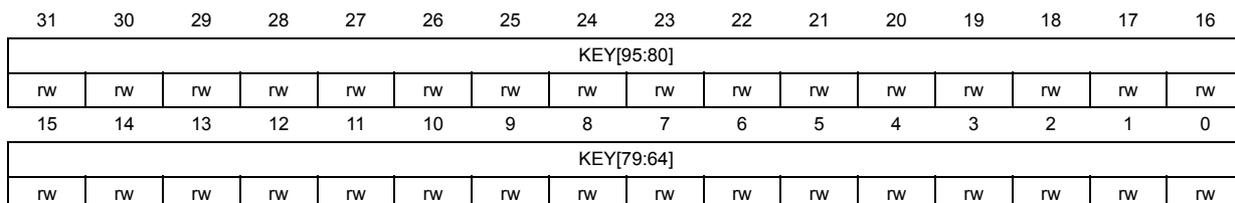
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| KEY[95:80] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| KEY[79:64] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 KEY[95:64] : Cryptographic key, bits [95:64]
Refer to the AES_KEYR0 register for description of the KEY[127:0] bitfield.
15.7.8 AES key register 3 (AES_KEYR3)
Address offset: 0x1C
Reset value: 0x0000 0000
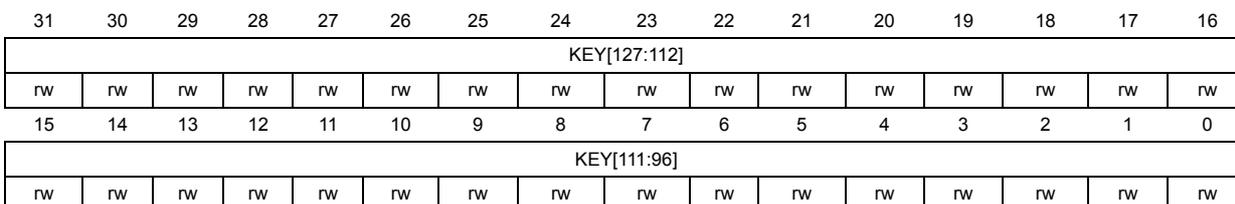
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| KEY[127:112] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| KEY[111:96] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 KEY[127:96] : Cryptographic key, bits [127:96]
Refer to the AES_KEYR0 register for description of the KEY[127:0] bitfield.
15.7.9 AES initialization vector register 0 (AES_IVR0)
Address offset: 0x20
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| IVI[31:16] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| IVI[15:0] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 IVI[31:0] : Initialization vector input, bits [31:0]
Refer to Section 15.4.12: AES initialization vector registers on page 357 for description of the IVI[127:0] bitfield.
The initialization vector is only used in chaining modes other than ECB.
The initialization vector may be written only when the AES peripheral is disabled.
Reading this bitfield while AES is enabled returns 0x0000 0000.
15.7.10 AES initialization vector register 1 (AES_IVR1)
Address offset: 0x24
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
| IVI[63:48] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| IVI[47:32] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 IVI[63:32] : Initialization vector input, bits [63:32]
Refer to Section 15.4.12: AES initialization vector registers on page 357 for description of the IVI[127:0] bitfield.
The initialization vector is only used in chaining modes other than ECB.
The initialization vector may be written only when the AES peripheral is disabled.
Reading this bitfield while AES is enabled returns 0x0000 0000.
15.7.11 AES initialization vector register 2 (AES_IVR2)
Address offset: 0x28
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| IVI[95:80] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| IVI[79:64] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 IVI[95:64] : Initialization vector input, bits [95:64]
Refer to Section 15.4.12: AES initialization vector registers on page 357 for description of the IVI[127:0] bitfield.
The initialization vector is only used in chaining modes other than ECB.
The initialization vector may be written only when the AES peripheral is disabled.
Reading this bitfield while AES is enabled returns 0x0000 0000.
15.7.12 AES initialization vector register 3 (AES_IVR3)
Address offset: 0x2C
Reset value: 0x0000 0000
| 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| IVI[127:112] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
| 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
| IVI[111:96] | |||||||||||||||
| rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw | rw |
Bits 31:0 IVI[127:96] : Initialization vector input, bits [127:96]
Refer to Section 15.4.12: AES initialization vector registers on page 357 for description of the IVI[127:0] bitfield.
The initialization vector is only used in chaining modes other than ECB.
The initialization vector may be written only when the AES peripheral is disabled.
Reading this bitfield while AES is enabled returns 0x0000 0000.
15.7.13 AES register map
Table 75. AES register map and reset values
| Offset | Register | 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 | 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0x0000 | AES_CR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | DMAOUTEN | DMAINEN | ERRIE | CCFIE | ERRC | CCFC | CHMOD[1:0] | MODE[1:0] | DATATYPE[1:0] | EN | |||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||||||||||||||||||||
Table 75. AES register map and reset values (continued)
| Offset | Register | 31 | 30 | 29 | 28 | 27 | 26 | 25 | 24 | 23 | 22 | 21 | 20 | 19 | 18 | 17 | 16 | 15 | 14 | 13 | 12 | 11 | 10 | 9 | 8 | 7 | 6 | 5 | 4 | 3 | 2 | 1 | 0 | |
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 0x0004 | AES_SR | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | Res. | WRERR | RDERR | CCF |
| Reset value | 0 | 0 | 0 | |||||||||||||||||||||||||||||||
| 0x0008 | AES_DINR x=96,64,32,0 | DIN[x+31:x] | ||||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||
| 0x000C | AES_DOUTR x=96,64,32,0 | DOUT[x+31:x] | ||||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||
| 0x0010 | AES_KEYR0 | KEY[31:0] | ||||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||
| 0x0014 | AES_KEYR1 | KEY[63:32] | ||||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||
| 0x0018 | AES_KEYR2 | KEY[95:64] | ||||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||
| 0x001C | AES_KEYR3 | KEY[127:96] | ||||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||
| 0x0020 | AES_IVR0 | IVI[31:0] | ||||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||
| 0x0024 | AES_IVR1 | IVI[63:32] | ||||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||
| 0x0028 | AES_IVR2 | IVI[95:64] | ||||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||
| 0x002C | AES_IVR3 | IVI[127:96] | ||||||||||||||||||||||||||||||||
| Reset value | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | 0 | ||
Refer to Section 2.2 on page 51 for the register boundary addresses.